- Preface
- Software Licensing
- The Cisco IOS command-line interface (CLI)
- Configuring Interfaces
- Switch Alarms
- Initial Switch Configuration (IP address assignments and DHCP autoconfiguration)
- How to Setup and Use the Cisco Configuration Engine
- How to Create and Manage Switch Clusters
- Performing Switch Administration
- Configuring Precision Time Protocol (PTP)
- Configuring PROFINET
- Common Industrial Protocol (CIP)
- Configuring SDM Templates
- Configuring Switch-Based Authentication
- Configuring IEEE 802.1x Port-Based Authentication
- MACsec
- Web-Based Authentication
- Configuring Smartports Macros
- Configuring SGACL Monitor Mode and SGACL Logging
- Configuring SGT Exchange Protocol over TCP (SXP) and Layer 3 Transport
- Configuring VLANs
- VLAN Trunking Protocol (VTP)
- Configuring Voice VLAN
- How to Configure Spanning Tree Protocol (STP)
- Configuring MSTP
- Configuring Optional Spanning-Tree Features
- Configuring Resilient Ethernet Protocol
- Configuring the FlexLinks and the MAC Address-Table Move Update
- Configuring DHCP
- Dynamic Address Resolution Protocol (ARP)
- Configuring IP Source Guard
- How to Configure Internet Group Management Protocol (IGMP) and Multicast VLAN Registration (MVR)
- Configuring Port-Based Traffic Control
- Configuring LLDP, LLDP-MED, and Wired Location Service
- Configuring SPAN and RSPAN
- One-to-one (1:1) Layer 2 Network Address Translation (NAT)
- How to Configure CDP
- Configuring UniDirectional Link Detection (UDLD)
- Configuring RMON
- Configuring System Message Logging
- Configuring Simple Network Management Protocol (SNMP)
- Network Security with ACLs
- Configuring Quality of Service (QoS)
- Configuring Static IP Unicast Routing
- Configuring IPv6 Host Functions
- Configuring Link State Tracking
- Configuring IP multicast routing
- Configuring Multicast Source Discovery Protocol (MSDP)
- Configuring Multicast Listener Discovery (MLD) snooping
- Configuring HSRP and VRRP
- Configuring IPv6 access control lists (ACLs)
- Configuring Embedded Event Manager (EEM)
- IP Unicast Routing
- IPv6 Unicast Routing
- Unicast Routing Overview
- Configuring Cisco IOS IP SLAs Operations
- Configuring Dying-Gasp
- How to Configure Enhanced Object Tracking
- Configuring MODBUS TCP
- Configuring Ethernet CFM
- Working with the Flash File System
- How to Configure EtherChannels
- Troubleshooting
- How to use a Secure Digital (SD) flash memory module (SD card)
- Restrictions for Port-Based Traffic Control
- Information About Port-Based Traffic Control
- How to Configure Port-Based Traffic Control
- Enabling Unicast Storm Control: Example
- Enabling Broadcast Address Storm Control on a Port: Example
- Enabling Small-Frame Arrival Rate: Example
- Configuring a Protected Port: Example
- Blocking Flooding on a Port: Example
- Configuring Port Security: Examples
- Configuring Port Security Aging: Examples
- Configuring Protocol Storm Protection: Example
Configuring Port-Based Traffic Control
Restrictions for Port-Based Traffic Control
■![]() To use this feature, the switch must be running the LAN Base image.
To use this feature, the switch must be running the LAN Base image.
Information About Port-Based Traffic Control
Storm Control
Storm control prevents traffic on a LAN from being disrupted by a broadcast, multicast, or unicast storm on one of the physical interfaces. A LAN storm occurs when packets flood the LAN, creating excessive traffic and degrading network performance. Errors in the protocol-stack implementation, mistakes in network configurations, or users issuing a denial-of-service attack can cause a storm.
