This section details how to troubleshoot specific errors that may occur when migrating Firewall Threat
Defense devices to Cloud-Delivered Firewall Management Center.
Migration of Firewall Threat
Defense cluster fails
The migration of a Firewall Threat
Defense cluster to the Cloud-Delivered Firewall Management Center fails during the migration process. When the failure occurs, Cloud-Delivered Firewall Management Center automatically performs a rollback, returning device management to the original On-Premises Firewall Management
Center to maintain configuration integrity and service continuity.
Cause:
The migration failure may occur due to temporary service latency, transient connectivity issues, or other temporary conditions
that interrupt the migration process.
Workaround:
-
Retry migration: Wait for some time and then initiate the migration again from the Secure Firewall
Management Center.
-
Contact support: If the migration continues to fail after multiple attempts, contact Cisco Technical Support and provide the relevant error
messages and migration details to assist with troubleshooting.
Configuration export from On-Premises Firewall Management Center failed
Cause:
-
Disk space is full or nearly full, preventing the export process from being completed.
-
Concurrent operations such as device upgrade, upgrade revert, moving a device between domains, device import and export, device
template import and export, or policy analysis are running in on-premises Firewall Management
Center.
-
Connectivity issues exist between the on-premises Firewall Management
Center and Security Cloud Control.
Workaround:
-
Perform these actions according to your requirements:
-
Ensure that at least 10% of disk space is available to accommodate the creation of necessary export files.
-
Ensure that no parallel operations are running during the migration.
-
Ensure that the network connection between on-premises Firewall Management
Center and Security Cloud Control is stable and reliable.
-
Retry the migration.
-
If the issue persists, contact Cisco TAC.
Failed to initiate import in Security Cloud Control
Cause:
Import can fail if:
-
Disk space is full or nearly full, preventing the import process from being completed.
-
Concurrent operations such as device upgrade, upgrade revert, moving a device between domains, device import and export, device
template import and export, or policy analysis are running in Cloud-Delivered Firewall Management Center.
Workaround:
-
Ensure that no other operations are running during import and retry migration.
-
If the issue persists, contact Cisco TAC.
Failed to retrieve the most recent device information from On-Premises Firewall Management Center
Cause:
Workaround:
-
Perform these actions according to your requirements:
-
Ensure that the network connection between Security Cloud Control and on-premises Firewall Management
Center is stable.
-
Ensure that DNS settings for resolving Firewall Management Center hostnames are correct.
-
Ensure network access for Firewall Threat
Defense devices through TCP ports 8305 and 443.
-
Ensure outbound connectivity to port 443 to Security Cloud Control and Cloud-Delivered Firewall Management Center hosts.
-
Ensure that the devices are synchronized without any pending changes.
-
Retry migration.
-
If the issue persists, contact Cisco TAC.
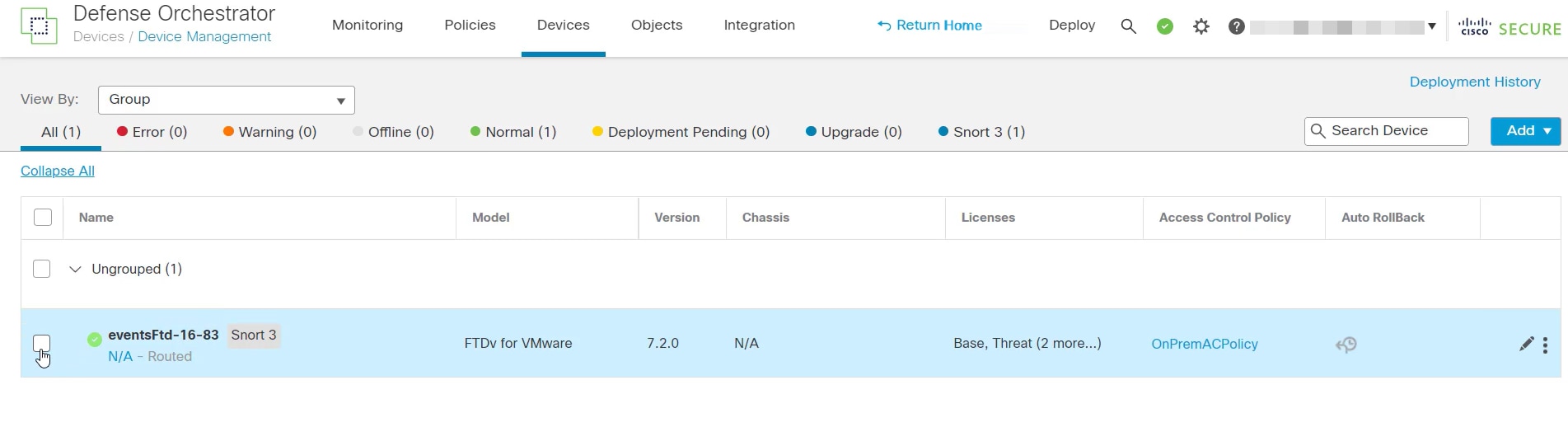
Failed to select Security Cloud Control as the manager for events and analytics
Cause:
Selected on-premises Firewall Management
Center for analytics during Firewall Threat
Defense migration and committed it or the Security Cloud Control automatically committed it after the 14-day evaluation period.
