Onboard an On-Premises Firewall Management Center to Security Cloud Control
Security Cloud Control provides these methods to onboard on-premises Firewall Management Centers:
-
(Recommended) Auto discover and onboard on-premises Firewall Management Center integrated with Cisco Security Cloud
 Note |
Security Cloud Control complements FMC by allowing you to:
|
Limitations and Guidelines
These are the limitations applicable to onboarding an on-premises Firewall Management Center:
-
When you onboard an on-premises Firewall Management Center, all devices registered to it are also onboarded. If a managed device is disabled or unreachable, Security Cloud Control may display that device in the Security Devices page. However, the system cannot send requests to or view information for the device.
-
Onboarding an on-premises Firewall Management Center does not cascade the policies in on-premises Firewall Management Center to Security Cloud Control or Cloud-Delivered Firewall Management Center. You can migrate a Firewall Threat Defense managed by on-premises Firewall Management Center to Cloud-Delivered Firewall Management Center using the built-in Migrate FTD to cdFMC feature, which brings all the policies linked to the device. For more information, see Migrate Threat Defense to Cloud-delivered Firewall Management Center.
-
We recommend creating a new user on on-premises Firewall Management Center specifically for Security Cloud Control communication with administrator-level permissions. If you onboard an on-premises Firewall Management Center and simultaneously log in to that on-premises Firewall Management Center using the same credentials, the onboarding process fails.
-
To create a new user on on-premises Firewall Management Center for Security Cloud Control communication, set the Maximum Number of Failed Logins for user configuration to zero.
-
For on-premises Firewall Management Centers running version 7.4 or later, if you experience a switchover and the FMC is no longer connected to the cloud, try disabling SecureX and then re-enabling it.
Auto onboard an On-Premises Firewall Management Center integrated with Cisco Security Cloud
The auto-discovery and onboarding feature is enabled by default in Security Cloud Control. All on-premises Firewall Management Centers running version 7.2 or later and integrated with Cisco Security Cloud are automatically discovered and onboarded to Security Cloud Control. The associated Firewall Threat Defense devices are onboarded to Security Cloud Control.
Security Cloud Control also onboards the on-premises Firewall Management Center high-availability (HA) pair.
Before you begin
Procedure
|
Step 1 |
Integrate the on-premises Firewall Management Center you want to onboard with Cisco Security Cloud and register it with a Security Cloud Control tenant. For more information, see Integrate an On-Premises Firewall Management Center With Cisco Security Cloud. |
|
Step 2 |
Log in to the Security Cloud Control tenant that was registered with the on-premises Firewall Management Center. |
|
Step 3 |
Choose Tools & Services > Firewall Management Center . All on-premises Firewall Management Centers associated with your tenant are displayed in the FMC tab. For more information, see View Onboarded On-Premises Firewall Management Center. |
Integrate an On-Premises Firewall Management Center With Cisco Security Cloud
This procedure describes how to integrate the On-Premises Firewall Management Center with Cisco Security Cloud. By enabling Cisco Security Cloud integration, your management center gets registered to the Cisco cloud tenancy.
Before you begin
When onboarding an on-premises Firewall Management Center:
-
If you already have a Security Cloud Control tenant, you will be prompted to confirm whether you want to attach the on-premises Firewall Management Center to that existing tenant.
-
If you do not have a tenant or account, the on-premises Firewall Management Center integration wizard will automatically create a new tenant for you during the registration task the onboarding process. This tenant is a free tier provided exclusively for on-premises Firewall Management Center AI Assist enablement. Allow the wizard to manage tenant creation so that you do not receive a trial tenant that would later require conversion. The wizard manages this process to provide a seamless experience.
-
If you intend to use the Cloud-Delivered Firewall Management Center or manage firewalls using the Security Cloud Control, you must purchase a base license and device entitlements. For detailed licensing information and product options, refer to the Security Cloud Control Licensing Overview.
