Monitoring Mobile Technologies
The following topics provide an overview of mobile technologies and describe how to work with mobile technologies in Prime Network Vision:
• User Roles Required to Work with Mobile Technologies
User Roles Required to Work with Mobile Technologies
• GPRS/UMTS Networks - An Overview
GPRS/UMTS Networks - An Overview
• Working With GPRS/UMTS Network TechnologiesLTE Networks - An Overview
Working With GPRS/UMTS Network TechnologiesLTE Networks - An Overview
• Working with LTE Network Technologies
Working with LTE Network Technologies
• Viewing Operator Policies, APN Remaps, and APN Profiles
Viewing Operator Policies, APN Remaps, and APN Profiles
• Working with Active Charging Service
Working with Active Charging Service
• Configuring and Viewing Mobile Technologies
Configuring and Viewing Mobile Technologies
User Roles Required to Work with Mobile Technologies
This topic identifies the GUI default permission or scope security level that is required to work with the mobile technologies in Prime Network Vision. Prime Network determines whether you are authorized to perform a task as follows:
• For GUI-based tasks (tasks that do not affect elements), authorization is based on the default permission that is assigned to your user account.
For GUI-based tasks (tasks that do not affect elements), authorization is based on the default permission that is assigned to your user account.
• For element-based tasks (tasks that do affect elements), authorization is based on the default permission that is assigned to your account. That is, whether the element is in one of your assigned scopes and whether you meet the minimum security level for that scope.
For element-based tasks (tasks that do affect elements), authorization is based on the default permission that is assigned to your account. That is, whether the element is in one of your assigned scopes and whether you meet the minimum security level for that scope.
For more information on user authorization, see the Cisco Prime Network 3.10 Administrator Guide.
The following tables identify the tasks that you can perform:
• Table 26-1 identifies the tasks that you can perform if a selected element is not in one of your assigned scopes.
Table 26-1 identifies the tasks that you can perform if a selected element is not in one of your assigned scopes.
• Table 26-2 identifies the tasks that you can perform if a selected element is in one of your assigned scopes.
Table 26-2 identifies the tasks that you can perform if a selected element is in one of your assigned scopes.
By default, users with the Administrator role have access to all managed elements. To change the Administrator user scope, see the topic on device scopes in the Cisco Prime Network 3.10 Administrator Guide.
Table 26-1 Default Permission/Security Level Required for Viewing GGSN, GTPU, and APN Properties - Element Not in User's Scope
|
|
|
|
|
|
|
Viewing GGSN properties |
— |
— |
— |
— |
X |
Viewing additional characteristics of a GGSN |
— |
— |
— |
— |
X |
Working with GGSN commands |
— |
— |
— |
— |
X |
Viewing GTPU properties |
— |
— |
— |
— |
X |
Working with GTPU commands |
— |
— |
— |
— |
X |
Viewing APN properties |
— |
— |
— |
— |
X |
Viewing additional characteristics of an APN |
— |
— |
— |
— |
X |
Working with APN commands |
— |
— |
— |
— |
X |
Viewing SAE-GW properties |
— |
— |
— |
— |
X |
Viewing P-GW properties |
— |
— |
— |
— |
X |
Working with P-GW commands |
— |
— |
— |
— |
X |
Viewing S-GW properties |
— |
— |
— |
— |
X |
Working with S-GW commands |
— |
— |
— |
— |
X |
Viewing GTPP properties |
— |
— |
— |
— |
X |
Viewing additional characteristics of a GTPP |
— |
— |
— |
— |
X |
Working with GTPP commands |
— |
— |
— |
— |
X |
Viewing EGTP properties |
— |
— |
— |
— |
X |
Working with EGTP commands |
— |
— |
— |
— |
X |
Viewing operator policies |
— |
— |
— |
— |
X |
Viewing APN remaps |
— |
— |
— |
— |
X |
Viewing APN profiles |
— |
— |
— |
— |
X |
Viewing additional characteristics of an APN profiles |
— |
— |
— |
— |
X |
Viewing active charging services (ACS) |
— |
— |
— |
— |
X |
Working with ACS commands |
— |
— |
— |
— |
X |
Viewing QCI-QoS mapping |
— |
— |
— |
— |
X |
Viewing the Layer 2 Tunnel Access Concentrator Configurations |
— |
— |
— |
— |
X |
Viewing the HSGW configuration |
— |
— |
— |
— |
X |
Viewing the Home Agent configuration |
— |
— |
— |
— |
X |
Viewing the Foreign Agent configuration details |
— |
— |
— |
— |
X |
Viewing the ePDG configuration details |
— |
— |
— |
— |
X |
Viewing the PDSN configuration details |
— |
— |
— |
— |
X |
Viewing the Local Mobility Anchor configuration |
— |
— |
— |
— |
X |
Table 26-2 Default Permission/Security Level Required for Viewing GGSN, GTPU, and APN Properties - Element in User's Scope
|
|
|
|
|
|
|
Viewing GGSN properties |
X |
X |
X |
X |
X |
Viewing additional characteristics of a GGSN |
X |
X |
X |
X |
X |
Working with GGSN commands |
— |
— |
— |
X |
X |
Viewing GTPU properties |
X |
X |
X |
X |
X |
Working with GTPU commands |
— |
— |
— |
X |
X |
Viewing APN properties |
X |
X |
X |
X |
X |
Viewing additional characteristics of an APN |
X |
X |
X |
X |
X |
Working with APN commands |
— |
— |
— |
X |
X |
Viewing SAE-GW properties |
X |
X |
X |
X |
X |
Viewing P-GW properties |
X |
X |
X |
X |
X |
Working with P-GW commands |
— |
— |
— |
X |
X |
Viewing S-GW properties |
X |
X |
X |
X |
X |
Working with S-GW commands |
— |
— |
— |
X |
X |
Viewing GTPP properties |
X |
X |
X |
X |
X |
Viewing additional characteristics of a GTPP |
X |
X |
X |
X |
X |
Working with GTPP commands |
— |
— |
— |
X |
X |
Viewing EGTP properties |
X |
X |
X |
X |
X |
Working with EGTP commands |
— |
— |
— |
X |
X |
Viewing operator policies |
X |
X |
X |
X |
X |
Viewing APN remaps |
X |
X |
X |
X |
X |
Viewing APN profiles |
X |
X |
X |
X |
X |
Viewing additional characteristics of an APN profiles |
X |
X |
X |
X |
X |
Viewing active charging services (ACS) |
X |
X |
X |
X |
X |
Working with ACS commands |
— |
— |
— |
X |
X |
Viewing QCI-QoS mapping |
X |
X |
X |
X |
X |
Viewing the Layer 2 Tunnel Access Concentrator Configurations |
X |
X |
X |
X |
X |
Viewing the HSGW configuration |
X |
X |
X |
X |
X |
Viewing the Home Agent configuration |
X |
X |
X |
X |
X |
Viewing the Foreign Agent configuration details |
X |
X |
X |
X |
X |
Viewing the ePDG configuration details |
X |
X |
X |
X |
X |
Viewing the PDSN configuration details |
X |
X |
X |
X |
X |
Viewing the Local Mobility Anchor configuration |
X |
X |
X |
X |
X |
GPRS/UMTS Networks - An Overview
General Packet Radio Service (GPRS) and Universal Mobile Telecommunication System (UMTS) are evolutions of Global System for Mobile Communication (GSM) networks.
GPRS is a 2.5G mobile communications technology that enables mobile wireless service providers to offer their mobile subscribers packet-based data services over GSM networks. UMTS is a 3G mobile communications technology that provides wideband code division multiple access (CDMA) radio technology. Figure 26-1 shows a basic GPRS/UMTS network topology.
Figure 26-1 Basic GPRS/UMTS Network Topology
The GPRS/UMTS packet core comprises two major network elements:
• Gateway GPRS support node (GGSN)—A gateway that provides mobile cell phone users access to a Packet Data Network (PDN) or specified private Internet Protocol (IP) networks.
Gateway GPRS support node (GGSN)—A gateway that provides mobile cell phone users access to a Packet Data Network (PDN) or specified private Internet Protocol (IP) networks.
• Serving GPRS support node (SGSN)—Connects the radio access network (RAN) to the GPRS/UMTS core and tunnels user sessions to the GGSN. The SGSN sends data to and receives data from mobile stations, and maintains information about the location of a mobile station (MS). The SGSN communicates directly with the MS and the GGSN.
Serving GPRS support node (SGSN)—Connects the radio access network (RAN) to the GPRS/UMTS core and tunnels user sessions to the GGSN. The SGSN sends data to and receives data from mobile stations, and maintains information about the location of a mobile station (MS). The SGSN communicates directly with the MS and the GGSN.
PDNs are associated with Access Point Names (APNs) configured on the system. Each APN consists of a set of parameters that dictate how subscriber authentication and IP address assignment is to be handled for that APN.
Prime Network Vision allows you to configure the mobile technologies by using commands and also view the properties configured for the mobile technologies. Figure 26-2 shows an example of the Inventory window with the mobile technology nodes/containers under the Mobile context.
From Prime Network 3.9, the mobile technologies are supported on Cisco Aggregation Service Router (ASR) 5000 series mobile gateways.
Figure 26-2 Mobile Technology Nodes in Logical Inventory
Working With GPRS/UMTS Network Technologies
The following topics explain how to work with GPRS/UMTS network technologies in Prime Network Vision:
• Working with GGSN
Working with GGSN
• Working with GTPU
Working with GTPU
• Working with APN
Working with APN
• Working with GTPP
Working with GTPP
• Working with EGTP
Working with EGTP
Working with GGSN
The GGSN works in conjunction with SGSNs within the network to perform the following functions:
• Establish and maintain subscriber Internet Protocol (IP) or Point-to-Point Protocol (PPP) type Packet Data Protocol (PDP) contexts originated by either the mobile or the network.
Establish and maintain subscriber Internet Protocol (IP) or Point-to-Point Protocol (PPP) type Packet Data Protocol (PDP) contexts originated by either the mobile or the network.
• Provide charging detail records (CDRs) to the charging gateway ((CG), also known as the Charging Gateway Function (CGF)).
Provide charging detail records (CDRs) to the charging gateway ((CG), also known as the Charging Gateway Function (CGF)).
• Route data traffic between the subscriber's Mobile Station (MS) and a PDN such as the Internet or an intranet.
Route data traffic between the subscriber's Mobile Station (MS) and a PDN such as the Internet or an intranet.
In addition, to providing basic GGSN functionality as described above, the system can be configured to support Mobile IP and/or Proxy Mobile IP data applications in order to provide mobility for subscriber IP PDP contexts. When supporting these services, the system can be configured to function as a GGSN and Foreign Agent (FA), a stand-alone Home Agent (HA), or a GGSN, FA, and HA simultaneously within the carrier's network.
The following topics explain how to work with GGSN in Prime Network Vision:
• Viewing GGSN Properties
Viewing GGSN Properties
• Viewing Additional Characteristics of a GGSN
Viewing Additional Characteristics of a GGSN
• GGSN Commands
GGSN Commands
Viewing GGSN Properties
Prime Network Vision displays the GGSNs in a GGSN container under the Mobile node in the logical inventory. The icon used for representing GGSNs in the logical inventory is explained in Logical Inventory Icons.
To view GGSN properties:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > GGSN Container.
In the logical inventory window, choose Logical Inventory > Context > Mobile > GGSN Container.
Prime Network Vision displays the list of GGSNs configured under the container. You can view the individual GGSN details from the table on the right pane or by choosing Logical Inventory > Context > Mobile > GGSN Container > GGSN.
Table 26-3 describes the details available for each GGSN.
Table 26-3 GGSN Properties in Logical Inventory
|
|
|
Service Name |
The name of the GGSN service. |
Status |
The status of the GGSN service. Value could be Unknown, Running, or Down. |
PLMN Policy |
The PLMN policy for handling communications from SGSNs that are not configured to communicate with. |
Newcall Policy |
Specifies whether to accept or reject a new incoming call. |
Authentication Server Timeout |
The code used by the GGSN as a response message if communication with an authentication server times out. Value could be System Failure or User Authentication Failed. |
Accounting Server Timeout |
The code used by the GGSN as a response message if communication with an accounting server times out. Value could be System Failure or No Resouces. |
GTPU |
The GTPU that is associated with the GGSN and manages the GTP messages between GGSN and a radio access network equipment (RNC). |
Accounting Context |
The context that processes accounting for PDP contexts handled by the GGSN service. |
Local IP Address |
The local IP address bounded with the GGSN service. |
If the GGSN is associated with SGSNs and Public Land Mobile Networks (PLMNs), you can view the details from the respective tabs for that GGSN.
Table 26-4 describes the SGSN and PLMN information associated with the GGSN.
Table 26-4 SGSN and PLMN information for a GGSN
|
|
|
SGSNs |
IP Address |
The IP address of the SGSN. |
Subnet Mask |
The subnet mask of the SGSN. |
PLMN ID |
The PLMN ID associated with the SGSN. |
MCC |
The mobile country code (MCC) portion of the PLMN. |
MNC |
The mobile network code (MNC) portion of the PLMN. |
PLMN Foreign |
Indicates whether the SGSN belongs to a home or foreign PLMN. This field is available only if MCC and MNC are not available. |
Reject Foreign Subscriber |
Specifies whether to accept or reject foreign subscriber. Value could be True or False. |
RAT Type |
The type of radio access technology (RAT) that is used for communication. |
Description |
The description of the SGSN entry in the GGSN service. |
PLMNs |
PLMN ID |
The ID of the PLMN associated with the GGSN. |
Primary |
Indicates whether the PLMN ID is the primary PLMN ID for the GGSN. Value could be True or False. When multiple PLMN IDs are configured, the one configured as primary is used for the Authentication, Authorization, and Accounting (AAA) attribute. |
Viewing Additional Characteristics of a GGSN
To view additional characteristics of a GGSN:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Mobile > GGSN Container >GGSN.
In the logical inventory window, choose Logical Inventory > Mobile > GGSN Container >GGSN.
Step 3  Expand the GGSN node. The following list of characteristics configured for the GGSN are displayed:
Expand the GGSN node. The following list of characteristics configured for the GGSN are displayed:
• Charging Characteristics
Charging Characteristics
• Timers And QoS
Timers And QoS
Step 4  Choose Charging Characteristics to view the properties on the right pane. See Table 26-5 for more details on the charging characteristics configured for the GGSN.
Choose Charging Characteristics to view the properties on the right pane. See Table 26-5 for more details on the charging characteristics configured for the GGSN.
Table 26-5 GGSN Charging Characteristics
|
|
|
|
|
Profile No |
Type of billing. For example: • 1—Hot billing 1—Hot billing • 2—Flat billing 2—Flat billing • 4—Prepaid billing 4—Prepaid billing • 8—Normal billing 8—Normal billing All other profiles from 0 - 15 are customized billing types. |
Buckets |
Denotes container changes in the GGSN Call Detail Record (GCDR). |
Prepaid |
Prepaid type, which could be Prohibited or Use-rulebase-configuration. |
Down Link Octets |
Downlink traffic volume of the bucket. |
Uplink Octets |
Uplink traffic volume of the bucket. |
Total Octets |
Total traffic volume of the bucket. |
|
|
Profile No |
Type of billing. |
Time1, Time2, and so on |
First time-of-day time values, and so on, to close the current statistics container. |
|
|
Profile No |
Type of billing. |
No. of SGSNs |
Number of SGSN changes (inter-SGSN switchovers) resulting in a new Routing Area Identity (RAI) that can occur before closing an accounting record. |
Interval |
Normal time duration that must elapse before closing an accounting record. |
Down Link Octets |
Downlink traffic volume reached within the time interval. |
Up Link Octets |
Uplink traffic volume reached within the time interval. |
Total Octets |
Total traffic volume reached within the time interval. |
Step 5  Under the GGSN node, choose Timers and QoS to view the properties on the right pane. See Table 26-6 for more details on the Timers and QoS parameters configured for the GGSN.
Under the GGSN node, choose Timers and QoS to view the properties on the right pane. See Table 26-6 for more details on the Timers and QoS parameters configured for the GGSN.
Table 26-6 GGSN Timers and QoS
|
|
|
Retransmission Timeout |
Timeout, in seconds, for retransmission of GTP control packets. |
Max Retransmissions |
Maximum retries for transmitting GTP control packets. |
Setup Timeout |
Maximum time, in seconds, allowed for session setup. |
Echo Interval |
Echo interval, in seconds, for GTP. |
Guard Interval |
Interval, in seconds, for which the GGSN maintains responses sent to SGSN. This optimizes the handling of retransmitted messages. |
QCI to DSCP Mapping |
QoS class index |
A set of transport characteristics used to differentiate various packet flows. |
DSCP |
Differentiated Services Code Point (DSCP), a mechanism for classifying and managing network traffic and providing QoS. |
QCI & ARP DSCP Mapping |
QoS class index |
A set of transport characteristics used to differentiate various packet flows. |
Allocation retention priority |
The priority of allocation and retention of the service data flow. This parameter allows prioritizing allocation of resources during bearer establishment and modification. During network traffic congestions, a lower ARP flow is dropped to free up the capacity. |
DSCP |
A mechanism for classifying and managing network traffic and providing QoS. |
GGSN Commands
The following commands can be launched from the inventory by right-clicking a GGSN and choosing GGSN > Commands > Configuration. Before executing any commands, you can preview them and view the results. If desired, you can also schedule the commands. To find out if a device supports these commands, see the Cisco Prime Network 3.10 Supported Cisco VNEs.
Note  You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
Table 26-7 GGSN Commands
|
|
|
|
Create PLMN Identifier |
Right-click on a GGSN group > Commands > Configuration |
Use this command to create a PLMN Identifier. |
Create SGSN |
Use this command to create an SGSN. |
Delete GGSN |
Use this command to delete a GGSN profile. |
Modify GGSN |
Use this command to modify a GGSN profile details. |
Working with GTPU
The GGSN communicates with SGSNs on a Public Land Mobile Network (PLMN) using the GPRS Tunneling Protocol (GTP). The signaling or control aspect of this protocol is referred to as the GTP Control Plane (GTPC) while the encapsulated user data traffic is referred to as the GTP User Plane (GTPU). GTPU is used for transferring user data in separated tunnels for each PDP context.
You can configure various parameters for a GTPU using the configuration commands in Prime Network Vision. You can view the configured parameters for a GTPU in the logical inventory.
The following topics explain how to work with GTPU in Prime Network Vision:
• Viewing GTPU Properties
Viewing GTPU Properties
• GTPU Commands
GTPU Commands
Viewing GTPU Properties
Prime Network Vision displays the GTPUs in a GTPU container under the Mobile node in the logical inventory. The icon used for representing GTPUs in the logical inventory is explained in Logical Inventory Icons.
To view GTPU properties:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > GTPU Container.
In the logical inventory window, choose Logical Inventory > Context > Mobile > GTPU Container.
Prime Network Vision displays the list of GTPUs configured under the container. You can view the individual GTPU details from the table on the right pane or by choosing Logical Inventory >Context > Mobile > GTPU Container > GTPU.
Table 26-8 describes the details available for each GTPU.
Table 26-8 GTPU Properties in Logical Inventory
|
|
|
Service Name |
The name of the GTPU service. |
State |
The status of the GTPU service. Status could be Unknown, Running, or Down. |
Max Retransmissions |
The maximum limit for GTPU echo retransmissions. Default value is 4. |
Retransmission Timeout |
The timeout in seconds for GTPU echo retransmissions. Default value is 5 Secs. |
Echo Interval |
The rate at which the GTPU echo packets are sent. |
IPSEC Tunnel Idle Timeout |
The IPSec tunnel idle timeout after which IPSec tunnel deletion is triggered. Default value is 60 Secs. |
Allow Error Indication |
Specifies whether error indication is dropped or sent without IPSec tunnel. Default value is Disabled. |
Include UDP Port Ext Hdr |
Specifies whether to include an extension header in the GTPU packet for error indication messages. Default value is False. |
IP Address |
The list of IP addresses configured on the GTPU. The IP addresses are available only when configured for the GTPU. |
GTPU Commands
The following commands can be launched from the inventory by right-clicking a GTPU and choosing Commands > Configuration. Before executing any commands, you can preview them and view the results. If desired, you can also schedule the commands. To find out if a device supports these commands, see the Cisco Prime Network 3.10 Supported Cisco VNEs.
Note  You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
Table 26-9 GTPU Commands
|
|
|
|
Create GTPU Bind IP Address |
Right-click on a GTPU defined > Commands > Configuration |
Use this command to create a bind IP address for GTPU. |
Modify GTPU Bind IP Address |
Select the GTPU node > right-click on an IP address in the content pane > Commands > Configuration |
Use this command to modify the Bind IP address for GTPU. |
Delete GTPU Bind IP Address |
Use this command to delete the Bind IP address for GTPU. |
Delete GTPU |
Right-click on a GTPU defined > Commands > Configuration |
Use this command to delete a GTPU group. |
Modify GTPU |
Use this command to modify a GTPU group. |
Working with APN
APN is the access point name that is configured in the GGSN configurations. The GGSN's APN support offers the following benefits:
• Extensive parameter configuration flexibility for the APN.
Extensive parameter configuration flexibility for the APN.
• Extensive QoS support.
Extensive QoS support.
• Virtual APNs to allow differentiated services within a single APN. The APN that is supplied by the mobile station is evaluated by the GGSN in conjunction with multiple configurable parameters. Then the GGSN selects an APN configuration based on the supplied APN and those configurable parameters.
Virtual APNs to allow differentiated services within a single APN. The APN that is supplied by the mobile station is evaluated by the GGSN in conjunction with multiple configurable parameters. Then the GGSN selects an APN configuration based on the supplied APN and those configurable parameters.
• Traffic policing that governs the subscriber traffic flow if it violates or exceeds configured peak or committed data rates. The traffic policing attributes represent a QoS data rate limit configuration for both uplink and downlink directions.
Traffic policing that governs the subscriber traffic flow if it violates or exceeds configured peak or committed data rates. The traffic policing attributes represent a QoS data rate limit configuration for both uplink and downlink directions.
Up to 1024 APNs can be configured in the GGSN. An APN may be configured for any type of PDP context, i.e., PPP, IPv4, IPv6 or both IPv4 and IPv6.
Many parameters can be configured independently for each APN on the device. They are categorized as given below:
• Accounting—Various parameters regarding accounting possibilities, such as, charging characteristics, accounting mode (RADIUS server-based accounting, GTPP-based accounting, and so on.)
Accounting—Various parameters regarding accounting possibilities, such as, charging characteristics, accounting mode (RADIUS server-based accounting, GTPP-based accounting, and so on.)
• Authentication—Various parameters regarding authentication, such as, protocols used, like, Challenge Handshake Authentication Protocol (CHAP), Password Authentication Protocol (PAP), or none, default username/password, server group to use, and limit for number of PDP contexts.
Authentication—Various parameters regarding authentication, such as, protocols used, like, Challenge Handshake Authentication Protocol (CHAP), Password Authentication Protocol (PAP), or none, default username/password, server group to use, and limit for number of PDP contexts.
• Enhanced Charging—Name of rulebase to use, which holds the enhanced charging configuration (for example, eG-CDR variations, charging rules, prepaid/postpaid options, etc.).
Enhanced Charging—Name of rulebase to use, which holds the enhanced charging configuration (for example, eG-CDR variations, charging rules, prepaid/postpaid options, etc.).
• IP: Method for IP address allocation (e.g., local allocation by GGSN, Mobile IP, Dynamic Host Control Protocol (DHCP), DHCP relay, etc.). IP address ranges, with or without overlapping ranges across APNs.
IP: Method for IP address allocation (e.g., local allocation by GGSN, Mobile IP, Dynamic Host Control Protocol (DHCP), DHCP relay, etc.). IP address ranges, with or without overlapping ranges across APNs.
• Tunneling: PPP may be tunneled with L2TP. IPv4 may be tunneled with GRE, IP-in-IP or L2TP. Load-balancing across multiple tunnels. IPv6 is tunneled in IPv4. Additional tunneling techniques, such as, IPsec and VLAN tagging may be selected by the APN, but are configured in the GGSN independently from the APN.
Tunneling: PPP may be tunneled with L2TP. IPv4 may be tunneled with GRE, IP-in-IP or L2TP. Load-balancing across multiple tunnels. IPv6 is tunneled in IPv4. Additional tunneling techniques, such as, IPsec and VLAN tagging may be selected by the APN, but are configured in the GGSN independently from the APN.
• QoS: IPv4 header ToS handling. Traffic rate limits for different 3GPP traffic classes. Mapping of R98 QoS attributes to work around particular handset defections. Dynamic QoS renegotiation (described elsewhere).
QoS: IPv4 header ToS handling. Traffic rate limits for different 3GPP traffic classes. Mapping of R98 QoS attributes to work around particular handset defections. Dynamic QoS renegotiation (described elsewhere).
You can configure the APN parameters using Prime Network Vision. You can view the configured parameters for an APN in the logical inventory. After an APN is determined by the GGSN, the subscriber may be authenticated/authorized with an AAA server. The GGSN allows the AAA server to return Vendor Specific Attributes (VSAs) that override any or all of the APN configuration. This allows different subscriber tier profiles to be configured in the AAA server, and passed to the GGSN during subscriber authentication/authorization.
The following topics explain how to work with APN in Prime Network Vision:
• Viewing APN Properties
Viewing APN Properties
• Viewing Additional Characteristics of an APN
Viewing Additional Characteristics of an APN
• APN Commands
APN Commands
Viewing APN Properties
Prime Network Vision displays the APNs in an APN container under the Mobile node in the logical inventory. You can also view additional characteristics configured on the APN as explained in Viewing Additional Characteristics of an APN. The icon used for representing APNs in the logical inventory is explained in Logical Inventory Icons.
To view APN properties:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory >Context > Mobile > APN Container >APN.
In the logical inventory window, choose Logical Inventory >Context > Mobile > APN Container >APN.
Table 26-10 describes the information that is available for the APN. The information that is displayed depends on the configuration of the APN.
Table 26-10 APN Properties in Logical Inventory
|
|
|
APN Name |
The APN name. |
Accounting Mode |
The accounting protocol in use in the APN. Values are GTPP (GPRS Tunneling Protocol Prime), RADIUS (Remote Authentication Dial In User Service), or None. |
Selection Mode |
The selection mode in use in the APN. Selection mode indicates the origin of the requested APN and whether or not the Home Location Register (HLR) has verified the user subscription. |
L3 to L2 Address Policy |
The layer 2 to layer 3 IP address allocation or validation policy. |
Allocation Type |
The method by which the APN obtains IP addresses for PDP contexts. |
IP Header Compression |
IP packet header compression parameters for the APN. |
New Call Policy |
Specifies whether to accept or reject a new incoming call in case of duplicate session calls with a request for same IP address. |
Step 3  To view additional details configured for the APN, use the following tabs:
To view additional details configured for the APN, use the following tabs:
• Virtual APNs—A virtual APN is a non-physical entity that represents an access point that does not itself provide direct access to a real target network. A virtual APN can be used to consolidate access to multiple, physical target networks through a single access point.
Virtual APNs—A virtual APN is a non-physical entity that represents an access point that does not itself provide direct access to a real target network. A virtual APN can be used to consolidate access to multiple, physical target networks through a single access point.
• QCI to DSCP Mapping—Shows the mapping between QoS Class Indices (QCI) to Differentiated Services Code Point (DSCP).
QCI to DSCP Mapping—Shows the mapping between QoS Class Indices (QCI) to Differentiated Services Code Point (DSCP).