Storm control (or traffic suppression) monitors packets passing from an interface to the switching bus and determines if the packet is unicast, multicast, or broadcast. The switch counts the number of packets of a specified type received within the 1-second time interval and compares the measurement with a predefined suppression-level threshold.
Storm control uses one of these methods to measure traffic activity:
■![]() Bandwidth as a percentage of the total available bandwidth of the port that can be used by the broadcast, multicast, or unicast traffic
Bandwidth as a percentage of the total available bandwidth of the port that can be used by the broadcast, multicast, or unicast traffic
■![]() Traffic rate in packets per second at which broadcast, multicast, or unicast packets are received.
Traffic rate in packets per second at which broadcast, multicast, or unicast packets are received.
■![]() Traffic rate in bits per second at which broadcast, multicast, or unicast packets are received.
Traffic rate in bits per second at which broadcast, multicast, or unicast packets are received.
■![]() Traffic rate in packets per second and for small frames. This feature is enabled globally. The threshold for small frames is configured for each interface.
Traffic rate in packets per second and for small frames. This feature is enabled globally. The threshold for small frames is configured for each interface.
With each method, the port blocks traffic when the rising threshold is reached. The port remains blocked until the traffic rate drops below the falling threshold (if one is specified) and then resumes normal forwarding. If the falling suppression level is not specified, the switch blocks all traffic until the traffic rate drops below the rising suppression level. In general, the higher the level, the less effective the protection against broadcast storms.
Note: When the storm control threshold for multicast traffic is reached, all multicast traffic except control traffic, such as bridge protocol data unit (BDPU) and Cisco Discovery Protocol (CDP) frames, are blocked. However, the switch does not differentiate between routing updates, such as OSPF, and regular multicast data traffic, so both types of traffic are blocked.
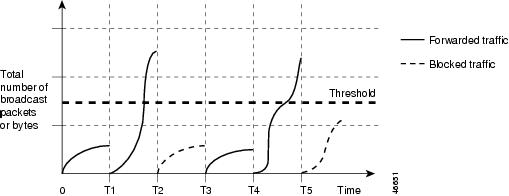
The graph in Figure 68 shows broadcast traffic patterns on an interface over a given period of time. The example can also be applied to multicast and unicast traffic. In this example, the broadcast traffic being forwarded exceeded the configured threshold between time intervals T1 and T2 and between T4 and T5. When the amount of specified traffic exceeds the threshold, all traffic of that kind is dropped for the next time period. Therefore, broadcast traffic is blocked during the intervals following T2 and T5. At the next time interval (for example, T3), if broadcast traffic does not exceed the threshold, it is again forwarded.
Figure 68 Broadcast Storm Control Example
The combination of the storm-control suppression level and the 1-second time interval controls the way the storm control algorithm works. A higher threshold allows more packets to pass through. A threshold value of 100 percent means that no limit is placed on the traffic. A value of 0.0 means that all broadcast, multicast, or unicast traffic on that port is blocked.
Note: Because packets do not arrive at uniform intervals, the 1-second time interval during which traffic activity is measured can affect the behavior of storm control.
You use the storm-control interface configuration commands to set the threshold value for each traffic type.
Default Storm Control Configuration
By default, unicast, broadcast, and multicast storm control are disabled on the switch interfaces; that is, the suppression level is 100 percent.
Storm Control and Threshold Levels
You configure storm control on a port and enter the threshold level that you want to be used for a particular type of traffic.
However, because of hardware limitations and the way in which packets of different sizes are counted, threshold percentages are approximations. Depending on the sizes of the packets making up the incoming traffic, the actual enforced threshold might differ from the configured level by several percentage points.
Note: Storm control is supported on physical interfaces. You can also configure storm control on an EtherChannel. When storm control is configured on an EtherChannel, the storm control settings propagate to the EtherChannel physical interfaces.
