SD-WAN capabilities
SD-WAN capabilities are software-defined networking features that
-
replace traditional WAN routers and are agnostic to WAN transport technologies
-
provide dynamic, policy-based, application path selection across multiple WAN connections, and
-
support service chaining for additional services such as WAN optimization and firewalls.
SD-WAN capabilities in Secure Firewall
As organizations expand their operations across multiple branch locations, ensuring secure and streamlined connectivity becomes paramount. Deploying a secure branch network infrastructure involves complex configurations, which can be time-consuming and prone to configuration errors if not handled properly. However, organizations can overcome these challenges by leveraging Management Center and Threat Defense devices for a simplified and secure branch deployment.
By integrating Secure Firewall as a foundational component of the branch network architecture, organizations can establish a strong security baseline while simplifying the deployment process. This approach enables organizations to enforce unified security policies, optimize traffic routing, and ensure resilient connectivity.
Some of the SD-WAN capabilities supported on the Cisco Secure Firewall include:
-
Simplified management:
-
SD-WAN Wizard
-
SASE: Umbrella auto tunnel deployment
-
Dynamic VTI (DVTI) hub spoke topology simplification
-
-
Application awareness:
-
Direct Internet Access (DIA) for public cloud and guest user
-
Policy based routing (PBR) using applications as a match criteria
-
Local tunnel ID support for Umbrella
-
-
Increased usable bandwidth:
-