Procedure
|
Step 1 |
In your on-premises Firewall Management Center, do the following:
|
|
Step 2 |
Based on your on-premises Firewall Management Center version, do the following:
A separate browser tab opens to log you in to your Security Cloud Control account. Make sure this page is not blocked by a pop-up blocker. |
|
Step 3 |
Click Continue to Cisco SSO. 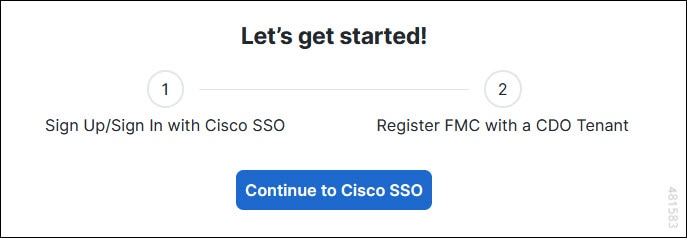
|
|
Step 4 |
Log in to your Security Cloud Control account. 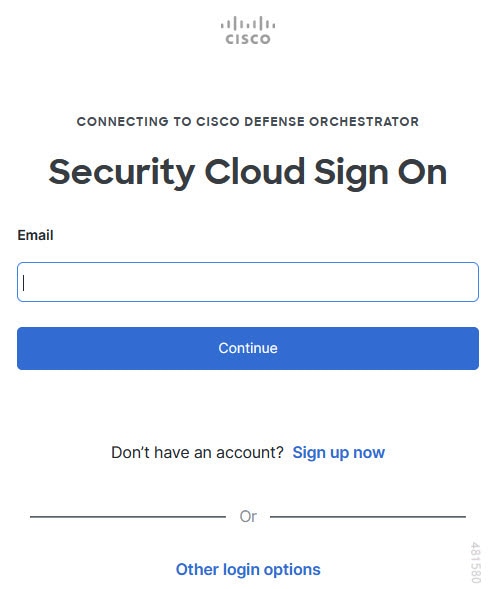
If you do not have a security cloud sign on account to log in to Security Cloud Control and you want to create one, click Sign up now in the Security Cloud Sign On page. See Create a New Cisco Security Cloud Sign On Account. |
|
Step 5 |
Choose a Security Cloud Control tenant that you want to use for this integration. The on-premises Firewall Management Center and the managed devices get onboarded to the Security Cloud Control tenant that you choose here. 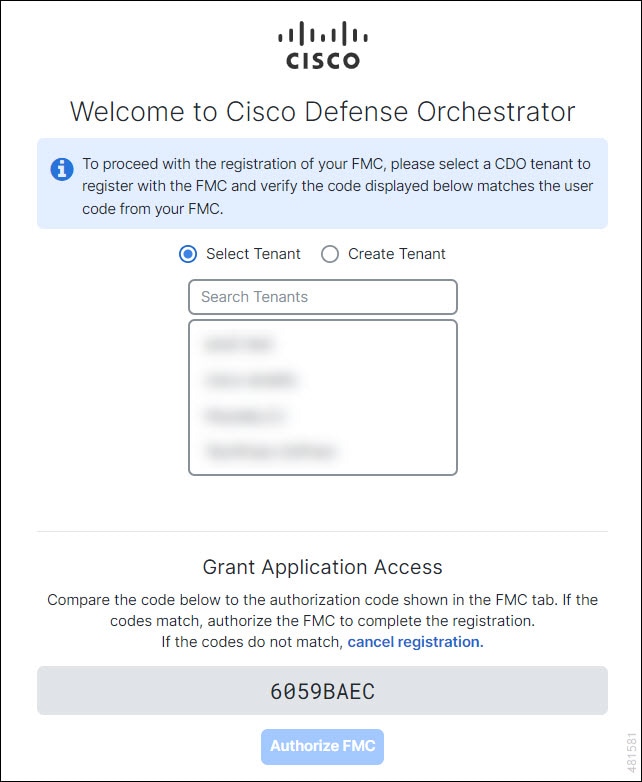
If you do not already have a Security Cloud Control tenant or if you want to use a new tenant for this integration, create a new tenant. |
|
Step 6 |
Verify that the code displayed in the Security Cloud Control login page matches the code provided by the on-premises Firewall Management Center. 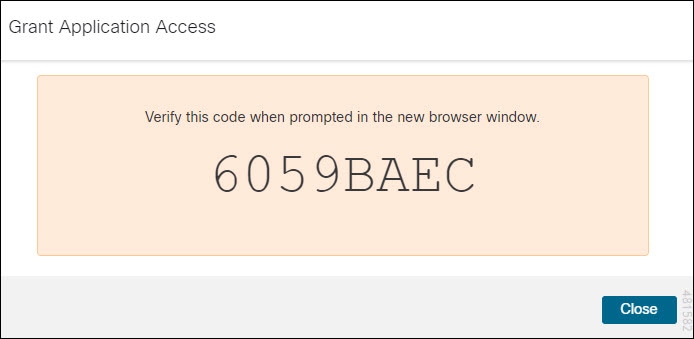
|
|
Step 7 |
Click Authorize FMC. |
|
Step 8 |
In the on-premises Firewall Management Center UI, click Save to save the configuration. You can view the task progress under . The registration task can take up to 90 seconds to complete. If you must use on-premises Firewall Management Center while the registration task is in progress, open the on-premises Firewall Management Center in a new window. |
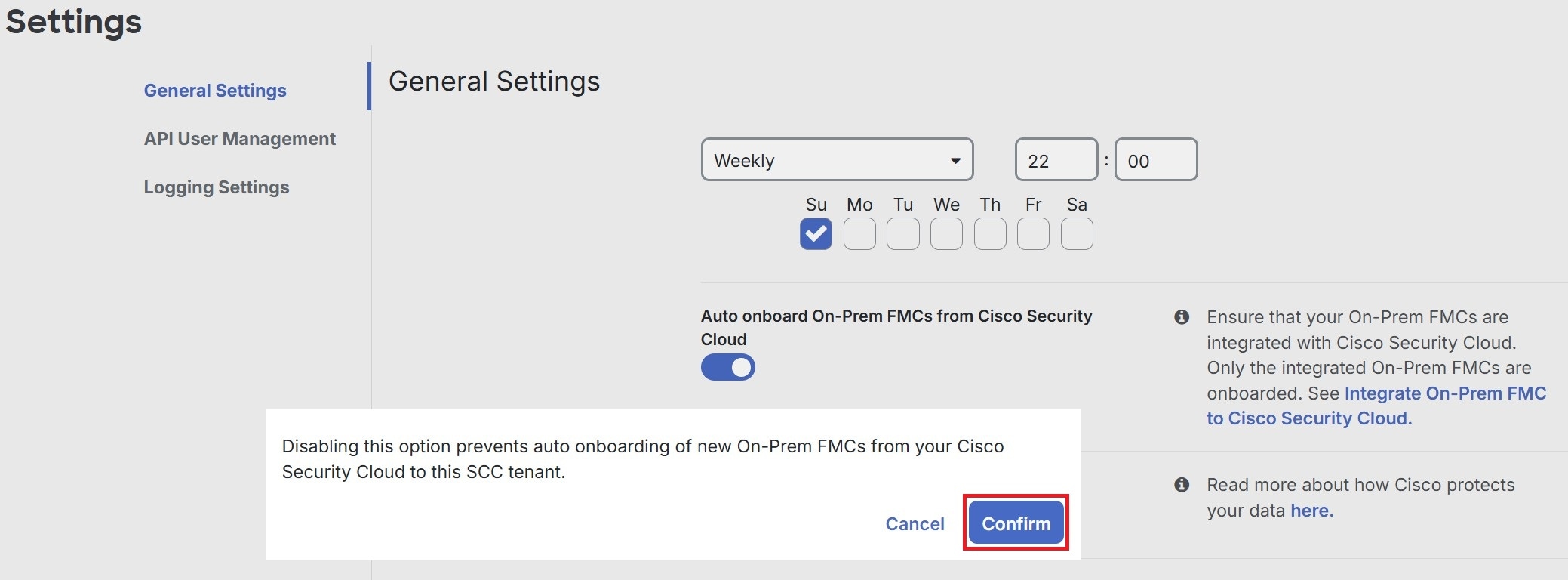
Auto onboard On-Prem FMCs from Cisco Security Cloud
Disabling the auto-onboarding functionality stops new on-premises Firewall Management Centers from being automatically added from your Cisco Security Cloud tenant.
 Note |
Only a Super Admin or Admin can enable or disable this functionality on Security Cloud Control. |
Procedure
|
Step 1 |
Choose Settings > General Settings. |
