Create and manage portal
A portal is a user interface that appears when a Wi-Fi user connects to an SSID. You can create the captive portals using Cisco Spaces and enhance them with portal modules provided by Cisco Spaces.
Cisco Spaces also allows you to create your own portals (Enterprise Captive Portals) for onboarding end users who connect to Wi-Fi. For more information on Enterprise Captive Portals, refer to Enterprise Captive Portals.
Prerequisites for creating a portal
-
To specify the locations for which the portal is applicable, you must define the location hierarchy. For more information on defining the location hierarchy, refer to the Defining the Location Hierarchy section.
-
To configure social authentication for the portal, configure your social app and then add it to Cisco Spaces. For more information on configuring for social authentication, refer to the Social authentication for portals section.
-
To configure SMS-based authentication for the portal, configure the SMS gateway. For more information on configuring the SMS gateway, refer to the Configure an SMS gateway in Cisco Spaces section.
Bandwidth requirements
For captive portals, we recommend a minimum bandwidth of 30Mbps for good end user experience.
This table shows the response time for loading the captive portal based on the bandwidth.
|
Bandwidth |
Number of users |
Response (in seconds) |
|---|---|---|
|
1 Mbps |
1 |
5.86 |
|
2 |
5.49 |
|
|
3 |
5.40 |
|
|
4 |
5.63 |
|
|
5 |
5.92 |
|
|
2 Mbps |
1 |
5.09 |
|
2 |
5.10 |
|
|
3 |
5.04 |
|
|
4 |
5.25 |
|
|
5 |
5.16 |
|
|
6 |
5.23 |
|
|
7 |
5.26 |
|
|
8 |
5.30 |
|
|
9 |
5.34 |
|
|
10 |
5.40 |
|
|
11 |
5.49 |
|
|
5Mbps |
5 |
4.92 |
|
10 |
4.98 |
|
|
11 |
5.05 |
|
|
12 |
5.08 |
|
|
13 |
5.11 |
|
|
14 |
5.13 |
|
|
15 |
5.17 |
|
|
16 |
5.18 |
|
|
20 |
5.25 |
|
|
7Mbps |
25 |
5.13 |
|
30 |
5.20 |
|
|
31 |
5.23 |
|
|
32 |
5.26 |
|
|
33 |
5.29 |
|
|
34 |
5.33 |
|
|
9Mbps |
30 |
4.93 |
|
35 |
4.98 |
|
|
40 |
5.05 |
|
|
41 |
5.07 |
|
|
42 |
5.10 |
|
|
43 |
5.13 |
|
|
44 |
5.15 |
|
|
45 |
5.17 |
|
|
46 |
5.19 |
|
|
47 |
5.15 |
|
|
11 Mbps |
35 |
4.68 |
|
40 |
4.91 |
|
|
50 |
5.05 |
|
|
55 |
5.16 |
|
|
56 |
5.18 |
|
|
57 |
5.20 |
|
|
58 |
5.24 |
|
|
59 |
5.28 |
|
|
60 |
5.25 |
|
|
61 |
5.30 |
Sample portals
Cisco Spaces provides sample portals for various authentication types.
-
Email authentication with data capture
-
Inline SMS with password verification & data capture
-
Inline social authentication
-
SMS with password verification & data capture
-
SMS with link verification
-
Email authentication
-
User agreements
These templates are intended as a reference for creating captive portals.
To view and make a copy of the sample portal, perform these steps:
Procedure
|
Step 1 |
In the Cisco Spaces dashboard, choose Home. |
|
Step 2 |
In the window that appears, choose Captive Portal. |
|
Step 3 |
In the Captive Portal window, choose Portal in the left pane. The sample portal for various authentication types are displayed at the bottom of the portal list. |
|
Step 4 |
Click the Make a Copy icon at the far right of the sample portal that you want. |
|
Step 5 |
In the portal wizard screen that appears, specify a name for the captive portal. |
|
Step 6 |
If necessary, customize the portal configuration. Save the portal. |
|
Step 7 |
Save the portal. |
Create a portal
 Note |
Portals created in the new version of the dashboard are not visible in the older version. |
When defining a portal, you can also configure the locations for which the portal must be available.
To create a portal, perform these steps:
Procedure
|
Step 1 |
In the Cisco Spaces dashboard, choose Home. In the window that appears, choose Captive Portal. In the Captive Portal window that appears, choose Portal in the left pane. Click Create New. The Portal window appears. 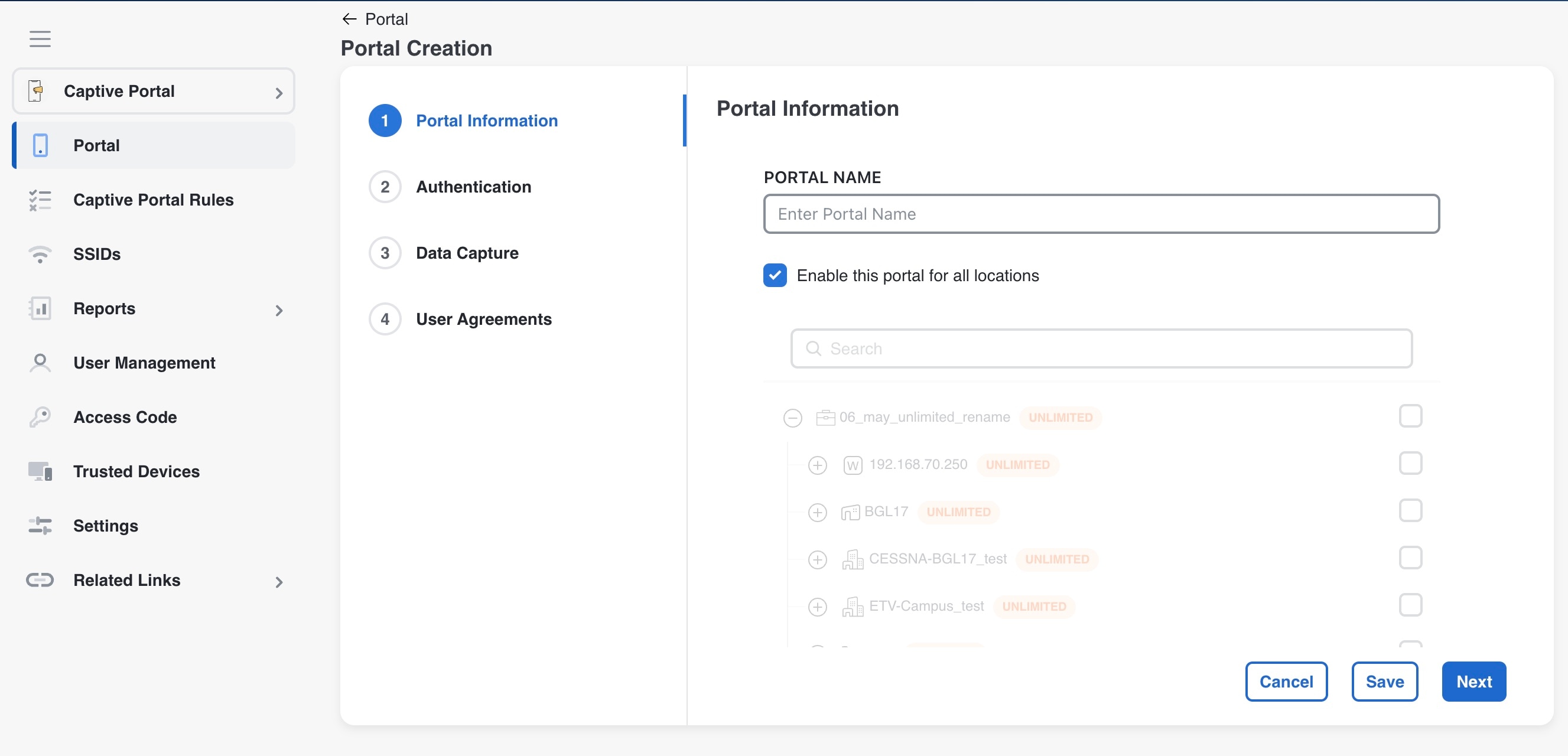
|
||||||
|
Step 2 |
In the Portal Name field, enter a name for portal. If you want this portal to be available only for certain locations, uncheck the Enable this portal forall locations check box. Click Next. The Authentication window appears.