Workaround:
-
Log in to the on-premises Firewall Management
Center and remove the Firewall Threat
Defense device from the on-premises Firewall Management
Center.
-
Enable the Firewall Threat
Defense device to send events to Security Analytics and Logging (SaaS) directly. For more information, see Send Cloud-delivered Firewall Management Center-Managed Event Logs to SAL (SaaS) Using a Direct Connection.
-
Verify if the SSE Connector is running in the Firewall Threat
Defense device. To verify, access Firewall Threat
DefenseCLI and do the following:
# more /ngfw/etc/sf/connector.properties
registration_interval=180
connector_port=8989
connector_fqdn=api-sse.cisco.com
-
Verify the connectivity between Firewall Threat
Defense and the SSE portal. The following URLs need to be allowed as IPs can change:
-
api.apj.sse.itd.cisco.com (primary SSE cloud API endpoint)
-
est.sco.cisco.com (common endpoint across geographies)
-
mx.apj.sse.itd.cisco.com
-
dex.apj.sse.itd.cisco.com (for customer success services)
-
eventing-ingest.apj.sse.itd.cisco.com (for Cisco XDR and Security Cloud Control services)
-
registration.apj.sse.itd.cisco.com (enables Firewall Threat
Defense device registration to the regional Cisco cloud)
-
access Firewall Threat
Defense CLI and perform a CURL request to validate tenant details using the following command:
root@firepower:/home/admin# curl localhost:8989/v1/contexts/default/tenant
-
Verify that the event logs are appearing in Security Cloud Control.
Failed to import configuration from On-Premises Firewall Management Center
Cause:
The On-Premises Firewall Management Center configuration may include policies or object configurations that are unsupported or are conflicting, leading to migration
failure.
Workaround:
-
Check the On-Premises Firewall Management Center configuration for unsupported policies or object configurations to ensure compatibility.
-
Retry migration.
-
If the issue persists, contact Cisco TAC.
Failed to complete device discovery
Cause:
Conflicts or unhandled scenarios exist in the device configuration or within Security Cloud Control's internal operations, such as incompatible settings or unsupported conditions that Security Cloud Control does not support.
Workaround:
-
Perform these actions according to your requirements:
-
Inspect the device configuration in On-Premises Firewall Management Center for incompatible settings or unsupported scenarios that Security Cloud Control does not support and make necessary updates.
-
Check system logs for errors and confirm that both the On-Premises Firewall Management Center and the device are functioning properly.
-
Retry migration.
-
If the issue persists, contact Cisco TAC.
Failed to connect the device to Security Cloud Control
Cause:
Possible causes include the device being powered off, network connectivity issues, or a firewall blocking the necessary ports.
Workaround:
-
Perform these actions according to your requirements:
-
Confirm that the device is powered on, and network connection is stable. Look for Firewall issues, blocked ports, and incorrect
cabling.
-
Ensure that your device has the correct DNS server configuration for resolving Security Cloud Control hostnames.
-
Retry migration.
-
If the issue persists, contact Cisco TAC.