|
Step 2 |
Choose . |
|
Step 3 |
Turn off the Auto onboard On-Prem FMCs from Cisco Security Cloud toggle button to disable the auto-onboarding of on-premises Firewall Management Center. |
|
Step 4 |
Click Confirm.
|
Onboard an On-Premises Firewall Management Center to Security Cloud Control with Credentials
To onboard an on-premises Firewall Management Center to Security Cloud Control with credentials, follow this procedure:
Before you begin
These prerequisites must be met:
-
For Cloud Secure Device Connector (SDC): Allow inbound traffic on port 443 of the on-premises Firewall Management Center.
The SDC reaches the on-premises Firewall Management Center by allowing inbound traffic on port 443.

Both the Security Cloud Control and the SDC are hosted in the cloud.
-
For On-Premises Secure Device Connector (SDC): Allow outbound connectivity on port 443 of the SDC.
The SDC requires connectivity to the Security Cloud Control, making it imperative to permit outbound traffic from the SDC to the Security Cloud Control. No additional port configuration is required on on-premises Firewall Management Center.

Procedure
|
Step 1 |
Choose . |
||
|
Step 2 |
Choose . |
||
|
Step 3 |
Click |
||
|
Step 4 |
Click Firewall Management Center. |
||
|
Step 5 |
Select the Use Credentials card. |
||
|
Step 6 |
Enter the device name and location and click Next. |
||
|
Step 7 |
Enter the Username and Password of the account credentials you want to use to access the on-premises Firewall Management Center. Click Next. |
||
|
Step 8 |
After you onboard the device, you can add labels to your on-premises Firewall Management Center, or you can click Go to Services to view the page of onboarded devices. If the device is healthy, the FMC displays a Synced status.
|
Redirect Security Cloud Control to an On-Premises Firewall Management Center
After you onboard an on-premises Firewall Management Center to Security Cloud Control, update the management interface's hostname in the on-premises Firewall Management Center UI so that it contains the FQDN. If you do not update the management interface's hostname, you cannot cross-launch from Security Cloud Control.