|
||||||
|
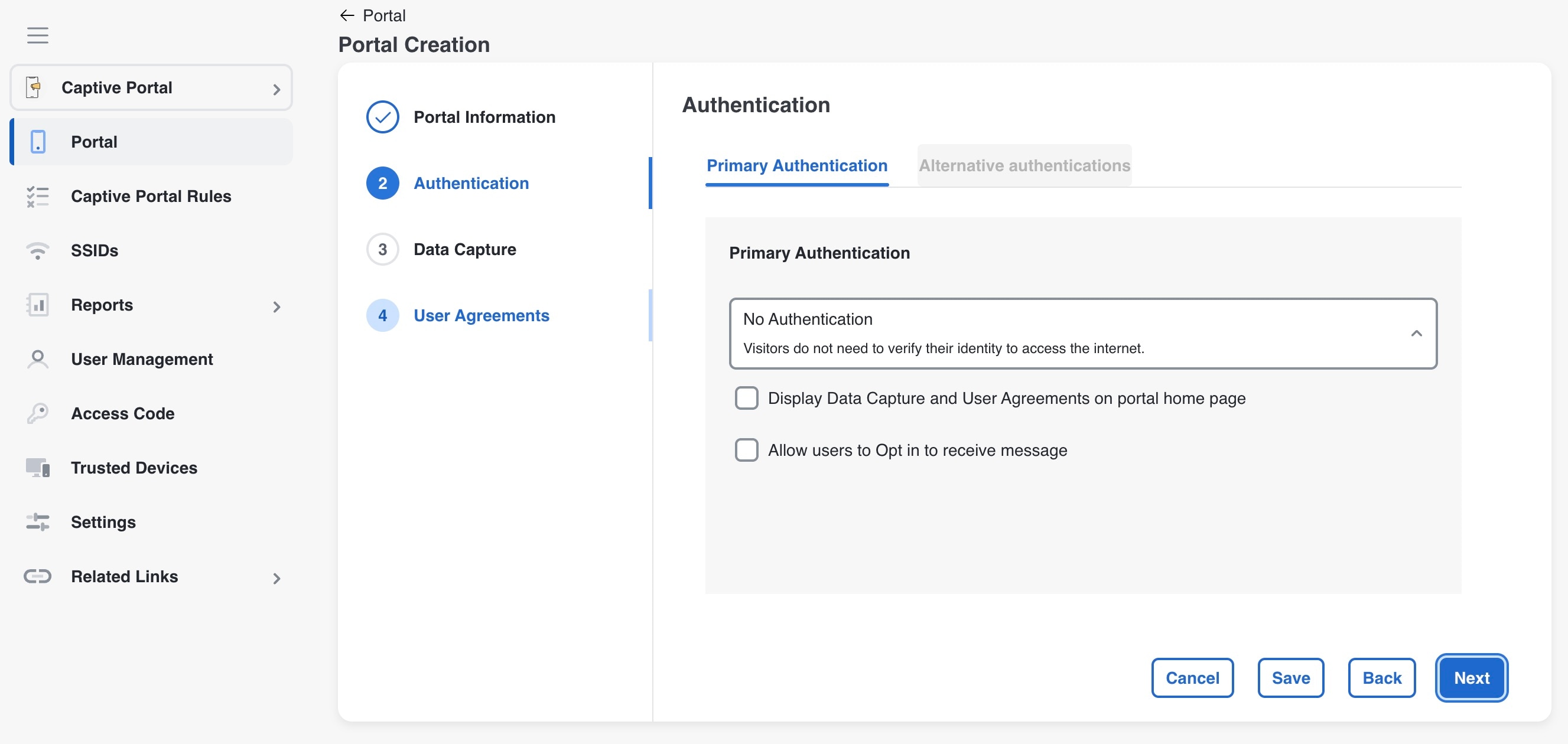
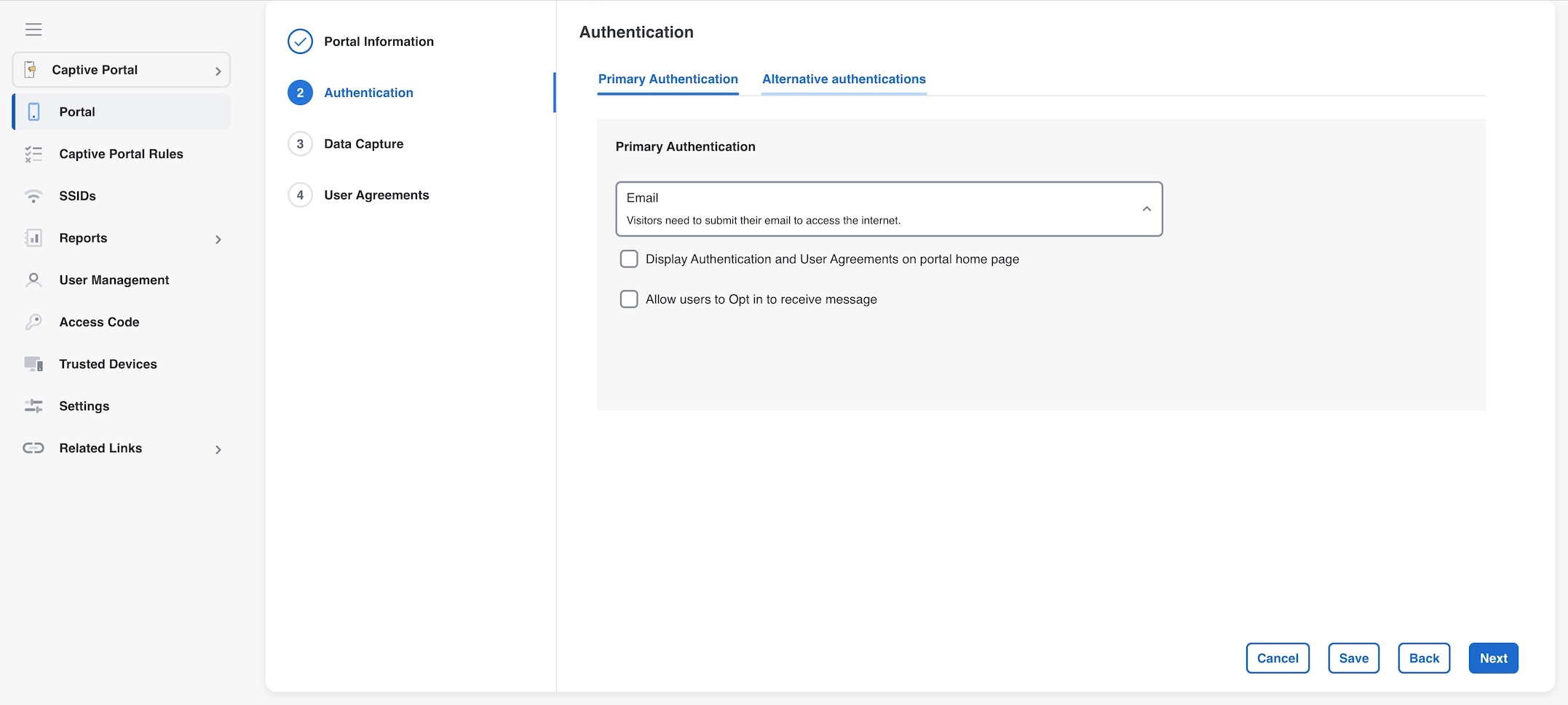
Step 3 |
In the Authentication window, select the authentication type that you want apply for the portal. There is a Primary Authentication tab which allows users to select only one authentication method during a session. The Alternate Authentication option allows the user to add multiple authentication methods. Based on the authentication type selected additional fields appear. For more information on various authentication types, see the Configure authentication for a portal.
|
||||||
|
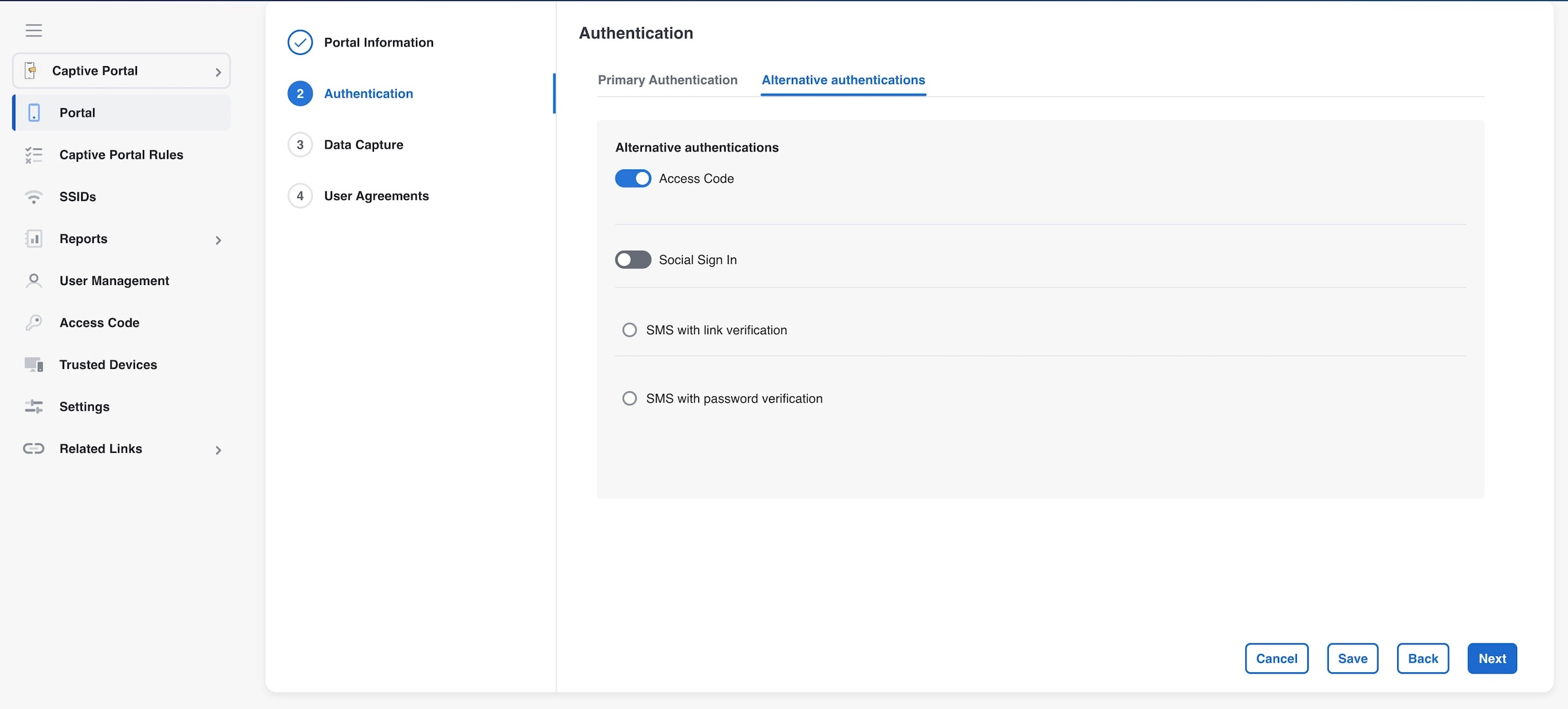
Step 4 |
In the Alternate Authentication window, users can select other authentications such as Access Code and Social Sign in. In addition to these two, SMS with link verification and SMS with password verification are also available. Only one of these SMS options can be selected at a time using the radio button support.