• QCI & ARP DSCP Mapping—Shows the mapping between QCI and Allocation/Retention Priority (ARP) to DSCP.
QCI & ARP DSCP Mapping—Shows the mapping between QCI and Allocation/Retention Priority (ARP) to DSCP.
• QoS Downlink Traffic Policing—Shows the attributes that represent QoS data rate limit configuration for downlink direction within the APN profile.
QoS Downlink Traffic Policing—Shows the attributes that represent QoS data rate limit configuration for downlink direction within the APN profile.
• QoS Uplink Traffic Policing—Shows the attributes that represent QoS data rate limit configuration for uplink direction within the APN profile.
QoS Uplink Traffic Policing—Shows the attributes that represent QoS data rate limit configuration for uplink direction within the APN profile.
Table 26-11 Additional Configuration Details for APN
|
|
|
Virtual APNs |
Preference |
Specifies the order in which the referenced APNs are compared by the system. Can be configured to any integer value from 1 (highest priority) to 1000 (lowest priority). |
APN |
Specifies the name of an alternative APN configured on the system that is to be used for PDP contexts with matching properties. Value can be from 1 to 62, alpha and/or numeric characters, and is not case-sensitive. It may also contain dots ( . ) and/or dashes (- ). |
Rule Definition |
The virtual APN rule definition can be one of the following: • access-gw-address—Specifies the access gateway (SGSN/SGW/Others) address for the virtual APN. The IP address can be an IPv4 or IPv6 address in decimal notation. IPv6 also supports :: notation for the IP address. access-gw-address—Specifies the access gateway (SGSN/SGW/Others) address for the virtual APN. The IP address can be an IPv4 or IPv6 address in decimal notation. IPv6 also supports :: notation for the IP address. • bearer-access-service—Specifies the bearer access service name for the virtual APN. bearer-access-service—Specifies the bearer access service name for the virtual APN. • service name—Specifies the service name. Service name is unique across all the contexts. Value is a string of size 1 to 63. service name—Specifies the service name. Service name is unique across all the contexts. Value is a string of size 1 to 63. • cc-profile—Specifies the APN for charging characteristics (CC) profile index. Value is an integer from 1 to 15. cc-profile—Specifies the APN for charging characteristics (CC) profile index. Value is an integer from 1 to 15. • Domain name—Specifies the subscriber's domain name (realm). Domain name can be from 1 to 79 alpha and/or numeric characters. Domain name—Specifies the subscriber's domain name (realm). Domain name can be from 1 to 79 alpha and/or numeric characters. • MCC—Specifies the MCC portion of the PLMN identifier. Value is an integer between 100 to 999. MCC—Specifies the MCC portion of the PLMN identifier. Value is an integer between 100 to 999. • MNC—Specifies the MNC portion of the PLMN identifier. Value is an integer between 100 to 999. MNC—Specifies the MNC portion of the PLMN identifier. Value is an integer between 100 to 999. • msisdn-range—Specifies the APN for this MSISDN range. The starting and ending values of the range is a string of size 2 to 15 with values between 00 and 999999999999999. msisdn-range—Specifies the APN for this MSISDN range. The starting and ending values of the range is a string of size 2 to 15 with values between 00 and 999999999999999. • Rat-Type—Specifies the rat-type option, which could be gan, geran, hspa, utran, or wlan. Rat-Type—Specifies the rat-type option, which could be gan, geran, hspa, utran, or wlan. • Roaming mode—Specifies the roaming mode, which could be Home, Visiting, or Roaming. Roaming mode—Specifies the roaming mode, which could be Home, Visiting, or Roaming. |
QCI to DSCP Mapping |
QoS class index |
Denotes a set of transport characteristics used to differentiate various packet flows. |
DSCP |
Denotes a mechanism for classifying and managing network traffic and providing QoS. |
QCI & ARP DSCP Mapping |
QoS class index |
Denotes a set of transport characteristics used to differentiate various packet flows. |
Allocation retention priority |
Indicates the priority of allocation and retention of the service data flow. This parameter allows prioritizing allocation of resources during bearer establishment and modification. During network traffic congestions, a lower ARP flow is dropped to free up the capacity. |
DSCP |
Denotes a mechanism for classifying and managing network traffic and providing QoS. |
QoS Downlink Traffic Policing |
QCI |
A scalar that denotes a set of transport characteristics and used to infer nodes specific parameters that control packet forwarding treatment. |
Peak Data Rate |
The peak data rate allowed, in bytes, for the downlink direction and QoS traffic class. |
Committed Data Rate |
The committed data rate allowed, in bytes, for the downlink direction and QoS traffic class. |
Negotiate Limit |
Indicates whether negotiation limit is enabled or disabled for the downlink direction and Qos traffic class. |
Rate Limit |
Indicates whether the rate limit is enabled or disabled for the downlink direction and Qos traffic class. |
Burst Size Auto Readjust |
Indicates whether the auto readjustment of burst size is enabled or disabled. This parameter is used in dynamic burst size calculation, for traffic policing, at the time of PDP activation of modification. |
Burst Size Auto Readjust Duration |
The burst size readjustment duration in seconds. This parameter indicates the number of seconds that the dynamic burst size calculation will last for. This allows the traffic to be throttled at the negotiated rates. |
Peak Burst Size (bytes) |
The peak burst size allowed, in bytes, for the downlink direction and QoS class. |
Guaranteed Burst Size (bytes) |
The guaranteed burst size allowed, in bytes, for the downlink direction and QoS class. |
Exceed Action |
The action to be taken on packets that exceed the committed data rate, but do not violate the peak data rate. The action could be one of the following: • Drop Drop • Lower IP Precedence Lower IP Precedence • Transmit Transmit |
Violate Action |
The action to be taken on packets that exceed both committed and peak data rates. The action could be one of the following: • Drop Drop • Lower IP Precedence Lower IP Precedence • Shape Shape • Transmit Transmit |
QoS Uplink Traffic Policing |
QCI |
A scalar that denotes a set of transport characteristics and used to infer nodes specific parameters that control packet forwarding treatment. |
Peak Data Rate |
The peak data rate allowed, in bytes, for the uplink direction and QoS traffic class. |
Committed Data Rate |
The committed data rate allowed, in bytes, for the uplink direction and QoS traffic class. |
Negotiate Limit |
Indicates whether negotiation limit is enabled or disabled for the uplink direction and Qos traffic class. |
Rate Limit |
Indicates whether the rate limit is enabled or disabled for the uplink direction and Qos traffic class. |
Burst Size Auto Readjust |
Indicates whether the auto readjustment of burst size is enabled or disabled. This parameter is used in dynamic burst size calculation, for traffic policing, at the time PDP. |
Burst Size Auto Readjust Duration |
The burst size readjustment duration in seconds. This parameter indicates the number of seconds that the dynamic burst size calculation will last for. This allows the traffic to be throttled at the negotiated rates. |
Peak Burst Size (bytes) |
The peak burst size allowed, in bytes, for the uplink direction and QoS class. |
Guaranteed Burst Size (bytes) |
The guaranteed burst size allowed, in bytes, for the uplink direction and QoS class. |
Exceed Action |
The action to be taken on packets that exceed the committed data rate, but do not violate the peak data rate. The action could be one of the following: • Drop Drop • Lower IP Precedence Lower IP Precedence • Transmit Transmit |
Violate Action |
The action to be taken on packets that exceed both committed and peak data rates. The action could be one of the following: • Drop Drop • Lower IP Precedence Lower IP Precedence • Shape Shape • Transmit Transmit |
Viewing Additional Characteristics of an APN
To view additional characteristics of an APN:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > APN Container >APN.
In the logical inventory window, choose Logical Inventory > Context > Mobile > APN Container >APN.
Step 3  Expand the APN node. The following list of characteristics configured for the APN are displayed:
Expand the APN node. The following list of characteristics configured for the APN are displayed:
– Charging Characteristics—Charging characteristics configured on the APN for different subscribers.
Charging Characteristics—Charging characteristics configured on the APN for different subscribers.
– DHCP—Dynamic Host Control Protocol (DHCP) parameter configured, if the APN supports dynamic address assignment for PDP contexts.
DHCP—Dynamic Host Control Protocol (DHCP) parameter configured, if the APN supports dynamic address assignment for PDP contexts.
– GSM-QoS—Represents the negotiated QoS attribute reliability class based on the configuration provided for service data unit (SDU) error ratio and residual bit error rate (BER) attributes in the APN.
GSM-QoS—Represents the negotiated QoS attribute reliability class based on the configuration provided for service data unit (SDU) error ratio and residual bit error rate (BER) attributes in the APN.
– IP Parameters—Represents the APN parameters related to IP.
IP Parameters—Represents the APN parameters related to IP.
– IPv6—Represents IPv6 configurations and related services for the APN.
IPv6—Represents IPv6 configurations and related services for the APN.
– Mediation Device—Represents the mediation device used by the APN for communication with the subscriber.
Mediation Device—Represents the mediation device used by the APN for communication with the subscriber.
– Mobile IP—Represents mobile IP configuration of the APN.
Mobile IP—Represents mobile IP configuration of the APN.
– Net BIOS—Represents the NetBIOS server configuration used by the APN.
Net BIOS—Represents the NetBIOS server configuration used by the APN.
– PDP Contexts Parameters—Represents the PDP contexts supported by the APN.
PDP Contexts Parameters—Represents the PDP contexts supported by the APN.
– PPP Profile—Represents the PPP profile used by the APN.
PPP Profile—Represents the PPP profile used by the APN.
– RADIUS—Represents the APN parameters related to communication with the RADIUS server.
RADIUS—Represents the APN parameters related to communication with the RADIUS server.
– Timeout—Represents the timeout parameters of the APN.
Timeout—Represents the timeout parameters of the APN.
– Tunnel Parameters—Represents the parameters configured for tunneling between the GGSN and an external gateway for the APN.
Tunnel Parameters—Represents the parameters configured for tunneling between the GGSN and an external gateway for the APN.
– DNS Configuration—Represents the Domain Name System (DNS) settings configured on the APN.
DNS Configuration—Represents the Domain Name System (DNS) settings configured on the APN.
Step 4  Click each of one of these characteristics to view its properties on the right pane. See Table 26-12 for more details on the properties of each characteristics configured for the APN.
Click each of one of these characteristics to view its properties on the right pane. See Table 26-12 for more details on the properties of each characteristics configured for the APN.
Table 26-12 APN Characteristics
|
|
|
Charging Characteristics |
Home Bit Behavior |
The behavior bit for charging a home subscriber. |
Home Profile |
The profile index for a home subscriber. |
Roaming Bit Behavior |
The behavior bit for charging a roaming subscriber. |
Roaming Profile |
The profile index for a roaming subscriber. |
Visiting Bit Behavior |
The behavior bit for charging a visiting subscriber. |
Visiting Profile |
The profile index for a visiting subscriber. |
All Bit Behavior |
The behavior bit for charging all subscribers. This value is used only if all subscribers are configured to use the same charging characteristics. This value is overridden by the behavior bit set for a subscriber type. |
All Profile |
The profile index for all subscribers. |
Use GGSN |
The type of the subscriber using the charging characteristics configured on the APN. Value could be Home, Roaming, Visitor, or None. None indicates that the subscriber is using the charging characteristics from the SGSN. |
Use RADIUS Returned |
Specifies whether the GGSN accepts charging characteristics returned from the RADIUS server for all subscribers for the APN. Value could be True or False. |
DHCP |
Lease Expiration Policy |
The action taken when leases for IP addresses assigned to PDP contexts that are facilitated by the APN, are about to expire. For example, auto renew. |
GSM-QoS |
SDU Error Ratio Code |
The SDU error ratio code based on which the negotiation of QoS attribute reliability class needs to be configured on the APN. Value is an integer between the range 1 and 7. Each code has an assigned value. |
Residual BER Code |
The residual bit error rate (BER) based on which the negotiation of QoS attribute reliability class needs to be configured on the APN. This value is specified if the SDU error ratio code is 1, 2, 3, or 7. Residual BER code is an integer in the range 1 and 9. Each code has an assigned value. |
IP Parameters |
In Access Group |
The name of the IPv4/IPv6 access group for the APN when configured for inbound traffic. |
Out Access Group |
The name of the IPv4/IPv6 access group for the APN when configured for outbound traffic. |
Local Address |
The static local IP address assigned to the APN. |
Next Hop Gateway Address |
The IP address of the next hop gateway for the APN. This parameter is available only if it is configured on the APN. |
Is Discard Enabled |
Specifies whether multicast discard is enabled or disabled. Value could be True or False. |
IPv6 |
Inbound Access Group Name |
The name of the IPv6 access group for the APN when configured for inbound traffic. |
Outbound Access Group Name |
The name of the IPv6 access group for the APN when configured for outbound traffic. |
Router Advertisement Interval |
The time interval (in milliseconds) the initial IPv6 router advertisement is sent to the mobile node. Value is an integer in the range 100 and 16,000. Smaller the advertisement interval greater is the chance of the router being discovered quickly. |
Router Advertisement Number |
The number of initial IPv6 router advertisements sent to the mobile node. Value is an integer in the range of 1 and 16. |
Prefix Pool Name |
The name of the IPv6 address prefix pool configured for the subscriber. You can configure upto a maximum of four pools per subscriber. |
Egress Address Filtering |
Specifies whether filtering of packets not meant for the mobile interface, is enabled or disabled. |
Mediation Device |
Mediation Accounting Enabled |
Indicates whether mediation accounting is enabled or disabled. |
No Early PDUs |
Indicates whether protocol data units (PDUs) must be delayed or not until a response to the GGSN's accounting start request is received from the mediation device. If No Early PDUs is `true', the chassis does not send any uplink or downlink data from or to a MS, until it receives a command from the mediation device. |
No Interims |
Indicates whether radius interim updates are sent to the mediation device or not for the APN for radius accounting. |
Delay GTP Response |
Indicates whether the GTP response must be delayed or not. If this value is `true', the GTP response is delayed and is sent to the SGSN only if the AAA server is up. If the value is `false', the subscriber will be connected to the SGSN even if the AAA server is down. |
Mobile IP |
Home Agent |
The IP address of the home agent (HA) used by the current APN to facilitate subscriber mobile IP sessions. |
Mobile Node Home Agent SPI |
The mobile node Security Parameter Index (SPI) configured for the APN. Value is an integer between 256 and 4294967295. |
Mobile Node Home Agent Hash Algorithm |
The encryption algorithm used (if any) by the APN for security. |
Mobile Node AAA Removal Indication |
Specifies whether the system is configured to remove various information elements when relaying registration request (RRQ) messages to HA. Value could be Enabled or Disabled. |
Net BIOS |
Primary NBNS Address |
Primary service address of the NetBIOS server. |
Secondary NBNS Address |
Secondary service address of the NetBIOS server. |
PDP Contexts Parameters |
Total Contexts |
The total number of primary and secondary PDP contexts that can be supported by the APN. Value is an integer between 1 and 4,000,000. |
PDP Type |
The type of the PDP contexts supported by the APN. |
Primary Contexts |
The status of the primary contexts of the APN. |
PPP Profile |
Data Compression Protocols |
The compression protocol used by the APN for compression of data packets. |
Keep Alive |
The frequency (in seconds) of sending the Link Control Protocol (LCP) keep alive messages. A value zero denotes that the keep alive messages are disabled completely. |
Data Compression Mode |
The compression mode used by the compression protocol which could be: • Normal—Packets are compressed using the packet history. Normal—Packets are compressed using the packet history. • Stateless—Each packet is compressed individually. Stateless—Each packet is compressed individually. |
MTU (bytes) |
The maximum transmission unit (MTU) for packets accessing the APN. |
Min. Compression Size (bytes) |
The smallest packet to which compression may be applied. |
RADIUS |
RADIUS Group |
The Authentication, Authorization, and Accounting (AAA) group name for the subscriber. If no group is set, the value is displayed as Default. |
RADIUS Secondary Group |
The secondary AAA group for the APN. If no group is set, the value is displayed as None. |
Returned Framed IP Address Policy |
The policy which indicates whether to accept or reject a call when the RADIUS server supplies 255.255.255.255 as the framed IP address and when the MS does not supply an IP address. |
Timeout |
Absolute |
Absolute timeout of a session, in seconds, for the APN. |
Idle |
Maximum duration, in seconds, after which the system considers the session as dormant or idle and invokes the long duration timer action. |
Long Duration |
Maximum duration, in seconds, before the system automatically reports or terminates the session. This is the maximum duration before the specified timeout action is activated for the session. |
Long Duration Inactivity |
Maximum duration, in seconds, before the session is marked as dormant. |
Emergency Inactivity |
Timeout duration, in seconds, to check inactivity on the emergency session. |
Idle Activity Downlink State |
Indicates whether the system must ignore the downlink traffic to consider as activity for idle-timeout. Only uplink packets will be able to reset the idle-timeout. |
MBMS Bearer Absolute |
Maximum time a Multimedia Broadcast and Multicast Server (MBMS) bearer can exist in active or idle state. |
MBMS Bearer Idle |
Maximum time an MBMS bearer context can be idle. |
MBMS UE Absolute |
Session timeout value for the MBMS user equipment. |
IPv6 Init Solicit Wait |
IPv6 initial router solicit wait timeout. |
Long Duration Action Type |
The action taken on long duration sessions. For example, the system performs any of the following actions: • Detects a long duration session and sends an SNMP trap and CORBA notification. Detects a long duration session and sends an SNMP trap and CORBA notification. • Disconnects the session after sending an SNMP trap and CORBA notification. Disconnects the session after sending an SNMP trap and CORBA notification. • Suppresses the SNMP trap and CORBA notification after detecting and disconnecting long duration session. Suppresses the SNMP trap and CORBA notification after detecting and disconnecting long duration session. |
Tunnel Parameters |
Address Policy |
The address allocation / validation policy for all tunneled calls except Layer 2 Tunneling Protocol (L2TP) calls. |
Peer Load Balancing |
The algorithm that defines how the tunnel peers are selected by the APN when multiple peers are configured in the APN. |
DNS Configuration |
Primary DNS Address |
The primary DNS server for the APN. |
Secondary DNS Address |
The secondary DNS server for the APN. |
APN Commands
The following commands can be launched from the inventory by right-clicking an APN and choosing Commands > Configuration. Before executing any commands, you can preview them and view the results. If desired, you can also schedule the commands. To find out if a device supports these commands, see the Cisco Prime Network 3.10 Supported Cisco VNEs.
Note  You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
Table 26-13 APN Commands
|
|
|
|
Create QoS to DSCP Mapping |
Right-click on an APN node > Commands > Configuration |
Use this command to create the mapping between QoS and DSCP. |
Create Virtual APN |
|
Use this command to create a virtual APN. |
Delete APN |
Use this command to delete an APN profile. |
Modify APN |
|
Use this command to delete an APN profile. |
Working with GTPP
GPRS Tunneling Protocol Prime (GTPP) is used for communicating accounting messages to CGs. Enhanced Ch7arging Service (ECS) supports different accounting and charging interfaces for prepaid and postpaid charging and record generation. GTPP accounting in ECS allows the collection of counters for different types of data traffic including the data in a GGSN CDR (G-CDR) that is sent to the CGF.
GTPP performs the following functions:
• Transfers CDRs between the Charging Data Function (CDF) and CGF.
Transfers CDRs between the Charging Data Function (CDF) and CGF.
• Redirects CDRs to another CGF.
Redirects CDRs to another CGF.
• Advertises to peers about its CDR transfer capability; for example, after a period of service down time.
Advertises to peers about its CDR transfer capability; for example, after a period of service down time.
• Prevents duplicate CDRs that might arise during redundancy operations. The CDR duplication prevention function is carried out by marking potentially duplicated CDR packets, and delegating the final duplicate deletion task to a CGF or the billing domain, instead of handling the possible duplicates solely by GTPP messaging.
Prevents duplicate CDRs that might arise during redundancy operations. The CDR duplication prevention function is carried out by marking potentially duplicated CDR packets, and delegating the final duplicate deletion task to a CGF or the billing domain, instead of handling the possible duplicates solely by GTPP messaging.
Prime Network provides support on gathering the GTPP accounting setup details that are configured in the mobile gateway for transferring the different types of CDRs from charging agent to a GTPP server or accounting server.
GTPP is configured within the accounting context of an APN and is also used by GGSN, P-GW, and S-GW to transmit CDRs to CGF.
The following topics provide details on how to work with GTPP in Prime Network Vision:
• Viewing GTPP Properties
Viewing GTPP Properties
• Viewing Additional Characteristics of a GTPP
Viewing Additional Characteristics of a GTPP
• GTPP Commands
GTPP Commands
Viewing GTPP Properties
Prime Network Vision displays the GTPPs in a GTPP container under the Mobile node in the logical inventory. The icon used for representing GTPPs in the logical inventory is explained in Logical Inventory Icons.
To view GTPP properties:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > GTPP Container.
In the logical inventory window, choose Logical Inventory > Context > Mobile > GTPP Container.
Prime Network Vision displays the list of GTPP groups configured under the container. You can view the individual GTPP group details from the table on the right pane or by choosing Logical Inventory >Context > Mobile > GTPP Container > GTPP Group.
Table 26-14 describes the details available for each GTPP group.
Table 26-14 GTPP Properties in Logical Inventory
|
|
|
Group Name |
Name of the GTPP group. |
CDR Storage Mode |
Storage mode for CDRs, which could be Local or Remote. |
CDR Timeout |
Maximum amount of time the system waits for a response from the CGF before assuming the packet is lost. |
CDR Max Retries |
Number of times the system attempts to a CGF that is not responding. |
Max CDR Size (bytes) |
Maximum payload size of the GTPP packet. |
Max CDR Wait Time |
Maximum payload size of the GTPP packet. The payload includes the CDR and the GTPP header. |
Max CDRs in Message |
Maximum number of CDRs allowed in a single packet. |
Recover Files Sequence Number |
Indicates whether recovery of file sequence number is enabled or not. If enabled, everytime the machine is rebooted, the file sequence number continues from the last sequence number. |
Data Request Start Sequence Number |
The starting sequence number to be used in the GTPP data record transfer (DRT) record. |
Start File Sequence Number |
Starting value of the file sequence number. |
Source Port Validation |
Indicates whether port checking is enabled or disabled for node alive/echo/redirection requests from the CGF. |
Dictionary |
Dictionary supported by the GTPP group. |
|
|
Group |
GTPP group, in which the accounting server is configured. |
Context Name |
Name of the context, in which the CGF is configured. |
Primary Accounting Server Address |
IPv4 or IPv6 address of the CGF. |
Port |
UDP port over which the GGSN communicates with the CGF. |
State |
Status of the CGF, which could be Active or Inactive. |
Priority |
Relative priority of the CGF. This priority determines which CGF server to send the accounting data to. |
Viewing Additional Characteristics of a GTPP
To view additional characteristics of a GTPP:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > GTPP Container >GTPP.
In the logical inventory window, choose Logical Inventory > Context > Mobile > GTPP Container >GTPP.
Step 3  Expand the GTPP node. The following list of characteristics configured for the GGSN are displayed:
Expand the GTPP node. The following list of characteristics configured for the GGSN are displayed:
– Accounting Server Failure Detection—Attributes of the CGF accounting server within the GTPP server group.
Accounting Server Failure Detection—Attributes of the CGF accounting server within the GTPP server group.
– CDR Attributes Indicator—Indicates whether associated attributes are enabled or disabled for CDR generation.
CDR Attributes Indicator—Indicates whether associated attributes are enabled or disabled for CDR generation.
– CDR Triggers—Attributes that trigger CDR generation.
CDR Triggers—Attributes that trigger CDR generation.
– Charging Agent— IP address and port of the system interface within the current context used to communicate with the CGF or the GTPP Storage Server (GSS).
Charging Agent— IP address and port of the system interface within the current context used to communicate with the CGF or the GTPP Storage Server (GSS).
– EGCDR Data Generation Configuration—Attributes that represent the GTPP eG-CDR data generation configuration.
EGCDR Data Generation Configuration—Attributes that represent the GTPP eG-CDR data generation configuration.
– Local Storage—Storage server information, if CDR storage mode is Local.
Local Storage—Storage server information, if CDR storage mode is Local.
– MBMS CDR Triggers—Attributes that trigger the MBMS CDR generation.
MBMS CDR Triggers—Attributes that trigger the MBMS CDR generation.
– Storage Server—Configuration information for the GTPP backup storage server.
Storage Server—Configuration information for the GTPP backup storage server.
Step 4  Click each of one of these characteristics to view its properties on the right pane. See Table 26-15 for more details on the properties of each characteristics configured for the GTPP.
Click each of one of these characteristics to view its properties on the right pane. See Table 26-15 for more details on the properties of each characteristics configured for the GTPP.
Table 26-15 GTPP Characteristics
|
|
|
Accounting Server Failure Detection |
Detect Dead Server Consecutive Failures |
Number of failures that could occur before marking a CGF as dead (down). |
Dead Server Suppress CDRs |
Indicates whether suppression of CDRs is enabled or disabled when the GTPP server is detected as dead or unreachable. |
Dead Time |
Maximum duration, in seconds, before marking a CGF as dead on consecutive failures. |
Echo Timeout |
The amount of time that must elapse before the system attempts to communicate with a CGF that was previously unreachable. |
Echo Max Retries |
Number of times the system attempts to communicate with a GTPP backup storage server that is not responding. |
Redirection Allowed |
Indicates whether redirection of CDRs is allowed or not, when the primary CGF is unavailable. |
Duplicate Hold Time Minutes |
Number of minutes to hold on to CDRs that may be duplicates, when the primary CGF is down. |
CDR Attributes Indicator |
Indicators |
Indicates whether the following CDR attributes are enabled or not: • PDP Type PDP Type • PDP Address PDP Address • Dynamic Flag Dynamic Flag • Diagnostics Diagnostics • Node ID Node ID • Charging Characteristic Selection Mode Charging Characteristic Selection Mode • Local Record Sequence Number Local Record Sequence Number • MSISDN MSISDN • PLMN ID PLMN ID • PGW PLMN ID PGW PLMN ID • IMEI IMEI • RAT RAT • User Location Information User Location Information • List of Service Data List of Service Data • Served MNAI Served MNAI • Start Time Start Time • Stop Time Stop Time • PDN Connection ID PDN Connection ID • Served PDP PDN Address Extension Served PDP PDN Address Extension • Duration Duration |
CDR Triggers |
Triggers |
Indicates whether the following CDR triggers are enabled or not: • Volume Limit Volume Limit • Time Limit Time Limit • Tariff Time Change Tariff Time Change • Serving Node Change Limit Serving Node Change Limit • Intra SGSN Group Change Intra SGSN Group Change • Inter PLMN SGSN Change Inter PLMN SGSN Change • EGCDR Max LOSDV Limit EGCDR Max LOSDV Limit • QOS Change QOS Change • RAT Change RAT Change • MS Timezone Change MS Timezone Change • Direct Tunnel Direct Tunnel |
Charging Agent |
IP Address |
IP address of the charging agent. |
Port |
Port of the charging agent. |
EGCDR Data Generation Configuration |
Service Interval |
The volume octet counts for the generation of the interim eG-CDRs to service data flow container in flow-based charging (FBC). |
Service Idle Timeout |
Time interval, in seconds, to close the eG-CDR, if the minimum time duration thresholds for service data flow containers are satisfied in FBC. |
Delete Service Thresholds |
Configured threshold in eG-CDR to be deleted in the service. |
Include All LOSDVs |
Indicates whether all content IDs are included in the final eG-CDR or not. |
LOSDV Max Containers |
Maximum number of List of Service Data Volume (LoSDV) containers in one eG-CDR. |
LOTDV Max Containers |
Maximum number of List of Service Data Volume (LoSDV) containers in one eG-CDR. |
Closing Cause Unique |
Indicates whether the same closing cause needs to be included for multiple final eG-CDRs or not. |
Local Storage |
File Format |
File format to store CDRs. |
File Compression |
Type of compression used on CDR files stored locally. None indicates that file compression is disabled. |
File Rotation Time Interval |
Time duration, in seconds, after which CDR file rotation happens. |
File Rotation Volume Limit (MB) |
Volume of CDR file, in MB, after which CDR file rotation happens. |
File Rotation CDR Count |
Number of CDRs to include in a CDR file after which CDR file rotation happens. |
Force File Rotation by Time Interval |
Indicates whether file rotation is forced or not. If this is enabled, the system is forced to do a file rotation at specified interval, even if there are no CDRs generated. |
Purge Processed Files |
Indicates whether processed files must be processed or not. |
MBMS CDR Triggers |
Interval |
Specifies the normal time duration that must elapse before closing an accounting record provided that any or all of the following conditions are satisfied: • Down link traffic volume is reached within the time interval Down link traffic volume is reached within the time interval • Tariff time based trigger occurred within the time interval Tariff time based trigger occurred within the time interval • Data volume (uplink and downlink) bucket trigger occurred within the time interval Data volume (uplink and downlink) bucket trigger occurred within the time interval |
Buckets |
Total number of data buckets configured for MBMS CDR trigger service. |
Storage Server |
IP Address |
IP address of the backup storage server. |
Port |
UDP port number over which the GGSN communicates with the backup storage server. |
Timeout |
Maximum amount of time, in seconds, the system waits for a response from the GTPP backup storage server before assuming the packet is lost. |
Max Retries |
Number of times the system attempts to communicate with a GTPP backup storage server that is not responding. |
GTPP Commands
The following commands can be launched from the inventory by right-clicking a GTPP and choosing Commands > Configuration or Commands > Show. Before executing any commands, you can preview them and view the results. If desired, you can also schedule the commands. To find out if a device supports these commands, see the Cisco Prime Network 3.10 Supported Cisco VNEs.