Small-Frame Arrival Rate
Incoming VLAN-tagged packets smaller than 67 bytes are considered small frames. They are forwarded by the switch, but they do not cause the switch storm-control counters to increment. In Cisco IOS Release 12.2(44)SE and later, you can configure a port to be error disabled if small frames arrive at a specified rate (threshold).
You globally enable the small-frame arrival feature on the switch and then configure the small-frame threshold for packets on each interface. Packets smaller than the minimum size and arriving at a specified rate (the threshold) are dropped since the port is error disabled.
If the errdisable recovery cause small-frame global configuration command is entered, the port is reenabled after a specified time. (You specify the recovery time by using errdisable recovery global configuration command.)
Protected Ports
Some applications require that no traffic be forwarded at Layer 2 between ports on the same switch so that one neighbor does not see the traffic generated by another neighbor. In such an environment, the use of protected ports ensures that there is no exchange of unicast, broadcast, or multicast traffic between these ports on the switch.
Protected ports have these features:
■![]() A protected port does not forward any traffic (unicast, multicast, or broadcast) to any other port that is also a protected port. Data traffic cannot be forwarded between protected ports at Layer 2; only control traffic, such as PIM packets, is forwarded because these packets are processed by the CPU and forwarded in software. All data traffic passing between protected ports must be forwarded through a Layer 3 device.
A protected port does not forward any traffic (unicast, multicast, or broadcast) to any other port that is also a protected port. Data traffic cannot be forwarded between protected ports at Layer 2; only control traffic, such as PIM packets, is forwarded because these packets are processed by the CPU and forwarded in software. All data traffic passing between protected ports must be forwarded through a Layer 3 device.
■![]() Forwarding behavior between a protected port and a nonprotected port proceeds as usual.
Forwarding behavior between a protected port and a nonprotected port proceeds as usual.
Protected Port Configuration Guidelines
You can configure protected ports on a physical interface (for example, Gigabit Ethernet port 1) or an EtherChannel group (for example, port-channel 5). When you enable protected ports for a port channel, it is enabled for all ports in the port-channel group.
Do not configure a private-VLAN port as a protected port. Do not configure a protected port as a private-VLAN port. A private-VLAN isolated port does not forward traffic to other isolated ports or community ports.
Port Blocking
By default, the switch floods packets with unknown destination MAC addresses out of all ports. If unknown unicast and multicast traffic is forwarded to a protected port, there could be security issues. To prevent unknown unicast or multicast traffic from being forwarded from one port to another, you can block a port (protected or nonprotected) from flooding unknown unicast or multicast packets to other ports.
Note: With multicast traffic, the port blocking feature blocks only pure Layer 2 packets. Multicast packets that contain IPv4 or IPv6 information in the header are not blocked.
Port Security
You can use the port security feature to restrict input to an interface by limiting and identifying MAC addresses of the stations allowed to access the port. When you assign secure MAC addresses to a secure port, the port does not forward packets with source addresses outside the group of defined addresses. If you limit the number of secure MAC addresses to one and assign a single secure MAC address, the workstation attached to that port is assured the full bandwidth of the port.
If a port is configured as a secure port and the maximum number of secure MAC addresses is reached, when the MAC address of a station attempting to access the port is different from any of the identified secure MAC addresses, a security violation occurs. Also, if a station with a secure MAC address configured or learned on one secure port attempts to access another secure port, a violation is flagged.
Secure MAC Addresses
You configure the maximum number of secure addresses allowed on a port by using the switchport port-security maximum value interface configuration command.
Note: If you try to set the maximum value to a number less than the number of secure addresses already configured on an interface, the command is rejected.
The switch supports these types of secure MAC addresses:
■![]() Static secure MAC addresses—These are manually configured by using the switchport port-security mac-address mac-address interface configuration command, stored in the address table, and added to the switch running configuration.
Static secure MAC addresses—These are manually configured by using the switchport port-security mac-address mac-address interface configuration command, stored in the address table, and added to the switch running configuration.
