Overview
Provides instructions to configure a Cisco Umbrella SASE auto tunnel in Firewall Management Center (FMC) to forward branch DNS and web traffic through a Secure Internet Gateway (SIG) tunnel for cloud security inspection.
Before you begin
Ensure that you review Prerequisites for Configuring Umbrella SASE Tunnels and Best Practices for SASE Umbrella Tunnels.
Procedure
| 1. | In Management Center, choose Devices > VPN > Site To Site. |
|
| 2. | Click + SASE Topology to open the SASE topology wizard. |
|
| 3. | Enter a unique Topology Name For our example, enter VPN-MumbaiUmbrella. |
|
| 4. | Pre-shared Key: This key is auto-generated according to the Umbrella PSK requirements. The device and Umbrella share this secret key, and IKEv2 uses it for authentication. You can override the auto-generated key. If you want to configure this key, it must be between 16 and 64 characters in length, include at least one uppercase letter, one lowercase letter, one numeral, and have no special characters. Each topology must have a unique pre-shared key. If a topology has multiple tunnels, all the tunnels have the same pre-shared key. |
|
| 5. | Choose a data center from the Umbrella Data center drop-down list. The Umbrella data centers are auto populated with the region and IP addresses. |
|
| 6. | Click Add to add a threat defense node as an endpoint in the SASE topology. |
|
| 7. | Click Next to view the summary of the Umbrella SASE tunnel configuration.
|
|
| 8. | Check the Deploy configuration on threat defense nodes check box to trigger deployment of the network tunnels to the threat defense. This deployment only occurs after the tunnels are deployed on Umbrella. Local tunnel ID is required for the threat defense deployment. |
|
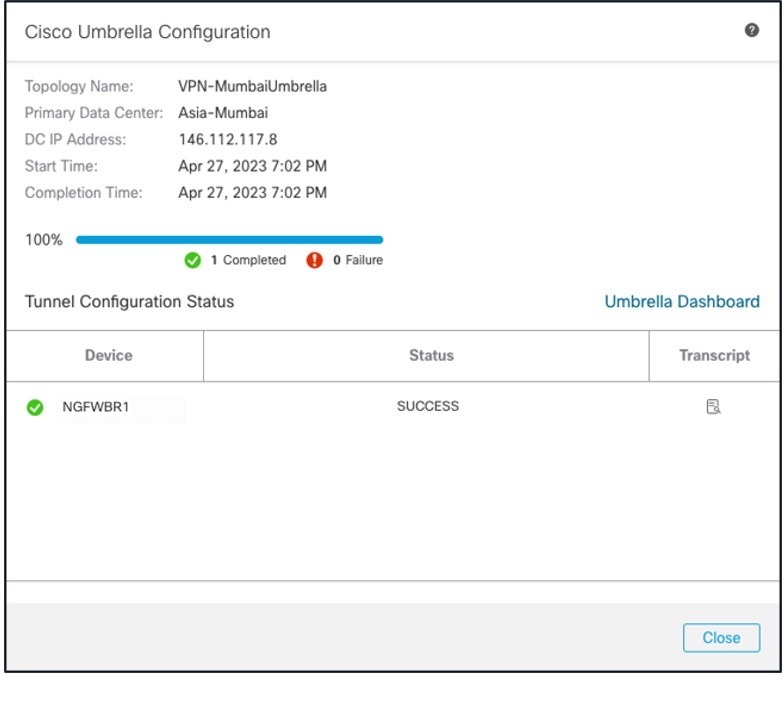
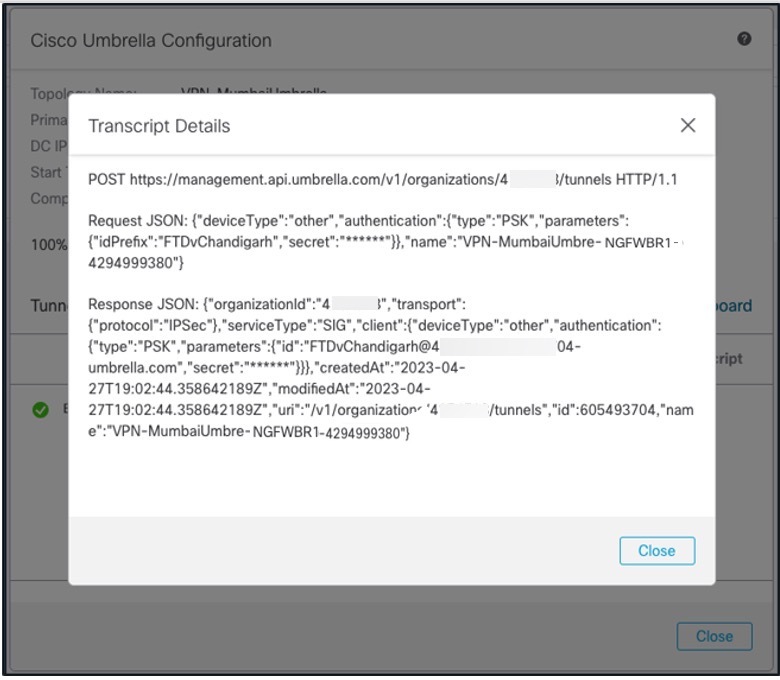
| 9. | Click Save.
