Information About SSL VPN Client
SSL VPN Support on Cisco Unified CME with DTLS
In Communications Manager Express 8.6 and later versions, Cisco Unified SCCP IP phones such as 7945, 7965, and 7975 located outside of the corporate network are able to register to Cisco Unified CME through an SSL VPN connection. The SSL VPN connection is set up between a phone and a VPN headend. The VPN headend can either be an Adaptive Secure Appliance (ASA 5500) or the Datagram Transport Layer Security (DTLS) enabled IOS SSL VPN router, see VPN connection between Cisco Unified IP Phone and VPN head ends (ASA and DTLS). Support for VPN feature on ASA headend was added in Cisco Unified CME 8.5. For more information, see SSL VPN Client for SCCP IP Phones.
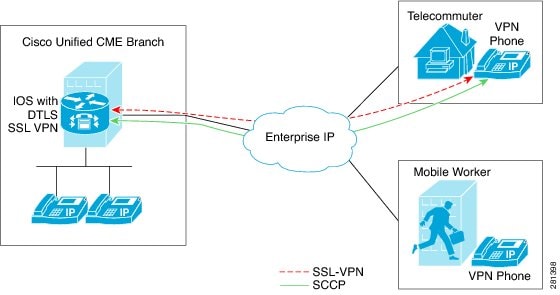
Cisco Unified CME 8.6 uses IOS SSL DTLS as a headend or gateway. To establish a VPN connection between a phone and a VPN head end, the phone must be configured with VPN configuration parameters. The VPN configuration parameters include VPN head end addresses, VPN head end credentials, user or phone ID, and credential policy. These parameters are considered as sensitive information and must be delivered in a secure environment using a signed configuration file or a signed and encrypted configuration file. The phone is required to be provisioned within the corporate network before the phone can be placed outside the corporate network.
After the phone is “staged” in a trusted environment, the phone can be deployed to a location where a VPN head end can be connected. The VPN configuration parameters for the phone dictate the user interface and behavior of the phone.
Phone or Client Authentication
-
Username and Password Authentication.
-
Certificate-based authentication (where the phone's authentication is done using the LSC or MIC certificate on the phone). The certificated-based authentication consists of two levels:
-
Certificate only Authentication - Where only the LSC of the phone is used (the user is not required to enter a username or password on the phone.)
-
Certification with AAA or two-factor - Where the LSC of the phone and username and password combination is used to authenticate phone. Two-factor authentication can be performed with or without the username prefill. (With the username prefilled, the phone does not ask for a username and a username is picked up depending on the configuration under the relevant trustpoint.)
-
 Note |
We recommend using LSC for certificate authentication. Use of MIC for certificate authentication is not recommended. We also recommend configuring ephone in “authenticated” (not encrypted) security mode when doing certificate authentication. More information on certificate-only authentication and two-factor authentication is available at the following location: https://www.cisco.com/en/US/docs/ios/sec_secure_connectivity/configuration/guide/sec_ssl_vpn_ps6350_TSD_Products_Configuration_Guide_Chapter.html#wp1465191. |
You can set up Cisco Unified CME with an encrypted mode, but encrypted SCCP phone has limited media call-flow support. Using a phone with authenticated mode does not have any media-related call-flow limitations.
SSL VPN Client Support on SCCP IP Phones
Cisco Unified CME 8.5 and later versions support Secure Sockets Layer (SSL) Virtual Private Network (VPN) on SCCP IP phones such as 7945, 7965, and 7975.
In Cisco Unified CME 8.5, SCCP IP phones outside of the corporate network can register with the Cisco Unified CME 8.5 through a VPN connection as shown in Connection between a phone and a VPN head end.
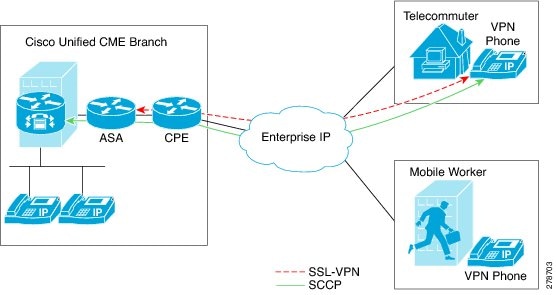
An SSL VPN provides secure communication mechanism for data and other information transmitted between two endpoints. The VPN connection is set up between a SCCP IP phone and a VPN head end or VPN gateway. Cisco Unified CME 8.5 uses an Adaptive Security Appliances (ASA model 55x0) as a VPN head end or gateway.
To establish a VPN connection between a phone and a VPN gateway, the phone is required to be configured with VPN configuration parameters such as VPN gateway addresses, VPN head end credentials, user or phone ID, and credential policy. These parameters contain sensitive information and should be delivered in a secure environment using a signed configuration file or a signed and encrypted configuration file. The phone is required to be provisioned within the corporate network before the phone is placed outside the corporate network.
After the phone is provisioned in a trusted secure environment, the phone can be connected to Cisco Unified CME from any location, from where VPN head end can be reached. The VPN configuration parameters for the phone control the user interface and behavior of the phone. For more information on configuring the SSL VPN feature on SCCP IP phones, see Configure ASA (Gateway) as VPN Headend.
You need to generate a trustpoint with exportable keys and use that as SAST1. For more information about CME System Administrator Security Token.
Restrictions for Configuring SSL VPN Client for SCCP IP Phones
SSL VPN Client is not supported with Cisco 4000 Series Integrated Services Routers on Unified CME.
Only Site-to-Site VPN configuration is supported on Unified CME.
 Feedback
Feedback