- Preface
- Software Licensing
- The Cisco IOS command-line interface (CLI)
- Configuring Interfaces
- Switch Alarms
- Initial Switch Configuration (IP address assignments and DHCP autoconfiguration)
- How to Setup and Use the Cisco Configuration Engine
- How to Create and Manage Switch Clusters
- Performing Switch Administration
- Configuring Precision Time Protocol (PTP)
- Configuring PROFINET
- Common Industrial Protocol (CIP)
- Configuring SDM Templates
- Configuring Switch-Based Authentication
- Configuring IEEE 802.1x Port-Based Authentication
- MACsec
- Web-Based Authentication
- Configuring Smartports Macros
- Configuring SGACL Monitor Mode and SGACL Logging
- Configuring SGT Exchange Protocol over TCP (SXP) and Layer 3 Transport
- Configuring VLANs
- VLAN Trunking Protocol (VTP)
- Configuring Voice VLAN
- How to Configure Spanning Tree Protocol (STP)
- Configuring MSTP
- Configuring Optional Spanning-Tree Features
- Configuring Resilient Ethernet Protocol
- Configuring the FlexLinks and the MAC Address-Table Move Update
- Configuring DHCP
- Dynamic Address Resolution Protocol (ARP)
- Configuring IP Source Guard
- How to Configure Internet Group Management Protocol (IGMP) and Multicast VLAN Registration (MVR)
- Configuring Port-Based Traffic Control
- Configuring LLDP, LLDP-MED, and Wired Location Service
- Configuring SPAN and RSPAN
- One-to-one (1:1) Layer 2 Network Address Translation (NAT)
- How to Configure CDP
- Configuring UniDirectional Link Detection (UDLD)
- Configuring RMON
- Configuring System Message Logging
- Configuring Simple Network Management Protocol (SNMP)
- Network Security with ACLs
- Configuring Quality of Service (QoS)
- Configuring Static IP Unicast Routing
- Configuring IPv6 Host Functions
- Configuring Link State Tracking
- Configuring IP multicast routing
- Configuring Multicast Source Discovery Protocol (MSDP)
- Configuring Multicast Listener Discovery (MLD) snooping
- Configuring HSRP and VRRP
- Configuring IPv6 access control lists (ACLs)
- Configuring Embedded Event Manager (EEM)
- IP Unicast Routing
- IPv6 Unicast Routing
- Unicast Routing Overview
- Configuring Cisco IOS IP SLAs Operations
- Configuring Dying-Gasp
- How to Configure Enhanced Object Tracking
- Configuring MODBUS TCP
- Configuring Ethernet CFM
- Working with the Flash File System
- How to Configure EtherChannels
- Troubleshooting
- How to use a Secure Digital (SD) flash memory module (SD card)
Configuring Embedded Event Manager
Embedded Event Manager (EEM) is a distributed and customized approach to event detection and recovery within a Cisco IOS device. EEM offers the ability to monitor events and take informational, corrective, or any other EEM action when the monitored events occur or when a threshold is reached. An EEM policy defines an event and the actions to be taken when that event occurs.
This chapter describes how to configure EEM and how to use it to monitor and manage the Cisco Industrial Ethernet Switches, hereafter referred to as switch.
Note: For complete syntax and usage information for the commands used in this chapter, see the documents listed in the Related Documents.
This chapter includes these sections:
■![]() Information About Embedded Event Manager
Information About Embedded Event Manager
■![]() Configuring Embedded Event Manager
Configuring Embedded Event Manager
Information About Embedded Event Manager
EEM monitors key system events and then acts on them through a set policy. This policy is a programmed script that you can use to customize a script to invoke an action based on a given set of events occurring. The script generates actions such as generating custom syslog or Simple Network Management Protocol (SNMP) traps, invoking CLI commands, forcing a failover, and so forth. The event management capabilities of EEM are useful because not all event management can be managed from the switch and because some problems compromise communication between the switch and the external network management device. Network availability is improved if automatic recovery actions are performed without rebooting the switch.
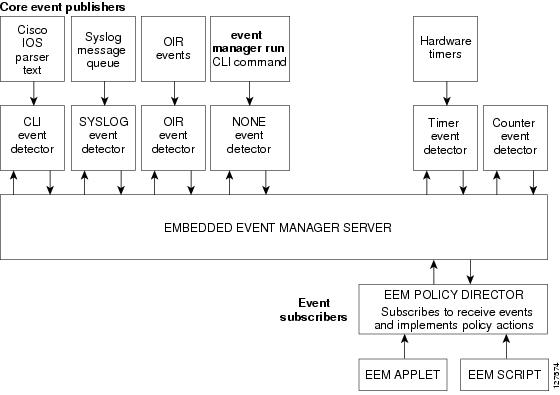
Figure 98 shows the relationship between the EEM server, the core event publishers (event detectors), and the event subscribers (policies). The event publishers screen events and when there is a match on an event specification that is provided by the event subscriber. Event detectors notify the EEM server when an event occurs. The EEM policies then implement recovery based on the current state of the system and the actions specified in the policy for the given event.