|
||||||
|
Step 5 |
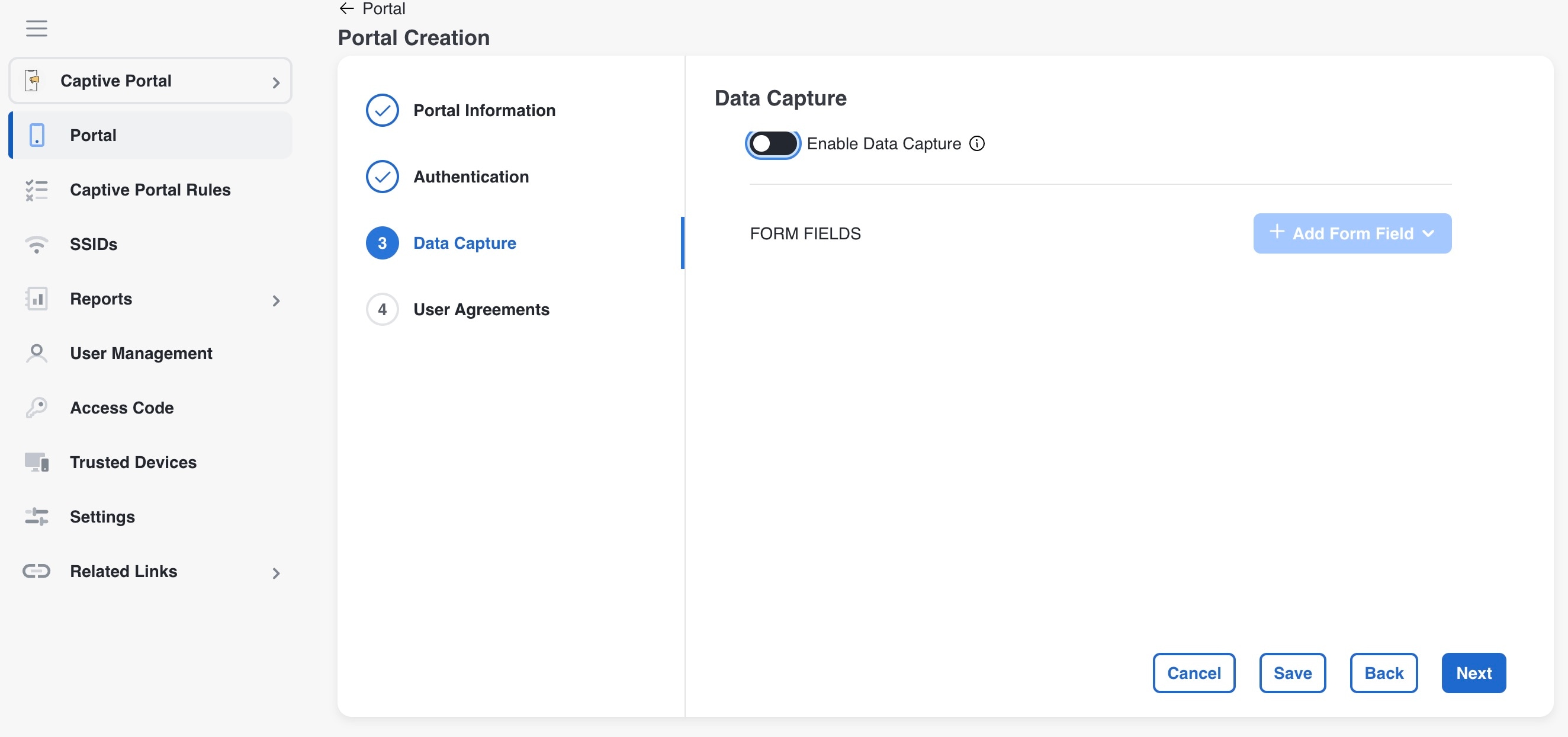
If you want to add Data Capture form for this portal, check the Enable Data Capture check box. Configure the Data Capture form. Add the fields required for the Data Capture form using the +Add Form Field button. For more information on adding fields to the Data Capture form, refer to the Add a data capture form to a portal. 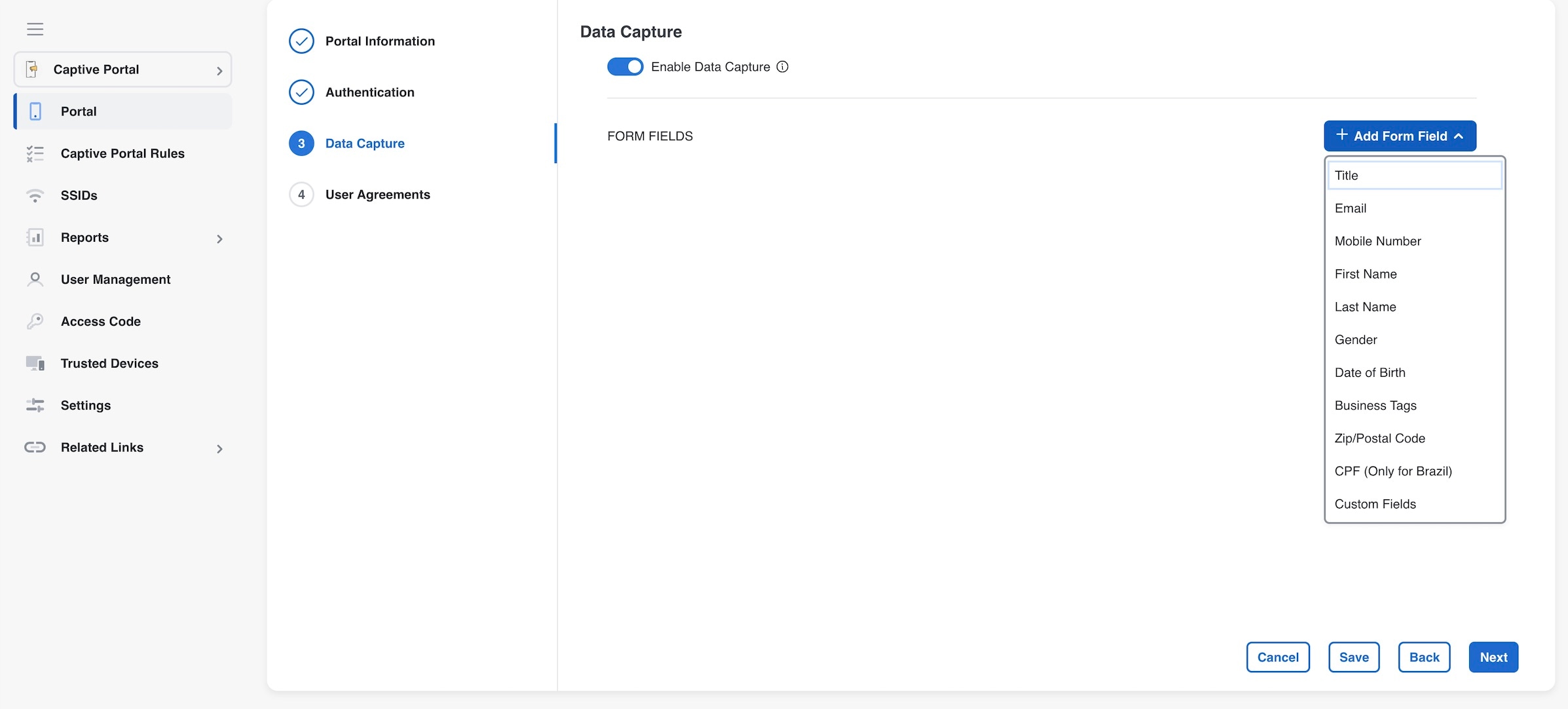
|
||||||
|
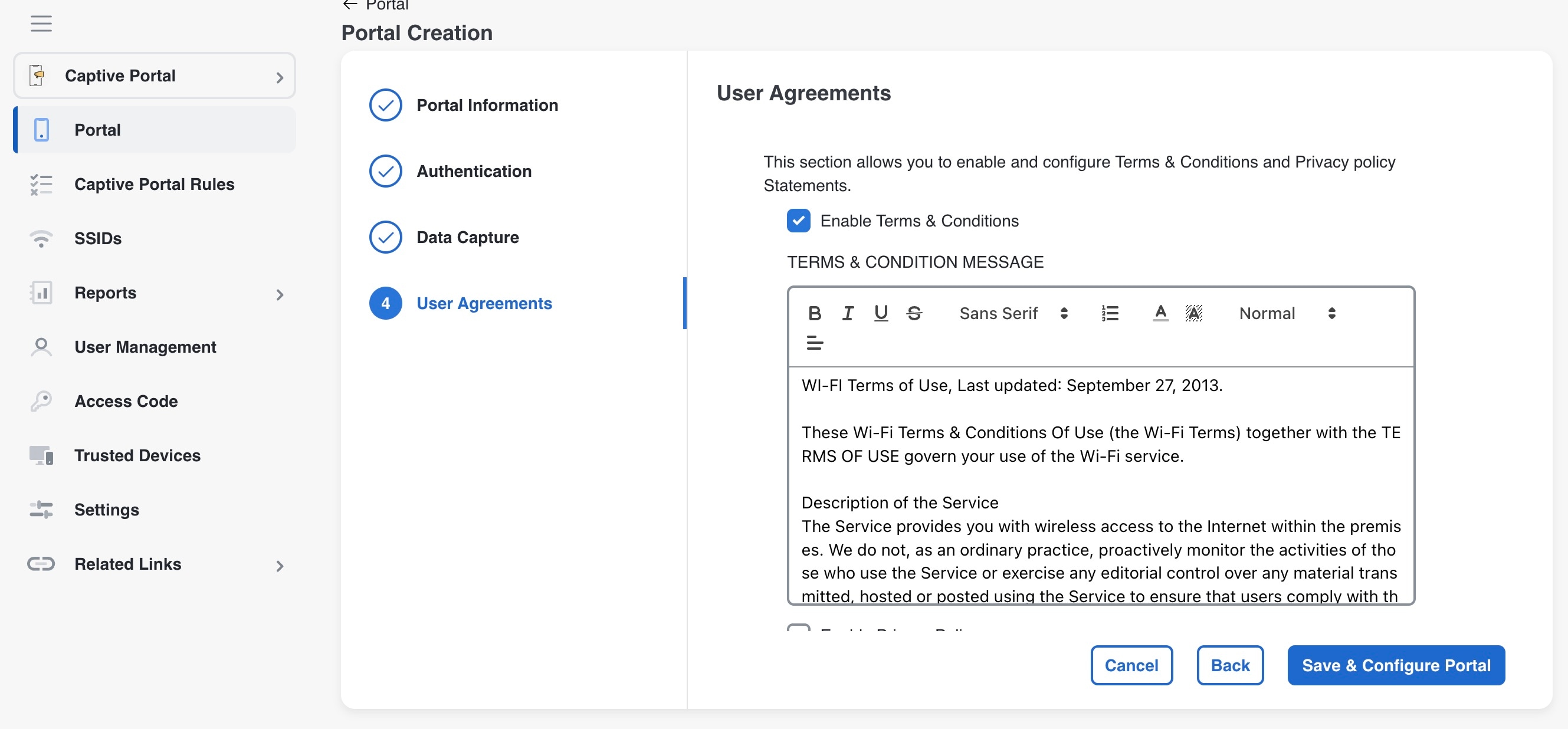
Step 6 |
In the Terms & Condition Message field, enter the Terms & Conditions for the portal. If you want to display privacy policy along with the Terms & Conditions, check the Enable Privacy Policy check box, and in the Privacy Policy field that appears, enter the privacy policy.