■![]() Dynamic secure MAC addresses—These are dynamically configured, stored only in the address table, and removed when the switch restarts.
Dynamic secure MAC addresses—These are dynamically configured, stored only in the address table, and removed when the switch restarts.
■![]() Sticky secure MAC addresses—These can be dynamically learned or manually configured, stored in the address table, and added to the running configuration. If these addresses are saved in the configuration file, when the switch restarts, the interface does not need to dynamically reconfigure them.
Sticky secure MAC addresses—These can be dynamically learned or manually configured, stored in the address table, and added to the running configuration. If these addresses are saved in the configuration file, when the switch restarts, the interface does not need to dynamically reconfigure them.
You can configure an interface to convert the dynamic MAC addresses to sticky secure MAC addresses and to add them to the running configuration by enabling sticky learning. To enable sticky learning, enter the switchport port-security mac-address sticky interface configuration command. When you enter this command, the interface converts all the dynamic secure MAC addresses, including those that were dynamically learned before sticky learning was enabled, to sticky secure MAC addresses. All sticky secure MAC addresses are added to the running configuration.
The sticky secure MAC addresses do not automatically become part of the configuration file, which is the startup configuration used each time the switch restarts. If you save the sticky secure MAC addresses in the configuration file, when the switch restarts, the interface does not need to relearn these addresses. If you do not save the sticky secure addresses, they are lost.
If sticky learning is disabled, the sticky secure MAC addresses are converted to dynamic secure addresses and are removed from the running configuration.
The maximum number of secure MAC addresses that you can configure on a switch is set by the maximum number of available MAC addresses allowed in the system. This number is determined by the active Switch Database Management (SDM) template. This number is the total of available MAC addresses, including those used for other Layer 2 functions and any other secure MAC addresses configured on interfaces.
Security Violations
It is a security violation when one of these situations occurs:
■![]() The maximum number of secure MAC addresses have been added to the address table, and a station whose MAC address is not in the address table attempts to access the interface.
The maximum number of secure MAC addresses have been added to the address table, and a station whose MAC address is not in the address table attempts to access the interface.
■![]() An address learned or configured on one secure interface is seen on another secure interface in the same VLAN and on the same switch.
An address learned or configured on one secure interface is seen on another secure interface in the same VLAN and on the same switch.
You can configure the interface for one of five violation modes, based on the action to be taken if a violation occurs:
■![]() protect—When the number of secure MAC addresses reaches the maximum limit allowed on the port, packets with unknown source addresses are dropped until you remove a sufficient number of secure MAC addresses to drop below the maximum value or increase the number of maximum allowable addresses. You are not notified that a security violation has occurred.
protect—When the number of secure MAC addresses reaches the maximum limit allowed on the port, packets with unknown source addresses are dropped until you remove a sufficient number of secure MAC addresses to drop below the maximum value or increase the number of maximum allowable addresses. You are not notified that a security violation has occurred.
We do not recommend configuring the protect violation mode on a trunk port. The protect mode disables learning when any VLAN reaches its maximum limit, even if the port has not reached its maximum limit.
■![]() restrict—When the number of secure MAC addresses reaches the maximum limit allowed on the port, packets with unknown source addresses are dropped until you remove a sufficient number of secure MAC addresses to drop below the maximum value or increase the number of maximum allowable addresses. In this mode, you are notified that a security violation has occurred. An SNMP trap is sent, a syslog message is logged, and the violation counter increments.
restrict—When the number of secure MAC addresses reaches the maximum limit allowed on the port, packets with unknown source addresses are dropped until you remove a sufficient number of secure MAC addresses to drop below the maximum value or increase the number of maximum allowable addresses. In this mode, you are notified that a security violation has occurred. An SNMP trap is sent, a syslog message is logged, and the violation counter increments.