Note  You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
Table 26-16 GTPP Commands
|
|
|
|
Create CGF |
Right-click on a GTPP group > Commands > Configuration |
The Charging Gateway Function (CGF) listens to GTP' messages sent from the GSNs on TCP/UDP port 3386. The core network sends charging information to the CGF, typically including PDP context activation times and the quantity of data which the end user has transferred. However, this communication which occurs within one network is less standardized and may, depending on the vendor and configuration options, use proprietary encoding or even an entirely proprietary system. Use this command to create a new CGF. |
Create Storage Server |
The GTPP Storage Server (GSS) provides an external management solution for the bulk storage of Charging Data Records (CDRs) coming from a GPRS Support Node (GSN) in a GPRS/UMTS network. Use this command to create a storage server. |
Modify Storage Server |
Right-click on a GTPP group > Storage Server |
Use this command to modify storage server configuration details. |
Delete Storage Server |
Use this command to delete a storage server. |
Delete CGF |
Right-click on a GTPP group > Commands > Configuration |
Use this command to delete a CGF. |
Delete GTPP |
Use this command to delete a GTPP. |
Modify CGF |
Use this command to modify CGF configuration details. |
Modify GTPP |
Use this command to modify GTPP configuration details. |
Show CGF |
Right-click on a GTPP group > Commands > Show |
Use this command to view and confirm CGF configuration details. |
Working with EGTP
Evolved GPRS Tunneling Protocol (EGTP) formulates the primary bearer plane protocol within an LTE / EPC architecture. It provides support for tunnel management including handover procedures within and across LTE networks.
This topic contains the following sections:
• Viewing EGTP Properties
Viewing EGTP Properties
• EGTP Commands
EGTP Commands
Viewing EGTP Properties
Prime Network Vision displays the EGTPs in an EGTP container under the Mobile node in the logical inventory. The icon used for representing EGTPs in the logical inventory is explained in Logical Inventory Icons.
To view EGTP properties:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > EGTP Container.
In the logical inventory window, choose Logical Inventory > Context > Mobile > EGTP Container.
Prime Network Vision displays the list of EGTPs configured under the container. You can view the individual EGTP details from the table on the right pane or by choosing Logical Inventory >Context > Mobile > EGTP Container > EGTP.
Table 26-17 describes the details available for each EGTP.
Table 26-17 EGTP Properties in Logical Inventory
|
|
|
Service Name |
Name of the EGTP service. |
Status |
Status of the EGTP service. |
Message Validation Mode |
Mode of message validation for the EGTP service. |
Interface Type |
Interface type for the EGTP service. |
Restart Counter |
Restart counter value for the EGTP service. |
GTPC Retransmission Timeout |
Control packet retransmission timeout for the EGTP service. |
GTPC Max Request Retransmissions |
Maximum number of request retransmissions for the EGTP service. |
GTPC IP QoS DSCP Value |
The IP QoS DSCP value for the EGTP service. |
GTPC Echo |
Indicates whether GTPC echo is configured for the EGTP service or not. |
GTPC Echo Interval |
GTPC echo interval for the EGTP service. |
GTPC Echo Mode |
GTPC echo mode, which could be Dynamic or Default. |
GTPC Smooth Factor |
Smooth factor used in the dynamic echo timer for the EGTP service. |
EGTP Commands
The following commands can be launched from the inventory by right-clicking an EGTP and choosing Commands > Configuration. Before executing any commands, you can preview them and view the results. If desired, you can also schedule the commands. To find out if a device supports these commands, see the Cisco Prime Network 3.10 Supported Cisco VNEs.
Note  You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
Table 26-18 EGTP Commands
|
|
|
|
Modify EGTP |
Right-click on a EGTP group > Commands > Configuration |
Use this command to modify EGTP configuration details. |
Delete EGTP |
Use this command to delete the EGTP. |
LTE Networks - An Overview
Long Term Evolution (LTE) is the latest step in moving forward from the cellular 3G services, such as GSM to UMTS to HSPA to LTE or CDMA to LTE. LTE is based on standards developed by the Third Generation Partnership Project (3GPP). LTE may also be referred more formally as Evolved UMTS Terrestrial Radio Access Network (E-UTRAN). Following are the main objectives of an LTE network.
• Increased downlink and uplink peak data rates
Increased downlink and uplink peak data rates
• Scalable bandwidth
Scalable bandwidth
• Improved spectral efficiency
Improved spectral efficiency
• All IP network
All IP network
Figure 26-3 provides the topology of a basic LTE network.
Figure 26-3 Basic LTE Network Topology
Working with LTE Network Technologies
The E-UTRAN uses a simplified single node architecture consisting of the eNodeBs (E-UTRAN Node B). The eNB communicates with the Evolved Packet Core (EPC) using the S1 interface, specifically with the Mobility Management Entity (MME) and Serving Gateway (S-GW) using S1-U interface. The PDN Gateway (P-GW0 provides connectivity to the external packet data networks.
Following sections provide more details on these services and their support in Prime Network:
• Monitoring SAE-GW
Monitoring SAE-GW
• Working with PDN-Gateway
Working with PDN-Gateway
• Working with Serving Gateway
Working with Serving Gateway
• Viewing QCI-QoS Mapping
Viewing QCI-QoS Mapping
• Viewing the Layer 2 Tunnel Access Concentrator Configurations
Viewing the Layer 2 Tunnel Access Concentrator Configurations
• Monitoring the HRPD Serving Gateway
Monitoring the HRPD Serving Gateway
• Viewing the HSGW Configuration
Viewing the HSGW Configuration
• Monitoring Home Agent (HA)
Monitoring Home Agent (HA)
• Monitoring the Foreign Agent
Monitoring the Foreign Agent
• Monitoring Evolved Packet Data Gateway (ePDG)
Monitoring Evolved Packet Data Gateway (ePDG)
• Monitoring Packet Data Serving Node
Monitoring Packet Data Serving Node
• Viewing the Local Mobility Anchor Configuration
Viewing the Local Mobility Anchor Configuration
Monitoring SAE-GW
Systems Architecture Evolution (SAE) has a flat all-IP architecture with separation of control plane and user plane traffic. The main component of SAE architecture is the Evolved Packet Core (EPC), also known as SAE Core. The EPC serves as an equivalent to GPRS networks by using its subcomponents Mobility Management Entities (MMEs), Serving Gateway (S-GW), and PDN Gateway (P-GW).
Mobility Management Entity (MME)
MME is the key control node for a Long Term Evolution (LTE) access network. It is responsible for idle mode User Equipment (UE) tracking and paging procedure including retransmissions. It is involved in the bearer activation/deactivation process and is also responsible for choosing the S-GW for a UE at the initial attach and at time of intra-LTE handover involving Core Network (CN) node relocation. The MME also provides the control plane function for mobility between LTE and 2G/3G access networks with the S3 interface terminating at the MME from the SGSN.
Serving Gateway (S-GW)
The S-GW routes and forwards user data packets, while also acting as the mobility anchor for the user plane during inter-eNodeB handovers and as the anchor for mobility between LTE and other 3GPP technologies. For idle state UEs, the S-GW terminates the downlink data path and triggers paging when downlink data arrives for the UE. It manages and stores UE contexts, such as parameters of the IP bearer service, network internal routing information, and so on. It also performs replication of the user traffic in case of lawful interception.
For more information, see Working with Serving Gateway.
PDN Gateway (P-GW)
The P-GW provides connectivity from the UE to external packet data networks by being the point of exit and entry of traffic for the UE. A UE may have simultaneous connectivity with more than one P-GW for accessing multiple PDNs. The P-GW performs policy enforcement, packet filtering for each user, charging support, lawful interception, and packet screening. Another key role of the P-GW is to act as the anchor for mobility between 3GPP and non-3GPP technologies such as WiMAX and 3GPP2.
For more information, see Working with PDN-Gateway.
Running S-GW and P-GW services together as a SAE-GW provides the following benefits:
• Higher capacity—For a UE with one PDN connection that is passing through standalone S-GW and P-GW services consumes 2 license units because both S-GW and P-GW services account for it separately. SAE-GW as a single node consumes only one license unit for the same, thus increasing the capacity.
Higher capacity—For a UE with one PDN connection that is passing through standalone S-GW and P-GW services consumes 2 license units because both S-GW and P-GW services account for it separately. SAE-GW as a single node consumes only one license unit for the same, thus increasing the capacity.
• Cohesive configuration—Configuration and management of SAE-GW as a node is simpler to follow and logical to explain.
Cohesive configuration—Configuration and management of SAE-GW as a node is simpler to follow and logical to explain.
See Viewing SAE-GW Properties for details on how to view SAE-GW properties in Prime Network Vision.
Viewing SAE-GW Properties
Prime Network Vision displays the SAE-GWs in a SAE-GW container under the Mobile node in the logical inventory. The icon used for representing SAE-GW in the logical inventory is explained in Logical Inventory Icons.
To view SAE-GW properties:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > SAE-GW Container.
In the logical inventory window, choose Logical Inventory > Context > Mobile > SAE-GW Container.
Prime Network Vision displays the list of SAE-GW services configured under the container. You can view the individual SAE-GW service details from the table on the right pane or by choosing Logical Inventory > Context > Mobile > SAE-GW Container > SAE-GW.
Table 26-19 describes the details available for each SAE-GW.
Table 26-19 SAE-GW Properties in Logical Inventory
|
|
|
Service Name |
Name of the SAE-GW service. |
Service ID |
ID of the SAE-GW service. |
Status |
Status of the SAE-GW service. |
P-GW Service |
The P-GW service associated with the SAE-GW. |
S-GW Service |
The S-GW service associated with the SAE-GW. |
New Call Policy |
Specifies if the new call related behavior of SAE-GW service is enabled or disabled, when duplicate sessions with same IP address request is received. |
Working with PDN-Gateway
PDN Gateway (P-GW) is the node that terminates the SGi interface towards the PDN. If a user equipment (UE) is accessing multiple PDNs, there may be more than one P-GW for that UE. The P-GW provides connectivity to the UE to external packet data networks by being the point of exit and entry of traffic for the UE. A UE may have simultaneous connectivity with more than one P-GW for accessing multiple PDNs.
The P-GW facilitates policy enforcement, packet filtering for each user, charging support, lawful interception, and packet screening. The features of P-GW include:
• Integration of multiple core network functions in a single node
Integration of multiple core network functions in a single node
• Multiple instances of P-GW can enable call localization and local breakout
Multiple instances of P-GW can enable call localization and local breakout
• High performance across all parameters like, signaling, throughput, density, and latency
High performance across all parameters like, signaling, throughput, density, and latency
• Integrated in-line services
Integrated in-line services
• Support for enhanced content charging, content filtering with blacklisting, dynamic network-based traffic optimization, application detection and optimization, stateful firewall, NAT translation, and lawful intercept
Support for enhanced content charging, content filtering with blacklisting, dynamic network-based traffic optimization, application detection and optimization, stateful firewall, NAT translation, and lawful intercept
• High-availability helps to ensure subscriber satisfaction
High-availability helps to ensure subscriber satisfaction
The following topics explain how to work with P-GW in Prime Network Vision:
• Viewing P-GW Properties
Viewing P-GW Properties
• P-GW Commands
P-GW Commands
Viewing P-GW Properties
Prime Network Vision displays the P-GWs in a P-GW container under the Mobile node in the logical inventory. The icon used for representing P-GW in the logical inventory is explained in Logical Inventory Icons.
To view P-GW properties:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > P-GW Container.
In the logical inventory window, choose Logical Inventory > Context > Mobile > P-GW Container.
Prime Network Vision displays the list of P-GW services configured under the container. You can view the individual P-GW service details from the table on the right pane or by choosing Logical Inventory >Context > Mobile > P-GW Container > P-GW.
Table 26-20 describes the details available for each P-GW.
Table 26-20 P-GW Properties in Logical Inventory
|
|
|
Service Name |
Name of the P-GW service. |
Service Status |
Status of the P-GW service. |
EGTP Service |
Evolved GPRS Tunneling Protocol (EGTP) service associated with the P-GW. EGTP provides tunneling support for the P-GW. |
GGSN Service |
GGSN service associated with the P-GW. |
LMA Service |
Local Mobility Anchor (LMA) that facilitates proxy mobile IP on the P-GW. |
QCI QoS Mapping Table Name |
Table name of QoS class indices that enfore QoS parameters. |
New Call Policy |
Specifies if the new call related behavior of P-GW service is enabled or disabled, when duplicate sessions with same IP address request is received. |
Session Delete Delay Timeout |
Duration, in seconds, to retain a session before terminating it. |
SAE-GW Service |
Systems Architecture Evolution (SAE) gateway service associated with the P-GW. |
Step 3  If the P-GW is associated with PLMNs, you can view the details of the PLMNs on clicking the specified P-GW.
If the P-GW is associated with PLMNs, you can view the details of the PLMNs on clicking the specified P-GW.
P-GW Commands
The following commands can be launched from the inventory by right-clicking a P-GW and choosing Commands > Configuration. Before executing any commands, you can preview them and view the results. If desired, you can also schedule the commands. To find out if a device supports these commands, see the Cisco Prime Network 3.10 Supported Cisco VNEs.
Note  You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
Table 26-21 P-GW Commands
|
|
|
|
Create P-GW PLMN |
Right-click on a P-GW service > Commands > Configuration |
Use this command to create a PLMN for P-GW. |
Delete P-GW |
Use this command to delete a P-GW. |
Modify P-GW |
Use this command to modify the configuration details for a P-GW. |
Working with Serving Gateway
In a Long Term Evolution (LTE) / Systems Architecture Evolution (SAE) network, a Serving Gateway (S-GW) acts as a demarcation point between the Radio Access Network (RAN) and core network, and manages user plane mobility. It serves as the mobility anchor when terminals move across areas served by different eNode-B elements in Evolved UMTS Terrestrial Radio Access Network (E-UTRAN), as well as across other 3GPP radio networks such as GSM EDGE Radio Access Network(GERAN) and UTRAN. S-GW buffers downlink packets and initiates network-triggered service request procedures. Other functions include lawful interception, packet routing and forwarding, transport level packet marking in the uplink and the downlink, accounting support for per user, and inter-operator charging. The S-GW routes and forwards user data packets, while also acting as the mobility anchor for the user plane during inter-eNode-B handovers and as the anchor for mobility between LTE and other 3GPP technologies.
For idle state user equipment (UE), the S-GW terminates the downlink data path and triggers paging when downlink data arrives for the UE. It manages and stores UE contexts, such as parameters of the IP bearer service, network internal routing information, and so on. It also performs replication of the user traffic in case of lawful interception.
The following topics provide details on how to work with S-GWs in Prime Network Vision:
• Viewing S-GW Properties
Viewing S-GW Properties
• S-GW Commands
S-GW Commands
Viewing S-GW Properties
Prime Network Vision displays the S-GWs in a S-GW container under the Mobile node in the logical inventory. The icon used for representing S-GW in the logical inventory is explained in Logical Inventory Icons.
To view S-GW properties:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > S-GW Container.
In the logical inventory window, choose Logical Inventory > Context > Mobile > S-GW Container.
Prime Network Vision displays the list of S-GW services configured under the container. You can view the individual S-GW service details from the table on the right pane or by choosing Logical Inventory >Context > Mobile > S-GW Container > S-GW.
Table 26-22 describes the details available for each S-GW.
Table 26-22 S-GW Properties in Logical Inventory
|
|
|
Service Name |
Name of the S-GW service. |
Service Status |
Status of the S-GW service. |
Accounting Context |
Name of the context configured on the system that processes accounting for service requests handled by the S-GW service. |
Accounting GTPP Group |
Name of the accounting GTPP group associated with the S-GW service. This will hold the configured GTPP server group (for GTPP servers redundancy) on a S-GW service for CGF accounting functionality. |
Accounting Mode |
Accounting protocol, which could be GTPP or Radius-Diameter. |
Egress Protocol |
Egress protocol used for the S-GW service, which could be GTP, GTP-PMIP, or PMIP. |
Ingress EGTP Service |
Ingress EGTP service associated with the S-GW. EGTP provides tunneling support for the S-GW. |
Egress Context |
Context used for S-GW service egress. |
Egress ETGP Service |
Ingress EGTP service associated with the S-GW. EGTP provides tunneling support for the S-GW. |
Egress Mag Service |
Mobile Access Gateway (MAG) egress service through calls are routed to the S-GW. |
IMS Authorization Service |
IMS authorization service associated with the S-GW. |
Accounting Policy |
Accounting policy configured for the S-GW. |
New Call Policy |
Specifies if the new call related behavior of S-GW service is enabled or disabled, when duplicate sessions with same IP address request is received. |
QCI QoS Mapping Table |
Table name of QoS class indices that enfore QoS parameters. |
SAE GW Service |
Systems Architecture Evolution (SAE) gateway service associated with the S-GW. |
Step 3  If the S-GW is associated with PLMNs, you can view the PLMN entries on clicking the specified S-GW.
If the S-GW is associated with PLMNs, you can view the PLMN entries on clicking the specified S-GW.
S-GW Commands
The following commands can be launched from the inventory by right-clicking an S-W and choosing Commands > Configuration. Before executing any commands, you can preview them and view the results. If desired, you can also schedule the commands. To find out if a device supports these commands, see the Cisco Prime Network 3.10 Supported Cisco VNEs.
Note  You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
Table 26-23 S-GW Commands
|
|
|
|
Create S-GW PLMN |
Right-click on a S-GW service > Commands > Configuration |
Use this command to create a PLMN for S-GW. |
Delete S-GW |
Use this command to delete a S-GW. |
Modify S-GW |
Use this command to modify the configuration details for a S-GW. |
Viewing QCI-QoS Mapping
The QoS Class Index (QCI) to QoS mapping configuration mode is used to map Dices to enforceable QoS parameters. Mapping can occur between the RAN and the S-GW, the MME, and/or the P-GW in an LTE network or between the RAN and the harped Serving Gateway (HSGW) in an eHRPD network. This is a global configuration. These maps can be imported by P-gateway and S-gateway to enforce these parameters on upstream/downstream traffic.
Prime Network Vision displays the QCI-QoS mapping information under the Mobile node in the logical inventory. See Figure 26-18.
Note  QCI-QoS mapping is applicable only for the `local' context in the logical inventory.
QCI-QoS mapping is applicable only for the `local' context in the logical inventory.
To view QCI-QoS mapping:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > local > Mobile > QCI-QoS Mapping.
In the logical inventory window, choose Logical Inventory > local > Mobile > QCI-QoS Mapping.
Prime Network Vision displays the list of QCI-QoS mapping records configured under the container. You can view the individual record from the table on the right pane or by choosing Logical Inventory >Context > Mobile > QCI-QoS Mapping > Mapping Name.
Table 26-24 describes the QCI-QoS mapping details.
Table 26-24 QCI-QoS Mapping
|
|
|
Mapping Name |
Name of the QCI-QoS mapping record. |
QCI-QoS Mapping Table |
QCI Number |
QCI number. |
QCI Type |
QCI type. |
Uplink |
DSCP marking to be used for encapsulation and UDP for uplink traffic |
Downlink |
DSCP marking to be used for encapsulation and UDP for downlink traffic |
Max Packet Delay |
Maximum packet delay, in milliseconds, that can be applied to the data. |
Max Error Rate |
Maximum error loss rate of non congestion related packet loss. |
Delay Class |
Packet delay. |
Precedence Class |
Indicates packet precedence. |
Reliability Class |
Indicates packet reliability. |
Traffic Policing Interval |
Traffic policing interval. |
Viewing the Layer 2 Tunnel Access Concentrator Configurations
In computer networking, Layer 2 Tunneling Protocol (L2TP) is a tunneling protocol used to support virtual private networks (VPNs) or as part of the delivery of services by ISPs. It does not provide any encryption or confidentiality by itself; it relies on an encryption protocol that it passes within the tunnel to provide privacy. The entire L2TP packet, including payload and L2TP header, is sent within a User Datagram Protocol (UDP) datagram. It is common to carry Point-to-Point Protocol (PPP) sessions within an L2TP tunnel.
The two endpoints of an L2TP tunnel are called the LAC (L2TP Access Concentrator) and the LNS (L2TP Network Server). The LAC is the initiator of the tunnel while the LNS is the server, which waits for new tunnels. Once a tunnel is established, the network traffic between the peers is bidirectional.
LAC allows users and telecommuters to connect to their corporate intranets or extranets using L2TP. In other words, it forwards packets to and from the LNS and a remote system. It connects to the LNS using a local area network or wide area network and directs subscriber sessions into L2TP tunnels based on the domain of each session. Figure 26-4 denotes the LAC architecture.
Figure 26-4 LAC Architecture
The packets that are exchanged within an L2TP tunnel can be categorized as control packets and data packets.
To view the LAC configuration details:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > LAC. The list of LAC services configured in Prime Network is displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > LAC. The list of LAC services configured in Prime Network is displayed in the content pane.
Step 3  From the LAC node, choose an LAC service. The LAC service details are displayed in the content pane as shown in Figure 26-5.
From the LAC node, choose an LAC service. The LAC service details are displayed in the content pane as shown in Figure 26-5.
Figure 26-5 LAC Service Details
Table 26-25 displays the LAC configuration details.
Table 26-25 LAC Configuration Details
|
|
|
Service Name |
The unique identification string for the LAC service. |
Status |
The status of the LAC service, which can be any one of the following: • Initiated Initiated • Running Running • Down Down • Started Started • Nonstarted Nonstarted • Unknown Unknown |
Local IP Address |
The local IP address bound with the LAC service. |
Max Sessions |
The maximum number of subscribers connected to this service at any time, which can be any value between 1 and 2500000. This field defaults to 2500000. |
Max Tunnels |
The maximum length (in bytes) of the tunnel challenge.
Note  The tunnel challenge is basically used to authenticate tunnels at the time of creation. The tunnel challenge is basically used to authenticate tunnels at the time of creation.
|
Max Sessions Per Tunnel |
The maximum number of sessions that can be handled by a single tunnel at one point of time, which can be any value between 1 and 65535. This field defaults to 512. |
Max Retransmissions |
The maximum number of times a control message is retransmitted to a peer, before clearing the tunnel and its sessions. |
Keep Alive Interval |
The amount of time after which a keep alive message is sent. |
Control Receive Window |
The number of control messages the remote peer LNS can send before an acknowledgement is received. |
Max Tunnel Challenge Length |
The maximum length (in bytes) of the tunnel challenge. |
First Retransmission Timeout |
The initial timeout before retransmitting a control message.
Note  Each tunnel maintains a queue of control messages that must be transmitted to its peer. If an acknowledgement is not received after the specified period, then the control message is retransmitted. Each tunnel maintains a queue of control messages that must be transmitted to its peer. If an acknowledgement is not received after the specified period, then the control message is retransmitted.
|
Max Retransmission Timeout |
The maximum amount of time between two retransmitted messages. |
Load Balancing |
The type of load balancing to select LNS for the LAC service, which can be any one of the following: • Balanced Balanced • Prioritized Prioritized • Random Random |
Tunnel Selection Key |
The selection key to create tunnels between the L2TP service and the LNS server, based on the value of the \u2015Tunnel-Server-Auth-ID\u2016 attribute received from the AAA server. |
New Call Policy |
The new call policy for busy-out conditions, which can be any one of the following: • None None • Accept Accept • Reject Reject |
Data Sequence Numbers |
Indicates whether data sequence numbering for sessions that use the current LAC service is enabled. This option is enabled by default. |
Tunnel Authentication |
Indicates whether tunnel authentication is enabled.
Note  If this option is enabled, a configured shared secret is used to ensure that the LAC service is communicating with an authorized peer LNS. The shared secret is configured by the command in the LAC service configuration mode, the command in the subscriber configuration mode, or the Tunnel-Password attribute in the subscribers RADIUS profile. If this option is enabled, a configured shared secret is used to ensure that the LAC service is communicating with an authorized peer LNS. The shared secret is configured by the command in the LAC service configuration mode, the command in the subscriber configuration mode, or the Tunnel-Password attribute in the subscribers RADIUS profile.
|
Proxy LCP Authentication |
Indicates whether the option to send proxy LCP authentication parameters to the LNS is enabled. |
Attribute Hiding |
Indicates whether certain attributes in control messages sent from the LAC to the LNS is hidden.
Note  The LAC hides these attributes only if the tunnel authentication option is enabled between the LAC and LNS. The LAC hides these attributes only if the tunnel authentication option is enabled between the LAC and LNS.
|
Framed IP Address Snoop |
Indicates whether the LAC can detect IPCP packets exchanged between the mobile node and the LNS and extract the framed-I-address assigned to the mobile node.
Note  The address that is extracted is reported in the accounting start/stop messages and will be displayed for each subscriber session. The address that is extracted is reported in the accounting start/stop messages and will be displayed for each subscriber session.
|
Allow AAA Assigned Host Name |
Indicates whether the Tunnel-Client-Auth ID assigned by AAA is used as the Host name AVP in the L2TP tunnel setup message.