Use this procedure to update the management interface hostname and redirect from Security Cloud Control to on-premises Firewall Management Center:
Procedure
|
Step 1 |
Log in to the On-Premises Firewall Management Center UI. |
||
|
Step 2 |
Choose . |
||
|
Step 3 |
Click the Management Interfaces tab. |
||
|
Step 4 |
Under Shared Settings, locate the Hostname field and enter the Firewall Management Center's FQDN. |
||
|
Step 5 |
Click Save.
|
 to onboard an
to onboard an 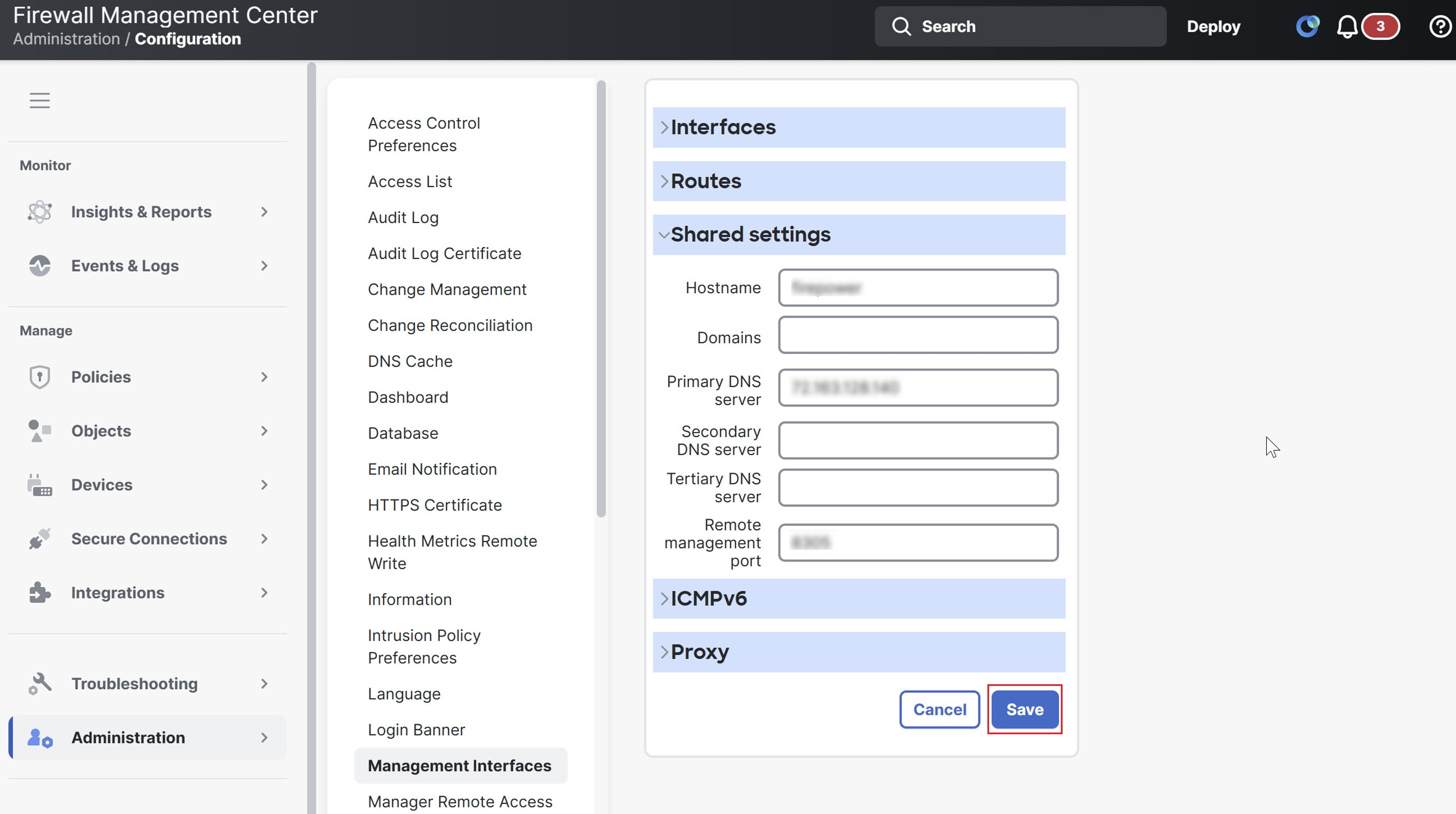
 Feedback
Feedback