■![]() shutdown—A port security violation causes the interface to become error-disabled and to shut down immediately, and the port LED turns off. An SNMP trap is sent, a syslog message is logged, and the violation counter increments. When a secure port is in the error-disabled state, you can bring it out of this state by entering the errdisable recovery cause psecure-violation global configuration command, or you can manually reenable it by entering the shutdown and no shut down interface configuration commands. This is the default mode.
shutdown—A port security violation causes the interface to become error-disabled and to shut down immediately, and the port LED turns off. An SNMP trap is sent, a syslog message is logged, and the violation counter increments. When a secure port is in the error-disabled state, you can bring it out of this state by entering the errdisable recovery cause psecure-violation global configuration command, or you can manually reenable it by entering the shutdown and no shut down interface configuration commands. This is the default mode.
■![]() shutdown vlan—Use to set the security violation mode per-VLAN. In this mode, the VLAN is error disabled instead of the entire port when a violation occurs.
shutdown vlan—Use to set the security violation mode per-VLAN. In this mode, the VLAN is error disabled instead of the entire port when a violation occurs.
■![]() report—This mode is similar to the restrict option, except that when the number of secure MAC addresses reaches the maximum limit allowed on the port, packets with unknown source addresses are not dropped. Packets from an unknown source are allowed, but you are notified that a security violation has occurred. A syslog message is logged with the unknown MAC address, and the violation counter also increments.
report—This mode is similar to the restrict option, except that when the number of secure MAC addresses reaches the maximum limit allowed on the port, packets with unknown source addresses are not dropped. Packets from an unknown source are allowed, but you are notified that a security violation has occurred. A syslog message is logged with the unknown MAC address, and the violation counter also increments.
Note: If you use report mode, do not configure the switchport port-security global command on the ingress interface.
To switch between the report violation mode and another mode, you must explicitly disable all port-security commands of the previous mode using the corresponding no command before adding the new configuration.
|
|
|
|
|
|
|
|
|---|---|---|---|---|---|---|
No3 |
||||||
Default Port Security Configuration
|
|
|
|---|---|
Shutdown. The port shuts down when the maximum number of secure MAC addresses is exceeded. |
|
Port Security Configuration Guidelines
■![]() Port security can only be configured on static access ports or trunk ports. A secure port cannot be a dynamic access port.
Port security can only be configured on static access ports or trunk ports. A secure port cannot be a dynamic access port.
■![]() A secure port cannot be a destination port for Switched Port Analyzer (SPAN).
A secure port cannot be a destination port for Switched Port Analyzer (SPAN).
■![]() A secure port cannot belong to a Fast EtherChannel port group.
A secure port cannot belong to a Fast EtherChannel port group.
Voice VLAN is only supported on access ports and not on trunk ports, even though the configuration is allowed.
■![]() When you enable port security on an interface that is also configured with a voice VLAN, set the maximum allowed secure addresses on the port to two. When the port is connected to a Cisco IP phone, the IP phone requires one MAC address. The Cisco IP phone address is learned on the voice VLAN, but is not learned on the access VLAN. If you connect a single PC to the Cisco IP phone, no additional MAC addresses are required. If you connect more than one PC to the Cisco IP phone, you must configure enough secure addresses to allow one for each PC and one for the phone.
When you enable port security on an interface that is also configured with a voice VLAN, set the maximum allowed secure addresses on the port to two. When the port is connected to a Cisco IP phone, the IP phone requires one MAC address. The Cisco IP phone address is learned on the voice VLAN, but is not learned on the access VLAN. If you connect a single PC to the Cisco IP phone, no additional MAC addresses are required. If you connect more than one PC to the Cisco IP phone, you must configure enough secure addresses to allow one for each PC and one for the phone.
■![]() When a trunk port configured with port security and assigned to an access VLAN for data traffic and to a voice VLAN for voice traffic, entering the switchport voice and switchport priority extend interface configuration commands has no effect.