Note  If the tunnel parameters are not received from the RADIUS server, then the parameters configured in APN are considered for LNS peer selection. When the parameters in APN are considered, the local-hostname configured with the APN command for the LNS peer is used as the LAC Host name. If the tunnel parameters are not received from the RADIUS server, then the parameters configured in APN are considered for LNS peer selection. When the parameters in APN are considered, the local-hostname configured with the APN command for the LNS peer is used as the LAC Host name.
|
Allow APN in Called Number |
Indicates whether the APN name in Called number AVP is sent as part of the Incoming-Call Request (ICRQ) message sent to the LNS. If this keyword is not configured, then the Called number AVP will not be included in the ICRQ message sent to the LNS> |
Single UDP Port Mode |
Indicates whether the standard L2TP port 1701 is used as a source port for all L2TP control and data packets that originate from the LAC node. |
Peer LNS Address |
Peer LNS Address |
The IP address of the peer LNS for the current LAC service, which is usually in standard IPv4 dotted decimal notation. |
Preference |
The priority of the peer LNS, which can be any number between 1 and 128. This priority is used when multiple peer LNS are configured. |
Crypto Map |
The name of crypto map that is configured for the selected context. |
Description |
The description of the specified peer LNS. |
Monitoring the HRPD Serving Gateway
The HRPD Serving Gateway (HSGW) is a component in the evolved High Rate Packet Data (eHRPD) mobile network. It is an evolution option for CDMA operators that helps ensure converged mobility and management between HRPD and LTE networks.
The HSGW terminates the eHRPD access network interface from the Evolved Access Network (eAN) or Evolved Packet Core Function (ePCF) and routes UE-originated or terminated packet data traffic. It provides interworking with the eAN/ePCF and the PDN Gateway (P-GW) within the Evolved Packet Core (EPC) or LTE/SAE core network.
HSGW performs the following functions:
• Mobility anchoring for inter-eAN handoffs
Mobility anchoring for inter-eAN handoffs
• Transport level packet marking in the uplink and the downlink. For example, setting the DiffServ Code Point, based on the QCI of the associated EPS bearer
Transport level packet marking in the uplink and the downlink. For example, setting the DiffServ Code Point, based on the QCI of the associated EPS bearer
• Uplink and downlink charging per UE, PDN, and QCI
Uplink and downlink charging per UE, PDN, and QCI
• Downlink bearer binding based on policy information
Downlink bearer binding based on policy information
• Uplink bearer binding verification with packet dropping of UL traffic that does not comply with established uplink policy
Uplink bearer binding verification with packet dropping of UL traffic that does not comply with established uplink policy
• MAG functions for S2a mobility (i.e., Network-based mobility based on PMIPv6)
MAG functions for S2a mobility (i.e., Network-based mobility based on PMIPv6)
• Support for IPv4 and IPv6 address assignment
Support for IPv4 and IPv6 address assignment
• EAP Authenticator function
EAP Authenticator function
• Policy enforcement functions defined for the Gxa interface
Policy enforcement functions defined for the Gxa interface
• Robust Header Compression (RoHC)
Robust Header Compression (RoHC)
• Support for VSNCP and VSNP with UE
Support for VSNCP and VSNP with UE
• Support for packet-based or HDLC-like framing on auxiliary connections
Support for packet-based or HDLC-like framing on auxiliary connections
• IPv6 SLACC, generating RAs responding to RSs
IPv6 SLACC, generating RAs responding to RSs
An HSGW also establishes, maintains and terminates link layer sessions to UEs. The HSGW functionality provides interworking of the UE with the 3GPP EPS architecture and protocols. This includes support for mobility, policy control and charging (PCC), access authentication, and roaming. The HSGW also manages inter-HSGW handoffs.
The topology of the HSGW network is shown in the following figure:
Figure 26-6 HSGW Topology
Basic Features of HSGW
The basic features supported by HSGW can be categorized as follows:
• Authentication
Authentication
• IP Address Allocation
IP Address Allocation
• Quality of Service
Quality of Service
• AAA, Policy and Charging
AAA, Policy and Charging
The Authentication features supported by HSGW are:
• EAP over PPP
EAP over PPP
• UE and HSGW negotiates EAP as the authentication protocol during LCP
UE and HSGW negotiates EAP as the authentication protocol during LCP
• HSGW is the EAP authenticator
HSGW is the EAP authenticator
• EAP-AKA' (trusted non-3GPP access procedure) as specified in TS 33.402
EAP-AKA' (trusted non-3GPP access procedure) as specified in TS 33.402
• EAP is performed between UE and 3GPP AAA over PPP/STa
EAP is performed between UE and 3GPP AAA over PPP/STa
The IP Address Allocation features supported by HSGW are:
• Support for IPv4 and IPv6 addressing
Support for IPv4 and IPv6 addressing
• Types of PDNs - IPv4, IPv6 or IPv4v6
Types of PDNs - IPv4, IPv6 or IPv4v6
• IPv6 addressing
IPv6 addressing
– Interface Identifier assigned during initial attach and used by UE to generate it's link local address
Interface Identifier assigned during initial attach and used by UE to generate it's link local address
– HSGW sends the assigned /64 bit prefix in RA to the UE
HSGW sends the assigned /64 bit prefix in RA to the UE
– Configure the 128-bits IPv6 address using IPv6 SLAAC (RFC 4862)
Configure the 128-bits IPv6 address using IPv6 SLAAC (RFC 4862)
– Optional IPv6 parameter configuration via stateless DHCPv6(Not supported)
Optional IPv6 parameter configuration via stateless DHCPv6(Not supported)
• IPv4 address
IPv4 address
– IPv4 address allocation during attach
IPv4 address allocation during attach
– Deferred address allocation using DHCPv4(Not supported)
Deferred address allocation using DHCPv4(Not supported)
– Option IPv4 parameter configuration via stateless DHCPv4(Not supported)
Option IPv4 parameter configuration via stateless DHCPv4(Not supported)
The Quality of Service features supported by HSGW include:
• HRPD Profile ID to QCI Mapping
HRPD Profile ID to QCI Mapping
• DSCP Marking
DSCP Marking
• UE Initiated Dedicated Bearer Resource Establishment
UE Initiated Dedicated Bearer Resource Establishment
• QCI to DSCP Mapping
QCI to DSCP Mapping
The AAA, Policy and Charging features supported by HSGW include:
• EAP Authentication (STa)
EAP Authentication (STa)
• Rf Diameter Accounting
Rf Diameter Accounting
• AAA Server Groups
AAA Server Groups
• Dynamic Policy and Charging: Gxa Reference Interface
Dynamic Policy and Charging: Gxa Reference Interface
• Intelligent Traffic Control
Intelligent Traffic Control
Viewing the HSGW Configuration
To view the HSGW configuration:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > HSGW. The list of HSGW services configured in Prime Network are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > HSGW. The list of HSGW services configured in Prime Network are displayed in the content pane.
Step 3  From the HSGW node, choose a HSGW service. The HSGW service details are displayed in the content pane as shown in Figure 26-7.
From the HSGW node, choose a HSGW service. The HSGW service details are displayed in the content pane as shown in Figure 26-7.
Figure 26-7 HSGW Service Details
Table 26-26 displays the HSGW service details.
Table 26-26 HSGW Service details
|
|
|
Name |
The name of the HSGW service. |
Status |
The status of the service, which can be any one of the following: • Started Started • Not Started Not Started This field defaults to Not Started. |
Bind Address |
The IPv4 address to which the service is bound to. This field defaults to Null if binding is not done. |
Local IP Port |
The User Datagram Protocol (UDG) port for the R-P interface of the IP socket. |
Maximum Subscribers |
The maximum number of subscriber sessions that the service can support. |
MAG Service |
The Mobile Access Gateway (MAG) service associated with the HSGW service. Clicking this link will take you to the relevant MAG service under the MAG node. |
DNS PGW Context |
The location of the Domain Name System (DNS) client, which is used to identify the Fully Qualified Domain Name (FQDN) for the peer P-GW. |
Registration Lifetime |
The registration lifetime that is configured for all the subscribers. |
Setup Timeout |
The maximum amount of time (in seconds) allowed for session setup. |
Context Retention Timeout |
The maximum number of time (in seconds) that the UE session context is maintained by the HSGW service before it is torn down.
Note  The UE session context includes the Link Control Protocol (LCP), authentication and the A10 session context for a given UE. The UE session context includes the Link Control Protocol (LCP), authentication and the A10 session context for a given UE.
|
Maximum Retransmission |
The maximum number of times the HSGW service will try to communicate with the eAN or PCF before it declares it as unreachable. |
Network Initiated QoS |
Indicates whether the Network Initiated QoS feature is supported by the HSGW service. |
Unauthorized Flow QoS Timeout |
The amount of time (in seconds) the service must wait before a QoS update is triggered to downgrade an unauthorized flow. |
SPI tab |
SPI Number |
The unique Security Parameter Index (SPI) number, which indicates a security context between the services. |
Remote Address |
The IP address of the source service, which can be an IPv4 dotted decimal notation or IPv6 colon separated notation. |
Zone ID |
The PCF zone id that must be configured for the HSGW service. |
Netmask |
The subnet mask of the service. |
Hash Algorithm |
The hash algorithm used between the source and destination services. |
Time Stamp Tolerance |
The difference (tolerance) in timestamps that is acceptable. If the actual difference in the timestamps exceeds this difference, then the session is rejected. |
Replay Protection |
The replay-protection scheme that must be implemented by the service. |
Description |
The description of the SPI. |
PLMN tab |
PLMN ID |
The unique id of the Public Land Mobile Network (PLMN), which is used to determine if a mobile station is visiting, roaming, or belongs to the network. |
Primary |
Indicates whether the PLMN Id must be used as the default and primary ID. |
Overload Policies tab |
IP Address |
The IP address of an alternate PDSN, which is in the IPv4 dotted decimal notation. |
Weight |
The weightage of the IP address, which determines the order in which the IP address is used in case of multiple IP addresses. |
You can also view the following configuration details for a HSGW service:
• A10/A11 Properties—The A10/A11 interface (also known as R-P interface for RAN-to-PDSN) supports the A10 protocol for user data transport between the PCF and PDSN, and the A11 protocol for the associated signaling. A11 signaling messages are also used for passing accounting related and other information from the PCF to the PDSN. The A10/A11 interfaces support mobility between PCFs under the same PDSN.
A10/A11 Properties—The A10/A11 interface (also known as R-P interface for RAN-to-PDSN) supports the A10 protocol for user data transport between the PCF and PDSN, and the A11 protocol for the associated signaling. A11 signaling messages are also used for passing accounting related and other information from the PCF to the PDSN. The A10/A11 interfaces support mobility between PCFs under the same PDSN.
• GRE Parameters—Generic Routing Encapsulation (GRE) is a tunneling protocol developed by Cisco Systems that can encapsulate a wide variety of network layer protocols inside virtual point-to-point links over an Internet Protocol internetwork.
GRE Parameters—Generic Routing Encapsulation (GRE) is a tunneling protocol developed by Cisco Systems that can encapsulate a wide variety of network layer protocols inside virtual point-to-point links over an Internet Protocol internetwork.
• IP Source Violation—IP source violations occur when the PDSN receives packets from a subscriber where the source address is not the same as the address given to the subscriber, and hence get discarded.
IP Source Violation—IP source violations occur when the PDSN receives packets from a subscriber where the source address is not the same as the address given to the subscriber, and hence get discarded.
Viewing the A10/A11 Configuration Details
To view the A10/A11 configuration details:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > HSGW > HSGW service > A10/A11 Properties. The configuration details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > HSGW > HSGW service > A10/A11 Properties. The configuration details are displayed in the content pane.
Table 26-27 displays the A10/A11 configuration details.
Table 26-27 A10 A11 Configuration Details
|
|
|
Overload Policy |
The method used by the HSGW service to handle overload conditions, which can be any one of the following: • Reject Reject • Redirect Redirect |
New Call Policy |
The new call policy configured for the HSGW service, which can be any one of the following: • None None • Reject Reject • Accept Accept This field defaults to None. |
Data Available Indicator Enabled |
Indicates whether the data available indicator in A10/A11 registration reply messages is enabled. |
Data Over Signalling |
Indicates whether the data over signaling marking feature for A10 packets is enabled. |
Airlink Bad Sequence |
The behavior for airlink related parameters configured for the HSGW service, which can be any one of the following: • Accept Accept • Deny Deny |
Airlink Bad Sequence Deny Code |
The reason for denying airlink bad sequence, which can be any one of the following: • Unsupported vendor ID Unsupported vendor ID • Poorly formed request Poorly formed request |
Handoff With No Connection Setup |
Indicates whether the HSGW service must accept or deny handoff R-P sessions that do not have an Airlink Connection setup record in the A11 registration request. |
RSVP Retransmission Timeout |
The maximum amount of time (in seconds) in which RP control packets must be retransmitted. |
RSVP Maximum Retransmission Count |
The maximum number of times the RP control packets can be retransmitted. |
Viewing the GRE Parameters
To view the GRE Parameters for the HSGW service:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > HSGW > HSGW service > GRE Parameters. The relevant details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > HSGW > HSGW service > GRE Parameters. The relevant details are displayed in the content pane.
Table 26-28 displays the GRE parameter details.
Table 26-28 GRE Parameter Details
|
|
|
Checksum |
Indicates whether insertion of GRE checksum in outgoing GRE data packets is enabled. |
Checksum Verify |
Indicates whether verification of GRE checksum in incoming GRE packets is enabled. |
Reorder Timeout |
The maximum amount of time (in milliseconds) to wait before reordered out-of-sequence GRE packets are processed. |
Sequence Mode |
The method to handle incoming out-of-sequence GRE packets, which can be any one of the following: • Reorder Reorder • None None |
Sequence Numbers |
Indicates whether the option to insert or remove GRE sequence numbers in GRE packets is enabled. |
Flow Control |
Indicates whether flow control is supported by the selected HSGW service. By default, this option is disabled. |
Flow Control Timeout |
The amount of time (in milliseconds) to wait for an Transmitter On (XON) indicator from the RAN. This time can be any value between 1 and 1000000, and defaults to 10000 milliseconds. |
Flow Control Action |
The action that must be taken when the timeout limit is reached, which can be any one of the following: • disconnect-session disconnect-session • resume-session. resume-session. |
Protocol Type |
The tunnel type for the GRE routing. This field defaults to Any. |
Is 3GPP Extension Header QoS Marking |
Indicates whether the 3GG Extension Header QoS Marking is enabled for the selected HSGW feature.
Note  If this feature is enabled and the PCF negotiation feature is enabled in A11 RRQ, then the HSGW will include QoS optional data attribute in the GRE 3GPP2 Extension Header. If this feature is enabled and the PCF negotiation feature is enabled in A11 RRQ, then the HSGW will include QoS optional data attribute in the GRE 3GPP2 Extension Header.
|
MTU |
The maximum transmission unit (MTU) for packets accessing the APN. |
IP Header DSCP |
The Differential Service Code Point (DSCP) value in the IP header that marks the GRE IP Header encapsulation. This can be any value between 0x0F and 0X3F, and defaults to 0X0F. |
IP Header DSCP Packet Type |
Indicates whether the IP Header DSCP Value packet type is specified for the packets, which can be any one of the following: • all-control-packets—Indicates that DSCP marking for GRE IP header encapsulation will be applied for all control packets for the session. all-control-packets—Indicates that DSCP marking for GRE IP header encapsulation will be applied for all control packets for the session. • setup-packets-only—Indicates that DSCP marking for GRE IP header encapsulation willbe applied only for session setup packets. setup-packets-only—Indicates that DSCP marking for GRE IP header encapsulation willbe applied only for session setup packets. |
GRE Segmentation |
Indicates whether segmentation of GRE packets is enabled. By default, this option is disabled. |
Viewing the IP Source Violation Details
To view the IP source Violation configuration details:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > HSGW > HSGW service > IP Source Violation. The configuration details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > HSGW > HSGW service > IP Source Violation. The configuration details are displayed in the content pane.
Table 26-29 displays the IP Source Violation configuration details.
Table 26-29 IP Source Violation Configuration Details
|
|
|
Renegotiation Limit |
The number of source violations that are allowed within a specified detection period, after which a PPP renegotiation is forced. |
Drop Limit |
The number of source violations that are allowed within a specified detection period, after which a call disconnect is forced. |
Clear On Valid PDU |
Indicates whether the service must reset the renegotiation limit and drop limit counters if a properly addressed packet is received. |
Period |
The amount of time (in seconds) for the source violation detection period. Once this value is reached, the drop limit and renegotiation limit counters are decremented. |
Configuration Commands for HSGW
The HSGW commands allow you to configure HSGW services in your network. Please note that these commands are available only for Cisco ASR 5000 Mobile devices.
These commands can be launched from the logical inventory by choosing the Context > Commands > Configuration or Context > Commands > Show.
Before executing any commands, you can preview them and view the results. If desired, you can also schedule the commands.
Note  You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
Note  In the GUI, parameters that are displayed in bold text are mandatory.
In the GUI, parameters that are displayed in bold text are mandatory.
Table 26-30 lists the HSGW configuration commands.
Table 26-30 HSGW Configuration Commands
|
|
|
|
Create HSGW |
Right-click context > Commands > Configuration |
Use this command to create a new HSGW service. |
Modify HSGW Delete HSGW |
Expand HSGW node > right-click HSGW service > Commands > Configuration |
Use this command to modify/delete the configuration details of an HSGW service. |
Show HSGW |
Expand HSGW node > right-click HSGW service > Commands > Show |
Use this command to view and confirm the configuration details of an HSGW service. |
Create SPI |
Expand HSGW node > right-click HSGW service > Commands > Configuration |
Use this command to create a new Security Parameter Index (SPI) for the HSGW service. |
Modify SPI Delete SPI |
Expand HSGW node > HSGW service > In content pane, click SPI tab > right-click on SPI No. field > Commands > Configuration |
Use this command to modify/delete the SPI configuration details for the HSGW service. |
Create PLMN entries |
Expand HSGW node > right-click HSGW service > Commands > Configuration |
Use this command to create a new Public Land Mobile Network (PLMN) for the HSGW service. |
Modify PLMN entries Delete PLMN entries |
Expand HSGW node > HSGW service > In content pane, click PLMN tab > right-click on PLMN ID field > Commands > Configuration |
Use this command to modify/delete the PLMN configuration details for the HSGW service. |
Create Overload Policy |
Expand HSGW node > right-click HSGW service > Commands > Configuration |
Use this command to create a new overload policy for the HSGW service. |
Modify Overload Policy Delete Overload Policy |
Expand HSGW node > HSGW service > In content pane, click Overload Policies tab > right-click on IP address field > Commands > Configuration |
Use this command to modify/delete the overload policy details for the HSGW service. |
Modify A10 A11 Interface |
Expand HSGW node > HSGW service > Right-click A10/A11 Properties > Commands > Configuration |
Use this command to modify the A10/A11 configuration details for the HSGW service. |
Modify GRE |
Expand HSGW node > HSGW service > right-click GRE > Commands > Configuration |
Use this command to modify the GRE configuration details for the HSGW service. |
Modify IP Source Violation |
Expand HSGW node > HSGW service > right-click IP Source Violation > Commands > Configuration |
Use this command to modify the IP source violation details for the HSGW service. |
Viewing the MAG Configuration for HSGW
A Mobile Access Gateway (MAG) performs mobility-related signaling on behalf of the mobile nodes (MN) attached to its access links. MAG is the access router for the MN; that is, the MAG is the first-hop router in the localized mobility management infrastructure
A MAG performs the following functions:
• Obtains an IP address from a Local Mobility Anchor (LMA) and assigns it to an MN
Obtains an IP address from a Local Mobility Anchor (LMA) and assigns it to an MN
• Retains the IP address of an MN when the MN roams across MAGs
Retains the IP address of an MN when the MN roams across MAGs
• Tunnels traffic from an MN to LMA
Tunnels traffic from an MN to LMA
To view the MAG configuration details:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > MAG > MAG service. The configuration details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > MAG > MAG service. The configuration details are displayed in the content pane.
Table 26-31 displays the configuration details for a MAG service.
Table 26-31 MAG Service Configuration Details
|
|
|
Name |
The unique name of the MAG service. |
Status |
The status of the MAG service, which can be any one of the following: • Started Started • Not Started Not Started This field defaults to Not Started. |
Bind Address |
The IP address to which the MAG service is bound to. |
Maximum Subscribers |
The maximum number of subscribers supported by the service. |
PMIP Maximum Retransmission |
The maximum number of times the MAG service will communicate with the LMA, before it is declared unreachable. |
Registration Lifetime |
The registration lifetime configured for all the subscribers who have subscribed to this service. |
PMIP Retransmission Timeout |
The maximum amount of time (in milliseconds) the MAG service must wait for a response from the LMA. |
PMIP Renewal Time |
Indicates the percentage of the registration lifetime when the registration renewal is sent to the LMA for subscribers using this service. |
PMIP Retransmission Policy |
The retransmission policy for PMIP control messages, which can be any one of the following: • Normal Normal • Exponential backoff Exponential backoff |
New Call Policy |
The method for handling new calls, which can be any one of the following: • Accept Accept • Reject Reject This field defaults to None. |
PMIPv6 Tunnel Encapsulation |
The encapsulation type used for PMIPv6 tunnel data between the MAG and the LMA. |
Information Set |
The mobility options to be used in Proxy Binding Update (PBU) messages, for those messages sent between MAG and LMA. |
Mobility Option Type |
The mobility option type used in the mobility messages. |
Signalling Packets IP Header DSCP |
The Differential Services Code Point (DSCP) value in the IP Header of the signalling packets. |
Viewing the Profile-QCI Mapping Details
You can view the configured mapping entries between a Rendezvous Point (RP) QoS Profile and the LTE QoS Class Index (QCI).
A QCI is a scalar that is used as a reference to access node-specific parameters that control bearer level packet forwarding treatment (e.g. scheduling weights, admission thresholds, queue management thresholds, link layer protocol configuration, etc.), and that have been pre-configured by the operator owning the access node.
To view the Profile-QCI mapping entries:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > local > Mobile > Profile > Profile-QCI Mapping > Profile-QCI Mapping. The mapping details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > local > Mobile > Profile > Profile-QCI Mapping > Profile-QCI Mapping. The mapping details are displayed in the content pane.
Table 26-32 displays the Profile-QCI Mapping details.
Table 26-32 Profile-QCI Mapping Details
|
|
|
Profile Name |
The name of the Profile-QCI Mapping profile that is associated with the HSGW. |
Profile-QCI Mapping Table |
QCI ID |
The QCI ID to which the profile is mapped. |
Profile ID |
The profile ID to which the QCI ID is mapped. |
Uplink GBR |
The Guaranteed Bit Rate (GBR) for the uplink data flow, which can be any value between 0 and 4294967295. |
Downlink GBR |
The GBR for the downlink data flow, which can be any value between 0 and 4294967295. |
Uplink MBR |
The Maximum Bit Rate (MBR) for the uplink data flow, which can be any value between 0 and 4294967295. |
Downlink MBR |
The MBR for the downlink data flow, which can be any value between 0 and 4294967295. |
Priority Level |
The priority level of the profile for the QCI, which can be any value between 1 and 15. |
Preemption Capability |
The preemption capability of the profile. |
Configuration Commands for MAG
The MAG commands allow you to configure MAG services in your network. Please note that these commands are available only for Cisco ASR 5000 Mobile devices.
These commands can be launched from the logical inventory by choosing the Context > Commands > Configuration or Context > Commands > Show.
Before executing any commands, you can preview them and view the results. If desired, you can also schedule the commands.
Note  You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
Note  In the GUI, parameters that are displayed in bold text are mandatory.
In the GUI, parameters that are displayed in bold text are mandatory.
Table 26-33 lists the MAG configuration commands.
Table 26-33 MAG Configuration Commands
|
|
|
|
Create MAG |
Right-click context > Commands > Configuration |
Use this command to create a new Mobile Access Gateway (MAG) service for the selected context. |
Modify MAG Delete MAG |
Expand MAG Node > right-click MAG service > Commands > Configuration |
Use this command to modify the MAG configuration details/delete the MAG profile for the selected context. |
Show MAG |
Expand MAG Node > right-click MAG service > Commands > Show |
Use this command to view and confirm the configuration details for the selected MAG service. |
Create Profile ID QCI Mapping |
Right-click on the context > Commands > Configuration |
Use this command to create a QCI profile. |
Delete Profile ID QCI Mapping |
Expand Profile node > right-click profile name > Commands > Configuration |
Use this command to delete QCI profile. |
Create Profile |
Expand Profile node > right-click profile name > Commands > Configuration |
Use this command to create an entry for the QCI mapping profile. |
Modify Profile Delete Profile |
Expand Profile node > Profile name > In content pane, right-click on profile entry > Commands > Configuration |
Use these commands to modify/delete the entry for the QCI mapping profile. |
Monitoring Home Agent (HA)
A Home Agent (HA) stores information about the mobile nodes whose permanent home address is in the home agent's network. When a node wants to communicate with the mobile node, it sends packets to the permanent address. Because the home address logically belongs to the network associated with the HA, normal IP routing mechanisms forward these packets to the home agent.
When a mobile node moves out of the home network, the HA still manages to deliver the packets to the mobile node. This is done by interacting with the Foreign Agent (FA) that the mobile node is communicating with using the Mobile IP (MIP) Standard. Such transactions are performed through the use of virtual private networks that create MIP tunnels between the HA and FA. The following figure displays the configuration between the FA and HA network deployment.
Figure 26-8 Home Agent Topology
When functioning as a HA, the system can either be located within the carrier's 3G network or in an external enterprise or ISP network. The FA terminates the mobile subscriber's PPP session, and then routes data to and from the appropriate HA on behalf of the subscriber.
In accordance with Request for Comments (RFC) 2002, the FA is responsible for mobile node registration with, and tunneling of data traffic from/to the subscriber's home network. The HA is also responsible for tunneling traffic, but it maintains subscriber location information separately in the Mobility Binding Records (MBR).
Viewing the Home Agent Configuration
To view the Home Agent configuration:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent. The list of home agent services configured in Prime Network are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent. The list of home agent services configured in Prime Network are displayed in the content pane.
Step 3  From the Home Agent node, choose a home agent service. The home agent service details are displayed in the content pane as shown in Figure 26-9.
From the Home Agent node, choose a home agent service. The home agent service details are displayed in the content pane as shown in Figure 26-9.
Figure 26-9 Home Agent Service Details
Table 26-34 displays the Home Agent service details.
Table 26-34 Home Agent Service Details
|
|
|
Service Name |
The name of the home agent service. |
Status |
The status of the home agent service, which can be any one of the following: • Down Down • Running Running • Initiated Initiated • Unknown Unknown This field defaults to Down. |
Default Subscriber |
The name of the subscriber template that is applied to the subscribers. |
Local IP Port |
The User Datagram Protocol (UDP) port for the R-P interface of the IP socket. This IP port can be any value between 1 and 65535 and defaults to 699. |
Bind Address |
The IP address to which the service is bound to. This can be any address in the IPV4/IPv6 range. |
MIP NAT Traversal |
Indicates whether the acceptance of UDP tunnels for NAT traversal is enabled. |
Max. Subscribers |
The maximum subscriber sessions that could be supported. |
Force UDP Tunnel |
Indicates whether HA would accept requests when Network Address Translation (NAT) is not detected but the Force bit is set in the Registration Request (RRQ) with the UDP Tunnel Request. |
Simultaneous Bindings |
The maximum number of care of addresses that can be simultaneously bound for the same user identified by Network Access Identifier (NAI) and Home address. |
Destination Context |
The name of the context to assign to the subscriber, after authentication. |
A11 Signalling Packets IP Header DSCP |
The Differential Services Code Point (DSCP) value in the IP header. |
Registration Life Time |
The registration lifetime configured for all the subscribers to the service. |
GRE Encapsulation Without Key |
Indicates whether Generic Routing Encapsulation (GRE) without encapsulation key is used during Mobile IP sessions with FA. |
Idle Time Out |
The method the HA service uses to determine the time to reset a session idle timer, which can be any one of the following: • Aggressive Aggressive • Handoff Handoff • Normal Normal |
SPI List |
The Security Parameter Index (SPI) between the HA service and the FA. |
Optimize Tunnel Reassembly |
Indicates whether the option to optimize tunnel reassembly is enabled. |
Wi-Max 3GPP |
Indicates whether the Worldwide Interoperability for Microwave Acces (Wi-Max)-3GPP option is enabled for the Home agent service. |
Setup Time Out |
The maximum time (in seconds) allowed for session setup. |
Reverse Tunnel |
Indicates whether reverse tunnel feature is enabled for the home agent feature.