If you specify the privacy policy, during customer acquisition, the privacy policy also appears along with the Terms & Conditions. |
||||||
|
Step 7 |
From the How frequently do you want users to accept agreements drop-down list, select the frequency at which the customer must accept the Terms & Conditions to access the internet. In the User Accepts Terms In area, choose how the Terms & Conditions must appear during customer acquisition.
|
||||||
|
Step 8 |
If you want to restrict the internet access to the customers below certain age, select the Enable Age gating check box, and then choose the required age gating method from these:
A message Portal saved successfully appears, and the Portal window opens with the portal modules on the left and portal preview on the right. |
||||||
|
Step 9 |
Add features to the portal using the Portal modules. Click Save to save the changes made to each module.
|
Portal modules
These are the portal modules of Cisco Spaces:
-
Header/Branding: Define your page title and brand name in the portal using this module.
Use the Page Title field to modify the captive portal page title. The updated Page Title is displayed in your Cisco Spaces: Captive Portal app. You can add the brand name as text or a logo image.
-
Welcome Message: Add a welcome message in the portal using this module. You can configure the portal to show different welcome messages for first-time users and repeat users.
-
Notice: Add a notice in the portal using this module. This helps you display notices to the portal users whenever required. You can choose to provide the notice in thicker text, plain text, or text with an image format.
-
Authentication: Based on the authentication type selected when creating the portal, an Authentication module appears for the portal. The name of the module will be based on the authentication type. For example, if you have selected SMS with link verification as authentication type for a portal, the authentication module for that portal will be named as SMS Authentication. The Authentication module provide how to configure the landing page URL for the portal. The Authentication module is not available for the authentication type, No Authentication, if both Data Capture and User Agreements are not enabled.
-
Venue Map: Add a label and icon for the Venue Map using this module. The venue map is uploaded in the portal from your wireless network based on the location.
-
Videos: Add YouTube videos in the portal using this module. You can also add an appropriate caption and icon for the video section in the portal. You can also view the preview of the video when uploading.
-
Feedback: Add the feedback questions in the portal using this module. You can add multiple choice and rating questions. This module also lets you customize the labels for the Submit button, Thank You message, and Post Submission button. You can enable a text box for customers to add comments. You can also specify the e-mail addresses and subject for feedback.
-
Help: Add a help line number that the customer can contact for assistance using this module. You can customize the caption and icon for Help.
-
Get Apps: Add apps to the portal using this module. You can add appropriate caption and icon for each app using this module.
-
Get Internet: Add the external URL to which customer can navigate from the Get Internet section in the portal. To navigate to this URL, the customer has to accept the terms and conditions provided.
-
Promotions and Offers: Add the promotions and offers to display through the portal using this module. You can modify the title of the promotion. For each promotion, you can add appropriate captions and images and specify the URL to the promotion details. Promotions are displayed as carousels.
-
Add Module: Add customized content and menu items to the portal using this module. All the modules mentioned earlier are the default modules provided by Cisco Spaces. You can add additional items to a portal based on your requirements using the Add Module button.
Configure a language for a portal
In Cisco Spaces, you can configure the language in which the module captions and static content in the portal are to display. To display static content in a language other than English, upload the corresponding text to Cisco Spaces. Cisco Spaces does not support entering content directly in languages other than English. By default, the language is set to English, but you can change this setting.
 Note |
Cisco Spaces does not provide a content translation feature. |
To configure the display language for portal content, complete these steps.
Procedure
|
Step 1 |
To show static content, such as messages and country names, in a language other than English, upload the key values in the desired language. For more details on uploading key values for a language, refer to the Upload static content key values for a language. |
|
Step 2 |
Open the portal where you want to configure the language. |
|
Step 3 |
Click the Languages icon at the top of the Portal window. The Add Language window appears. |
|
Step 4 |
Click Add Language. |
|
Step 5 |
In the search field, enter the language. If Cisco Spaces supports this language, the name appears in the drop-down list. |
|
Step 6 |
Click the Add button next to the language name. The language gets added to the Added Languages list. |
|
Step 7 |
Click Add. A drop-down list now appears next to the Languages icon in the portal, showing the newly added language. |
|
Step 8 |
From this list, select the language for displaying static portal content. The captions of the modules are displayed in the chosen language. |
Set a default language
To set a default language, do the following:
Procedure
|
Step 1 |
In the portal, click the Languages icon at the top right of the window. |
|
Step 2 |
In the Add Language window, from the “Default Language” drop-down list, select the default language. |
|
Step 3 |
Click Add. |
Upload static content key values for a language
To set to display the static content in any language other than English, perform these steps:
Procedure
|
Step 1 |
In the portal, click the Languages icon at the top right of the window. |
|
Step 2 |
In the Add Language window, click Download to download and save the template. |
|
Step 3 |
Open the template. The template contains keys for various static messages. It also includes the message that appears if your language is English. The column for English has “en” as first row. |
|
Step 4 |
In the column next to the English column, enter the identifier for the language you want to use for the static content. For example, to display content in Arabic, enter “AR” in the first row. |
|
Step 5 |
Enter the text for each key in the remaining rows. |
|
Step 6 |
Save the file. |
|
Step 7 |
In the Add Language window, click Upload. |
|
Step 8 |
Click Add. |
What to do next
To know how to display the static content in a language, refer to the Configure a language for a portal.
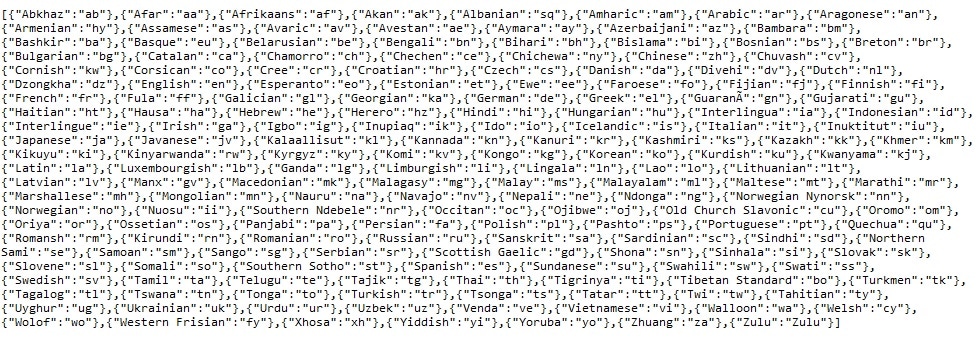
The language code for various languages are shown in this figure.
Configure authentication for a portal
To secure your portal from hacking or misuse, you can configure various authentication options for your portal. The customer is granted access only if authentication succeeds.
You can authenticate the internet provisioning through SMS, e-mail, access code, or social networks such as Facebook, Twitter, or LinkedIn. Cisco Spaces supports the SMS gateway of the third party vendors for SMS authentication. You can configure to provide SMS authentication through “SMS with password verification” or “SMS with link verification”. For “SMS with password verification”, you can define a custom verification code for a portal or you can configure to auto-generate the verification code.