Figure 98 Embedded Event Manager Core Event Detectors
See EEM Configuration for Cisco Integrated Services Router Platforms Guide for examples of EEM deployment.
This section includes the following topics:
■![]() Embedded Event Manager Actions
Embedded Event Manager Actions
■![]() Embedded Event Manager Policies
Embedded Event Manager Policies
■![]() Embedded Event Manager Environment Variables
Embedded Event Manager Environment Variables
Event Detectors
EEM software programs known as event detectors determine when an EEM event occurs. Event detectors are separate systems that provide an interface between the agent being monitored, for example SNMP, and the EEM polices where an action can be implemented.
EEM allows these event detectors:
■![]() Application-specific event detector—Allows any EEM policy to publish an event.
Application-specific event detector—Allows any EEM policy to publish an event.
■![]() IOS CLI event detector—Generates policies based on the commands entered through the CLI.
IOS CLI event detector—Generates policies based on the commands entered through the CLI.
■![]() Generic Online Diagnostics (GOLD) event detector—Publishes an event when a GOLD failure event is detected on a specified card and subcard.
Generic Online Diagnostics (GOLD) event detector—Publishes an event when a GOLD failure event is detected on a specified card and subcard.
■![]() Counter event detector—Publishes an event when a named counter crosses a specified threshold.
Counter event detector—Publishes an event when a named counter crosses a specified threshold.
■![]() Interface counter event detector—Publishes an event when a generic Cisco IOS interface counter for a specified interface crosses a defined threshold. A threshold can be specified as an absolute value or an incremental value. For example, if the incremental value is set to 50, an event would be published when the interface counter increases by 50.
Interface counter event detector—Publishes an event when a generic Cisco IOS interface counter for a specified interface crosses a defined threshold. A threshold can be specified as an absolute value or an incremental value. For example, if the incremental value is set to 50, an event would be published when the interface counter increases by 50.
This detector also publishes an event about an interface based on the rate of change for the entry and exit values.
■![]() None event detector—Publishes an event when the event manager run CLI command executes an EEM policy. EEM schedules and runs policies on the basis on an event specification within the policy itself. An EEM policy must be manually identified and registered before the event manager run command executes.
None event detector—Publishes an event when the event manager run CLI command executes an EEM policy. EEM schedules and runs policies on the basis on an event specification within the policy itself. An EEM policy must be manually identified and registered before the event manager run command executes.
■![]() Online insertion and removal event detector—Publishes an event when a hardware insertion or removal (OIR) event occurs.
Online insertion and removal event detector—Publishes an event when a hardware insertion or removal (OIR) event occurs.
■![]() Remote procedure call (RPC) event detector—Invokes EEM policies from outside the switch over an encrypted connecting using Secure Shell (SSH) and uses Simple Object Access Protocol (SOAP) data encoding for exchanging XML-based messages. It also runs EEM policies and then gets the output in a SOAP XML-formatted reply.
Remote procedure call (RPC) event detector—Invokes EEM policies from outside the switch over an encrypted connecting using Secure Shell (SSH) and uses Simple Object Access Protocol (SOAP) data encoding for exchanging XML-based messages. It also runs EEM policies and then gets the output in a SOAP XML-formatted reply.
■![]() SNMP event detector—Allows a standard SNMP MIB object to be monitored and an event to be generated when
SNMP event detector—Allows a standard SNMP MIB object to be monitored and an event to be generated when
–![]() The object matches specified values or crosses specified thresholds.
The object matches specified values or crosses specified thresholds.
–![]() The SNMP delta value, the difference between the monitored Object Identifier (OID) value at the beginning the period and the actual OID value when the event is published, matches a specified value.
The SNMP delta value, the difference between the monitored Object Identifier (OID) value at the beginning the period and the actual OID value when the event is published, matches a specified value.
■![]() SNMP notification event detector—Intercepts SNMP trap and inform messages received by the switch. The event is generated when an incoming message matches a specified value or crosses a defined threshold.