Note  A reverse tunnel is a tunnel that starts at the care-of address of the mobile node and terminates at the home agent. A mobile node can request a reverse tunnel between the foreign agent and the home agent when the mobile node registers. A reverse tunnel is a tunnel that starts at the care-of address of the mobile node and terminates at the home agent. A mobile node can request a reverse tunnel between the foreign agent and the home agent when the mobile node registers.
|
Min. Life Time |
The minimum registration life time for a mobile IP session. |
GRE Encapsulation With Key |
Indicates whether GRE is used during mobile IP sessions with an FA. |
FA HA SPIs / MN HA SPIs tab |
SPI Number |
The number to indicate the security context between services. |
Remote Address |
The IP address of the source service. |
Hash Algorithm |
The hash algorithm used between the source and destination services. |
Time Stamp Tolerance |
The acceptable allowable difference in time stamps. If this difference is exceeded, then the session is rejected. |
Replay Protection |
The replay protection scheme that should be implemented by the service. |
Permit Any Hash Algorithm |
Indicates whether verification of MN-HA authenticator using other hash algorithms is allowed, on failure of the configured hash algorithm.
Note  This field is available only in the MN HA SPIs tab. This field is available only in the MN HA SPIs tab.
|
Description |
The description of the SPI. |
IPSEC Crypto Maps |
Map Name |
The name of the crypto map that is configured in the same context that defines the IPSec tunnel properties. |
Peer FA Address |
The IP address of the Peer FA to which the IPSEC SA will be established. |
Skey Expiry |
The expiry information of the secret key. |
Viewing the AAA Configuration for Home Agent Service
In order to support Packet Data Serving Node (PDSN), FA, and HA functionality, the system must be configured with at least one source context and at least two destination contexts as shown in the following figure.
The source context will facilitate the PDSN service(s), and the R-P interfaces. The AAA context will be configured to provide foreign/home AAA functionality for subscriber sessions and facilitate the AAA interfaces.
To view the AAA configuration:
Step 1  In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent > Home agent service > AAA. The AAA configuration details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent > Home agent service > AAA. The AAA configuration details are displayed in the content pane.
Table 26-35 displays the AAA configuration for a home agent service.
Table 26-35 AAA Configuration for Home Agent Service
|
|
|
AAA Context |
The AAA context for the home agent service. Click this link to view the relevant AAA context. |
AAA Accounting |
Indicates whether the Home Agent can send AAA accounting information for subscriber sessions. |
AAA Accounting Group |
The AAA Accounting group for the Home agent service. |
AAA Distributed MIP Keys |
Indicates the usage of AAA distributed MIP keys for authenticating RRQ for WiMax HA calls. |
DMU Refresh Key |
Indicates whether the Home Agent is allowed to retrieve the MN-HA key again from the AAA during the call and use this freshly retrieved key value to recheck authentication. |
IMSI Authentication |
Indicates whether MN-AAA or MN-FAC extensions are present in the RRQ. |
MN HA Authentication Type |
Indicates whether the HA service looks for an MN-HA authentication in the RRQ. |
MN AAA Authentication Type |
The method used to send authentication request to AAA for each re-registration attempt.
Note  The initial registration request and de-registrations are handled normally. The initial registration request and de-registrations are handled normally.
|
PMIP Authentication |
Indicates whether the HA service looks for an PMIP authentication in the RRQ. |
Stale Key Disconnect |
Indicates whether the call must be disconnected immediately on failure of MN-HA authentication. |
Skew Lifetime |
The IKE pre-shared key\u2018s time skew. |
Viewing the GRE Configuration for Home Agent Service
To view the GRE configuration:
Step 1  In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent > Home agent service > GRE. The GRE configuration details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent > Home agent service > GRE. The GRE configuration details are displayed in the content pane.
Table 26-36 displays the GRE configuration for a home agent service.
Table 26-36 GRE Configuration for Home Agent Service
|
|
|
Checksum |
Indicates whether insertion of GRE checksum in outgoing GRE data packets is enabled. |
Checksum Verify |
Indicates whether verification of GRE checksum in incoming GRE packets is enabled. |
Reorder Timeout |
The maximum amount of time (in milliseconds) to wait before reordered out-of-sequence GRE packets are processed. |
Sequence Mode |
The method to handle incoming out-of-sequence GRE packets, which can be any one of the following: • Reorder Reorder • None None |
Sequence Numbers |
Indicates whether the option to insert or remove GRE sequence numbers in GRE packets is enabled. |
Viewing the Policy Configuration for Home Agent Service
To view the Policy configuration:
Step 1  In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent > Home agent service > Policy. The Policy configuration details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent > Home agent service > Policy. The Policy configuration details are displayed in the content pane.
Table 26-37 displays the Policy configuration for a home agent service.
Table 26-37 Policy Configuration for Home Agent Service
|
|
|
BC Response Code |
The response code for a binding cache (BC) query result in response to a network failure or error. |
NW-Reachability Policy |
The action to be taken on detection of an upstream network-reachability failure. |
Over Load Policy |
The overload policy within the HA service. |
New Call Policy |
The new call policy within the HA service. |
Over Load Redirect / NW-Reachability Redirect |
IP Address |
The IP address associated with the policy. |
Weight |
The weightage of the IP address associated with the policy. |
Viewing the Registration Revocation Details for a Home Agent Service
To view the Registration revocation configuration details:
Step 1  In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent > Home agent service > Registration Revocation. The configuration details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent > Home agent service > Registration Revocation. The configuration details are displayed in the content pane.
Table 26-38 displays the Registration Revocation configuration for a home agent service.
Table 26-38 Registration Revocation configuration for Home Agent Service
|
|
|
Registration Revocation State |
Indicates whether the Registration Revocation Status is enabled. |
Revocation IBit |
Indicates whether the Revocation Ibit feature is enabled. |
Send NAI Extension |
Indicates whether the option to send NAI extension in the revocation message is enabled. |
Handoff Old FA |
Indicates whether the option to send a revocation message from the HA to the FA is enabled.
Note  The revocation message is sent from the HA to the FA when an inter-access gateway or FA handoff of the MIP session occurs. The revocation message is sent from the HA to the FA when an inter-access gateway or FA handoff of the MIP session occurs.
|
Idle Timeout |
Indicates whether the HA must send a revocation message to the FA when the session times out. |
Revocation Max Retries |
The number of times the revocation message can be retransmitted. |
Revocation Timeout |
The maximum amount of time (in seconds) to wait for the receipt of an acknowledgement from the FA before the revocation message is transmitted again. |
Monitoring the Foreign Agent
A Foreign Agent (FA) is basically a router on a mobile node's visited network that provides routing services to the mobile node. The FA acts as a mediator between the mobile node and it's home agent (HA). When the mobile node moves out of its home network, the FA registers the mobile node with a Care of Address (CoA). It also facilitates routing information to the mobile node's home agent, which contains the permanent address of the node.
When a node tries to communicate with a mobile node that is roaming, it sends packets to the permanent address. The HA interacts with the FA and delivers the packets to the mobile node using the COA.
Figure 26-10 depicts the function of a foreign agent in a network and the different components that it interacts with.
Figure 26-10 Foreign Agent Architecture
Viewing the Foreign Agent Configuration Details
To view the Foreign Agent configuration details:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > FA. The list of Foreign agents configured in Prime Network are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > FA. The list of Foreign agents configured in Prime Network are displayed in the content pane.
Step 3  From the FA node, choose a FA service. The FA service details are displayed in the content pane as shown in Figure 26-11.
From the FA node, choose a FA service. The FA service details are displayed in the content pane as shown in Figure 26-11.
Figure 26-11 Foreign Agent Service Details
Table 26-39 displays the Foreign Agent configuration details.
Table 26-39 FA Configuration Details
|
|
|
Service Name |
The unique name to identify the FA service. |
Status |
The status of the FA service, which can be any one of the following: • Down Down • Running Running • Initiated Initiated • Unknown Unknown This field defaults to Down. |
Bind Address |
The IPv4 address to which the service is bound. |
Local IP Port |
The UDP port for the R-P Interface of the IP socket. This port can be any value between 1 and 65535, and defaults to 434. |
Max. Subscribers |
The maximum subscriber sessions that is supported by the service. This can be any value between 0 and 2500000, and defaults to 2500000. |
Default Subscriber |
The name of the subscriber template that is applicable to the subscribers using this domain alias. |
A11 Signalling Packets IP Header DSCP |
The Differential Service Code Point (DSCP) value in the IP header. This value can range between 0x0 and 0x3F, and defaults to 0x0F.
Note  The Differentiated Services (DS) field of a packet contains 6 bits that represents the DSCP value. Out of these 6 bits, five of them represent the DSCP. Hence, you can assign upto 32 DSCPs for various priorities. The Differentiated Services (DS) field of a packet contains 6 bits that represents the DSCP value. Out of these 6 bits, five of them represent the DSCP. Hence, you can assign upto 32 DSCPs for various priorities.
|
Registration Life Time |
The amount of time (in seconds) that an A10 connection can exist before its registration expires. This time can be any value between 1 and 65534, and defaults to 1800 seconds. |
New Call Policy |
The call policy for one or all the services, which can be any one of the following: • Reject Reject • None None This field defaults to None. |
Challenge Window |
The number of challenges that can be handled by the FA. |
Dynamic MIP Key Update |
The status of the Dynamic Mobile IP Key update feature. This option is disabled by default. |
Ignore Stale Challenge |
The status of the Ignore Stale Challenge in MIP RRQ. This option is disabled by default. |
Ignore MIP Key Data |
The status of the Ignore MIP Key data. This option is disabled by default. |
Allow Private Address Without Reverse Tunnel |
Indicates whether the mobile node can use reverse tunnel for a private address. This option is disabled by default. |
Registration Timeout |
The amount of time (in seconds) for the registration reply timeout. |
Idle Timeout Mode |
The idle timeout method, which can be any one of the following: • Normal Normal • Aggressive Aggressive |
Reverse Tunnel |
Indicates whether reverse tunneling is applicable for client mobile IP sessions. This option is enabled by default. |
Limit Registration Time |
Indicates whether MIP registration lifetime is shorter than session idle, absolute, and long-duration timeouts. By default, this option is enabled. |
Maximum Challenge Length |
The maximum length of the FA challenge. |
Optimize Tunnel Reassembly |
Indicates whether tunnel reassembly is optimized for fragmented large packets passed between HA and FA. By default, this option is disabled. |
MN-AAA Removal Indication |
Indicates whether the FA can remove MN-FAC and MN-AAA extensions from RRQs. By default, this option is disabled. |
You can also view the following configuration details for a Foreign Agent service:
• Advertisement—Foreign agents advertise their presence on their attached links by periodically multicasting or broadcasting messages called agent advertisements. Mobile nodes listen to these advertisements and determine if they are connected to their home link or foreign link. Rather than waiting for agent advertisements, an MN can also send an agent solicitation. This solicitation forces any agents on the link to immediately send an agent advertisement.
Advertisement—Foreign agents advertise their presence on their attached links by periodically multicasting or broadcasting messages called agent advertisements. Mobile nodes listen to these advertisements and determine if they are connected to their home link or foreign link. Rather than waiting for agent advertisements, an MN can also send an agent solicitation. This solicitation forces any agents on the link to immediately send an agent advertisement.
• Authentication—Authentication verifies users before they are allowed access to the network and network services.
Authentication—Authentication verifies users before they are allowed access to the network and network services.
• GRE—Generic routing encapsulation (GRE) is a tunneling protocol used by Mobile IP. The GRE tunnel interface creates a virtual point-to-point link between two routers at remote points over an IP internetwork. If the GRE for Cisco Mobile Networks feature is enabled, the mobile router will request GRE encapsulation in the registration request only if the FA advertises that it is capable of GRE encapsulation (the G bit is set in the advertisement). If the registration request is successful, packets will be tunneled using GRE encapsulation. If the GRE for Cisco Mobile Networks feature is enabled and the mobile router is using collocated care-of address (CCoA), the mobile router will attempt to register with the HA using GRE encapsulation. If the registration request is successful, packets will be tunneled using GRE encapsulation.
GRE—Generic routing encapsulation (GRE) is a tunneling protocol used by Mobile IP. The GRE tunnel interface creates a virtual point-to-point link between two routers at remote points over an IP internetwork. If the GRE for Cisco Mobile Networks feature is enabled, the mobile router will request GRE encapsulation in the registration request only if the FA advertises that it is capable of GRE encapsulation (the G bit is set in the advertisement). If the registration request is successful, packets will be tunneled using GRE encapsulation. If the GRE for Cisco Mobile Networks feature is enabled and the mobile router is using collocated care-of address (CCoA), the mobile router will attempt to register with the HA using GRE encapsulation. If the registration request is successful, packets will be tunneled using GRE encapsulation.
• HA Configurations—Once the mobile node roams to a new network, it must register with the home agent as being away from home. Its registration is sent by way of the Foreign Agent (FA), the router providing service on the foreign network. A security association between the home agent (HA) and the foreign agent (FA) is mandatory.
HA Configurations—Once the mobile node roams to a new network, it must register with the home agent as being away from home. Its registration is sent by way of the Foreign Agent (FA), the router providing service on the foreign network. A security association between the home agent (HA) and the foreign agent (FA) is mandatory.
• Proxy Mobile IP—Proxy Mobile IP supports Mobile IP for wireless nodes without requiring specialized software for those devices. The wireless access point acts as a proxy on behalf of wireless clients that are not aware of the fact that they have roamed onto a different Layer 3 network. The access point handles the IRDP communications to the foreign agent and handles registrations to the home agent.
Proxy Mobile IP—Proxy Mobile IP supports Mobile IP for wireless nodes without requiring specialized software for those devices. The wireless access point acts as a proxy on behalf of wireless clients that are not aware of the fact that they have roamed onto a different Layer 3 network. The access point handles the IRDP communications to the foreign agent and handles registrations to the home agent.
• Registration Revocation—Registration Revocation is a method by which a mobility agent (one that provides Mobile IP services to a mobile node) can notify the other mobility agent of the termination of a registration due to administrative reasons or MIP handoff. When a mobile changes its point of attachment (FA), or needs to terminate the session administratively, the HA sends a registration revocation message to the old FA. The old FA tears down the session and sends a registration revocation acknowledgement message to the HA. Additionally, if the PDSN/FA needs to terminate the session administratively, the FA sends a registration revocation message to the HA. The HA deletes the binding for the mobile, and sends a registration revocation acknowledgement to FA.
Registration Revocation—Registration Revocation is a method by which a mobility agent (one that provides Mobile IP services to a mobile node) can notify the other mobility agent of the termination of a registration due to administrative reasons or MIP handoff. When a mobile changes its point of attachment (FA), or needs to terminate the session administratively, the HA sends a registration revocation message to the old FA. The old FA tears down the session and sends a registration revocation acknowledgement message to the HA. Additionally, if the PDSN/FA needs to terminate the session administratively, the FA sends a registration revocation message to the HA. The HA deletes the binding for the mobile, and sends a registration revocation acknowledgement to FA.
Viewing the Advertisement Configuration Details
To view the Advertisement configuration details for a foreign agent:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > Advertisement. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > Advertisement. The details are displayed in the content pane.
Table 26-40 displays the Advertisement configuration details.
Table 26-40 Advertisement Configuration Details
|
|
|
Advertisement Delay |
The time delay (in milliseconds) for the first advertisement for a WiMax call. This time can be any value between 10 and 5000, and defaults to 1000. |
Advertisement Interval |
The advertisement interval time (in milliseconds). This time can be any value between 100 and 1800000, and defaults to 5000 milliseconds. |
Advertisement Life Time |
The maximum registration life time (in seconds) of the advertisement. This time can be any value between 1 and 65535, and defaults to 600 seconds. |
Number of Advertisements Sent |
The number of initial agent advertisements sent. This number can be any value between 1 and 65535, and defaults to 5. |
Prefix Length Extension |
Indicates whether the service address of the FA must be included in the Router Address field of the agent advertisement. If this field is set to Yes, then a prefix-length extension is appended to the router address field. By default, this option is set to No. |
Viewing the Authentication Configuration Details
To view the Authentication configuration details for a foreign agent:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > Authentication. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > Authentication. The details are displayed in the content pane.
Table 26-41 displays the Authentication configuration details.
Table 26-41 Authentication Configuration Details
|
|
|
MN AAA Authentication Policy |
The MN AAA Authentication policy, which can be any one of the following: • Ignore-after-handoff Ignore-after-handoff • Init-reg Init-reg • Init-reg-except-handoff Init-reg-except-handoff • Always Always • Renew-reg-noauth Renew-reg-noauth • Renew-and-dereg-noauth Renew-and-dereg-noauth This field defaults to Always. |
MN HA Authentication Policy |
The policy to authenticate Mobile Node HA in the RRP, which can be any one of the following: • Always Always • Allow-noauth Allow-noauth This field defaults to Allow-noauth. |
AAA Distributed MIP Keys Override |
Indicates whether the AAA distributed MIP Keys Override option is enabled. In other words, if this feature is enabled, then the authentication parameters for the FA service will override the dynamic keys from AAA with static keys.
Note  This feature supports those MIP registrations with an HA that does not support dynamic keys. This feature supports those MIP registrations with an HA that does not support dynamic keys.
|
MN AAA Optimized Retries |
Indicates whether the authentication request must be sent to the AA for each re-registration. |
Viewing the GRE Configuration Details
To view the Generic Routing Encapsulation (GRE) configuration details for a foreign agent:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > GRE. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > GRE. The details are displayed in the content pane.
Table 26-42 displays the GRE configuration details.
Table 26-42 GRE Configuration Details
|
|
|
Checksum |
Indicates whether the Checksum feature is enabled in outgoing GRE packets. By default, this option is disabled. |
GRE Encapsulation |
Indicates whether GRE is used when establishing a Mobile IP session. If this option is enabled, the FA requests HA to use GRE when establishing a MIP session. If this option is disabled, the FA will not set the GRE bit in agent advertisements to the mobile node. |
Checksum Verify |
Indicates whether the checksum field must be verified in the incoming GRE packets. By default, this option is disabled. |
Reorder Timeout |
The maximum time (in milliseconds) to wait before processing the GRE packets that are out of sequence. This time can be any value between 0 and 5000, and defaults to 100 milliseconds. |
Sequence Mode |
The mode used to handle the incoming out-of-sequence packets, which can be any one of the following: • Reorder Reorder • None None This field defaults to None. |
Sequence Numbers |
Indicates whether GRE sequence numbers must be inserted into the data that is about to be transmitted over the A10 interface. This option is disabled by default. |
Viewing the HA Configuration Details
To view the HA configuration details for a foreign agent:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > HA. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > HA. The details are displayed in the content pane.
Table 26-43 displays the HA configuration details.
Table 26-43 HA Configuration Details
|
|
|
HA Monitoring |
The HA monitoring status of the FA. This option is disabled by default. |
AAA-HA Override |
Indicates whether AAA HA can override Mobile Node during call establishment for HA assignment. |
Dynamic HAFailover |
Indicates whether failover during call establishment for Home Agent assignment is allowed. |
HA Monitor Interval |
The time interval (in seconds) to send HA monitoring requests. This time can be any value between 1 and 36000, and defaults to 30 seconds. |
HA Monitor Maximum Inactivity Time |
The maximum amount of time (in seconds) when there is no MIP traffic between FA and HA, which triggers the HA monitoring feature. This time can be any value between 30 and 600, and defaults to 60 seconds. |
HA Monitor Retry Count |
The number of times HA monitoring requests are sent before deciding that the HA is not reachable. This count can be any value between 0 and 10, and defaults to 5. |
FA SPI List Name |
The name of the SPI list linked with the FA service and configured for the selected context. Clicking on this link will take you to the relevant list under the SPI node. |
IKE |
Peer HA Address |
The IP address of the peer home agent. |
Crypto Map Name |
The IKE crypto map for the peer home agent. |
SPI |
SPI Number |
The unique SPI number that indicates a security context between the services. This number can be any value between 256 and 4294967295. |
Remote Address |
The IP address of the source service, which is expressed either in the IPv4 dotted decimal notation or IPv6 colon separated notation. |
Hash Algorithm |
The hash algorithm used between the source and destination services. |
Time Stamp Tolerance |
The acceptable time difference (in seconds) in timestamps, which can be any value between 0 and 65535.
Note  If the actual timestamp difference exceeds the value here, then the session is rejected. If this value is 0, then the timestamp tolerance checking is disabled at the receiving end. If the actual timestamp difference exceeds the value here, then the session is rejected. If this value is 0, then the timestamp tolerance checking is disabled at the receiving end.
|
Replay Protection |
The replay protection scheme that is implemented by the service. |
Description |
The description of the SPI. |
Net Mask |
The net mask for the IP address of the SPI. This field defaults to 255.255.255.255. |
HA Monitor |
Indicates whether HA monitoring is enabled. |
Viewing the Proxy Mobile IP Configuration Details
To view the Proxy Mobile IP configuration details for a foreign agent:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > Proxy Mobile IP. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > Proxy Mobile IP. The details are displayed in the content pane.
Table 26-44 displays the Proxy Mobile IP configuration details.
Table 26-44 Proxy Mobile IP Configuration Details
|
|
|
Proxy MIP |
Indicates the status of the Proxy Mobile IP. |
Encapsulation Type |
The data encapsulation type to be used in PMIP call for specific FA services, which can be any one of the following: • IPIP IPIP • GRE GRE This field defaults to IPIP. |
HA Failover |
The failover status of the FA. This option is disabled by default. |
HA Failover Max Attempts |
The maximum number of times for HA Failover. This can be any value between 1 and 10, and defaults to 4. |
HA Failover Timeout |
The timeout (in seconds) for the HA failover. This time can be any value between 1 and 50, and defaults to 2. |
HA Failover Attempts Before Switching |
The number of times HA Failover was attempted, before switching over to an alternate HA. This can be any value between 1 and 5, and defaults to 2. |
HA Failover Reply Code Trigger |
The action to be taken on receipt of the configured reject code. |
Max Retransmissions |
The maximum number of times the FA is allowed to retransmit Proxy Mobile IP registration requests to the HA. This number can be any value between 1 and 4294967295, and defaults to 5. |
Retransmission Timeout |
The retransmission timeout (in seconds) for Proxy Mobile IP messages on event of failover. This time can be any value between 1 and 100, and defaults to 3. |
Renew Time |
The percentage of lifetime at which point the renewal is sent. This percent can be between 0 and 100, and defaults to 75. |
Viewing the Registration Revocation Configuration Details
To view the Registration Revocation configuration details for a foreign agent:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > Registration Revocation. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > Registration Revocation. The details are displayed in the content pane.
Table 26-45 displays the Registration Revocation configuration details.
Table 26-45 Registration Revocation Configuration Details
|
|
|
Registration Revocation State |
Indicates the status of the registration revocation. If this feature is enabled, then the FA can send a revocation message to the HA when revocation is negotiated with the HA and MIP binding is terminated. This feature is disabled by default. |
Revocation IBit |
The status of the Ibit on the registration revocation. If this feature is enabled, the FA can negotiate the Ibit via PRQ/RRP messages and process the Ibit revocation messages. This feature is disabled by default. |
Internal Failure |
Indicates whether a revocation message must be sent to the HA for those sessions that are affected by internal task failure. |
Revocation Maximum Retries |
The maximum number times a revocation message must be retransmitted before failure. This value can be any value between 0 and 10, and defaults to 3. |
Revocation Timeout |
The time period (in seconds) to wait for an acknowledgement from the HA before the revocation message is retransmitted. This time can be any value between 1 and 10, and defaults to 3. |
Configuration Commands for Foreign Agent
To enable Mobile IP services on your network, you must determine which home agents will facilitate the tunneling for selected IP address, and where these devices or router will be allowed to roam. The areas, or subnets, into which the hosts are allowed to roam determine where foreign agent services need to be set up.
The foreign agent commands allow you to configure foreign agents in your network. Please note that these commands are available only for Cisco ASR 5000 Mobile devices.
These commands can be launched from the logical inventory by choosing the Context > Commands > Configuration or Context > Commands > Show.
Before executing any commands, you can preview them and view the results. If desired, you can also schedule the commands.
Note  You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
Note  In the GUI, parameters that are displayed in bold text are mandatory.
In the GUI, parameters that are displayed in bold text are mandatory.
Table 26-46 lists the Foreign Agent configuration commands.
Table 26-46 Foreign Agent Configuration Commands
|
|
|
|
Create FA |
Right-click on a context > Commands > Configuration |
Use this command to create a new foreign agent service for the selected context. |
Modify FA Delete FA |
Expand FA node > right-click FA service > Commands > Configuration |
Use these commands to modify/delete an existing foreign agent service configured for the selected context. |
Show FA |
Expand FA node > right-click FA service > Commands > Show |
Use this command to view and confirm the foreign agent configuration details. |
Create SPI |
Expand FA node > right-click FA service > Commands > Configuration |
Use this command to configure Security Parameter Index (SPI) for a foreign agent service. |
Modify SPI Delete SPI |
Expand FA node > expand FA service node > HA Configuration > right-click on SPI Number in content pane > Commands > Configuration |
Use these commands to modify and delete an existing SPI configured for a foreign agent service. |
Create IKE |
Expand FA node > right-click FA service > Commands > Configuration |
Use this command to configure Internet Key Exchange (IKE) for a foreign agent service. If foreign agent reverse tunneling creates a tunnel that transverses a firewall, any mobile node that knows the addresses of the tunnel endpoints can insert packets into the tunnel from anywhere in the network. It is recommended to configure Internet Key Exchange (IKE) or IP Security (IPSec) to prevent this. |
Modify IKE Delete IKE |
Expand FA node > expand FA service node > HA Configuration > right-click on IKE Number in content pane > Commands > Configuration |
Use these commands to modify and delete an existing IKE configured for a foreign agent service. |
Modify Advertisement |
Expand FA node > FA service > right-click Advertisement > Commands > Configuration |
Use this command to modify the advertisement configuration settings specified for a foreign agent. |
Modify Authentication |
Expand FA node > FA service > right-click Authentication > Commands > Configuration |
Use this command to modify the authentication configuration settings specified for a foreign agent. |
Modify GRE |
Expand FA node > FA service > right-click GRE > Commands > Configuration |
Use this command to modify the Generic Routing Encapsulation (GRE) configuration settings specified for a foreign agent. |
Modify HA Configuration |
Expand FA node > FA service > right-click HA Configuration > Commands > Configuration |
Use this command to modify the Home Agent configuration settings specified for a foreign agent. |
Modify Proxy Mobile IP |
Expand FA node > FA service > right-click Proxy Mobile IP > Commands > Configuration |
Use this command to modify the Proxy Mobile IP configuration settings specified for a foreign agent. |
Modify Registration Revocation |
Expand FA node > FA service > right-click Registration Revocation > Commands > Configuration |
Use this command to modify the Registration revocation configuration settings specified for a foreign agent. |
Monitoring Evolved Packet Data Gateway (ePDG)
In today's market, there are multiple access networks for mobile technologies. For example, the following access networks are available for 3rd Generation Partnership Project (3GPP) network:
• General Packet Radio Service (GPRS). See GPRS/UMTS Networks - An Overview.
