Overview
Describes BGP Accept Own feature, covering preference mechanisms in best path selection, processing of Accept Own routes in BGP VPN configurations, and step-by-step procedures to enable BGP Accept Own in deployments.
A BGP Accept Own mechanism is a BGP routing feature that
-
allows a BGP speaker to accept VPN routes that it originally advertised but receives back from a route-reflector
-
uses the special ACCEPT_OWN community attribute to bypass standard self-origination filters such as ORIGINATOR_ID and NEXTHOP checks, and
-
enables centralized control of route imports across VRFs in MPLS VPN environments without requiring configuration changes on provider edge routers.
Default BGP route rejection behavior:
By default, according to BGP protocol (RFC 4271), a BGP speaker rejects routes it originated if they are returned by a route-reflector.
BGP Accept Own:
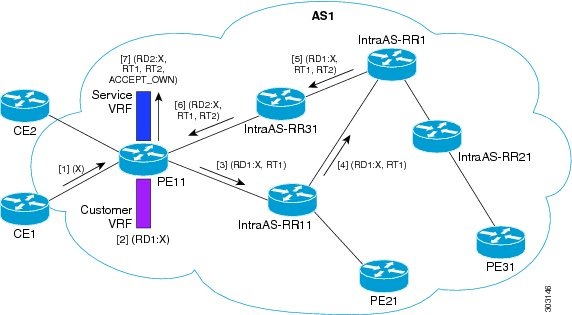
The BGP Accept Own feature changes this behavior: when the ACCEPT_OWN community is attached to a prefix (by a route-reflector via an outbound route-policy), it signals the receiving router to accept the reflected route even if it originally advertised that prefix. This is especially valuable in MPLS VPN extranets, where route import/export must be managed centrally.
Use case: Extranet auto-configuration in MPLS VPNs:
One primary use case is auto-configuration of extranets within MPLS VPNs. Conventionally, controlling route imports between VRFs for extranets requires updating import route-targets or policies on each PE router. With BGP Accept Own, route-reflectors can manage which prefixes are imported between VRFs without additional PE configuration. This approach makes operations more scalable and flexible.
Route-reflector handling and community propagation
Route-reflectors attach the ACCEPT_OWN community when advertising selected prefixes to the originating PE. The addition of this community should be limited to outbound policies targeting only the originator, to avoid unnecessary propagation. The InterAS route-reflector may also adjust the set of route targets (RTs) when sending routes with the ACCEPT_OWN community. This enables precise control over which VRFs receive the reflected routes.