During customer acquisition, the authentication process is initiated when the customer click any menu item in the portal. However, you can configure for inline authentication also, so that the Authentication module will be shown in the captive portal. For more information on inline authentication, refer to the Inline authentication.
Cisco Spaces supports these authentication types:
-
SMS with password verification: For this authentication type, validation of mobile number is mandatory. When the customer enters a valid mobile number, an SMS is sent to that mobile number, which contains a link and verification code. The customer can access the internet by providing the verification code in the SMS. The customer is not allowed to proceed further until the verification code is entered. Some use cases for this authentication type are SMS-based engagement campaigns, country specific requirements to verify the users connecting to internet, and so on. To know the authentication steps during customer acquisition, refer to the Steps for SMS with password verification authentication. For more information on configuring the “SMS with password verification”, refer to the Configure a portal for SMS with password verification section.
SMS with link verification: For this authentication type, validation of mobile number is optional. When the customer provides a valid mobile number, an SMS is sent to that mobile number with verification link. The customer can complete the validation by clicking the verification link in the SMS. However, customer can skip the validation process and proceed further. This authentication type can be used if the validation of the mobile number is not mandatory . To know the authentication steps during customer acquisition, refer to the Steps for SMS with link verification authentication. For more information, refer to the Configure a portal for SMS with link verification section.
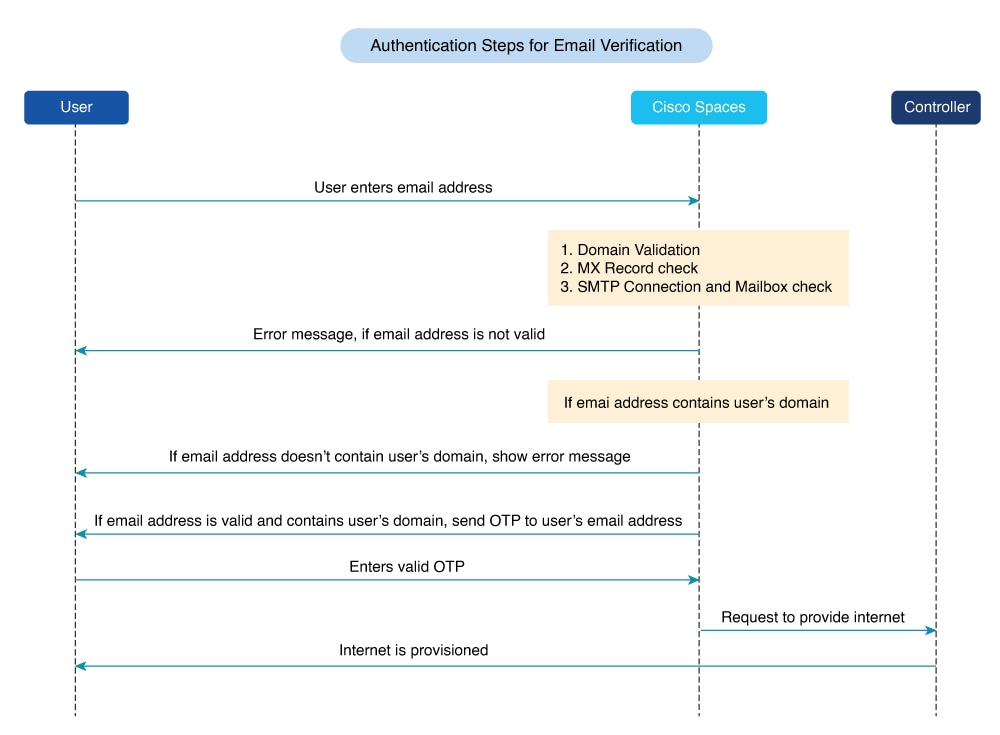
Email: The customer has to provide a valid e-mail ID to access the internet. To know the authentication steps during customer acquisition, refer to the Steps for E-mail authentication. For more information on configuring e-mail authentication, refer to the Configure a portal for E-mail authentication section.
Social Sign In: The internet access is provided only if the customer is logged in to a social site configured for authentication. You must configure at least one social site to use this option. To know the authentication steps during customer acquisition, refer to the Steps for social authentication. For more information on configuring the Social Sign In authentication, refer to the Configure a portal for social sign in authentication section.
Access Code: The customer has to provide a valid access code to access the internet. To know the authentication steps during customer acquisition, refer to Steps for access code authentication. For more information on configuring Access code authentication, refer to the Configure a portal for access code authentication section.
No Authentication: The internet access is provided without any authentication process. To know the authentication steps during customer acquisition, refer to Steps for no authentication with terms and conditions. For more information on configuring a portal for No Authentication, refer to the Configure a portal with no authentication section.
 Note |
The Opt In option is not available for the "Social Sign In" authentication type. You can configure the Data Capture form for all the authentication types, except “Social Sign In”. For more information on configuring the Data Capture form, refer to the Add a data capture form to a portal. For more information on Opt In feature, refer to the “Opted In Option for Users” section. |
 Note |
For SMS with link verification and SMS with password verification, you can include additional information that needs to be passed to the SMS gateways. For example, if you want to send the SMS in a language other than English to your customers, provision is now available to include that information in the SMS sent to the SMS Gateways. |
Configure a portal for SMS with link verification
To configure a portal for “SMS with link verification”, do these:
Procedure
|
Step 1 |
When creating a portal, from the Authentication Type drop-down list, select SMS with Link verification. |
||
|
Step 2 |
If you want to configure inline authentication for this portal, and display the “Data Capture form” and “User Agreements” in the home page, check the Display Authentication, Data Capture, and User Agreements on portal home page check box. For more information on inline authentication, refer to the Inline authentication. |
||
|
Step 3 |
If you want the customers to provide an option to opt for receiving notifications, check the “Allow users to Opt in to receive message” check box. |
||
|
Step 4 |
If the “Allow users to Opt in to receive message” check box is checked, these fields appear:
|
||
|
Step 5 |
In the SMS Text field, enter the text message that must appear in the SMS sent to the customer.
|
||
|
Step 6 |
From the Default Country drop-down list, select the country for which this setting is applicable. |
||
|
Step 7 |
From the SMS Gateway drop-down list, select the SMS gateway. The SMS Gateways configured in the Settings option are available for selection. You can also use the Demo Gateway provided by Cisco that is chargeable.
|
||
|
Step 8 |
Save the changes. |
What to do next
 Note |
Portals with SMS with link verification authentication type will have an authentication module named SMS Authentication. For more information on the Authentication Module, refer to the Authentication module. |
 Note |
If you have not configured the authentication type when creating the portal, you can specify it at any time using the Edit Portal button for that portal in the Portals window. |
Configure a portal for SMS with password verification
To configure a portal for “SMS with password verification”, perform these steps:
Procedure
|
Step 1 |
When creating a portal, from the Authentication Type drop-down list, select SMS with password verification. |
||
|
Step 2 |
If you want to configure inline authentication for this portal, and display user agreements on portal home page, check the Display Authentication and User Agreements on portal home page check box. For more information on inline authentication, refer to the Inline authentication. |
||
|
Step 3 |
If you want the customers to provide an option to opt for receiving notifications, check the “Allow users to Opt in to receive message” check box. |
||
|
Step 4 |
If the “Allow users to Opt in to receive message” check box is checked, these fields appear:
|
||
|
Step 5 |
Click the required Password Type.
|
||
|
Step 6 |
In the SMS field field, enter the text that must appear in the SMS that is sent to the customer.
|
||
|
Step 7 |
From the Default Country drop-down list, select the country for which this setting is applicable. |
||
|
Step 8 |
From the SMS Gateway drop-down list, select the SMS Gateway. The SMS Gateways configured in the Settings option are available for selection. You can also use the Demo Gateway provided by Cisco that is chargeable.
|
||
|
Step 9 |
Save the changes. |
What to do next
 Note |
Portals with SMS with password verification authentication type will have an authentication module named SMS Authentication. For more information on the Authentication module, refer to the Authentication module. |
 Note |
If you have not configured the authentication type when creating the portal, you can specify it at any time using the Edit Portal button for that portal in the Portals window. |
Configure a portal for social sign in authentication
Cisco Spaces supports authentication through these social networks:
-
Facebook
-
Twitter
-
LinkedIn
 Note |
To authenticate the access to the internet through a social network, you must configure the app for that social network in Cisco Spaces. You can configure the social app in Cisco Spaces through the Settings option. For more information, refer to the Add social apps for social authentication. |
To authenticate the access to a portal through social sign in, perform these steps:
Procedure
|
Step 1 |
When creating a portal, from the Authentication Type drop-down list, select Social Sign In. The social networks that are supported by Cisco Spaces for authentication appear along with the configured social apps. |
|
Step 2 |
If you want to configure inline authentication for this portal, and display user agreements in the portal home page, check the Display Authentication and Users Agreements on portal home page check box. For more information on inline authentication, refer to the Inline authentication. |
|
Step 3 |
Check the check box adjacent to the social networks through which you want to authenticate access to the internet. The social networks configured in the Social Apps option under the Settings section will be available for selection. For more information on configuring the Social Apps, refer to the Add social apps for social authentication. |
|
Step 4 |
Save the changes. |
What to do next
-
Portals with Social Sign In authentication type will have an authentication module named Social Authentication. For more information on the Authentication Module, refer to the Authentication module.
-
The +Add button takes you to the Social Apps window where you can configure the customized apps.
-
If you have not configured the authentication type when creating the portal, you can specify it at any time using the Edit Portal button for that portal in the Portals window.