General Packet Radio Service (GPRS). See GPRS/UMTS Networks - An Overview.
• Global System for Mobile communication (GSM)
Global System for Mobile communication (GSM)
• Universal Mobile Telecommunication System (UMTS). See GPRS/UMTS Networks - An Overview.
Universal Mobile Telecommunication System (UMTS). See GPRS/UMTS Networks - An Overview.
The following access network are available for Non-3GPP network:
• Worldwide Interoperability for Microwave Access (WiMAX)
Worldwide Interoperability for Microwave Access (WiMAX)
• CDMA2000
CDMA2000
• Wireless local area network (WLAN)
Wireless local area network (WLAN)
• Fixed networks
Fixed networks
The Non-3GPP networks can be categorized into two—Trusted and Untrusted. While the trusted non-3GPP networks can interact directly with the Evolved Packet Core (EPC), the untrusted networks are required to pass through a security gateway to gain access to the EPC. This security gateway is called the Evolved Packet Data Gateway or ePDG.
When a user transmits data to the EPC using an untrusted non-3GPP network access, the ePDG must act as a termination node of IPSec tunnels established with the user equipment and secure the data being sent. Figure 26-12 shows the ePDG architecture.
Figure 26-12 ePDG Architecture
IP Security (IPSec)
Internet Protocol Security or IPSec is a protocol suite that interacts with one another to provide secure private communications across IP networks. These protocols allow the system to establish and maintain secure tunnels with peer security gateways. In accordance with the following standards, IPSec provides a mechanism for establishing secure channels from mobile subscribers to pre-defined end points (such as enterprise or home networks):
• RFC 2401, Security Architecture for the Internet Protocol
RFC 2401, Security Architecture for the Internet Protocol
• RFC 2402, IP Authentication Header (AH)
RFC 2402, IP Authentication Header (AH)
• RFC 2406, IP Encapsulating Security Payload (ESP)
RFC 2406, IP Encapsulating Security Payload (ESP)
• RFC 2409, The Internet Key Exchange (IKE)
RFC 2409, The Internet Key Exchange (IKE)
• RFC-3193, Securing L2TP using IPSEC, November 2001
RFC-3193, Securing L2TP using IPSEC, November 2001
IPSec can be implemented for the following applications:
• PDN Access: Subscriber IP traffic is routed over an IPSec tunnel from the system to a secure gateway on the packet data network (PDN) as determined by access control list (ACL) criteria.
PDN Access: Subscriber IP traffic is routed over an IPSec tunnel from the system to a secure gateway on the packet data network (PDN) as determined by access control list (ACL) criteria.
• Mobile IP: Mobile IP control signals and subscriber data is encapsulated in IPSec tunnels that are established between foreign agents (FAs) and home agents (HAs) over the Pi interfaces.
Mobile IP: Mobile IP control signals and subscriber data is encapsulated in IPSec tunnels that are established between foreign agents (FAs) and home agents (HAs) over the Pi interfaces.
IKEv2 and IPSec Encryption
ePDG supports Internet Key Exchange Version 2 (IKEv2) and IP Security Encapsulating Security Payload (IPSec ESP) encryption over IPv4 transport. The IKEv2 and IPSec encryption takes care of network domain security for all IP packet switched networks. It uses cryptographic techniques to ensure ensures confidentiality, integrity, authentication, and anti-replay protection.
ePDG Security
In Prime Network, the following security services are available for ePDG:
• Crypto template—Used to define the IKEv2 and IPSec policies. In other words, it includes IKEv2 and IPSec parameters for keepalive, lifetime, NAT-T and cryptographic and authentication algorithms.
Crypto template—Used to define the IKEv2 and IPSec policies. In other words, it includes IKEv2 and IPSec parameters for keepalive, lifetime, NAT-T and cryptographic and authentication algorithms.
• EAP Profile—Defines the EAP authentication method and associated parameters.
EAP Profile—Defines the EAP authentication method and associated parameters.
• Transform Set—Define the negotiable algorithms for IKE SAs (Security Associations) and Child SAs to enable calls to connect to the ePDG.
Transform Set—Define the negotiable algorithms for IKE SAs (Security Associations) and Child SAs to enable calls to connect to the ePDG.
Viewing the Crypto Template Service Details
To view the Crypto template details:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Security Association > Crypto Template. The list of crypto templates are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Security Association > Crypto Template. The list of crypto templates are displayed in the content pane.
Step 3  In the Crypto Template node, choose the crypto template. The template details are displayed in the content pane. Figure 26-13 displays the crytpo template details.
In the Crypto Template node, choose the crypto template. The template details are displayed in the content pane. Figure 26-13 displays the crytpo template details.
Figure 26-13 Crypto Template Details
Table 26-47 displays the Crypto template details.
Table 26-47 Crypto Template Details
|
|
|
Template Name |
The unique name of the template. |
Control Don't Fragment |
The Don't Fragment (DF) bit in the IPSec tunnel data packet, which is encapsulated in the IPSec headers at both ends. The values for this field are: • clear-bit—Clear DF Bit clear-bit—Clear DF Bit • copy-bit—Copy DF bit from inner header copy-bit—Copy DF bit from inner header • set-bit—Set DF Bit set-bit—Set DF Bit This field defaults to copy-bit. |
Cookie Challenge-Detect DOS Attack |
The cookie challenge parameters for the crypto template, which is used to prevent malicious Denial of Service (DOS) attacks against the server.
Note  This feature prevents DOS attacks by sending a challenge cookie. If the response from the sender does not incorporate the expected cookie data, the packets are dropped. This feature prevents DOS attacks by sending a challenge cookie. If the response from the sender does not incorporate the expected cookie data, the packets are dropped.
|
Notify Payload - Half Open Session Start |
The initial count of the number of half-open sessions per IPSec manager. Transmission of information will start only when the number of half-open sessions currently open exceed the starting count.
Note  A session is considered half open if a Packet Data Interworking Function (PDIF) has responded to an IKEv2 INIT request with an IKEv2 INIT response, but no further messages were received on the particular IKE SA. A session is considered half open if a Packet Data Interworking Function (PDIF) has responded to an IKEv2 INIT request with an IKEv2 INIT response, but no further messages were received on the particular IKE SA.
|
Notify Payload - Half Open Session End |
The maximum count of half open sessions per IPSec manager. Transmission of information will stop when the number of half-open sessions currently open is less than this count. |
Authentication Local |
The local gateway key used for authentication. |
Authentication Remote |
The remote gateway key used for authentication. |
Keepalive Interval |
The period of time (in seconds) that must elapse before the next keepalive request is sent. |
Keepalive Retries |
The period of time (in seconds) that must elapse before the keepalive request is resent. |
Keepalive Timeout |
The keepalive time (in terms of seconds) for dead peer detection. |
Maxchild SA Count |
The maximum number of child SA per IKEv2 policy, which can be any value between 1 and 4. |
Maxchild SA Overload Action |
The action to be taken when the specified soft limit for the maximum number of SA is reached, which can be any one of the following: Ignore—The IKEv2 stack ignores the specified soft limit for the SA and allows new SA to be created. Terminate—The IKEv2 stack does not allow new child SA to be created when the specified soft limit is reached. |
NAI CustomIDr |
The unique user specified identification number to be used in the crypto template for Network Access Identifier (NAI). |
Crypto Template Payloads |
Payload Instance |
The payload instance configured for the crypto template. |
Payload Name |
The unique name of the crypto template payload. |
Ignore Rekeying Requests |
Indicates whether IKESA rekeying requests must be ignored. |
IP Address Allocation |
The IP Address Allocation scheme configured for the crypto template payload. |
Lifetime |
The lifetime (in seconds) for the IPSec Child Security Associations derived from the crypto template. |
Lifetime (KB) |
The lifetime (in kilo bytes) for the IPSec Child Security Associations derived from the crypto template. |
Maximum Child SA |
The maximum number of IPSec Child Security Associations (SA) that may be derived from a single IKEv2 IKE SA. |
Rekey |
Indicates whether IPSec Child Security Association rekeying must be enabled, after approximately 90% of the child SA lifetime has expired. |
Rekey Keepalive |
Indicates whether rekeying must be allowed if data is not received on the security association since the last rekey. |
TSI Start Address |
The IKEv2 Initiator Traffic Selector payload start address configured for the crypto template. |
TSI End Address |
The IKEv2 Initiator Traffic Selector payload end address configured for the crypto template. |
TSR Start Address |
The IKEv2 Responder Traffic Selector payload start address. |
TSR End Address |
The IKEv2 Responder Traffic Selector payload end address. |
Crypto Template IKESAs |
IKESA Instance |
The IKESA instance configured for the crypto template. |
Allow Empty IKESA |
Indicates whether empty IKESA is allowed. By default, empty IKESA is not allowed. |
Certificate Sign |
The certificate sign to be used. This field defaults to pkcs1.5. |
Ignore Notify Protocol ID |
Indicates whether the IKEv2 Exchange Notify Payload Protocol-ID values must be ignored for strict RFCA 4306 compliance. |
Ignore Rekeying Requests |
Indicates whether IKESA rekeying requests must be ignored. |
Keepalive User Activity |
Indicates whether the user inactivity timer must be reset when keepalive messages are received from the peer. |
Max Retransmission |
The maximum number of retransmissions of an IKEv2 IKE exchange request that is allowed if a response is not received. |
Policy Congestion Rejection Notify Status |
Indicates whether an error notification message must be sent in response to an IKE_SA INIT exchange, when IKESA sessions cannot be established anymore. |
Policy Error Notification |
Indicates whether an error notification message must be sent for invalid IKEv2 exchange message ID and syntax. |
Rekey |
Indicates whether IKESA rekeying must occur before the configured lifetime expires (which is approximately at 90% of the lifetime interval). By default, rekeying is not allowed. |
Retransmission Timeout |
The time period (in milliseconds) that must elapse before a retransmission of an IKEv2 IKE exchange request is sent when a corresponding response is not received. |
Setup Timer |
The number of seconds before a IKEv2 security association, which is not fully established, is terminated. |
Viewing the EAP Profile Details
To view the EAP Profile details:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Security Association > EAP Profile. The list of profiles are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Security Association > EAP Profile. The list of profiles are displayed in the content pane.
Step 3  In the EAP Profile node, choose the profile. The profile details are displayed in the content pane.
In the EAP Profile node, choose the profile. The profile details are displayed in the content pane.
Table 26-48 displays the EAP Profile details.
Table 26-48 EAP Profile Details
|
|
|
Name |
The unique name of the EAP Profile. |
Mode |
The operative mode of the EAP profile, which can be any one of the following: • Authenticator Pass Through—Indicates that the EAP Authentication Requests must be passed to an external EAP Server. Authenticator Pass Through—Indicates that the EAP Authentication Requests must be passed to an external EAP Server. • Authenticator Terminate—Indicates that the EAP must act as an EAP Authentication Server. Authenticator Terminate—Indicates that the EAP must act as an EAP Authentication Server. |
Authentication Method |
The EAP Authentication method to be used for the profile, which can be any one of the following: • If the Mode is Authenticator Pass Through: If the Mode is Authenticator Pass Through: – eap-aka eap-aka – eap-gtc eap-gtc – eap-md5 eap-md5 – eap-sim eap-sim – eap-tls eap-tls • If the Mode is Authenticator Terminate: If the Mode is Authenticator Terminate: – eap-gtc eap-gtc – eap-md5 eap-md5 |
Viewing the Transform Set Details
To view the Transform Set details for IKEv2 IPSec/IKEv2:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Security Association > Transform Set > IKEv2 IPSec Transform Set or IKEv2 Transform set. The list of profiles are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Security Association > Transform Set > IKEv2 IPSec Transform Set or IKEv2 Transform set. The list of profiles are displayed in the content pane.
Step 3  In the IKEv2 IPSec Transform Set or IKEv2 Transform set node, choose the transform set. The relevant details are displayed in the content pane.
In the IKEv2 IPSec Transform Set or IKEv2 Transform set node, choose the transform set. The relevant details are displayed in the content pane.
Table 26-49 displays the IKEv2 IPSec Transform set or IKEv2 Transform set details.
Table 26-49 IKEv2 IPSec Transform Set/IKEv2 Transform set Details
|
|
|
Name |
The name of the transform set. |
DH Group |
The Diffie-Hellman (DH) group for the transform set, which can be any one of the following: • 1—Configure Diffie-Hellman Group 1:768-bit MODP Group 1—Configure Diffie-Hellman Group 1:768-bit MODP Group • 14—Configure Diffie-Hellman Group 14:2048-bit MODP Group 14—Configure Diffie-Hellman Group 14:2048-bit MODP Group • 2—Configure Diffie-Hellman Group 2:1024-bit MODP Group 2—Configure Diffie-Hellman Group 2:1024-bit MODP Group • 5—Configure Diffie-Hellman Group 5:1536-bit MODP Group 5—Configure Diffie-Hellman Group 5:1536-bit MODP Group This field defaults to 2—Configure Diffie-Hellman Group 2:1024-bit MODP Group.
Note  The DH group is used to determine the length of the base Prime numbers used during the key exchange process in IKEv2. The cryptographic strength of any key derived, depends in part, on the strength of the DH group upon which the prime numbers are based. The DH group is used to determine the length of the base Prime numbers used during the key exchange process in IKEv2. The cryptographic strength of any key derived, depends in part, on the strength of the DH group upon which the prime numbers are based.
|
Cipher |
The appropriate encryption algorithm and encryption key length for the IKEv2 IKE security association, which can be any one of the following: • 3des-cbc 3des-cbc • aes-cbc-128 aes-cbc-128 • aes-cbc-256 aes-cbc-256 • des-cbc des-cbc • Null Null This field defaults to AESCBC-128. |
HMAC |
The Hash Message Authentication Code (HMAC) for the IKEv2 IPSec transform set,which can be any one of the following: • aes-xcbc-96 aes-xcbc-96 • md5-96 md5-96 • sha1-96 sha1-96 • sha2-256-128 sha2-256-128 • sha2-384-192 sha2-384-192 • sha2-512-256 sha2-512-256 This field defaults to sha1-96.
Note  HMAC is a type of message authentication code calculated using a cryptographic hash function in combination with a secret key to verify both data integrity and message authenticity. A hash takes a message of any size and transforms it into a message of fixed size (the authenticator value), which is truncated and transmitted. HMAC is a type of message authentication code calculated using a cryptographic hash function in combination with a secret key to verify both data integrity and message authenticity. A hash takes a message of any size and transforms it into a message of fixed size (the authenticator value), which is truncated and transmitted.
|
Mode |
The encapsulation mode for the transform set, which can be any one of the following: • transport transport • tunnel tunnel |
PRF |
The Pseudo-random Function (PRF) for the transform set, which can be any one of the following: • aes-xcbc-128 aes-xcbc-128 • md5 md5 • sha1 sha1 • sha2-256 sha2-256 • sha2-384 sha2-384 • sha2-512 sha2-512 This field defaults to SHA1. This field is applicable only for IKEv2 transform sets.
Note  This function is used to generate keying material for all cryptographic algorithms. It produces a string of bits that cannot be distinguished from random bit strings without the secret key. This function is used to generate keying material for all cryptographic algorithms. It produces a string of bits that cannot be distinguished from random bit strings without the secret key.
|
Life Time |
The time period for which the secret keys used for various aspects of a configuration is valid (before it times out). This field is applicable only for IKEv2 transform sets. |
Viewing the ePDG Configuration Details
To view the ePDG configuration details:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > EPDG. The list of EPDG services configured in Prime Network are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > EPDG. The list of EPDG services configured in Prime Network are displayed in the content pane.
Step 3  From the EPDG node, choose an EPDG service. The EPDG service details are displayed in the content pane.
From the EPDG node, choose an EPDG service. The EPDG service details are displayed in the content pane.
Table 26-50 displays the EPDG service details.
Table 26-50 EPDG Service Details
|
|
|
Service Name |
The unique name of the ePDG service. |
Status |
The status of the ePDG service, which can be any one of the following: • Initiated Initiated • Running Running • Down Down • Started Started • Nonstarted Nonstarted |
IP Address |
The IPV4 address of the ePDG service. |
UDP Port |
The User Datagram Protocol (UDP) port of the ePDG service. |
Crypto Template |
The name of the IKEv2 crypto template to be used by the ePDG service. This template is used to define the cryptographic policy for the ePDG service. |
Max Sessions |
The maximum number of sessions allowed for the ePDG service. |
PLMN ID |
The unique identification code of the Public Land Mobile Network (PLMN) for the ePDG service. This id is made up of the Mobile Country Code (MCC) and the Mobile Network Code (MNC). |
MAG Service Context |
The name of the context where the Mobile Access Gateway (MAG) services are configured. If a MAG service is not configured for the ePDG service, then one of the MAG services defined in the context is selected. |
MAG Service |
The name of the MAG service that handles the mobile IPv6 sessions. |
Setup Timeout |
The maximum time (in seconds) allowed for the session setup. |
DNS PGWClient Context |
The name of the context where the Domain Name System (DNS) client is configured for the Packet Data Network Gateway (PWG) selection. |
DNS PGW Selection |
The criteria to select a PGW service from the DNS. This criteria is based on the topology and/or weight from the DNS. |
FQDN |
The Fully Qualified Domain Name (FQDN), which is used for longest suffix match during dynamic allocation. |
PGW Selection Agent Info Error Action |
The action to be taken when the expected MIP6 agent information is not received from Authentication, Authorization, and Accounting (AAA) or Hosting Solution Software (HSS). |
User Name MAC Address Stripping |
Indicates whether the MAC address in the username obtained from the user equipment must be stripped. |
User Name MAC Address Validation |
Indicates whether the MAC address in the username obtained from the user equipment must be validated. |
User Name MAC Address Validation Failure Action |
Indicates the action that must be taken on failure of the validation of the MAC address in the user name obtained from the user equipment. |
New Call Policy |
Indicates the busy-out policy that must be followed to reject the incoming calls from individual users. |
Configuration Commands for ePDG
The ePDG commands allow you to configure ePDG services in your network. Please note that these commands are available only for Cisco ASR 5000 Mobile devices.
These commands can be launched from the logical inventory by choosing the Context > Commands > Configuration or Context > Commands > Show.
Before executing any commands, you can preview them and view the results. If desired, you can also schedule the commands.
Note  You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
Note  In the GUI, parameters that are displayed in bold text are mandatory.
In the GUI, parameters that are displayed in bold text are mandatory.
Table 26-51 lists the ePDG configuration commands.
Table 26-51 ePDG Configuration Commands
|
|
|
|
Create ePDG Service |
Right-click context > Commands > Configuration > |
Use this command to create a new ePDG service. |
Modify ePDG Service |
Expand EPDG Node > right-click EPDG service > Commands > Configuration |
Use this command to modify the configuration details for an ePDG service. |
Delete ePDG Service |
Expand EPDG Node > right-click EPDG service > Commands > Configuration |
Use this command to delete an ePDG service. |
Show ePDG Service |
Expand EPDG Node > right-click EPDG service > Commands > Show |
Use this command to view and confirm the configuration details of an ePDG Service. |
Monitoring Packet Data Serving Node
Packet Data Serving Node, or PDSN, is a component of the Code Division Multiple Access (CDMA) 2000 mobile network. It acts as a connection point between the Radio Access Network (RAN) and IP Network. PDSN also manages PPP sessions between the mobile provider's core IP network and the mobile node.
In other words, it provides access to the Internet, intranets, and applications servers for mobile stations that utilize a CDMA2000 RAN. Acting as an access gateway, PDSN provides simple IP and mobile IP access, foreign agent support, and packet transport for virtual private networking. It acts as a client for Authentication, Authorization, and Accounting (AAA) servers and provides mobile stations with a gateway to the IP network.
PDSN Configurations
The following paragraphs list the different configurations for PDSN:
• Simple IP—In this protocol, the mobile user is assigned an IP address dynamically. The user can use this IP address within a defined geographical area, which is lost when the user moves out of the area. If the user moves out of the designated area, they must register with the service provider again to obtain a new IP address. Figure 26-14 depicts the working of this protocol.
Simple IP—In this protocol, the mobile user is assigned an IP address dynamically. The user can use this IP address within a defined geographical area, which is lost when the user moves out of the area. If the user moves out of the designated area, they must register with the service provider again to obtain a new IP address. Figure 26-14 depicts the working of this protocol.
Figure 26-14 Simple IP configuration for PDSN
• Mobile IP—In this protocol, the mobile user is assigned a static or dynamic IP address, which is basically the "home address" assigned by the user's Home Agent (HA). Even if the user moves out of the home network, the IP address does not change or is not lost. This enables the user to use applications that require seamless mobility such as transferring files. How does this work? The Mobile IP protocol provides a network-layer solution that allows mobile nodes to receive IP packets from their home network even when they are connected to a visitor network. The PDSN in the visitor's network performs as a Foreign Agent (FA), which assigns a Care-of-Address (CoA) to the mobile node and establishes a virtual session with the mobile node's HA. IP packets are encapsulated into IP tunnels and transported between the FA, HA and mobile node. Figure 26-15 depicts the working of this protocol.
Mobile IP—In this protocol, the mobile user is assigned a static or dynamic IP address, which is basically the "home address" assigned by the user's Home Agent (HA). Even if the user moves out of the home network, the IP address does not change or is not lost. This enables the user to use applications that require seamless mobility such as transferring files. How does this work? The Mobile IP protocol provides a network-layer solution that allows mobile nodes to receive IP packets from their home network even when they are connected to a visitor network. The PDSN in the visitor's network performs as a Foreign Agent (FA), which assigns a Care-of-Address (CoA) to the mobile node and establishes a virtual session with the mobile node's HA. IP packets are encapsulated into IP tunnels and transported between the FA, HA and mobile node. Figure 26-15 depicts the working of this protocol.
Figure 26-15 Mobile IP Configuration for PDSN
• Proxy Mobile IP—This protocol provides a mobility solution for subscribers whose mobile nodes do not support the Mobile IP protocol. On behalf of the mobile node, PDSN proxies the Mobile IP tunnel with the HA. In turn, the service provider or the home agent assigns an IP address to the subscriber. This IP address does not change or is not lost even if the user moves out of the home network.
Proxy Mobile IP—This protocol provides a mobility solution for subscribers whose mobile nodes do not support the Mobile IP protocol. On behalf of the mobile node, PDSN proxies the Mobile IP tunnel with the HA. In turn, the service provider or the home agent assigns an IP address to the subscriber. This IP address does not change or is not lost even if the user moves out of the home network.
Viewing the PDSN Configuration Details
To view the PDSN configuration details:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN. The list of PDSN services configured in Prime Network are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN. The list of PDSN services configured in Prime Network are displayed in the content pane.
Step 3  From the PDSN node, choose a PDSN service. The PDSN service details are displayed in the content pane as shown in Figure 26-16.
From the PDSN node, choose a PDSN service. The PDSN service details are displayed in the content pane as shown in Figure 26-16.
Figure 26-16 PDSN Service Details
Table 26-52 displays the PDSN service details.
Table 26-52 PDSN Service Details
|
|
|
Service Name |
The unique name of the PDSN service. |
Status |
The status of the PDSN service, which can be any one of the following: • Initiated Initiated • Running Running • Down Down • Started Started • Nonstarted Nonstarted • Unknown Unknown |
Bind Address |
The IP address to which the service is bound. This can be a IPv4 or IPv6 address.
Note  Multiple IP addresses belonging to the same IP interface can be bound to different PDSN services, but one address can be bound to only one service. Multiple IP addresses belonging to the same IP interface can be bound to different PDSN services, but one address can be bound to only one service.
|
Local IP Port |
The User Datagram Protocol (UDP) port for the R-P interface of the IP socket. This IP port can be any value between 1 and 65535 and defaults to 699. |
Mobile IP |
The IP address of the Foreign agent that is configured for the PDSN service. |
Simple IP |
Indicates whether the Simple IP configuration is available for the PDSN service, which can be any one of the following: • Allowed Allowed • Not Allowed (default value) Not Allowed (default value) |
Max Subscribers |
The maximum number of subscribers that the PDSN service can support. |
Registration Life Time |
The registration lifetime configured for all the subscribers to the service. |
Max Retransmissions |
Maximum retries for transmitting RP control packets. This count can be any value between 1 and 1000000 and defaults to 5. |
A11 Signalling Packets IP Header DSCP |
The Differential Services Code Point (DSCP) value in the IP header. |
NAI Construction Domain |
The Network Access Identifier for the PDSN service. This field is made up of the Mobile Station Identifier (MSID) of the subscriber, a separator character and a domain name.
Note  The domain name used here can be either the name supplied as part of the subscriber's name or the domain alias. The domain name used here can be either the name supplied as part of the subscriber's name or the domain alias.
|
Airlink Bad Sequence Number |
The action to be taken when the PDSN receives an airlink record with a bad sequence number, which can be any one of the following: • Accept (default value) Accept (default value) • Reject Reject
Note  At the time of the R-PA10 connection setup, an airlink record is assigned a unique sequence number. At the time of the R-PA10 connection setup, an airlink record is assigned a unique sequence number.
|
Airlink Bad Sequence Number Deny Code |
The reason for rejecting the airlink record with a bad sequence number, which can be any one of the following: • Poorly Formed Request Poorly Formed Request • Unsupported Vendor ID Unsupported Vendor ID |
AAA 3GPP2 Service Option |
The service options for which AAA 3GPP2 authentication is applicable. |
Service Option Entries |
Service Option Number |
The service option numbers applicable for the PDSN service.
Note  Each service option relates to a standard data service. Hence, these numbers determine the data services that are supported by the PDSN service. Each service option relates to a standard data service. Hence, these numbers determine the data services that are supported by the PDSN service.
|
You can also view the following configuration details for a PDSN service:
• GRE
GRE
• IP Source Violation
IP Source Violation
• MSID
MSID
• PCF
PCF
• Policy
Policy
• PPP
PPP
• QoS
QoS
• Registrations
Registrations
• Timers and Restrictions
Timers and Restrictions
Viewing the GRE Configuration Details
To view the Generic Routing Encapsulation (GRE) configuration details for a PDSN service:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > GRE. The GRE details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > GRE. The GRE details are displayed in the content pane.
Table 26-53 displays the GRE configuration details.
Table 26-53 GRE Configuration Details
|
|
|
Checksum |
Indicates whether the Checksum field is applicable for outgoing GRE packets.By default, this option is disabled. |
Checksum Verify |
Indicates whether the verification of the Checksum field is enabled for incoming GRE packets. |
Reorder Time Out |
The maximum time (in milliseconds) for processing the GRE packets that are coming out of order. This time can be any value between 0 and 5000, and defaults to 100 milliseconds. |
Sequence Mode |
The mode in which incoming out-of-sequence GRE packets are handled, which can be any one of the following: • Reorder Reorder • None None This field defaults to None. |
Sequence Numbers |
Indicates whether GRE sequence numbers are inserted in data that is about to be transmitted over the A10 interface. By default, this option is disabled. |
Flow Control |
Indicates whether flow control is supported by the selected PDSN service. If this option is enabled, PDSN sends flow control enabled Normal Vendor Specific Extensions (NSVE) in A11 RRPs. By default, this option is disabled. |
Flow Control Time Out |
The amount of time (in milliseconds) to wait for an Transmitter On (XON) indicator from the RAN. This time can be any value between 1 and 1000000, and defaults to 1000 milliseconds. |
Flow Control Action |
The action that must be taken when the timeout limit is reached, which can be any one of the following: • disconnect-session disconnect-session • resume-session. resume-session. |
Protocol Type |
The tunnel type for the GRE routing. This field defaults to Any. |
Is 3GPP Ext Header QoS Marking |
Indicates whether the 3GPP Extension Header QoS Marking is enabled for the selected PDSN feature.
