Rule conditions specify the traffic that each rule handles. You can configure each rule with multiple conditions, and traffic
must match all conditions to match the rule. The available condition types depend on the rule type.
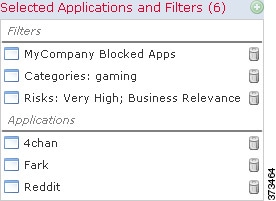
In rule editors, each condition type has its own tab page. Build conditions by choosing the traffic characteristics you want
to match. In general, choose criteria from one or two lists of available items on the left, then add or combine those criteria
into one or two lists of selected items on the right. For example, in URL conditions in access control rules, you can combine
URL category and reputation criteria to create a single group of websites to block.
To help you build conditions, you can match traffic using various system-provided and custom configurations, including realms,
ISE attributes, and various types of objects and object groups. Often, you can manually specify rule criteria.
Leave matching criteria empty whenever possible, especially those for security zones, network objects, and port objects. When
you specify multiple criteria, the system must match against every combination of the contents of the criteria you specify.

Caution
|
Failure to set up your access control rules properly can have unexpected results, including traffic being allowed that should
be blocked. In general, application control rules should be lower in your access control list because it takes longer for
those rules to match than rules based on IP address, for example.
Access control rules that use specific conditions (such as networks and IP addresses) should be ordered before rules that use general conditions (such as applications). If you're familiar with the Open Systems Interconnect (OSI) model,
use similar numbering in concept. Rules with conditions for layers 1, 2, and 3 (physical, data link, and network) should be
ordered first in your access control rules. Conditions for layers 5, 6, and 7 (session, presentation, and application) should
be ordered later in your access control rules. For more information about the OSI model, see this Wikipedia article.
|
Source and Destination Criteria
Where a rule involves source and destination criteria (zones, networks, ports), usually you can use either or both criteria
as constraints. If you use both, matching traffic must originate from one of the specified source zones, networks, or ports
and leave through one of the destination zones, networks, or ports.
Items per Condition
You can add up to 50 items to each condition. For rules with source and destination criteria, you can use up to 50 of each.
Traffic that matches any of the selected items matches the condition.
Simple Rule Mechanics
In rule editors, you have the following general choices. For detailed instructions on building conditions, see the topics
for each condition type.
-
Choose Item—Click an item or check its check box. Often you can use Ctrl or Shift to choose multiple items, or right-click
to Select All.
-
Search—Enter criteria in the search field. The list updates as you type. The system searches item names and, for objects and
object groups, their values. Click Reload ( ) or Clear (
) or Clear ( ) to clear the search.
) to clear the search.
-
Add Predefined Item—After you choose one or more available items, click an Add button or drag and drop. The system prevents you from adding invalid items: duplicates, invalid combinations, and so on.
-
Add Manual Item—Click the field under the Selected items list, enter a valid value, and click Add. When you add ports, you may also choose a protocol from the drop-down list.
-
Create Object—Click Add ( ) to create a new, reusable object that you can immediately use in the
condition you are building, then manage in the object manager. When using
this method to add application filters on the fly, you cannot save a filter
that includes another user-created filter.
) to create a new, reusable object that you can immediately use in the
condition you are building, then manage in the object manager. When using
this method to add application filters on the fly, you cannot save a filter
that includes another user-created filter.
-
Delete—Click the Delete ( ) for an item, or choose one or more items and right-click to Delete Selected.
) for an item, or choose one or more items and right-click to Delete Selected.


 )
) )
) )
) )
)

 )
) )
) )
)
 )
) )
) Feedback
Feedback