About the Event Log
Open the Event Log screen to search for events that happen across your network. This screen provides an interface where you can search and sort through the events generated across the network. Up to 500,000 of these events are stored for a maximum of 90 days. You can use the filter controls provided to limit the events displayed based on any combination of the following parameters:
Add a Time to specify the start and end times for the period of interest. Only events occurring in this period will be displayed.

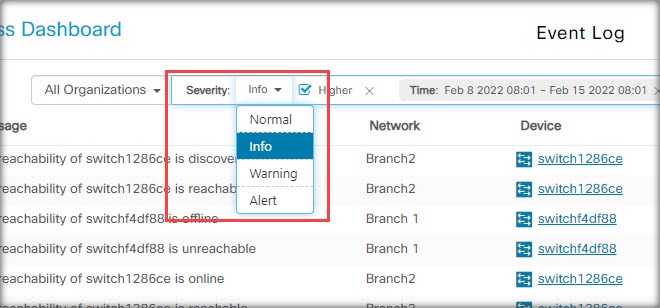
Add a Severity filter to select the level of events to display. You can also check the Higher checkbox to include events with a higher severity level.
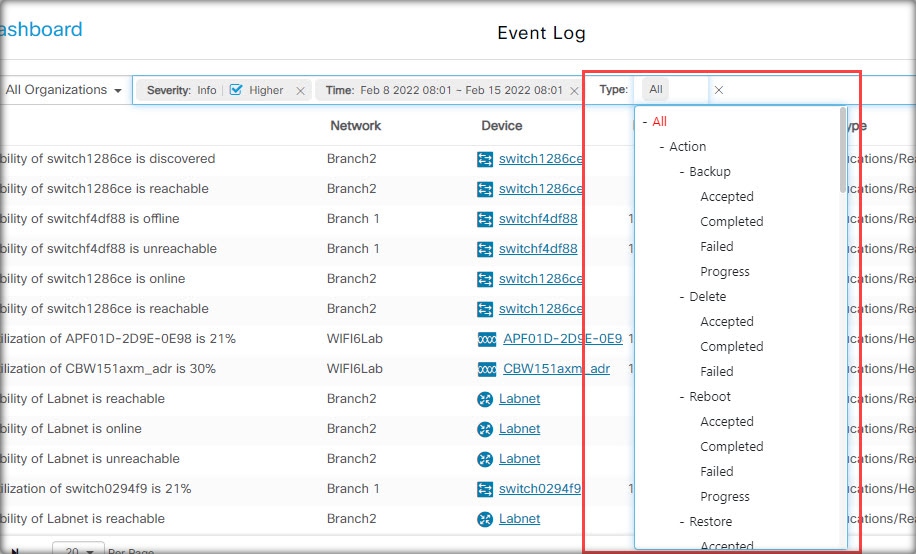
Add the Type filter to select one or more event types to display. The types are arranged in a tree structure, and selecting a type will automatically include all event types underneath the selected type in the tree.
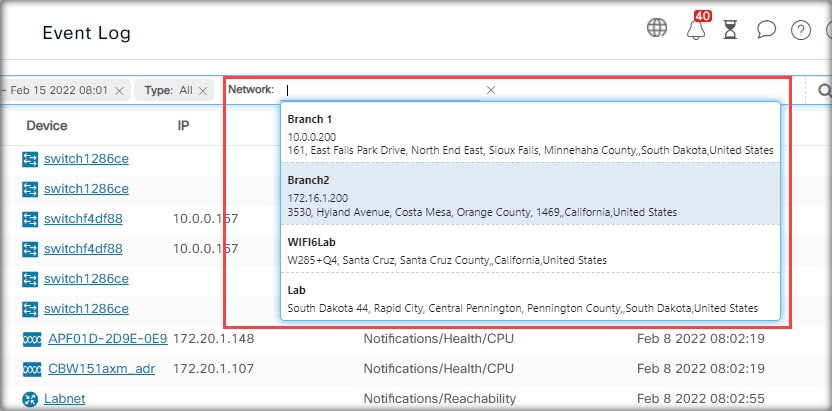
Use the Networkfilter to display events by one or more networks. As you type, matching sites will be displayed.
Use the Devicefilter to display events by one or more devices. As you type, matching devices will be displayed. You can also specify devices by name, IP address, or MAC address.

Events that match the filter conditions will be displayed in a table like the example shown below. You can also sort the information in the table using the column headings.


 Feedback
Feedback