When a trunk port configured with port security and assigned to an access VLAN for data traffic and to a voice VLAN for voice traffic, entering the switchport voice and switchport priority extend interface configuration commands has no effect.
When a connected device uses the same MAC address to request an IP address for the access VLAN and then an IP address for the voice VLAN, only the access VLAN is assigned an IP address.
■![]() When configuring port security, first specify the total number of MAC addresses you want to allow, by using the switchport port-security maximum interface configuration command and then configure the number of access VLANs ( switchport port-security vlan access interface configuration command) and voice VLANs ( switchport port-security vlan voice interface configuration command) you want to allow. If you do not specify the total number first, the system returns to the default setting (1 MAC address).
When configuring port security, first specify the total number of MAC addresses you want to allow, by using the switchport port-security maximum interface configuration command and then configure the number of access VLANs ( switchport port-security vlan access interface configuration command) and voice VLANs ( switchport port-security vlan voice interface configuration command) you want to allow. If you do not specify the total number first, the system returns to the default setting (1 MAC address).
■![]() When you enter a maximum secure address value for an interface, and the new value is greater than the previous value, the new value overwrites the previously configured value. If the new value is less than the previous value and the number of configured secure addresses on the interface exceeds the new value, the command is rejected.
When you enter a maximum secure address value for an interface, and the new value is greater than the previous value, the new value overwrites the previously configured value. If the new value is less than the previous value and the number of configured secure addresses on the interface exceeds the new value, the command is rejected.
■![]() The switch does not support port security aging of sticky secure MAC addresses.
The switch does not support port security aging of sticky secure MAC addresses.
|
|
|
|---|---|
Dynamic-access port6 |
|
Voice VLAN port7 |
|
Port Security Aging
You can use port security aging to set the aging time for all secure addresses on a port. Two types of aging are supported per port:
■![]() Absolute—The secure addresses on the port are deleted after the specified aging time.
Absolute—The secure addresses on the port are deleted after the specified aging time.
■![]() Inactivity—The secure addresses on the port are deleted only if the secure addresses are inactive for the specified aging time.
Inactivity—The secure addresses on the port are deleted only if the secure addresses are inactive for the specified aging time.
Use this feature to remove and add devices on a secure port without manually deleting the existing secure MAC addresses and to still limit the number of secure addresses on a port. You can enable or disable the aging of secure addresses on a per-port basis.
Port Security and Private VLANs
Ports that have both port security and private VLANs (PVLANs) configured can be labeled secure PVLAN ports. When a secure address is learned on a secure PVLAN port, the same secure address cannot be learned on another secure PVLAN port belonging to the same primary VLAN. However, an address learned on unsecure PVLAN port can be learned on a secure PVLAN port belonging to same primary VLAN.
Secure addresses that are learned on host port get automatically replicated on associated primary VLANs, and similarly, secure addresses learned on promiscuous ports automatically get replicated on all associated secondary VLANs. Static addresses (using the mac-address-table static command) cannot be user configured on a secure port.
Protocol Storm Protection
When a switch is flooded with Address Resolution Protocol (ARP) or control packets, high CPU utilization can cause the CPU to overload. These issues can occur:
■![]() Routing protocol can flap because the protocol control packets are not received, and neighboring adjacencies are dropped.
Routing protocol can flap because the protocol control packets are not received, and neighboring adjacencies are dropped.
■![]() Spanning Tree Protocol (STP) reconverges because the STP bridge protocol data unit (BPDU) cannot be sent or received.
Spanning Tree Protocol (STP) reconverges because the STP bridge protocol data unit (BPDU) cannot be sent or received.
Using protocol storm protection, you can control the rate at which control packets are sent to the switch by specifying the upper threshold for the packet flow rate. The supported protocols are ARP, ARP snooping, Dynamic Host Configuration Protocol (DHCP) v4, DHCP snooping, Internet Group Management Protocol (IGMP), and IGMP snooping.