Note  If this feature is enabled and the PCF negotiation feature is enabled in A11 RRQ, then the PDSN will include QoS optional data attribute in the GRE 3GPP2 Extension Header. If this feature is enabled and the PCF negotiation feature is enabled in A11 RRQ, then the PDSN will include QoS optional data attribute in the GRE 3GPP2 Extension Header.
|
IP Header DSCP Value |
The Differential Service Code Point (DSCP) value in the IP header that marks the GRE IP Header encapsulation. This can be any value between 0x0F and 0X3F, and defaults to 0X0F. |
IP Header DSCP Value Packet Type |
Indicates whether the IP Header DSCP Value packet type is specified for the packets. By default, this option is disabled. |
GRE Segmentation |
Indicates whether segmentation of GRE packets is enabled. By default, this option is disabled. |
Viewing the IP Source Violation Details
A Source violation occurs when a mobile device sources packets to the PDSN with a IP address that is different from the one specified during setup. Using this feature, the packets that need not be sent over the network are dropped when it tries to pass through PDSN.
To view the IP Source Violation configuration details for a PDSN service:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > IP Source Violation. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > IP Source Violation. The details are displayed in the content pane.
Table 26-54 displays the IP Source Violation configuration details.
Table 26-54 IP Source Violation Configuration Details
|
|
|
Clear on Valid Packet |
Indicates whether the service to reset the negotiation and drop limit counters upon receipt of properly addressed packet is enabled. By default, this feature is disabled. |
Drop Limit |
The maximum number of IP source violations within the detection period, before the call is dropped. This number can be any value between 0 and 1000000, and defaults to 10. |
Period |
The detection period (in seconds) for the IP source violation. This field can be any value between 1 and 1000000, and defaults to 120. |
Renegotiation Limit |
The maximum number of IP source violations within the detection period before renegotiating PPP for the call. This field can be any value between 1 and 1000000, and defaults to 5. |
Viewing the MSID Configuration Details
To view the Mobile Station ID (MSID) configuration details for a PDSN service:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > MSID. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > MSID. The details are displayed in the content pane.
Table 26-55 displays the MSID configuration details.
Table 26-55 MSID Configuration Details
|
|
|
MSID Length Max |
The maximum length of the MSID configured for the PDSN service. This length can be any value between 10 and 15, and defaults to 15. |
MSID Length Min |
The minimum length of the MSID configured for the PDSN service. This length can be any value between 10 and 15, and defaults to 10. |
MSID Authentication |
Indicates whether the MSID authentication feature is enabled. |
MSID Length Check |
Indicates whether MSID length is enabled for the PDSN service. By default, this option is disabled.
Note  This configuration is required to reject the A11-RRQs with illegal International Mobile Station Identification (IMSI). This configuration is required to reject the A11-RRQs with illegal International Mobile Station Identification (IMSI).
|
Viewing the PCF Configuration Details
To view the Packet Control Function (PCF) configuration details for a PDSN service:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > PCF. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > PCF. The details are displayed in the content pane.
Table 26-56 displays the PCF configuration details.
Table 26-56 PCF Configuration Details
|
|
|
PCF Monitor Num Retries |
The maximum number of retries before deciding that the PCF service is down. |
PCF Session ID Change Restart PPP |
Indicates whether the PPP must be restarted if there is a change in the session ID of an existing session. |
New Call Conflict Terminate Old Session |
Indicates whether the session with a PCF must be terminated when a new call request for an existing session is received from another PCF. |
PDSN Security Entries |
SPI Number |
The unique Security Parameters Index number that indicates a security context between the services. |
Remote Address |
The IP address of the source service. |
Netmask |
The subnet mask of the source service. |
Zone ID |
The ID of the zone to which the IP address belongs to. |
Hash Algorithm |
The hash algorithm used to encrypt the data. |
Time Stamp Tolerance |
The acceptable difference (in seconds) in the timestamps.
Note  If the actual difference exceeds the difference specified here, then the session is rejected. If this difference is 0, the timestamp tolerance checking is disabled at the receiving end. If the actual difference exceeds the difference specified here, then the session is rejected. If this difference is 0, the timestamp tolerance checking is disabled at the receiving end.
|
Replay Protection |
The replay protection schemes that is implemented by the service. |
Description |
The description of the security profile. |
Viewing the Policy Configuration Details
To view the Policy configuration details for a PDSN service:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > Policy. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > Policy. The details are displayed in the content pane.
Table 26-57 displays the Policy configuration details.
Table 26-57 Policy Configuration Details
|
|
|
Unknown CVSE Policy |
Indicates whether the unknown Critical Vendor Specific Extension (CVSE) policy is enforced. |
RRQ MEI From Current PCF |
Indicates whether PPP must be restarted after getting MEI in RRQ. |
New Call Policy |
The call policy for one or all the services, which can be any one of the following: • Accept Accept • Reject Reject • Redirect Redirect • Reject on MSID Reject on MSID • Redirect on MSID Redirect on MSID • None None This field defaults to None. |
Overload Policy |
The action to be taken by the PDSN service in case of an overload condition. |
Overload Policy Reject Code |
The reject code for the overload policy. |
Service Option Policy |
The policy followed by PDSN for configuring services. |
Reject MSID |
The Mobile Station Identifier (MSID) for which new calls are rejected.
Note  If the New Call Policy field is set to Reject MSID, then this field will display the relevant MSID. If the New Call Policy field is set to Reject MSID, then this field will display the relevant MSID.
|
Viewing the PPP Configuration Details
To view the Point-to-Point Protocol details for a PDSN service:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > PPP. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > PPP. The details are displayed in the content pane.
Table 26-58 displays the PPP configuration details.
Table 26-58 PPP Configuration Details
|
|
|
Context Name |
The destination context where the Layer 2 Tunneling protocol Access Concentrator (LAC) service is configured.
Note  This context is the same as the PPP tunneling context. This context is the same as the PPP tunneling context.
|
Tunnel Type |
The type of the PPP tunnel established between the PDSN and the PFC, which can be any one of the following values: • L2TP L2TP • None None This field defaults to None. |
Fragment State |
Indicates whether the PPP fragmentation is enabled. By default, this is option is disabled. |
Alt PPP |
Indicates whether the Alternate Point-to-Point (PPP) protocol sessions are enabled for the PDSN service. By default, this option is disabled. |
Allow No Authentication |
Indicates whether subscribers can gain network access even if they have not been authenticated. |
Authentication |
The authentication mode and priority when multiple modes are selected, which can be any one of the following: • chap—Uses the Challenge Handshake Authentication Protocol (CHAP) for authentication. Must be followed by a priority value, which can be any value between 0 and 1000 with a lower number indicating higher preference. This protocol is enabled by default and commands the highest priority. chap—Uses the Challenge Handshake Authentication Protocol (CHAP) for authentication. Must be followed by a priority value, which can be any value between 0 and 1000 with a lower number indicating higher preference. This protocol is enabled by default and commands the highest priority. • mschap—Uses the Microsoft Challenge Handshake Authentication Protocol (MS-CHAP) for authentication. Must be followed by a priority value, which can be any value between 0 and 1000 with a lower number indicating higher preference. This protocol is disabled by default. mschap—Uses the Microsoft Challenge Handshake Authentication Protocol (MS-CHAP) for authentication. Must be followed by a priority value, which can be any value between 0 and 1000 with a lower number indicating higher preference. This protocol is disabled by default. • pap—Uses Password Authentication Protocol (PAP) for authentication. Must be followed by a priority value, which can be any value between 0 and 1000 with a lower number indicating higher preference. This protocol seconds CHAP in terms of priority. This protocol is enabled by default. pap—Uses Password Authentication Protocol (PAP) for authentication. Must be followed by a priority value, which can be any value between 0 and 1000 with a lower number indicating higher preference. This protocol seconds CHAP in terms of priority. This protocol is enabled by default. |
Viewing the QoS Configuration Details
To view the Quality of Service configuration details for a PDSN service:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > QoS. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > QoS. The details are displayed in the content pane.
Table 26-59 displays the QoS configuration details.
Table 26-59 QoS Configuration Details
|
|
|
Policy Mismatch |
Indicates whether the PDSN must raise a Traffic FLow Template (TFT) violation if there is a policy mismatch of QoS. |
Qos Wait |
Indicates whether parameters related to QoS are enabled.
Note  While configuring parameters for QoS, the minimum and maximum waiting time for transmission are also specified. Also, the action to be performed when the minimum time elapses is also specified. While configuring parameters for QoS, the minimum and maximum waiting time for transmission are also specified. Also, the action to be performed when the minimum time elapses is also specified.
|
Associate |
The unique identification number of the associated QoS Profile that is configured for the selected context. |
QoS Profile tab |
ID |
The unique code of the QoS profile. |
Description |
The description of the QoS profile. |
Uplink Bandwidth |
The uplink bandwidth (in kbps) of your profile. |
Downlink Bandwidth |
The downlink bandwidth (in kbps) of your profile. |
Latency |
The latency (in milliseconds) of the profile. |
Drop Rate |
The maximum drop rate percent of the packet. |
QoS Class |
The type of QoS class associated with the profile. |
Viewing the Registration Details
To view the Registration details for a PDSN service:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > Registrations. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > Registrations. The details are displayed in the content pane.
Table 26-60 displays the Registration details.
Table 26-60 Registration Details
|
|
|
Accept Session Disconnect In Progress |
Indicates whether A11 registration request messages must be accepted from the PCF when a session disconnection is in progress. |
Ask Deny Terminate Session on Error |
Indicates whether A11 sessions must be terminated when a registration acknowledgement is received from PCF with an error status. |
Max Deny Reply Limit |
Maximum number of retries for an erroneous registration request message from PCF, before PDSN terminates the session. |
Deny Mismatched COA Address |
Indicates whether RP Requests must be denied, when the Care of Address field does not match the source address of the requests. |
Deny New Call Connection Setup Record Absent |
Indicates whether new calls that do not have airlink connection setup record in the RRQ must be denied. |
Deny New Call Connection Setup Record Absent Deny Code |
The reason for denying new calls that do not have airlink connection setup record in RRQ. |
Deny New Call Connection Reverse Tunnel Unavailable |
Indicates whether new calls whose GRE key is the same as that of another user must be denied. |
Deny Session Already Active |
Indicates whether renew requests that have Airlink Start record for already active R-P sessions must be denied. |
Deny Session Already Closed |
Indicates whether renew and de registration requests for closed R-P sessions must be denied. |
Deny Session Already Dormant |
Indicates whether renew requests that have Airlink Start record for already dormant R-P sessions must be renewed. |
Deny Terminate Session On Error |
Indicates whether termination of session on receipt of erroneous registration request message must be denied. |
Deny Use Zero GRE Key |
Indicates whether the GRE key must be initialized to 0 when denying a new R-P session. |
Discard Bad Extension |
Indicates whether A11 registration request messages containing bad extensions must be discarded. |
Discard GRE Key Change |
Indicates whether A11 registration request messages for an existing A11 session that contain a different GRE key must be discarded. |
Update Wait Timeout |
The time taken (in seconds) by A11 RRQ for QoS changes. |
Viewing the Timers and Restrictions Details
To view the Timers and Restrictions details for a PDSN service:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > Timers and Restrictions. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > Timers and Restrictions. The details are displayed in the content pane.
Table 26-61 displays the Timers and Restrictions details.
Table 26-61 Timers and Restrictions Details
|
|
|
Inter PDSN Handoff |
Indicates whether the Inter-PDSN handoff feature off is enabled. Inter-PDSN handoff relates to the handoff between two PCFs with connectivity to different PDSNs.
Note  Inter-PDSN handoff can be of two types: Fast Handoff and Dormant Handoff. Fast Handoff uses a GRE tunnel between two PDSNs to transport user data for a single service instance. Dormant Handoff occurs when a mobile station with a dormant packet session determines that it has crossed a packet zone boundary. Inter-PDSN handoff can be of two types: Fast Handoff and Dormant Handoff. Fast Handoff uses a GRE tunnel between two PDSNs to transport user data for a single service instance. Dormant Handoff occurs when a mobile station with a dormant packet session determines that it has crossed a packet zone boundary.
|
Inter PDSN Handover Use CANIDPANID |
Indicates whether usage of Current Access Network ID (CANID) or Previous Access Network ID (PAN) is supported during an Inter-PDSN handover. |
Data Available Indicator |
Indicates whether data transfer is available. |
PMA Capability Indicator |
The Proxy Mobile Agent capability (PMA) indicator, which determines whether PMIP is supported by Prime Network.
Note  PDSN sends the capability indicator through RADIUS to the AAA server as an access-request packet to indicate to the AAA server that PDSN supports PMIP. If the capability indicator attribute is missing, then PMIP is not supported by PDSN. PDSN sends the capability indicator through RADIUS to the AAA server as an access-request packet to indicate to the AAA server that PDSN supports PMIP. If the capability indicator attribute is missing, then PMIP is not supported by PDSN.
|
Direct LTE Indicator |
Indicates whether PDSN can send Direct LTE indicator in the Access Request. |
Data Over Signalling |
Indicates whether data transfer over a10 signalling channel instead of bearer or subscriber channels from PCF or PDSN is allowed. By default, this feature is not allowed. |
Dormant Transition |
Indicates whether dormant transition of the RP link during the initial setup of the subscriber session is allowed. If this option is disabled, then the subscriber session will be disconnected if the RP link becomes dormant during the initial setup. |
ROHC IP Header Compression |
Indicates whether the Robust Header Compression (ROHC) is enabled for headers in the IP packets that are being sent by or sent to the PDSN. By default, this option is disabled. |
Always On Indication |
Indicates whether the Always On feature is enabled for a subscriber.
Note  When the idle-time out limit runs out for a subscriber, the IP/PPP session remains connected as long as the subscriber is reachable. By default, this feature is disabled. When the idle-time out limit runs out for a subscriber, the IP/PPP session remains connected as long as the subscriber is reachable. By default, this feature is disabled.
|
Setup TimeOut |
The maximum time (in seconds) allowed for a session to be setup between PCF and PDSN. This time can be any value between 1 and 1000000, and defaults to 60 seconds. |
Retransmission TimeOut |
The timeout period (in seconds) for retransmission of RP control packets. This time can be any value between 1 and 1000000 and defaults to 3 seconds. |
Pdsn Type0 Tft |
Indicates whether Traffic Flow Template (TFT) of the PDSN is changed from type 0 TFT to type 1 TFT. |
Tft Validation TimeOut |
The TFT validation timeout (in seconds) for QoS changes. This time can be any value between 1 and 100000, and defaults to 0. |
Access Flow Traffic Violations |
The number of violations that are permitted in the access flow traffic. |
Access Flow Traffic Violations Interval |
The time interval between two subsequent access flow traffic violations. |
Configuration Commands for PDSN
The PDSN commands allow you to configure PDSNs in your network. Please note that these commands are available only for Cisco ASR 5000 Mobile devices.
These commands can be launched from the logical inventory by choosing the Context > Commands > Configuration or Context > Commands > Show.
Before executing any commands, you can preview them and view the results. If desired, you can also schedule the commands.
Note  You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
Note  In the GUI, parameters that are displayed in bold text are mandatory.
In the GUI, parameters that are displayed in bold text are mandatory.
Table 26-62 lists the PDSN configuration commands.
Table 26-62 PDSN Configuration Commands
|
|
|
|
Create PDSN |
Right-click on a context > Commands > Configuration |
Use this command to create a new PDSN service for the selected context. |
Modify PDSN Delete PDSN |
Expand PDSN node > right-click PDSN service > Commands > Configuration |
Use these commands to modify/delete an existing PDSN service configured for the selected context. |
Show PDSN |
Expand PDSN node > right-click PDSN service > Commands > Show |
Use this command to view and confirm the PDSN service configuration details. |
Modify GRE |
Expand PDSN node > PDSN service > right-click GRE > Commands > Configuration |
Use this command to modify the Generic Routing Encapsulation (GRE) configuration settings for a specified PDSN service. |
Modify IP Source Violation |
Expand PDSN node > PDSN service > right-click IP Source Violation > Commands > Configuration |
Use this command to modify the IP Source Violation configuration details for the specified PDSN service. |
Modify MSID |
Expand PDSN node > PDSN service > right-click MSID > Commands > Configuration |
Use this command to modify the mobile station ID (MSID) configuration details for the specified PDSN service. |
Modify PCF Parameters |
Expand PDSN node > PDSN service > right-click PCF > Commands > Configuration |
Use this command to modify the Packet Control Function (PCF) configuration details for the specified PDSN service. |
Create PCF Security Entry |
Expand the PDSN node > right-click PDSN service > Commands > Configuration |
Use this command to create a new PCF security entry. |
Modify PCF Security Entry Delete PCF Security Entry |
Expand PDSN node > PDSN service > PCF > Under Security Profiles tab n the content pane, right-click SPI Number > Commands > Configuration |
Use these commands to modify/delete the PCF security entry details. |
Modify Policy |
Expand PDSN node > PDSN service > right-click Policy > Commands > Configuration |
Use this command to modify the policy configuration details for the PDSN service. |
Modify PPP |
Expand PDSN node > PDSN service > right-click PPP> Commands > Configuration |
Use this command to modify the Point-to-Point Protocol configuration details for the selected PDSN service. |
Modify Registrations |
Expand PDSN node > PDSN service > right-click Registrations > Commands > Configuration |
Use this command to modify the registration details for the selected PDSN service. |
Modify Timers and Registrations |
Expand PDSN node > PDSN service > right-click Timers and Registrations > Commands > Configuration |
Use this command to modify the timers and registration details for the selected PDSN service. |
Viewing the Local Mobility Anchor Configuration
Proxy Mobile IPv6 (or PMIPv6, or PMIP) is a network-based mobility management protocol for building a common access technology independent of mobile core networks, accommodating various access technologies such as WiMAX, 3GPP, 3GPP2 and WLAN based access architectures.
The PMIPv6 provides network-based IP Mobility management to a mobile node, without requiring the participation of the MN in any IP mobility-related signaling. The mobility entities in the network track the movements of the MN, initiate the mobility signaling, and set up the required routing state.
The major functional entities of PMIPv6 are Mobile Access Gateways (MAGs), Local Mobility Anchors (LMAs), and Mobile Nodes (MNs).
The Local Mobility Anchor (LMA) is the home agent for a mobile node in a Proxy Mobile IPv6 (PMIPv6) domain. It is the topological anchor point for mobile node home network prefixes and manages the binding state of an mobile node. An LMA has the functional capabilities of a home agent as defined in the Mobile IPv6 base specification (RFC 3775) along with the capabilities required for supporting the PMIPv6 protocol.
To view the LMA configuration details:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > Context > Mobile > LMA. The list of LMA services configured in Prime Network is displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > LMA. The list of LMA services configured in Prime Network is displayed in the content pane.
Step 3  From the LMA node, choose an LMA service. The LMA service details are displayed in the content pane as shown in Figure 26-17.
From the LMA node, choose an LMA service. The LMA service details are displayed in the content pane as shown in Figure 26-17.
Figure 26-17 LMA Service Details
Table 26-63 displays the LMA service details.
Table 26-63 LMA Service Details
|
|
|
Service Name |
The unique service name of the LMA. |
Status |
The status of the LMA service, which can be any one of the following: • Down Down • Running Running • Initiated Initiated • Unknown. Unknown. This field defaults to Down. |
Local IPv6 Address |
The IP address of the interface serving as S2a (that is connected to HSGW) or S5/S8 (that is connected to S-GW) interface. |
Local IPv4 Address |
The IP address of the interface connected to HA/P-GW. |
Local IP Port |
The User Datagram Protocol (UDP) port for the LMA service. |
Max Subscribers |
The maximum number of subscribers that the LMA service can support. This number can be any value between 0 and 3000000. |
Default Subscriber Name |
The name of the subscriber template to be used for subscribers who are using this domain alias. |
Mobility Option Type Value |
The mobility option type used in mobility messages, which can be any one of the following: • Custom 1 Custom 1 • Custom 2 Custom 2 • Standard Standard |
Refresh Advice Option |
Indicates whether refresh advice option must be included in the Binding Acknowledgement sent by the LMA service. By default, this option is disabled. |
Refresh Interval |
The percent of granted lifetime to be used in the Refresh Interval Mobility option pertaining to the Binding Acknowledgement sent by the LMA service. This percentage can be any value between 1 and 99 and defaults to 75. |
Setup Timeout |
The maximum time (in seconds) allowed for the session to setup. This field defaults to 60. |
Lifetime |
The registration lifetime (in seconds) of the mobile IPv6 session. This number can be any value between 1 and 262140. |
Bind Revocation |
Indicates whether the binding revocation support is available for the LMA service. By default, this option is disabled. |
Bind Revocation Max Retries |
The maximum number of retries for the binding revocation, which can be any value between 1 and 10. This field defaults to 3. |
Bind Revocation Timeout |
The time interval (in milliseconds) of the retransmission of the binding revocation, which can be any value between 500 and 10000. This field defaults to 3000. |
Sequence Number Validation |
Indicates whether the sequence number of the MIPv6 control packet received by the LMA service must be validated. This option is enabled by default. |
Signalling Packet IP Header DSCP |
The Differentiated Services Code Point (DSCP) marking that is applicable to the IP header that is carrying outgoing signalling packets. |
Simultaneous Binding |
The maximum number of Care of addresses that can be bound for the same user as identified by their Network Access Identifier (NAI) and home address. This can be any value ranging from 1 to 3. This field defaults to 1. |
Standalone Mode |
Indicates whether the LMA service can be started in the standalone mode. This option is disabled by default. |
Timestamp Option Validation |
Indicates whether the Timestamp option in the Binding Acknowledgement must be validated. This option is disabled by default. |
Timestamp Tolerance |
The time (in seconds) to validate Timestamp reply protection, which can be any value between 0 and 65535. This field defaults to 7 seconds. |
AAA Accounting |
Indicates whether the AAA Accounting information for subscriber sessions must be sent. This option is enabled by default. |
New Call Policy |
Indicates whether the new call policy must be accepted or rejected. By default, this field is set to None. |
Viewing Operator Policies, APN Remaps, and APN Profiles
Operator policy provides mechanisms to fine tune the behavior of subsets of subscribers above and beyond the behaviors described in the user profile. It can also be used to control the behavior of visiting subscribers in roaming scenarios, enforcing roaming agreements, and providing a measure of local protection against foreign subscribers.
An operator policy associates APNs, APN profiles, an APN remap table, and a call-control profile to ranges of International Mobile Subscriber Identities (IMSIs). These profiles and tables are created and defined within their own configuration modes to generate sets of rules and instructions that can be reused and assigned to multiple policies. In this manner, an operator policy manages the application of rules governing the services, facilities, and privileges available to subscribers. These policies can override standard behaviors and provide mechanisms for an operator to get around the limitations of other infrastructure elements, such as DNS servers and HSSs.
Note  Operator policies and APN profiles are applicable only for the `local' context in the logical inventory.
Operator policies and APN profiles are applicable only for the `local' context in the logical inventory.
The following topics explain how to view operator policies, APN remaps, and APN profiles in Prime Network Vision:
• Viewing Operator Policies
Viewing Operator Policies
• Viewing APN Remaps
Viewing APN Remaps
• Viewing APN Profiles
Viewing APN Profiles
Viewing Operator Policies
Operator policies provide an operator with a range of control to manage the services, facilities, and privileges available to subscribers. By configuring the various components of an operator policy, the operator fine tunes any desired restrictions or limitations needed to control call handling and this can be done for a group of callers within a defined IMSI range or per subscriber.
Besides enhancing operator control through configuration, the operator policy feature minimizes configuration by drastically reducing the number of configuration lines needed. Operator policy maximizes configurations by breaking them into the following reusable components that can be shared across IMSI ranges or subscribers:
• Call-control profiles
Call-control profiles
• IMEI profiles (SGSN only)
IMEI profiles (SGSN only)
• APN profiles
APN profiles
• APN remap tables
APN remap tables
• Operator policies
Operator policies
• IMSI ranges
IMSI ranges
To view operator policies in logical inventory:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > local > Mobile > Policy > Operator Policies
In the logical inventory window, choose Logical Inventory > local > Mobile > Policy > Operator Policies
Prime Network Vision displays the list of operator policies configured under the container. You can view the individual policy details from the table on the right pane or by choosing Logical Inventory > local > Mobile > Policy > Operator Policies > Policy.
Table 26-64 describes the details available for each operator policy.
If an operator policy is configured with IMEI ranges and APN entries, the details are displayed in the respective tabs IMEI Ranges and APN Entries on the content pane.
Table 26-64 Operator Policies in Logical Inventory
|
|
|
Name |
Name of the operator policy. |
Description |
Description of the operator policy. |
Call Control Profile Name |
Name of the call control profile associated with the operator policy. |
Call Control Validity |
Indicates whether the call control profile name associated with the operator policy is valid or is not created yet (invalid). |
APN Remap Table Name |
Name of the APN remap table associated with the operator policy. |
APN Remap Table Validity |
Indicates whether the APN remap table name associated with the operator policy is valid or is not created yet (invalid). |
Default APN Profile Name |
Name of the default APN profile associated with the operator policy. |
Default APN Profile Validity |
Indicates whether the default APN profile name associated with the operator policy is valid or is not created yet (invalid). |
IMEI Ranges |
Start Range |
The starting number in the range of IMEI profiles. |
To Range |
The ending number in the range of IMEI profiles. |
Software Version |
Software version to fine tune the IMEI definition. |
Profile Name |
Name of the IMEI profile associated with the IMEI range. Displays `None', if no profile is associated with the range. |
Validity |
Validity of the IMEI profile. |
APN Entries |
NI |
APN network identifier. |
NI APN Profile |
Name of the APN profile associated with the network identifier. An APN profile groups a set of APN-specific parameters that may be applicable to one or more APNs. When a subscriber requests an APN that has been identified in a selected operator policy, the parameter values configured in the associated APN profile are applied. |
NI APN Profile Validity |
Indicates whether the NI APN profile associated with the operator policy is valid or is not created yet (invalid). |
OI |
APN operator identifier. |
OI APN Profile |
Name of the APN profile associated with the operator identifier. An APN profile groups a set of APN-specific parameters that may be applicable to one or more APNs. When a subscriber requests an APN that has been identified in a selected operator policy, the parameter values configured in the associated APN profile are applied. |
OI APN Profile |
Indicates whether the OI APN profile associated with the operator policy is valid or is not created yet (invalid). |
Viewing APN Remaps
An APN remap tables allow an operator to override an APN specified by a user, or the APN selected during the normal APN selection procedure, as specified by 3GPP TS 23.060. This level of control enables operators to deal with situations such as:
• An APN is provided in the activation request that does not match with any of the subscribed APNs; either a different APN was entered or the APN could have been misspelled. In such situations, the SGSN rejects the activation request. It is possible to correct the APN, creating a valid name so that the activation request is not rejected.