This action:
|
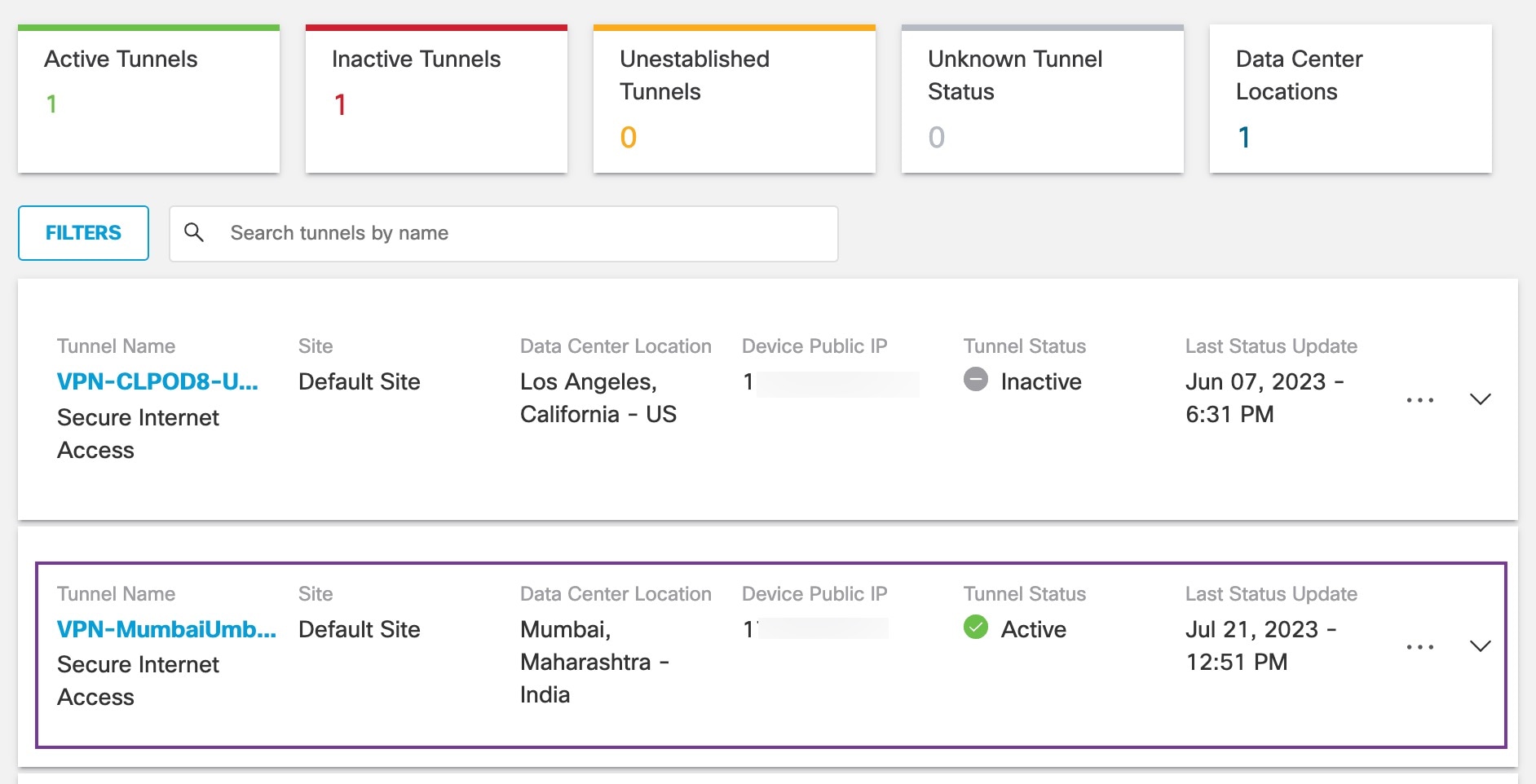
What to do next
For the traffic intended to flow through the SASE tunnel, configure a PBR policy with a specific match criteria to send the traffic through the VTI.