When the packet rate exceeds the defined threshold, the switch drops all traffic arriving on the specified virtual port for 30 seconds. The packet rate is measured again, and protocol storm protection is again applied if necessary.
For further protection, you can manually error disable the virtual port, blocking all incoming traffic on the virtual port. You can manually enable the virtual port or set a time interval for automatic reenabling of the virtual port.
Note: Excess packets are dropped on no more than two virtual ports.
Virtual port error disabling is not supported for EtherChannel and Flex Link interfaces.
Protocol storm protection is disabled by default. When it is enabled, auto-recovery of the virtual port is disabled by default.
How to Configure Port-Based Traffic Control
Configuring Storm Control
Configuring Storm Control and Threshold Levels
Configuring Small-Frame Arrival Rate
Configuring Protected Ports
|
|
|
|
|---|---|---|
Specifies the interface to be configured, and enter interface configuration mode. |
||
Configuring Port Blocking
Blocking Flooded Traffic on an Interface
Note: The interface can be a physical interface or an EtherChannel group. When you block multicast or unicast traffic for a port channel, it is blocked on all ports in the port-channel group.
Configuring Port Security
Enabling and Configuring Port Security
Enabling and Configuring Port Security Aging
Configuring Protocol Storm Protection
Enabling Protocol Storm Protection
Monitoring and Maintaining Port-Based Traffic Control
Configuration Examples for Port-Based Traffic Control
Enabling Unicast Storm Control: Example
This example shows how to enable unicast storm control on a port with an 87-percent rising suppression level and a 65-percent falling suppression level:
Enabling Broadcast Address Storm Control on a Port: Example
This example shows how to enable broadcast address storm control on a port to a level of 20 percent. When the broadcast traffic exceeds the configured level of 20 percent of the total available bandwidth of the port within the traffic-storm-control interval, the switch drops all broadcast traffic until the end of the traffic-storm-control interval:
Enabling Small-Frame Arrival Rate: Example
This example shows how to enable the small-frame arrival-rate feature, configure the port recovery time, and configure the threshold for error-disabling a port:
Configuring a Protected Port: Example
This example shows how to configure a port as a protected port:
Blocking Flooding on a Port: Example
This example shows how to block unicast and Layer 2 multicast flooding on a port:
Configuring Port Security: Examples
This example shows how to enable port security on a port and to set the maximum number of secure addresses to 50. The violation mode is the default, no static secure MAC addresses are configured, and sticky learning is enabled:
This example shows how to configure a static secure MAC address on VLAN 3 on a port:
This example shows how to enable sticky port security on a port, to manually configure MAC addresses for data VLAN and voice VLAN, and to set the total maximum number of secure addresses to 20 (10 for data VLAN and 10 for voice VLAN).
Configuring Port Security Aging: Examples
This example shows how to set the aging time as 2 hours for the secure addresses on a port:
This example shows how to set the aging time as 2 minutes for the inactivity aging type with aging enabled for the configured secure addresses on the interface:
You can verify the previous commands by entering the show port-security interface interface-id privileged EXEC command.
Configuring Protocol Storm Protection: Example
This example shows how to configure protocol storm protection to drop incoming DHCP traffic on DHCP when it exceeds 35 packets per second:
Additional References
The following sections provide references related to switch administration:
Related Documents
|
|
|
|---|---|
Standards
|
|
|
|---|---|
No new or modified standards are supported by this feature, and support for existing standards has not been modified by this feature. |
MIBs
|
|
|
|---|---|
To locate and download MIBs using Cisco IOS XR software, use the Cisco MIB Locator found at the following URL and choose a platform under the Cisco Access Products menu: http://cisco.com/public/sw-center/netmgmt/cmtk/mibs.shtml |
RFCs
|
|
|
|---|---|
No new or modified RFCs are supported by this feature, and support for existing RFCs has not been modified by this feature. |
 Feedback
Feedback