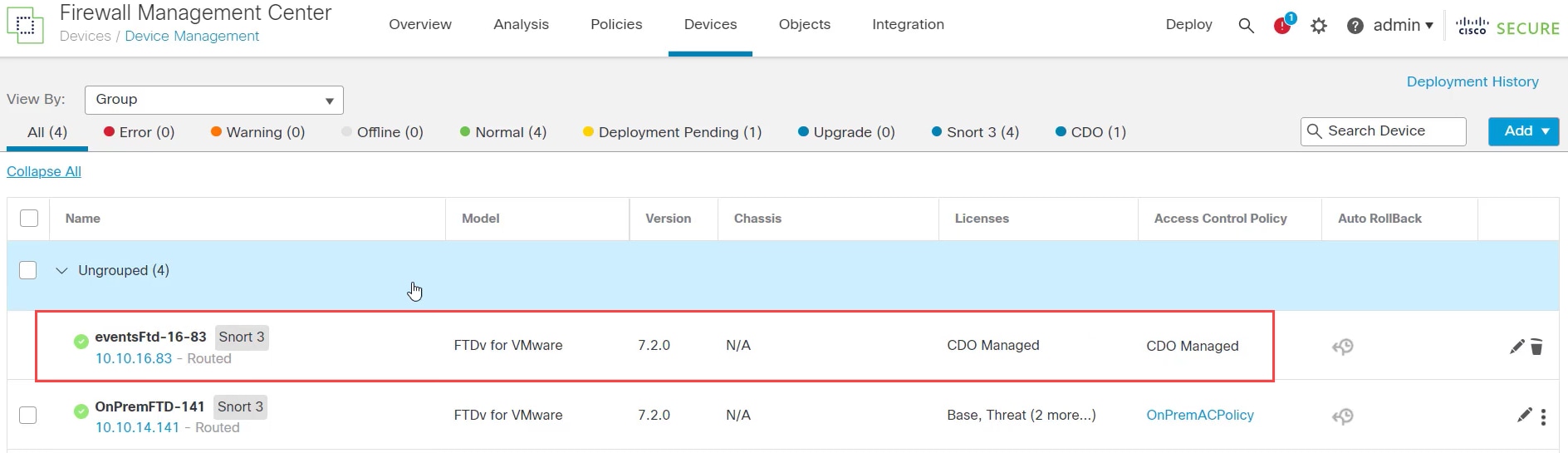
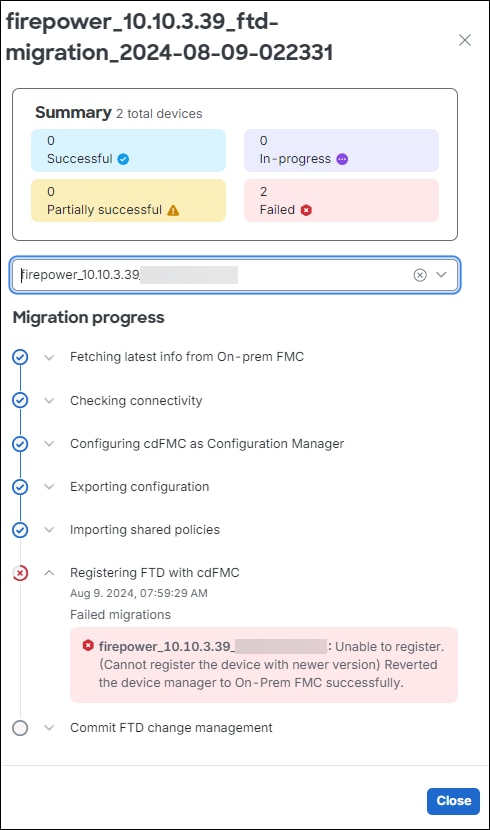
Failed to register the device, causing the manager to revert to On-Premises Firewall Management Center
Cause:
The device failed to register with Cloud-Delivered Firewall Management Center during migration, causing the system to revert the device manager to On-Premises Firewall Management Center. This may be because of connectivity issues.
Workaround:
-
Perform these actions according to your requirements:
-
Verify DNS settings for resolving Security Cloud Control hostnames.
-
Ensure that network access is enabled for TCP port 8305, allowing the Firewall Threat
Defense devices to connect to the Cloud-Delivered Firewall Management Center.
-
Allow outbound HTTPS connections on Firewall Threat
Defense devices to reach the Cloud-Delivered Firewall Management Center and upload configurations to Security Cloud Control.
-
Retry migration.
-
If the issue persists, contact Cisco TAC.
