Data Datagram Transport Layer Security
A data Datagram Transport Layer Security (DTLS) is a security protocol that
-
encrypts CAPWAP data packets sent between an access point and a controller
-
uses separate UDP ports for control (5246) and data (5247) packets,
-
is a standards-track IETF protocol that can encrypt both control and data packets based on TLS, and
-
supports v1.2 as the latest version available.
Feature history for data DTLS
|
Feature name |
Release information |
Feature description |
|---|---|---|
|
Data Datagram Transport Layer Security |
Cisco IOS XE Gibraltar 16.7.1 |
The data Datagram Transport Layer Security (DTLS) is a standards-track IETF protocol that can encrypt both control and data packets based on TLS. |
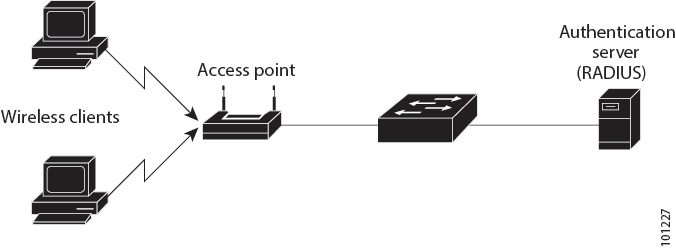
CAPWAP control and data packets
CAPWAP control packets are management packets that are exchanged between a controller and an AP. CAPWAP data packets encapsulate forwarded wireless frames.
If an AP does not support DTLS data encryption, DTLS is enabled only for the control plane, and a DTLS session for the data plane is not established.
DTLS handshake
If an AP supports Data DTLS
-
It enables data DTLS after receiving the new configuration from the controller
-
The AP performs a DTLS handshake on port 5247 and after successfully establishing the DTLS session, and
-
All the data traffic (from the access point to the controller and the controller to the access point) is encrypted.
 Note |
The throughput is affected for some APs that have data encryption enabled. |
The controller does not perform a DTLS handshake immediately after processing client-hello with a cookie, if the following incorrect settings are configured:
-
ECDHE-ECDSA cipher in ap dtls-cipher and RSA-based certificate in “wireless management trustpoint”.
-
RSA cipher in ap dtls-cipher and EC-based certificate in “wireless management trustpoint”.
This is applicable when you move from CC > FIPS > non-FIPS mode.
 Note |
If the DHCP lease time of the AP is less and the DHCP pool is small, the AP join may fail or a failure in establishing the Data Datagram Transport Layer Security (DTLS) session may occur. In such scenarios, associate the AP with a named site-tag and increase the DHCP lease time for at least eight days. |
 Feedback
Feedback