Configure a portal for E-mail authentication
To configure a portal for e-mail authentication, do these:
Procedure
|
Step 1 |
When creating a portal, from the Authentication Type drop-down list, select Email. |
|
Step 2 |
If you want to configure inline authentication for this portal, check the Display Authentication and User Agreements on portal home page check box. For more information on inline authentication, refer to the Inline authentication. |
|
Step 3 |
If you want to provide the customer an option to opt for receiving notifications, check the Allow users to Opt in to receive message check box. |
|
Step 4 |
If the Allow users to Opt in to receive message check box is checked, these fields appear:
|
|
Step 5 |
Save the changes. |
What to do next
 Note |
Portals with Email authentication type will have an authentication module named Email. For more information on the Authentication Module, refer to the Authentication module. |
Configure a portal for access code authentication
To configure a portal for the Access Code authentication, do these:
Procedure
|
Step 1 |
When creating a portal, from the Authentication Type drop-down list, select Access Code. |
|
Step 2 |
If you want to configure inline authentication for this portal, and display user agreements on portal home page, check the Display Authentication and User Agreements on portal home page check box. For more information on inline authentication, refer to the Inline authentication. |
|
Step 3 |
If you want the customers to provide an option to opt for receiving notifications, check the Allow users to Opt in to receive message check box. |
|
Step 4 |
If the Allow users to Opt in to receive message check box is checked, these fields appear:
|
|
Step 5 |
Save the changes. You can create access codes and share it with your customers using the Access Code option displayed in the left pane of the Captive Portals app. For more information on creating and sharing the access codes, refer to the Access codes. |
What to do next
 Note |
Portals with Access Code authentication type, provided Data Capture or User Agreements is enabled. For more information on the Authentication module, refer to the Authentication module. |
Configure a portal with no authentication
To configure a portal for No Authentication, perform these steps:
Procedure
|
Step 1 |
When creating a portal, from the Authentication Type drop-down list, select No Authentication. |
|
Step 2 |
If you want to display data capture and user agreements on portal home page, check the Display Data Capture and User Agreements on portal home page check box. |
|
Step 3 |
If you want the customers to provide an option to opt for receiving notifications, check the Allow users to Opt in to receive message check box. |
|
Step 4 |
If the Allow users to Opt in to receive message check box is checked, these fields appear:
|
|
Step 5 |
Save the changes. |
Inline authentication
A captive portal inline authentication is a user authentication method that
-
displays the authentication module before the user clicks any link on the portal
-
reduces the number of steps required for users to initiate authentication, and
-
supports multiple authentication types, including SMS with verification, email, and social authentication.
To configure inline authentication, select the check box for inline authentication on the Authentication screen.
For the SMS with Link verification and SMS with password verification authentication types, the authentication section includes a field for entering the mobile number and a Connect button. For Email authentication, the authentication section includes a field to enter the email address. For social authentication, the authentication section provides buttons for each social network configured for the portal. Customers can complete authentication by selecting the appropriate social network.
Authentication module
When you select the authentication type for a portal, the system creates an authentication module for that portal based on the selected type.
However, if you select No Authentication or Access Code, and either Data Capture or User Agreements is not enabled, the portal will not have an authentication module.
The authentication module includes a field to specify an alternate landing page for the portal.
Add a data capture form to a portal
If you choose an authentication type other than Social Sign In for the portal, you can add a Data Capture form in the captive portal. You can add fields to the Data Capture form when creating the portal. These fields can capture customer details, such as first name, last name, mobile number, and other information. You can also add business tags based on which you can filter your customers.
 Note |
The business tags defined in the Data Capture form are accessible in the “Add Tags” option used in rules such as Captive Portal Rule, Engagement Rule, and Profile Rule. |
To configure a Data Capture form in a captive portal, perform these steps:
Procedure
|
Step 1 |
When creating a portal, after specifying the Terms and Conditions, click Next. The Data Capture screen appears. |
||||
|
Step 2 |
Enable the Data Capture check box. |
||||
|
Step 3 |
Click Add Form Field. You can only add Custom Fields to the Data Capture form although there are other elements such as:
|
||||
|
Step 4 |
Click the corresponding option to add the fields. General Fields
Element-Specific Fields
|
||||
|
Step 5 |
Save the changes.
|
Define a brand name for a portal
Cisco Spaces enables you to add your brand name and page title in the portal using the Header/Branding module. You can add the brand name as text or image. For example, you can use your company logo as a brand name.
To define a brand name and page title in the portal, perform these steps:
Procedure
|
Step 1 |
Open the portal for which you want to define the brand name. |
||
|
Step 2 |
Click the Header/Branding module. |
||
|
Step 3 |
In the Page Title field, edit the page title. 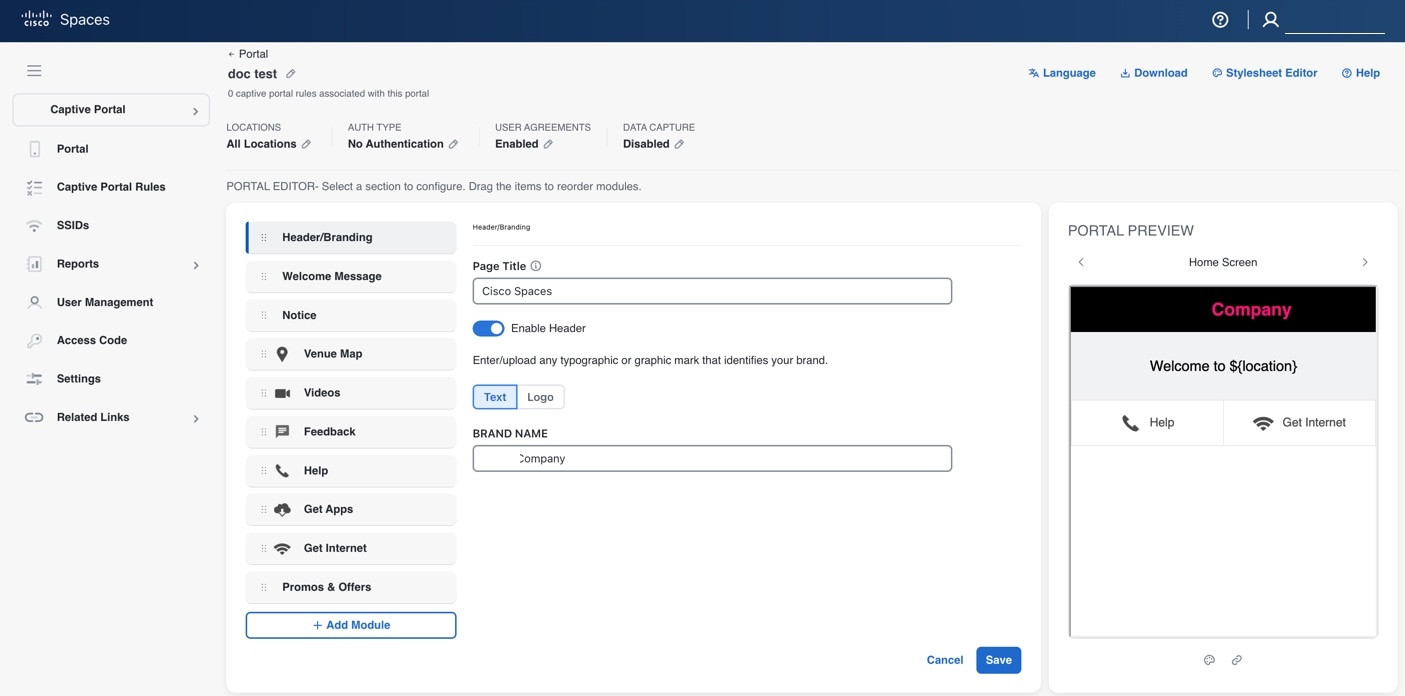
|
||
|
Step 4 |
Click Enable Header to view the portal preview. |
||
|
Step 5 |
Choose the type of brand.
|
||
|
Step 6 |
Click Save. The brand name and page title for the portal are defined. |
What to do next
 Note |
If you are modifying a portal that is already associated with a published captive portal, click the Save & Publish button to immediately publish the changes. The Save & Publish button appears only if the portal is associated with a captive portal rule. For more information on creating a captive portal rule, refer to the Create a captive portal rule to display captive portals. |
Add a welcome message to a portal
Add a welcome message to your portal using the Welcome module. The welcome message displays when a customer accesses your portal. Configure the portal to display different welcome messages for first-time and repeat users.
To add a welcome message to a portal, perform these steps:
Procedure
|
Step 1 |
Open the portal in which you need to add the welcome message. |
|
Step 2 |
Click the Welcome Message module. The Welcome Message window appears. |
|
Step 3 |
In the First time visitor welcome text field, enter the welcome message that must appear when a customer accesses your portal for the first time. You can include the location details using the smart link variables. For more information on smart link, refer to the Smart links and text variables for Captive Portals. |
|
Step 4 |
To display a different welcome message for repeat users, check the Add a custom message for Repeat Visitors check box. Add a custom message for Repeat Visitors check box. Enter the welcome message for repeat users in the adjacent text box. You can include the name and location details using the smart link variables. The variables 'firstName' and 'lastName' are available only if you configure a Data Capture module in the portal with the fields First Name and Last Name. 'firstName' and 'lastName' are available for authentication types except 'Social Sign In'. For more information on smart link, refer to the Smart links and text variables for Captive Portals. |
|
Step 5 |
Click Save. The welcome message is successfully defined for the portal. |
What to do next
 Note |
If the portal is associated with a published captive portal, click Save and Publish button to publish the changes. Save and Publish button appears only when the portal is associated with a captive portal rule. For more information on creating a captive portal rule, refer to the Create a captive portal rule to display captive portals. |
Add a notice to a portal
The Notice module allows you to provide notices in your portal. This module is useful when you want to pass any important information to your customers. You can add ticker notices, text notices, and images with text notices.