Failed to unregister the device due to an ongoing deployment
Cause:
Migration failed because a deployment is in progress on the device.
Workaround:
-
Perform these actions according to your requirements:
-
Retry migration.
-
If the issue persists, contact Cisco TAC for support.
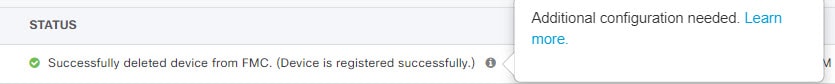
Report generation failed after successful FTD migration to Cloud-Delivered Firewall Management Center
Cause:
The report generation failure may be because of temporary system glitches.
Workaround:
-
Generate the report after some time to overcome the temporary system issues that might have caused the initial failure.
-
If the issue persists, contact Cisco TAC.
Failed to initiate FTD migration to Cloud-Delivered Firewall Management Center
Cause:
-
Ongoing migration in the source manager.
-
Unsupported device version.
-
Incorrect DNS and network configuration.
Workaround:
-
Perform these actions according to your requirements:
-
Confirm that no other migration jobs are active in the same source manager.
-
Verify that the devices are on supported versions, have no pending changes to be deployed, and are active.
-
Ensure that the DNS settings are correct, and network access is available to communicate with Cloud-Delivered Firewall Management Center.
-
If the issue persists, contact Cisco TAC.
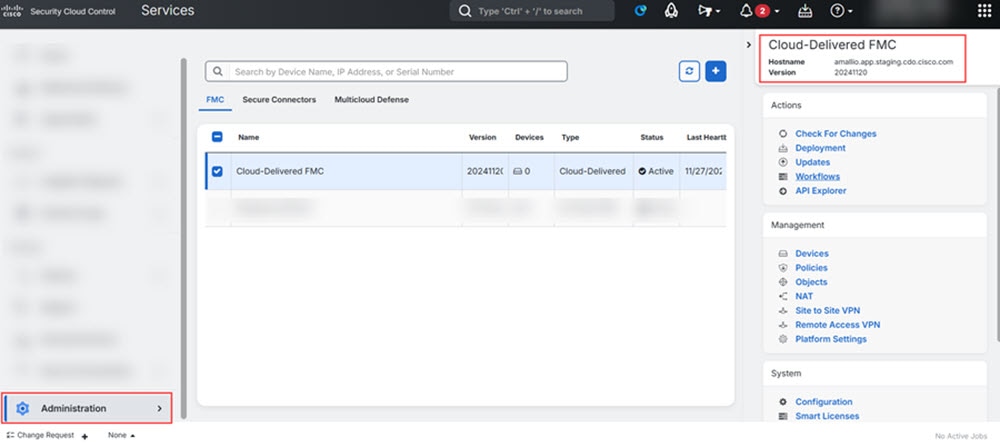
Failed to deploy changes from Security Cloud Control
Cause:
Device migration to Cloud-Delivered Firewall Management Center failed during deployment.
Workaround:
-
Perform these actions according to your requirements:
-
Attempt the deployment again from the Deployment page on Cloud-Delivered Firewall Management Center.
-
Check for out-of-band changes, which are changes made directly in the device, and not through Security Cloud Control. If out-of-band changes exist, they may interfere with the deployment. Use Security Cloud Control's Check for changes functionality to identify and address out-of-band changes.
-
Ensure that all the configurations are supported and do not conflict with the current device settings.
-
Verify that the device is onboarded and reachable by both the Security Cloud Control and management center, with the necessary internet access and communication capabilities.
-
If the issue persists, contact Cisco TAC.
Failed to commit FTD migration to Cloud-Delivered Firewall Management Center
Cause:
-
The 14-day evaluation period has expired.
-
Firewall Threat
Defense devices have been reverted to or deleted from the On-Premises Firewall Management Center, preventing further actions.
Workaround:
-
Try committing again to address any transient network or device issues.
-
If the issue persists, contact Cisco TAC.
Failed to retain device on On-Premises Firewall Management Center for Analytics
Cause:
If your source manager is an On-Premises Firewall Management Center 1000/2500/4500, it cannot support retaining for Analytics because of the limited resources.
Workaround:
-
Ensure that the Retain on On-Prem FMC for Analytics option is selected during the migration process.
-
If the issue persists, contact Cisco TAC.
