Feature history for RADIUS and TACACS
| Feature name | Release information | Description |
|---|---|---|
| RADIUS and TACACS Support for Multitenancy |
Cisco IOS XE Catalyst SD-WAN Release 17.12.1a Cisco Catalyst SD-WAN Manager Release 20.12.1 |
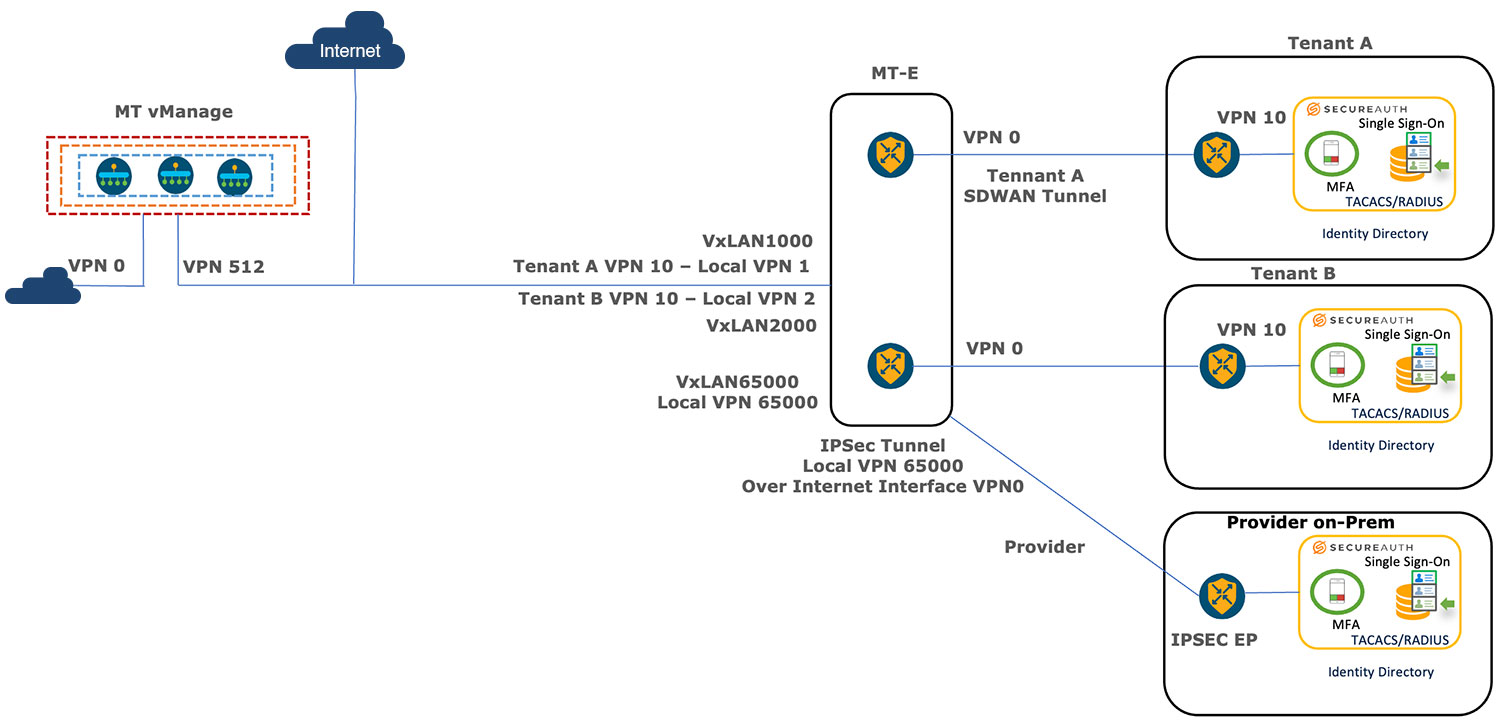
This feature enables support for Remote Authentication Dial-In User Service (RADIUS) and Terminal Access Controller Access Control System (TACACS) authentication in a multitenant deployment on WAN edge devices. |
| Configure RADIUS and TACACS Servers to Receive Authentication Requests Over Management VPN 512 |
Cisco IOS XE Catalyst SD-WAN Release 17.16.1a Cisco Catalyst SD-WAN Manager Release 20.16.1 |
This feature provides increased security by allowing you to configure tenants to send and receive AAA traffic over WAN transport VPN 0 or management VPN 512. |
 Feedback
Feedback