You can configure the date up to which the notice is to be displayed in the portal.
To add notices in a portal from the dashboard, follow these steps:
Procedure
|
Step 1 |
Open the portal where you want to add a notice. |
|
Step 2 |
Click the Notice module. The Notice window appears. |
|
Step 3 |
Click the type of notice you want. These options are available:
|
|
Step 4 |
In the Hide After field, choose the date up to which the notice is to display in the portal. |
|
Step 5 |
Click Save . The notice is successfully added to the portal. |
What to do next
 Note |
If you are modifying a portal that is already associated with a published captive portal, click the Save and Publish button to immediately publish the changes. The Save and Publish button appears only if the portal is associated with a captive portal rule. For more information on creating a captive portal rule, refer to the Create a captive portal rule to display captive portals. |
Provide the venue details in a portal
You can provide the venue details in a portal using the Venue Map module. You can define a label name, upload an icon image, and display a map for the venue using this module.
The default name of the module is Venue Map, but the module name changes when you edit the Label field.
To add the venue details for a portal, perform these steps:
Procedure
|
Step 1 |
Open the portal where you want to add venue details. |
||
|
Step 2 |
Click the Venue Map module. The VENUE MAP window appears. |
||
|
Step 3 |
In the Label field, enter the venue map label name to display in the portal.
|
||
|
Step 4 |
In the Logo area, upload the map icon to appear next to the map label. You can drag or click the Upload button.
|
||
|
Step 5 |
In the Store Map area, the map for this venue as in the wireless network appears.
|
||
|
Step 6 |
Click Save. The venue map is configured for the portal. |
What to do next
 Note |
If you are modifying a portal that is already associated with a published captive portal, click the Save and Publish button to immediately publish the changes. The Save and Publish button appears only if the portal is associated with a captive portal rule. For more information on creating a captive portal rule, refer to the Create a captive portal rule to display captive portals. |
Upload videos to a portal
You can upload the videos to Cisco Spaces portals using the videos module. In this module, you can add a label and an image for the area where the video appears in the portal and specify the YouTube URL of the video.
The default name of the module is videos. The module name changes according to the value you enter in the Label field.
 Note |
You can show only YouTube videos in your portal. |
To upload videos to a portal, perform these steps:
Procedure
|
Step 1 |
Open the portal in which you want to upload the video. |
||
|
Step 2 |
Click the Videos module. The VIDEOS window appears. |
||
|
Step 3 |
In the Label field, enter the label that appears for the area where the video displays in the portal.
|
||
|
Step 4 |
In the Logo area, upload the video icon adjacent to the video label. You can drag or click the Upload button.
|
||
|
Step 5 |
In the YouTube URL field, enter the YouTube URL of the video that you want to display in the portal. |
||
|
Step 6 |
Click Save. The video is successfully uploaded to the portal. |
What to do next
 Note |
If you modify a portal that is associated with a published captive portal, click the Save and Publish button to publish your changes. The Save and Publish button is available only if the portal is associated with a captive portal rule. For more information on creating a captive portal rule, refer to the Create a captive portal rule to display captive portals. |
Provide a feedback section in a portal
The Feedback module enables you to collect feedback from your portal customers. This module lets you add multiple questions to the feedback section. You can configure questions with multiple-choice answers or rating-based answers. You can also provide a text box for customers to add comments.
To add a feedback section in a portal, perform these steps:
Procedure
|
Step 1 |
Open the portal where you want to add the feedback section. Click the Feedback module. The FEEDBACK window appears. |
||
|
Step 2 |
In the Label field, enter a name to display for the feedback section. In the Icon area, upload an icon image that appears next to the feedback label. You can drag or click the Upload button. |
||
|
Step 3 |
In the Question field, enter a question for which you want the answer from the customer. In the Question Image area, upload an image that must appear adjacent to the question using the Upload button. |
||
|
Step 4 |
In the Question Type area, select a question type:
|
||
|
Step 5 |
In the Submit Button Label field, enter the name for the submit button, using which the customer must submit the answer. In the Thank You/Success message field, enter the message shown to customers after they submit their answer. |
||
|
Step 6 |
In the Post Submission button label field, enter the name for the button that appears after submission. This button takes the customer to the Cisco Spaces dashboard. If you want to provide a text box for the customer to enter the comments, select the Add a text box for additional comments from end user? check box. |
||
|
Step 7 |
In the Email to field, enter the destination email address for feedback. |
||
|
Step 8 |
In the Email from field, enter the From e-mail address to display to the receiver of the e-mail for the feedback e-mails. |
||
|
Step 9 |
In the Email Subject field, enter the subject line for feedback emails. Click Save. The feedback section is successfully created in the portal. |
What to do next
 Note |
If you are modifying a portal that is linked to a published captive portal, click the Save and Publish button to to apply your changes immediately. The Save and Publish button appears only if the portal uses a captive portal rule. For more information on creating a captive portal rule, refer to the Create a captive portal rule to display captive portals. |
Add a help option to a portal
You can add a helpline in your Cisco Spaces portal using the Help module. Customers can use this helpline to contact you if they need assistance. In this module, you can add a label and image for the area where the helpline appears in the portal. You can also specify the contact number for assistance.
The default name of the module is Help. The module name updates based on the value you enter in the Label field.
To add a Help option to a portal, perform the steps:
Procedure
|
Step 1 |
Open the portal in which you need to add a help option. |
||
|
Step 2 |
Click the Help module. The HELP window appears. |
||
|
Step 3 |
In the Label field, enter the label that must appear for the area where the helpline appears in the portal.
|
||
|
Step 4 |
In the Icon area, upload the help icon that must appear adjacent to the help label. You can drag or click the Upload button.
|
||
|
Step 5 |
In the Contact field, enter the help line number. |
||
|
Step 6 |
Click Save . The help option is successfully defined for the portal. |
What to do next
 Note |
If you are modifying a portal that is already associated with a published captive portal, click the Save and Publish button to immediately publish the changes. The Save and Publish button appears only if the portal is associated with a captive portal rule. For more information on creating a captive portal rule, refer to the Create a captive portal rule to display captive portals. |
Add apps to a portal
You can add applications to your Cisco Spaces portal using the Apps module, which supports apps from both the iOS App Store and Google Play Store. Within the Apps module, you can add a label and image for the section where the applications are displayed in the portal.
By default, the module is named Get Apps. If you modify the Button Label field, the module name updates accordingly.
To add an app to a portal, perform these steps:
Procedure
|
Step 1 |
Open the portal you want to modify. |
||
|
Step 2 |
Click the Get Apps module. The GET APPS window appears. |
||
|
Step 3 |
In the Label field, enter the label to be displayed in the portal for the application area.
|
||
|
Step 4 |
In the Icon area, you can drag or click the Upload button to add the app icon that will appear next to the app label.
|
||
|
Step 5 |
Click Add an App. |
||
|
Step 6 |
In the Add App area, do these: |
||
|
Step 7 |
Click Save. The app is successfully added to the portal. |
What to do next
 Note |
If you are modifying a portal that is already associated with a published captive portal, click the Save and Publish button to immediately publish the changes. The Save and Publish button appears only if the portal is associated with a captive portal rule. For more information on creating a captive portal rule, refer to the Create a captive portal rule to display captive portals. |
Provide access to the internet from a portal
You can provide access to the internet using the Get Internet module. You can add an external URL to a portal using the Get Internet module. In this module, you can add a label and image for the area where the internet link appears in the portal.
The default name of the module is Get Internet. The module name changes according to the value you enter in the Button Label field.
 Note |
If inline authentication is configured for the captive portal, the Get Internet module is not shown during customer acquisition, even if it is configured. For more information on inline authentication, refer to the Inline authentication. |
To provide access to the internet from a portal, perform these steps:
Procedure
|
Step 1 |
Open the portal where you want to add a link to the internet. |
||
|
Step 2 |
Click the Get Internet module. The GET INTERNET window appears. |
||
|
Step 3 |
In the Label field, enter the text to display for the internet link in the portal.
|
||
|
Step 4 |
You can drag or click the Upload button to upload the icon that must appear adjacent to the internet link.
|
||
|
Step 5 |
To change the landing page, ensure that the Change Landing page URL check box is checked. |
||
|
Step 6 |
In the Launch Page field, enter the URL for internet access from the portal. |
||
|
Step 7 |
Click Save. An option to access the internet is successfully configured in the portal. |
What to do next
 Note |
If the portal is already associated with a published captive portal, click Save and Publish to update the changes immediately. The Save and Publish button is visible only if the portal has an associated captive portal rule. For more information on creating a captive portal rule, refer to the Create a captive portal rule to display captive portals. |
Add promotions and offers to a portal
The Promos & Offers module enables you to add promotions and offers for customers in your portal. You can add various promotion items to your portal and link them to specific promotion URLs. The module enables you to add a label, icon, and web URL for each promotion.