SNMP notification event detector—Intercepts SNMP trap and inform messages received by the switch. The event is generated when an incoming message matches a specified value or crosses a defined threshold.
■![]() Syslog event detector—Allows for screening syslog messages for a regular expression pattern match. The selected messages can be further qualified, requiring that a specific number of occurrences be logged within a specified time. A match on a specified event criteria triggers a configured policy action.
Syslog event detector—Allows for screening syslog messages for a regular expression pattern match. The selected messages can be further qualified, requiring that a specific number of occurrences be logged within a specified time. A match on a specified event criteria triggers a configured policy action.
■![]() Timer event detector—Publishes events for the following different types of timers:
Timer event detector—Publishes events for the following different types of timers:
–![]() An absolute-time-of-day timer publishes an event when a specified absolute date and time occurs.
An absolute-time-of-day timer publishes an event when a specified absolute date and time occurs.
–![]() A countdown timer publishes an event when a timer counts down to zero.
A countdown timer publishes an event when a timer counts down to zero.
–![]() A watchdog timer publishes an event when a timer counts down to zero. The timer automatically resets itself to its initial value and starts to count down again.
A watchdog timer publishes an event when a timer counts down to zero. The timer automatically resets itself to its initial value and starts to count down again.
–![]() A CRON timer publishes an event by using a UNIX standard CRON specification to define when the event is to be published. A CRON timer never publishes events more than once per minute.
A CRON timer publishes an event by using a UNIX standard CRON specification to define when the event is to be published. A CRON timer never publishes events more than once per minute.
■![]() Watchdog event detector (IOSWDSysMon)— Publishes an event when one of these events occurs:
Watchdog event detector (IOSWDSysMon)— Publishes an event when one of these events occurs:
–![]() CPU utilization for a Cisco IOS process crosses a threshold.
CPU utilization for a Cisco IOS process crosses a threshold.
–![]() Memory utilization for a Cisco IOS process crosses a threshold.
Memory utilization for a Cisco IOS process crosses a threshold.
Two events can be monitored at the same time, and the event publishing criteria requires that one or both events cross their specified thresholds.
Embedded Event Manager Actions
These actions occur in response to an event:
■![]() Publishing an application-specific event.
Publishing an application-specific event.
Embedded Event Manager Policies
EEM can monitor events and provide information, or take corrective action when the monitored events occur or a threshold is reached. An EEM policy is an entity that defines an event and the actions to be taken when that event occurs.
There are two types of EEM policies: an applet or a script. An applet is a simple policy that is defined within the CLI configuration. It is a concise method for defining event screening criteria and the actions to be taken when that event occurs. Scripts are defined on the networking device by using an ASCII editor. The script, which can be a bytecode (.tbc) and text (.tcl) script, is then copied to the networking device and registered with EEM. You can also register multiple events in a.tcl file.
Cisco enhancements to TCL in the form of keyword extensions facilitate the development of EEM policies. These keywords identify the detected event, the subsequent action, utility information, counter values, and system information.
For complete information on configuring EEM policies and scripts, see Embedded Event Manager Configuration Guide, Cisco IOS Release 15M&T.
Embedded Event Manager Environment Variables
EEM uses environment variables in EEM policies. These variables are defined in an EEM policy tool command language (TCL) script by running a CLI command and the event manager environment command.
Defined by the user for a user-defined policy.
Defined by Cisco for a specific sample policy.
■![]() Cisco built-in variables (available in EEM applets)
Cisco built-in variables (available in EEM applets)
Defined by Cisco and can be read-only or read-write. The read-only variables are set by the system before an applet starts to execute. The single read-write variable, _exit_status, allows you to set the exit status for policies triggered from synchronous events.
Cisco-defined environment variables and Cisco system-defined environment variables might apply to one specific event detector or to all event detectors. Environment variables that are user-defined or defined by Cisco in a sample policy are set by using the event manager environment global configuration command. You must defined the variables in the EEM policy before you register the policy.
For information about the environmental variables that EEM supports, see Embedded Event Manager Configuration Guide, Cisco IOS Release 15M&T.
EEM 3.2
EEM 3.2 introduces these event detectors:
■![]() Neighbor Discovery—Provides the ability to publish a policy to respond to automatic neighbor detection when:
Neighbor Discovery—Provides the ability to publish a policy to respond to automatic neighbor detection when:
–![]() a Cisco Discovery Protocol (CDP) cache entry is added, deleted, or updated.
a Cisco Discovery Protocol (CDP) cache entry is added, deleted, or updated.
–![]() a Link Layer Discovery Protocol (LLDP) cache entry is added, deleted or updated.
a Link Layer Discovery Protocol (LLDP) cache entry is added, deleted or updated.