Failed to revert the device manager to On-Premises Firewall Management Center
Cause:
-
The device cannot be reverted if the 14-day evaluation period has expired.
-
Firewall Threat
Defense devices have been reverted to or deleted from the On-Premises Firewall Management Center, preventing further actions.
Workaround:
-
Perform these actions according to your requirements:
-
Try committing the changes again to address the temporary server or network issues.
-
If changes have occurred in the high availability configuration after migration, reset the devices to their original migration
state before attempting to commit.
-
If the issue persists, contact Cisco TAC.
Failed to configure Security Cloud Control as the configuration manager
Cause:
The device already has a configuration manager.
Workaround:
-
If another configuration manager is present, remove it manually and retry the migration.
-
If the issue persists, contact Cisco TAC.
Failed to commit migration; the device is ineligible
Cause:
-
The device has pending changes that have to be deployed.
-
The device to be migrated is part of FTD high availability (HA), but the current state is invalid, for example, it is in
Active/Active state.
-
The device to be migrated is connected in Analytics-only mode.
-
Cluster migration is supported only for FTDs version 7.4 and above.
-
Migration for chassis and MI FTDs on models 3100/4200 is currently not supported.
Workaround:
-
Perform these actions according to your requirements:
-
Verify that the device is up to date with On-Premises Firewall Management Center, then retry migration.
-
Ensure all pending changes on the devices are deployed.
-
Confirm that the Firewall Threat
Defense device is in a valid state, such as Active/Standby. If the status isn't correctly reflected in On-Premises Firewall Management Center, use the Force refresh node status option on the device listing page to update the correct status on management center.
-
If the issue persists, contact Cisco TAC.
Failed to import site-to-site VPN policies from On-Premises Firewall Management Center
Cause:
The failure may be due to various factors, such as VPN policy configuration or network connectivity issues.
Workaround:
-
Perform these actions according to your requirements:
-
Verify your site-to-site VPN policies in On-Premises Firewall Management Center to ensure there are no configuration errors. If object overrides are used within network objects, manually add these overrides
to Security Cloud Control after migration.
-
Ensure that both the On-Premises Firewall Management Center and the targeted device have stable and reliable network connections to Security Cloud Control.
-
If the authentication type is set as Pre-shared Automatic Key in On-Premises Firewall Management Center, Security Cloud Control generates a new pre-shared key for the VPN post-migration deployment without disrupting existing tunnels.
-
Retry migration.
-
If the issue persists, contact Cisco TAC.
Failed to migrate as all devices within the topology need to be migrated simultaneously
Cause:
Migrating multiple devices, particularly those within the same network topology, requires synchronizing their migrations to
avoid inconsistencies and potential errors. All devices should be migrated within the same timeframe.
Workaround:
-
Perform these actions according to your requirements:
-
Devices registered for Analytics -only with the On-Premises Firewall Management Center or those with pending changes are not eligible for migration.
-
When selecting a device associated with a site-to-site VPN topology, Security Cloud Control automatically selects peer devices from the same or different topology, as all devices in the topology must be migrated together
for success. Extranet devices, if any, are not listed by the wizard.
-
The S2S VPN Topology column shows the number of site-to-site VPN topologies a device is part of. Click the topology link to view the topologies
and devices migrating with the selected device. This field does not apply to devices outside the site-to-site VPN topology.
-
A high-availability pair is shown as a single node. Select this node to include both active and standby devices in the migration.
-
If the issue persists, contact Cisco TAC.
HTTP status code 201 (created) found in On-Premises Firewall Management Center response
Cause:
The Secure Device Connector (SDC) version is not compatible.
Workaround:
-
Ensure that the SDC is upgraded to version 202205191350 or later.


 ).
).
 ).