 Note |
The promotions are displayed as carousels. |
To add promotions and offers to a portal, perform these steps:
Procedure
|
Step 1 |
Open the portal in which you want to add the promotions and offers module. |
|
Step 2 |
Click the Promos & Offers module. The PROMOS & OFFERS window appears. |
|
Step 3 |
In the Label field, enter the label that must appear for the area in which the promotions and offers appear. |
|
Step 4 |
Click Add a Promotion. |
|
Step 5 |
In the Promo Name field, enter a name for the promotion link. |
|
Step 6 |
In the Promo Image area, you can drag or click the Upload button to upload the icon that must appear adjacent to the promotion link. |
|
Step 7 |
In the Link Promo to URL field, enter the URL that links to the promotion web page. |
|
Step 8 |
Click Save. The promotions and offers link is successfully added to the portal. |
What to do next
 Note |
You can add more than one promotion to your portal using the Add a Promotion button. |
 Note |
If you are modifying a portal that is already associated with a published captive portal, click the Save and Publish button to immediately publish the changes. The Save and Publish button appears only if the portal is associated with a captive portal rule. For more information on creating a captive portal rule, refer to the Create a captive portal rule to display captive portals. |
Delete a promotion and an offer for a portal
Cisco Spaces enables you to remove a promotion from a portal after the required time line.
To delete a promotion from your portal, perform these steps.
Procedure
|
Step 1 |
Open the portal from which you want to delete the promotion. |
|
Step 2 |
Click the Promos & Offers module. The PROMOS & OFFERS window appears with the promotions added to that portal. |
|
Step 3 |
Click the Delete icon that appears at the top right of the promotion that you want to delete. |
Add custom content and menu items to a portal
The “Add Module” module enables you to add custom content and menu items in your portal according to your requirements. You can add multiple menu items to your portal. Each menu item can be linked to a different web page. The module enables you to add a label, icon, and web URL for each menu item. You can also enable a Back button if the linked web page is compatible.
To add a customized menu item to a portal, perform these steps:
Procedure
|
Step 1 |
Open the portal where you want to add a custom menu item. |
|
Step 2 |
Click Add Module. |
|
Step 3 |
Choose one of these options:
The custom module is added to the portal module list and its page opens. The fields that appear for the custom module depend on the custom module type. |
|
Step 4 |
For “Custom Content”, provide these details for the custom module:
|
|
Step 5 |
For Menu Item field, enter these details for the custom module. |
|
Step 6 |
To enable a back button in the linked web page, check the Enable Back button check box. |
|
Step 7 |
Click Save . The customized content or menu item is successfully added to the portal. |
What to do next
 Note |
The menu items added appear as text in the preview of the portal, but appear as links in the runtime. |
 Note |
If you are modifying a portal that is already associated with a published captive portal, click the Save and Publish button to immediately publish the changes. The Save and Publish button appears only if the portal is associated with a captive portal rule. For more information on creating a captive portal rule, refer to the Create a captive portal rule to display captive portals. |
Export a portal
Cisco Spaces enables you to export a portal created using the portal modules.
To export a portal, perform these steps:
Procedure
|
Step 1 |
Open the portal that you want to export. |
|
Step 2 |
Click the Export Portal icon at the top of the Portal window. The Export Portal dialog box appears. |
|
Step 3 |
Click Download. |
|
Step 4 |
In the window that appears, choose any of these options: |
Edit the portal style sheet
The Style Sheet Editor option in Cisco Spaces enables you to update the style sheet of a portal. This helps you change the font properties and appearance of your portal.
To edit a portal style sheet, perform these steps:
Procedure
|
Step 1 |
Open the portal whose style sheet you want to edit. |
|
Step 2 |
Click Stylesheet Editor at the top of the Portal window. |
|
Step 3 |
In the CSS Editor tab, make necessary changes in the style sheet. |
|
Step 4 |
Click Save. |
What to do next
You can upload the style sheet from an external source such as CSS designed for another portal.
You can also download the style sheet to make necessary updates, and then upload the edited style sheet. For example, if you want a CSS designer to edit the portal, you can download the style sheet using the Download CSS button. After making changes to the style sheet, you can upload it to Cisco Spaces by clicking the Upload CSS button.
Add asset to the style sheet
To improve the outlook of your portal, you can add assets such as images and fonts to the Stylesheet Editor of your portal. You can add image files such as jpeg, png, and tif. After uploading the assets, edit your style sheet to use them in your portal.
To add assets to a portal style sheet, perform these steps:
Procedure
|
Step 1 |
Open the portal of which you want to edit the style sheet. |
||
|
Step 2 |
Click Stylesheet Editor. |
||
|
Step 3 |
Click the Asset Library tab. |
||
|
Step 4 |
Drag and drop the asset file, or upload it using the Choose File button.
The file gets added to the assets list. |
What to do next
You can copy the URL of an asset using the Copy Asset url button displayed for an asset at the bottom of the asset. To add this asset in your portal, add the URL in the style sheet in the appropriate location.
You can delete an asset using the delete icon displayed for the asset in the assets list.
Import a portal
Cisco Spaces enables you to import a portal from an external path. For example, if you want to enhance a portal using an external application, you can export the portal using the Export Portal icon, make necessary enhancements, and import the portal file to Cisco Spaces using the Import Portal option.
To import a portal, perform these steps:
Procedure
|
Step 1 |
In the Cisco Spaces dashboard, choose Home. |
|
Step 2 |
In the window that appears, click Captive Portal. |
|
Step 3 |
In the Captive Portal window, choose Portal in the left pane. The Captive Portal window appears. |
|
Step 4 |
Click Import Portal at the top-right of the window. |
|
Step 5 |
In the Import Portal window that appears, do these: |
|
Step 6 |
Click Import. |
Delete a portal
To delete a portal, perform these steps:
Procedure
|
Step 1 |
In the Cisco Spaces dashboard, choose Home. |
||||
|
Step 2 |
In the window that appears, click Captive Portal. |
||||
|
Step 3 |
In the Captive Portal window, choose Portal in the left pane. The Captive Portal window appears with the list of available portals in Cisco Spaces. |
||||
|
Step 4 |
Click the Delete icon at the far right of the portal you want to delete. |
||||
|
Step 5 |
In the Delete Portals window that appears, click Yes. The portal gets deleted from Cisco Spaces.
|
Edit a portal
To edit a portal, perform these steps:
Procedure
|
Step 1 |
In the Cisco Spaces dashboard, choose Home. |
|
Step 2 |
In the window that appears, click Captive Portal. |
|
Step 3 |
In the Captive Portal window, choose Portal in the left pane. The Captive Portal window appears with the list of available portals in Cisco Spaces. |
|
Step 4 |
Click the Edit icon that appears at the far right of the portal that you want to edit. |
|
Step 5 |
Make necessary changes and save the changes made for each module. |
|
Step 6 |
To publish the changes, click the Save and Publish button for the portal. |
Edit the locations for a portal
To edit the locations for a portal, perform these steps:
Procedure
|
Step 1 |
In the Cisco Spaces dashboard, choose Home. |
|
Step 2 |
In the window that appears, click Captive Portal. |
|
Step 3 |
In the Captive Portal window, choose Portal in the left pane. |
|
Step 4 |
In the Captive Portal window that appears, check the check box for the portal for which you want to edit the locations. |
|
Step 5 |
Click Add Locations that appears at the top of the window. |
|
Step 6 |
In the Add Locations to Portals window that appears, select the locations for the portal, and click Save Changes. |
|
Step 7 |
To publish the changes, click the Save and Publish button for the portal. |
E-mail a portal preview URL
You can e-mail the preview URL of a portal for the receiver to preview the portal.
To e-mail the preview URL of a portal, perform these steps:
Procedure
|
Step 1 |
Open the portal whose preview URL you want to e-mail. The portal appears. |
|
Step 2 |
Click the Link icon in the Portal Preview area at the far right of the window. |
|
Step 3 |
In the Email Portal URL field, enter the recipient's e-mail address for the portal preview URL. |
|
Step 4 |
Click Send. A message confirms that the URL was sent to the specified e-mail address. |
Preview a portal using QR code
Cisco Spaces allows you to preview a portal by scanning its QR code. To use this feature, install a QR code reader app on your mobile device.
To scan the QR code of a portal, perform these steps:
Procedure
|
Step 1 |
Open the portal whose QR code you want to scan. |
|
Step 2 |
Click the Link icon in the Portal Preview area at the far right of the window. |
|
Step 3 |
Open the QR code reader app on your mobile. |
|
Step 4 |
In the portal, point your mobile device at the area labeled Scan with QR code reader on your mobile device. The mobile device scans the QR code and displays a message asking whether to open the URL. |
|
Step 5 |
Click Ok . The portal is opened in your mobile screen. |
Preview a portal
Cisco Spaces enables you to to preview each module and screen of a captive portal before deployment. Cisco Spaces enables you to preview each module in the captive portal separately. The default preview is of the Captive Portal home screen. The preview of authentication module simulates the customer acquisition (runtime) flow. Module previews appear as carousels.
To preview a captive portal, perform these steps:
Procedure
|
Step 1 |
Open the portal of which you want to view the preview. The preview of the portal home screen appears in the Portal Preview area. |
|
Step 2 |
Click the right arrow to navigate to the next screen. |
Preview the portal in various devices
Cisco Spaces lets you view how the captive portal appears on different devices. You can preview the portals for mobile, tablets, and laptops. Cisco Spaces lets you preview each module of the captive portal individually. By default, the preview displays the Captive Portal home screen.
To preview a captive portal for a device, perform these steps:
Procedure
|
Step 1 |
Open the portal of which you want to view the preview in various devices. The preview of the portal home screen appears, and the devices are displayed on the right side of the portal. The CSS Editor window appears, showing the device preview in the right pane. |
||
|
Step 2 |
Do any of these: |
||
|
Step 3 |
To preview a particular module in the captive portal, select the module from the adjacent drop-down list.
|
Display, hide or reorder the modules in a captive portal
Portal administrators can display or hide a module in the portal. To do this, use the ON/OFF toggle switch at the top left of the module. To reorder the modules, drag and drop the modules to the required location. The preview section reflects the changes.
 Feedback
Feedback