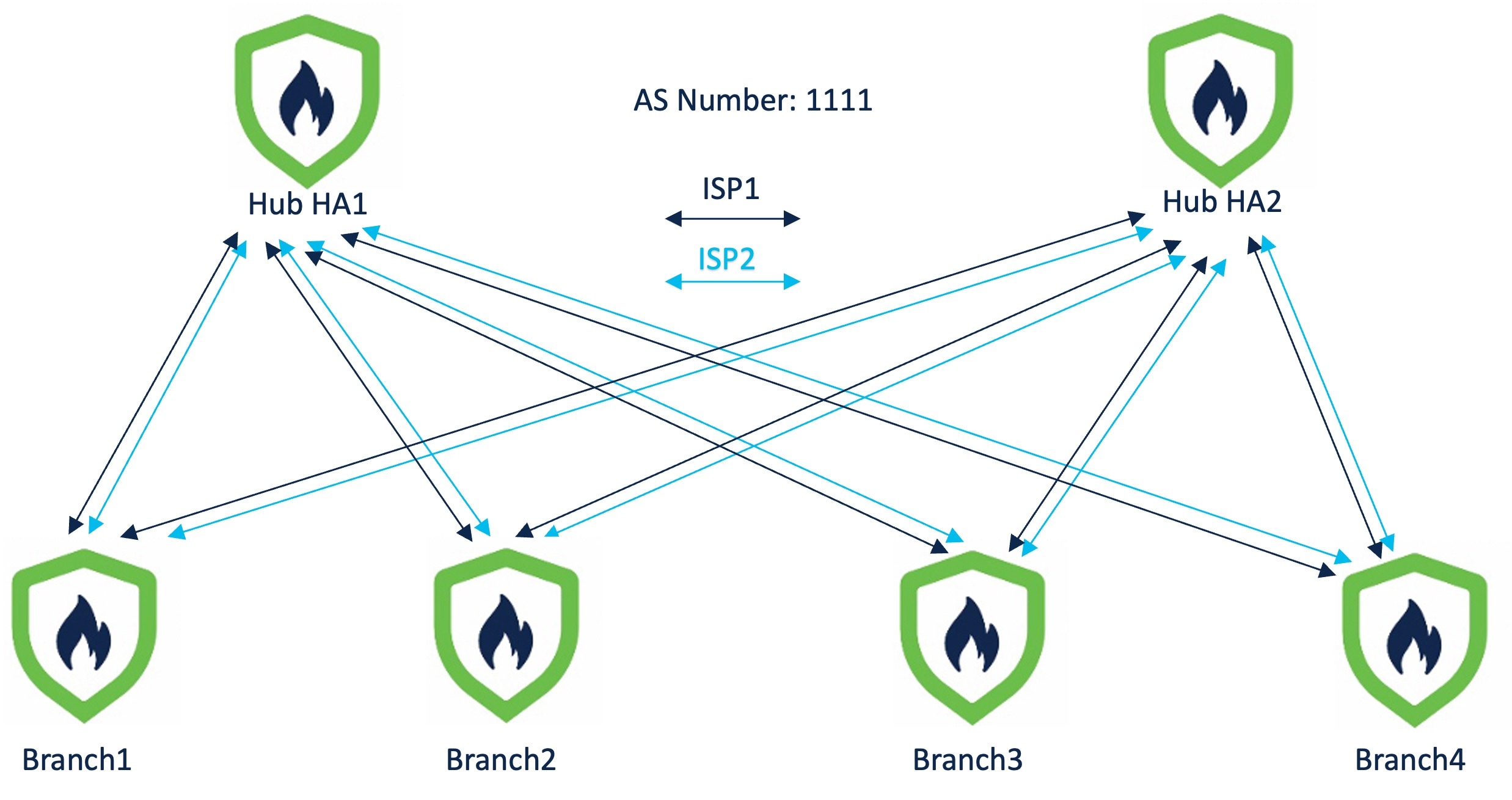
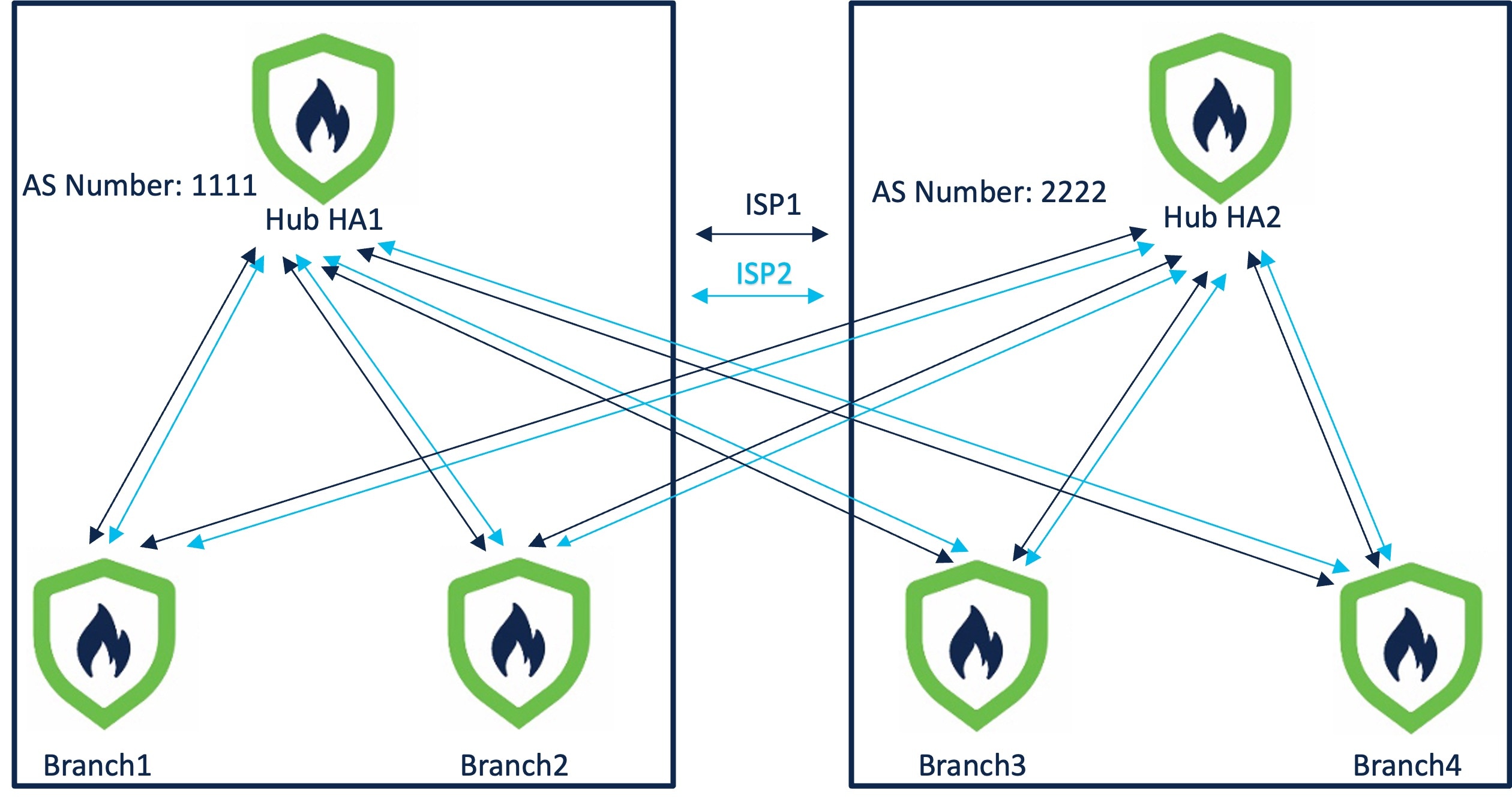
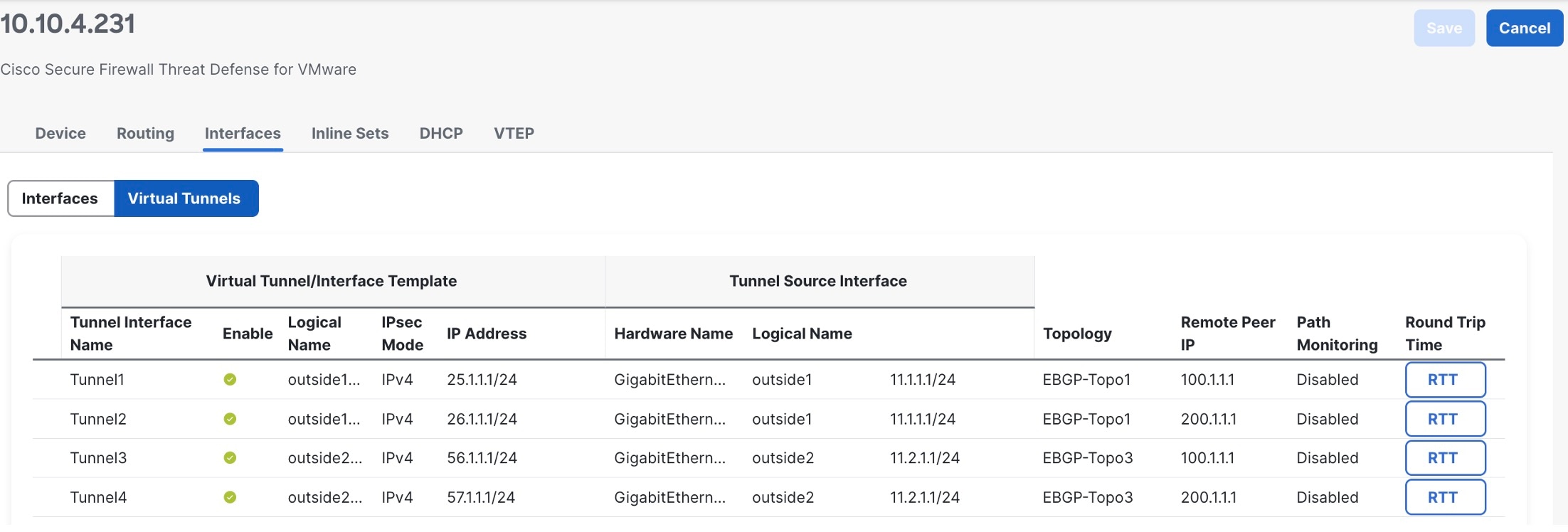
ECMP support for load balancing across multiple ISPs and VTIs
-
Application-based load balancing using PBR
-
-
High availability with near zero network downtime:
-
Dual ISP configuration
-
Optimal path selection based on application-based interface monitoring.
-
-
Secure elastic connectivity:
-
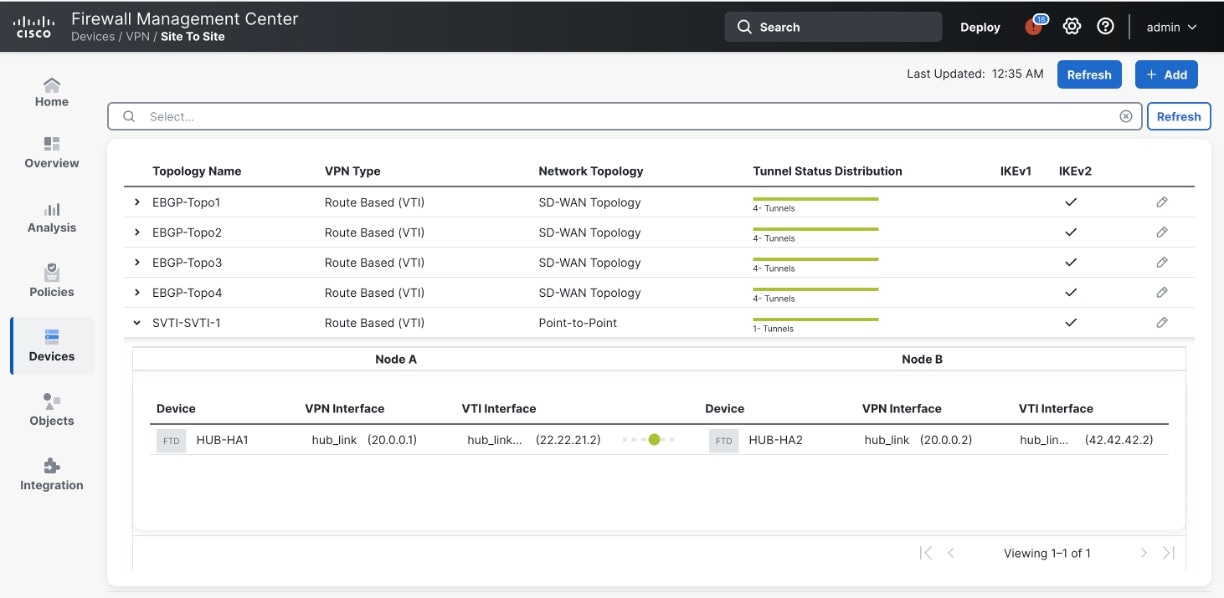
Route-based (VTI) VPN tunnels between headquarters (hub) and branches (spokes)
-
IPv4 and IPv6 BGP, IPv4 and IPv6 OSPF, and IPv4 EIGRP over VTI
-
DVTI hubs that support spokes with static or dynamic IP
-


 ) icon. A pane with tunnel details and more actions is displayed.
) icon. A pane with tunnel details and more actions is displayed.



 Feedback
Feedback