).
 and choose
and choose 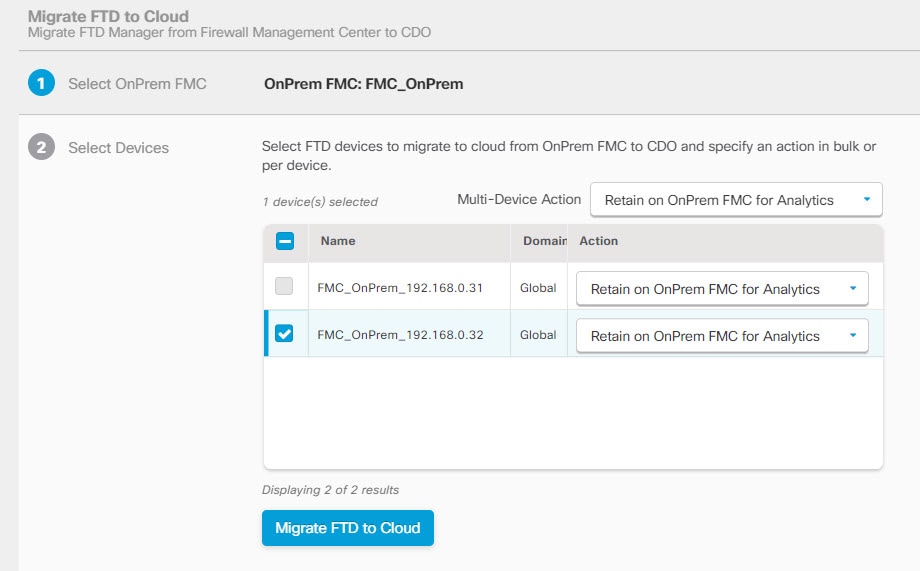
 to see the alerts that have been triggered during the migration process. Additionally, if you have opted to receive email
notifications from
to see the alerts that have been triggered during the migration process. Additionally, if you have opted to receive email
notifications from  to execute the following actions:
to execute the following actions:
 under the
under the 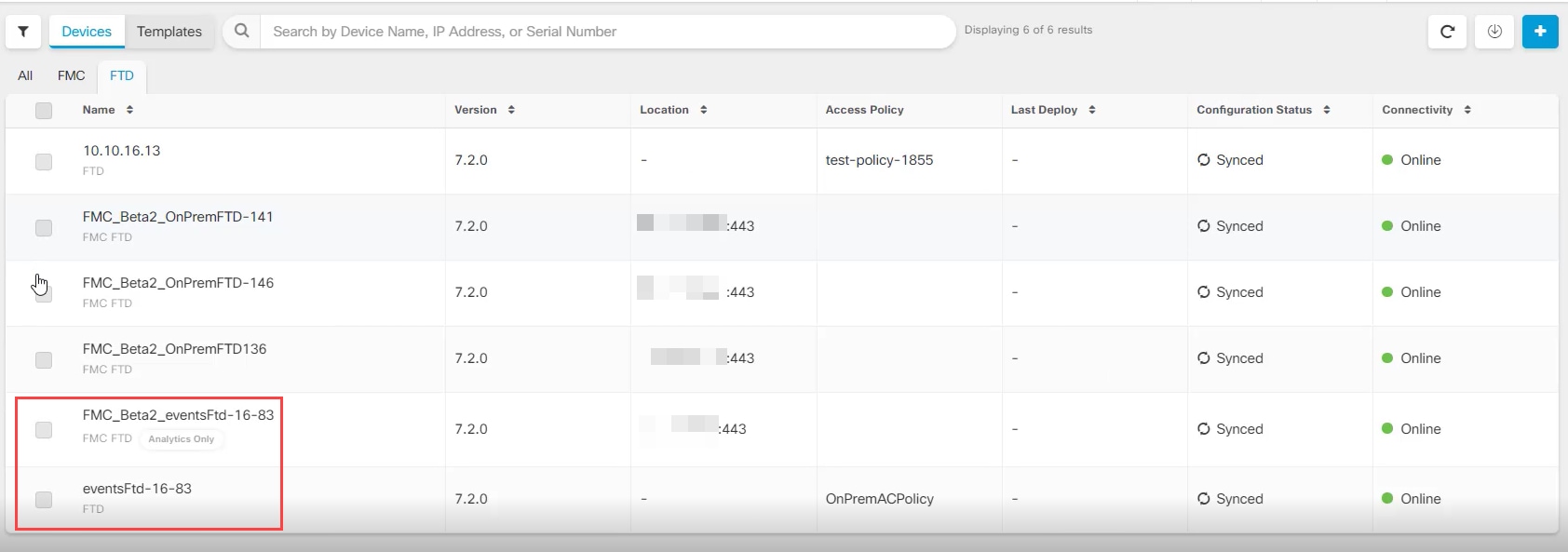
 Feedback
Feedback