–![]() an interface link status changes.
an interface link status changes.
–![]() an interface line status changes.
an interface line status changes.
■![]() Identity—Generates an event when AAA authorization and authentication is successful, when failure occurs, or after normal user traffic on the port is allowed to flow.
Identity—Generates an event when AAA authorization and authentication is successful, when failure occurs, or after normal user traffic on the port is allowed to flow.
■![]() Mac-Address-Table—Generates an event when a MAC address is learned in the MAC address table.
Mac-Address-Table—Generates an event when a MAC address is learned in the MAC address table.
Note: The Mac-Address-Table event detector is supported only on switch platforms and can be used only on Layer 2 interfaces where MAC addresses are learned. Layer 3 interfaces do not learn addresses, and routers do not usually support the MAC address-table infrastructure needed to notify EEM of a learned MAC address.
EEM 3.2 also introduces CLI commands to support the applets to work with the new event detectors.
Prerequisites
■![]() Review the Information About Embedded Event Manager.
Review the Information About Embedded Event Manager.
■![]() If the action snmp-trap command is used, the snmp-server enable traps event-manager command must be enabled to permit SNMP traps to be sent from the Cisco IOS device to the SNMP server. Other relevant snmp-server commands must also be configured; for details see the action snmp-trap command page.
If the action snmp-trap command is used, the snmp-server enable traps event-manager command must be enabled to permit SNMP traps to be sent from the Cisco IOS device to the SNMP server. Other relevant snmp-server commands must also be configured; for details see the action snmp-trap command page.
Guidelines and Limitations
The EEM feature is supported with both Lanbase and IP Services license starting with the 15.2(4)EC release for the IE 4010 and with the15.2(5)E release for IE 4000 and IE 5000. Prior to the 15.2(5)E release, IP Services license was required on the IE 4000 and IE 5000 platforms.
For complete information about configuring embedded event manager, see Embedded Event Manager Configuration Guide, Cisco IOS Release 15M&T.
Default Settings
Configuring Embedded Event Manager
■![]() Registering and Defining an Embedded Event Manager Applet
Registering and Defining an Embedded Event Manager Applet
■![]() Registering and Defining an Embedded Event Manager TCL Script
Registering and Defining an Embedded Event Manager TCL Script
Registering and Defining an Embedded Event Manager Applet
BEFORE YOU BEGIN
Review the Information About Embedded Event Manager.
DETAILED STEPS
Note: Only one event applet command is allowed in an EEM applet. Multiple action applet commands are permitted. If you do not specify the no event and no action commands, the applet is removed when you exit configuration mode.
EXAMPLE
The following example shows how to configure an EEM applet that runs when there is an exact match on the value of a specified SNMP object ID that represents the amount of current process memory.
These examples show actions that are taken in response to an EEM event:
Registering and Defining an Embedded Event Manager TCL Script
BEFORE YOU BEGIN
Review the Information About Embedded Event Manager.
DETAILED STEPS
EXAMPLE
This example shows the sample output for the show event manager environment command:
This example shows a CRON timer environment variable, which is assigned by the software, to be set to every second minute, every hour of every day:
This example shows the sample EEM policy named tm_cli_cmd.tcl registered as a system policy. The system policies are part of the Cisco IOS image. User-defined TCL scripts must first be copied to flash memory.
Verifying Configuration
To display information about EEM, including EEM registered policies and EEM history data, see Cisco IOS Embedded Event Manager Command Reference.
Configuration Example
This example shows the output for EEM when one of the fields specified by an SNMP object ID crosses a defined threshold:
These examples show actions that are taken in response to an EEM event:
This example shows the sample output for the show event manager environment command:
This example shows a CRON timer environment variable, which is assigned by the software, to be set to every second minute, every hour of every day:
This example shows the sample EEM policy named tm_cli_cmd.tcl registered as a system policy. The system policies are part of the Cisco IOS image. User-defined TCL scripts must first be copied to flash memory.
Related Documents
■![]() Cisco IOS Master Command List, All Releases
Cisco IOS Master Command List, All Releases
■![]() Cisco IOS Embedded Event Manager Command Reference
Cisco IOS Embedded Event Manager Command Reference
■![]() Cisco IOS 15.2M&T Command References, Network Management
Cisco IOS 15.2M&T Command References, Network Management
■![]() Embedded Event Manager Configuration Guide, Cisco IOS Release 15M&T
Embedded Event Manager Configuration Guide, Cisco IOS Release 15M&T
 Feedback
Feedback