An APN is provided in the activation request that does not match with any of the subscribed APNs; either a different APN was entered or the APN could have been misspelled. In such situations, the SGSN rejects the activation request. It is possible to correct the APN, creating a valid name so that the activation request is not rejected.
• In some cases, an operator might want to force certain devices or users to use a specific APN. For example, a set of mobile users may need to be directed to a specific APN. In such situations, the operator needs to override the selected APN.
In some cases, an operator might want to force certain devices or users to use a specific APN. For example, a set of mobile users may need to be directed to a specific APN. In such situations, the operator needs to override the selected APN.
An APN remap table group is a set of APN-handling configurations that may be applicable to one or more subscribers. When a subscriber requests an APN that has been identified in a selected operator policy, the parameter values configured in the associated APN remap table are applied. For example, an APN remap table allows configuration of the following:
• APN aliasing—Maps incoming APN to a different APN, based on partial string match (MME and SGSN) or matching charging characteristic (SGSN only).
APN aliasing—Maps incoming APN to a different APN, based on partial string match (MME and SGSN) or matching charging characteristic (SGSN only).
• Wildcard APN—Allows APN to be provided by the SGSN, when wildcard subscription is present and the user has not requested an APN.
Wildcard APN—Allows APN to be provided by the SGSN, when wildcard subscription is present and the user has not requested an APN.
• Default APN—Allows a configured default APN to be used, when the requested APN cannot be used.
Default APN—Allows a configured default APN to be used, when the requested APN cannot be used.
APN remap tables are configured with commands in the APN Remap Table configuration mode. A single APN remap table can be associated with multiple operator policies, but an operator policy can only be associated with a single APN remap table.
To view APN remap properties in logical inventory:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > local > Mobile > > Profile > APN Remaps
In the logical inventory window, choose Logical Inventory > local > Mobile > > Profile > APN Remaps
Prime Network Vision displays the list of APN remaps configured under the container. You can view the individual APN remap details from the table on the right pane or by choosing Logical Inventory > local > Mobile > Profile > APN Remaps > APN Remap.
Table 26-65 describes the details available for each APN remap.
If an APN remap is configured with charging characteristics and NI and OI entries, the details are displayed in the respective tabs Charging Characteristics and Network And Operator Identifier Entries on the content pane.
Table 26-65 APN Remap Properties in Logical Inventory
|
|
|
Name |
Name of the APN remap. |
Description |
Description of the APN remap. |
APN When No APN Requested |
APN network identifier that will be used when no APN is requested. |
Wildcard APN for IPv4 |
Wildcard APN included in the subscriber record, with PDP type as IPv4 context. |
Wildcard APN for IPv6 |
Wildcard APN included in the subscriber record, with PDP type as IPv6 context. |
Wildcard APN for IPv4v6 |
Wildcard APN included in the subscriber record, with PDP type as both IPv4 and IPv6 contexts. |
Wildcard APN for PPP |
Wildcard APN included in the subscriber record, with PDP type as PPP context. |
Charging Characteristics |
Profile Index |
Profile index in charging characteristics. |
Behavior Bit Value |
Behavior bit in charging characteristics. |
APN For Overriding |
Name of the APN profile that the charging characteristic attributes must be applied to, to generate CDRs. |
Network And Operator Identifier Entries |
Requested NI |
The old network identifier that is being mapped for replacement. |
Mapped to NI |
The new network identifier. |
NI Wildcard Replace String |
When a wildcard character is included in the old APN network identifier, this parameter identifies the information to replace the wildcard in the new APN network identifier. |
Requested OI |
The old operator identifier that is being mapped for replacement. |
Mapped to OI |
The new operator identifier. |
OI MNC Replace String |
When a wildcard character is included in the MNC portion of the old APN operator identifier, this parameter identifies the information to replace the wildcard in the new APN operator identifier. |
OI MCC Replace String |
When a wildcard character is included in the MCC portion of the old APN operator identifier, this parameter identifies the information to replace the wildcard in the new APN operator identifier. |
Step 3  If a default APN is configured for the remap, click the Default APN node under the APN remap. You can view the following details on the content pane.
If a default APN is configured for the remap, click the Default APN node under the APN remap. You can view the following details on the content pane.
Table 26-66 Default APN Properties in Logical Inventory
|
|
|
Default APN Name |
Name of the default APN. |
Use Default APN When No APN is Requested |
Indicates whether the configured default APN can be used or not, if there is no APN in the request. |
Use Default APN When DNS Query Fails |
Indicates whether the configured default APN can be used or not, if DNS query fails. |
Fallback APN to Use |
A fallback APN to be used when the configured default APN is not present in the subscription, so that activation does not fail. |
Fallback APN in First Subscription |
Indicates whether APN from the first subscription record must be used, when the configured default APN is not available. |
Use APN From Single Subscription Record |
Indicates whether APN from the subscription record must be used, if it is the only record available and the normal APN selection fails. |
Viewing APN Profiles
APN Profile defines a set of parameters controlling the SGSN or MME behavior, when a specific APN is received or no APN is received in a request. An APN profile is a key element in the Operator Policy feature. An APN profile is not used or valid unless it is associated with an APN and this association is specified in an operator policy.
Essentially, an APN profile is a template which groups a set of APN-specific commands that may be applicable to one or more APNs. When a subscriber requests an APN that has been identified in a selected operator policy, then the set of commands in the associated APN profile will be applied. The same APN profile can be associated with multiple APNs and multiple operator policies.
An APN profile groups a set of APN-specific parameters that may be applicable to one or more APNs. When a subscriber requests an APN that has been identified in a selected operator policy, the parameter values configured in the associated APN profile are applied. For example:
• Enable or disable a direct tunnel (DT) per APN (SGSN).
Enable or disable a direct tunnel (DT) per APN (SGSN).
• Define charging characters for calls associated with a specific APN.
Define charging characters for calls associated with a specific APN.
• Identify a specific GGSN to be used for calls associated with a specific APN (SGSN).
Identify a specific GGSN to be used for calls associated with a specific APN (SGSN).
• Define various quality of service (QoS) parameters to be applied to calls associated with a specific APN.
Define various quality of service (QoS) parameters to be applied to calls associated with a specific APN.
• Restrict or allow PDP context activation on the basis of access type for calls associated with a specific APN.
Restrict or allow PDP context activation on the basis of access type for calls associated with a specific APN.
A single APN profile can be associated with multiple operator policies.
To view APN profile properties in logical inventory:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > local > Mobile > Profile > APN Profiles.
In the logical inventory window, choose Logical Inventory > local > Mobile > Profile > APN Profiles.
Prime Network Vision displays the list of APN profiles configured under the container. You can view the individual APN profile details from the table on the right pane or by choosing Logical Inventory > local > Mobile > Profile > APN Profiles > APN Profile.
Table 26-67 describes the details available for each APN remap.
If additional properties are configured for the APN profile, you can click the respective tabs on the content pane to view the details:
– Gateway Entries
Gateway Entries
– RANAP ARP Entries
RANAP ARP Entries
– QoS Class Entries
QoS Class Entries
– Uplink Traffic Policing Entries/Downlink Traffic Policing Entries
Uplink Traffic Policing Entries/Downlink Traffic Policing Entries
Table 26-67 APN Profile Properties in Logical Inventory
|
|
|
Name |
Name of the APN profile. |
Description |
Description of the APN profile. |
QoS Service Capping Prefer Type |
Operational preferences for QoS parameters, specifically QoS bit rates. Value could be one of the following: • both-hlr-and-local—Instructs the SGSN to use the locally configured QoS or HLR subscription. both-hlr-and-local—Instructs the SGSN to use the locally configured QoS or HLR subscription. • hlr-subscription—Instructs the SGSN to use QoS bit rate from HLR configuration and use the same for session establishment. hlr-subscription—Instructs the SGSN to use QoS bit rate from HLR configuration and use the same for session establishment. • local—Instructs the SGSN to use the locally configured QoS bit rate and use the same for session establishment. local—Instructs the SGSN to use the locally configured QoS bit rate and use the same for session establishment. |
Address Resolution Mode |
Address resolution mode of the APN profile, which could be one of the following: • fallback-for-dns—Uses DNS query for address resolution. fallback-for-dns—Uses DNS query for address resolution. • local—Uses locally configured address. local—Uses locally configured address. |
CC Preferred Source |
Charging characteristic settings to be used for S-CDRs, which could be one of the following: • hlr-value-for-scdrs—Instructs the system to use charging characteristic settings received from the HLR for S-CDRs. hlr-value-for-scdrs—Instructs the system to use charging characteristic settings received from the HLR for S-CDRs. • local-value-for-scdrs—Instructs the profile preference to use only locally configured/stored charging characteristic settings for S-CDRs. local-value-for-scdrs—Instructs the profile preference to use only locally configured/stored charging characteristic settings for S-CDRs. |
CC Local SCDR Behavior Bit |
Value of the behavior bit for the charging characteristics for S-CDRs. |
CC Local SCDR Behavior Profile Index |
Value of the profile index for the charging characteristics for S-CDRs. |
GGSN Algorithm Applicable |
Selection algorithm for GGSNs. This parameter allows the operator to configure multiple GGSN pools by assigning the GGSN to a secondary pool of GGSNs. |
IP Source Validation |
Configures settings related to IP source violation detection with one of the following criteria: • deactivate—Deactivates the PDP context with one of the following conditions: deactivate—Deactivates the PDP context with one of the following conditions: – Deactivates all PDP contexts of the MS/UE. Default is to deactivate errant PDP contexts. Deactivates all PDP contexts of the MS/UE. Default is to deactivate errant PDP contexts. – Excludes packets having an invalid source IP address from the statistics used in the accounting records. Excludes packets having an invalid source IP address from the statistics used in the accounting records. – Deactivates all assosiated PDP contexts (primary/secondary). Default is to deactivate errant PDP contexts. Deactivates all assosiated PDP contexts (primary/secondary). Default is to deactivate errant PDP contexts. – Configures maximum number of allowed IP source violations before the session is deactivated. Configures maximum number of allowed IP source violations before the session is deactivated. • discard—Discards errant packets and excludes packets having an invalid source IP address from the statistics used in the accounting records. discard—Discards errant packets and excludes packets having an invalid source IP address from the statistics used in the accounting records. • ignore—Ignores checking of packets for MS/UE IP source violation. ignore—Ignores checking of packets for MS/UE IP source violation. |
IP Source Validation Tolerance Limit |
Maximum number of allowed IP source violations before the session is deactivated. |
Direct Tunnel |
Permission for direct tunnel establishment by GGSNs, which could be not-permitted-by-ggsn or remove. |
Private Extension LORC IE to GGSN |
Indicates whether GTPC private extension is enabled or not for the over charging protection feature of the GGSN. |
Private Extension LORC IE to SGSN |
Indicates whether GTPC private extension is enabled or not for the over charging protection feature of the SGSN. |
Idle Mode Access Control List IPV4 |
Group of IPv4 Access Control Lists (ACLs) that define rules to apply to downlink data destined for UEs in an idle mode. |
Idle Mode Access Control List IPV6 |
Group of IPv6 ACLs that define rules to apply to downlink data destined for UEs in an idle mode. |
DNS Query with MSISDN Start Offset Position |
The position of the first digit in the MSISDN to start an offset and create a new APN DNS query string that is intended to assist roaming subscribers to use the local GGSN. |
DNS Query with MSISDN End Offset Position |
The position of the last digit in the MSISDN to be part of the offset. |
DNS Query with LAC or RAC |
Indicates whether geographical information must be appended to the APN string that is sent to the DNS query or not. This information is used during the DNS query process to select the geographically closest GGSN. |
DNS Query with RNC ID |
Indicates whether the SGSN must include the ID of the calling RNC in the APN DNS query string or not. |
DNS Query with Charging Characteristics |
Indicates whether charging characteristic configuration is enabled for the APN profile or not. |
DNS Query Charging Characteristics ID Format |
Format of the charging characteristic information to be included. |
Gateway Entries |
Gateway Entry |
Gateway entry configured for the APN profile. |
IP Address |
IPv4 or IPv6 addresses of the gateway configured. |
Priority |
Priority of the gateway to consider during address selection. |
Weight |
Weightage or importance assigned to the gateway for load balancing. |
Pool |
Gateway pool assigned. |
Gateway Type |
Type of gateway configured, which could be GGSN or P-GW. |
RANAP ARP Entries |
Traffic Class |
Traffic class of the Radio Access Network Application Part (RANAP) configuration. |
Subscription Priority |
Subscription priority of the traffic class; the lowest number denoting the highest priority. |
Priority Level |
Priority level for the subscription priority. |
Preemption Capability |
Preemption capability value of the traffic class. |
Preemption Vulnerability |
Preemption vulnerability value of the traffic class. |
Queuing Allowed |
Indicates whether queuing is allowed for the traffic class or not. |
QoS Class Entries |
Class Name |
Traffing class of the QoS configuration. |
Service Delivery Unit Delivery Order |
Indicates whether bearer should provide in-sequence delivery of service data units (SDUs) or not. |
Delivery of Erroneous Service Delivery Units |
Indicates whether SDUs detected as erroneous should be delivered or discarded. |
Max Bit Rate Uplink |
Maximum bit rate, in kbps, allowed for uplink between MS and the core network. |
Max Bit Rate Downlink |
Maximum bit rate, in kbps, allowed for downlink between MS and the core network. |
Allocation Retention Priority |
Relative importance compared to other Radio Access Bearers (RABs) for allocation and retention of the RAB. |
Traffic Handling Priority |
Relative importance for traffic handling when compared to other RABs. |
SDU Max Size |
Maximum allowed SDU size, in bytes. |
SDU Error Ratio |
Fraction of SDUs lost or detected as erroneous. |
Guaranteed Bit Rate Uplink |
Uplink bit rate, in kbps, that is assured for a given RAB between MS and the core network. |
Guaranteed Bit Rate Downlink |
Downlink bit rate, in kbps, that is assured for a given RAB between MS and the core network. |
Minimum Transfer Delay |
Minimum transfer delay, in milliseconds. |
Residual BER |
Undetected bit error ratio (BER) in the delivered SDUs. |
MBR Map Down |
Attribute that maps or converts the received HLR maximum bit rate (MBR) (from value) to a locally configured downlink MBR value (to value). |
MBR Map Up |
Attribute that maps or converts the received HLR MBR (from value) to a locally configured uplink MBR value (to value). |
Uplink Traffic Policing Entries/Downlink Traffic Policing Entries |
Traffic Class |
Traffic class of the QoS configuration. |
Burst Size Auto Readjust |
Indicates whether the auto readjustment of burst size is enabled or disabled. This parameter is used in dynamic burst size calculation, for traffic policing, at the time of PDP activation or modification. |
Burst Size Auto Readjust Duration |
The burst size readjustment duration in seconds. This parameter indicates the number of seconds that the dynamic burst size calculation will last for. This allows the traffic to be throttled at the negotiated rates. |
Peak Burst Size (bytes) |
The peak burst size allowed, in bytes, for the uplink/downlink direction and QoS class. |
Guaranteed Burst Size (bytes) |
The guaranteed burst size allowed, in bytes, for the uplink/downlink direction and QoS class. |
Exceed Action |
The action to be taken on packets that exceed the committed data rate, but do not violate the peak data rate. The action could be one of the following: • Drop Drop • Lower IP Precedence Lower IP Precedence • Transmit Transmit |
Violate Action |
The action to be taken on packets that exceed both committed and peak data rates. The action could be one of the following: • Drop Drop • Lower IP Precedence Lower IP Precedence • Shape Shape • Transmit Transmit |
Viewing Additional Characteristics of an APN Profile
To view additional characteristics of an APN profile:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > local > Mobile > Profile > APN Profiles > APN Profile.
In the logical inventory window, choose Logical Inventory > local > Mobile > Profile > APN Profiles > APN Profile.
Step 3  Expand the APN Profile node. The following list of characteristics configured for the APN profile are displayed:
Expand the APN Profile node. The following list of characteristics configured for the APN profile are displayed:
– PDP Inactivity Actions—Attributes related to PDP data inactivity. Once a data communication is in progress there are cases where this data communication can be inactive after some time, for example, when the user has locked the phone after browsing the internet or when the battery suddenly drains out. In such a case, the SGSN can take a configured action based on this inactivity. The inactivity timeout and the actions that can be taken based on certain conditions are modeled in this configuration.
PDP Inactivity Actions—Attributes related to PDP data inactivity. Once a data communication is in progress there are cases where this data communication can be inactive after some time, for example, when the user has locked the phone after browsing the internet or when the battery suddenly drains out. In such a case, the SGSN can take a configured action based on this inactivity. The inactivity timeout and the actions that can be taken based on certain conditions are modeled in this configuration.
– QoS to DSCP Mapping (Downlink) / Qos to DSCP Mapping (Uplink)—Mapping of QoS parameters to DSCP. Configuration of the local values for the traffic class (TC) parameters for QoS configured for the APN.
QoS to DSCP Mapping (Downlink) / Qos to DSCP Mapping (Uplink)—Mapping of QoS parameters to DSCP. Configuration of the local values for the traffic class (TC) parameters for QoS configured for the APN.
– PDP Restrictions (UMTS) / PDP Restrictions (GPRS)—Activation restrictions on PDP.
PDP Restrictions (UMTS) / PDP Restrictions (GPRS)—Activation restrictions on PDP.
Step 4  Click each of one of these characteristics to view its properties on the right pane. See Table 26-68 for more details on the properties of each characteristics configured for the APN profile.
Click each of one of these characteristics to view its properties on the right pane. See Table 26-68 for more details on the properties of each characteristics configured for the APN profile.
Table 26-68 APN Profile Additional Characteristics
|
|
|
PDP Inactivity Actions |
PDP Inactivity Idle Timeout |
Timeout duration for PDP inactivity. PDP context is deactivated, if it is inactive for the given duration. |
PDP Inactivity Idle Timeout Action |
Action to be taken when the PDP data communication is inactive for the timeout duration. |
PDP Inactivity Idle Timeout Action Condition |
Condition when the GPRS detach procedure should be executed on the PDP context, when the timeout is reached or exceeded. |
PDP IPV4 IPV6 Override |
PDP type to use, per APN, if dual PDP type addressing is not supported by the network. |
QoS to DSCP Mapping (Downlink) / Qos to DSCP Mapping (Uplink) |
Conversational |
Real time conversational traffic class of service, which is reserved for voice traffic. |
Streaming |
Streaming traffic class of service, which handes one-way, real-time data transmission, such as streaming video or audio. |
Interactive Threshold Priority 1/2/3 |
Interactive traffic class of service with threshold priorities 1, 2, and 3. |
Background |
Background traffic class of service. This best-effort class manages traffic that is handled as a background function, such as e-mail, where time to delivery is not a key factor. |
Interactive TP1 Alloc P1/P2/P3 |
Interactive traffic class of service, with threshold priority 1 and allocation priorities 1, 2, and 3. |
Interactive TP2 Alloc P1/P2/P3 |
Interactive traffic class of service, with threshold priority 2 and allocation priorities 1, 2, and 3. |
Interactive TP3 Alloc P1/P2/P3 |
Interactive traffic class of service, with threshold priority 3 and allocation priorities 1, 2, and 3. |
PDP Restrictions (UMTS) / PDP Restrictions (GPRS) |
QoS Class Background |
Indicates whether background traffic class of service is enabled or not. |
QoS Class Interactive |
Indicates whether interactive traffic class of service is enabled or not. |
QoS Class Streaming |
Indicates whether streaming traffic class of service is enabled or not. |
QoS Class Conversational |
Indicates whether conversational traffic class of service is enabled or not. |
Working with Active Charging Service
Enhanced Charging Service (ECS), also known as Active Charging Service (ACS), is an in-line service, which is integrated within the platform and provides mobile operators the ability to offer tiered, detailed, and itemized billing to subscribers. Data packets flow through the ECS subsystem and relevant actions are performed based on the configured rules. Charging records (xCDRs) will be generated and forwarded to ESS or billing systems for prepaid and post paid billing.
The major components and functions of an ECS solution are given below.
Content Service Steering
Content Service Steering (CSS) enables directing selective subscriber traffic into the ECS subsystem. CSS uses Access Control Lists (ACLs) to redirect selective subscriber traffic flows. ACLs control the flow of packets into and out of the system. ACLs consist of rules (ACL rules) or filters that control the action taken on packets matching the filter criteria.
ACLs are configurable on a per-context basis and apply to a subscriber through either a subscriber profile (for PDSN) or an APN profile (for GGSN) in the destination context.
Protocol Analyzer
Protocol analyzer stack is responsible for analyzing the individual protocol fields during packet inspection. The analyzer supports the following types of packet inspection:
• Shallow Packet Inspection—Inspection of the Layer 3 (IP header) and Layer 4 (for example, UDP or TCP header) information.
Shallow Packet Inspection—Inspection of the Layer 3 (IP header) and Layer 4 (for example, UDP or TCP header) information.
• Deep Packet Inspection—Inspection of Layer 7 and above information. This functionality includes:
Deep Packet Inspection—Inspection of Layer 7 and above information. This functionality includes:
– Detection of Uniform Resource Identifier (URI) information at level 7 (example, HTTP)
Detection of Uniform Resource Identifier (URI) information at level 7 (example, HTTP)
– Identification of true destination in the case of terminating proxies, where shallow packet inspection only reveals the destination IP address/port number of a terminating proxy
Identification of true destination in the case of terminating proxies, where shallow packet inspection only reveals the destination IP address/port number of a terminating proxy
Rule Definitions
Rule definitions (ruledefs) are user-defined expressions, based on protocol fields and protocol states, which define what actions to take when specific field values are true.
Most important rule definitions are related to Routing and Charging as explained below:
• Routing Ruledefs—Routing ruledefs are used to route packets to content analyzers. Routing ruledefs determine which content analyzer to route the packet to, when the protocol fields and/or protocol states in ruledef expression are true.
Routing Ruledefs—Routing ruledefs are used to route packets to content analyzers. Routing ruledefs determine which content analyzer to route the packet to, when the protocol fields and/or protocol states in ruledef expression are true.
• Charging Ruledefs—Charging ruledefs are used to specify what action to take based on the analysis done by the content analyzers. Actions can include redirection, charge value, and billing record emission.
Charging Ruledefs—Charging ruledefs are used to specify what action to take based on the analysis done by the content analyzers. Actions can include redirection, charge value, and billing record emission.
Rule Base
A rule base is a collection of rule definitions and their associated billing policy. The rule base determines the action to be taken when a rule is matched. Rule bases can also be used to apply the same rule definitions for several subscribers, which eliminate the need to have unique rule definition for each subscriber. We can set priority, default bandwidth policy, type of billing for subscriber sessions, for a rule definition or group of rule definitions in the rule base.
Content Filtering
ACS also offers a content filtering mechanism. Content filtering is an in-line service available for 3GPP and 3GPP2 networks to filter HTTP and WAP requests from mobile subscribers, based on the URLs in the requests. Content filtering uses the DPI feature of ECS to discern HTTP and WAP requests. This enables operators to filter and control the content that an individual subscriber can access, so that subscribers are inadvertently not exposed to universally unacceptable content and/or content inappropriate as per the subscribers' preferences.
The content filtering service offers the following solutions:
• URL Blacklisting—With this solution, all HTTP/WAP URLs in subscriber requests are matched against a database of blacklisted URLs. If there is a match, the flow is discarded, redirected, or terminated as configured. If there is no match, subscribers view the content as they would normally.
URL Blacklisting—With this solution, all HTTP/WAP URLs in subscriber requests are matched against a database of blacklisted URLs. If there is a match, the flow is discarded, redirected, or terminated as configured. If there is no match, subscribers view the content as they would normally.
• Category-based Content Filtering
Category-based Content Filtering
– Category-based Static Content Filtering—In this method, all HTTP/WAP URLs in subscriber requests are matched against a static URL categorization database. Action is taken based on a URL's category, and the action configured for that category in the subscriber's content filtering policy. Possible actions include permitting, blocking, redirecting, and inserting content.
Category-based Static Content Filtering—In this method, all HTTP/WAP URLs in subscriber requests are matched against a static URL categorization database. Action is taken based on a URL's category, and the action configured for that category in the subscriber's content filtering policy. Possible actions include permitting, blocking, redirecting, and inserting content.
– Category-based Static-and-Dynamic Content Filtering—In this method, each URL first undergoes static rating. If the URL cannot be rated by the static database or if the URL static rating categorizes a URL as either Dynamic or Unknown, the requested content is sent for dynamic rating; wherein the requested content is analyzed and categorized. Action is taken based on the category determined by dynamic rating, and the action configured for that category in the subscriber's content filtering policy. Possible actions include permitting, blocking, redirecting, and inserting content.
Category-based Static-and-Dynamic Content Filtering—In this method, each URL first undergoes static rating. If the URL cannot be rated by the static database or if the URL static rating categorizes a URL as either Dynamic or Unknown, the requested content is sent for dynamic rating; wherein the requested content is analyzed and categorized. Action is taken based on the category determined by dynamic rating, and the action configured for that category in the subscriber's content filtering policy. Possible actions include permitting, blocking, redirecting, and inserting content.
Note  ACS is applicable only for the `local' context in the logical inventory.
ACS is applicable only for the `local' context in the logical inventory.
The following topics explain how to work with ACS in Prime Network Vision:
• Viewing Active Charging Services
Viewing Active Charging Services
• ACS Commands
ACS Commands
Viewing Active Charging Services
You can view the active charging services in logical inventory as shown in Figure 26-18.
Figure 26-18 Mobile Technology Setup Nodes
Additionally, you can also perform the following for each ACS:
• Viewing Content Filtering Categories
Viewing Content Filtering Categories
• Viewing Credit Control Properties
Viewing Credit Control Properties
• Viewing Charging Action Properties
Viewing Charging Action Properties
• Viewing Rule Definitions
Viewing Rule Definitions
• Viewing Rule Base for the Charging Action
Viewing Rule Base for the Charging Action
• Viewing Bandwidth Policies
Viewing Bandwidth Policies
• Viewing Fair Usage Properties
Viewing Fair Usage Properties
To view ACS details in logical inventory:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services.
Prime Network Vision displays the list of active charging services configured under the container. You can view the individual ACS details from the table on the right pane or by choosing Logical Inventory > local > Mobile > Active Charging Services > ACS.
Table 26-69 describes the details available for each ACS.
Table 26-69 Active Charging Services in Logical Inventory
|
|
|
Service Name |
Name of the active charging service. |
TCP Flow Idle Timeout |
Maximum duration, in seconds, a TCP flow can remain idle. |
UDP Flow Idle Timeout |
Maximum duration, in seconds, a UDP flow can remain idle. |
ICMP Flow Idle Timeout |
Maximum duration, in seconds, an Internet Control Message Protocol (ICMP) flow can remain idle. |
ALG Media Idle Timeout |
Maximum duration, in seconds, an application level gateway (ALG) media flow can remain idle. |
TCP Flow Mapping Idle Timeout |
The time for which the TCP flow mapping timer holds the resources. |
UDP Flow Mapping Idle Timeout |
The time for which the UDP flow mapping timer holds the resources. |
Deep Packet Inspection |
Indicates whether configuration of DPI is enabled or disabled in the mobile video gateway. |
Passive Mode |
Indicates whether the ACS is in or out of passive mode operation. |
CDR Flow Control |
Indicates whether flow control is enabled or disabled between the ACS Manager (ACSMGR) and Charging Data Record Module (CDRMOD). |
CDR Flow Control Unsent Queue Size |
Flow control unsent queue size at ACSMGR level. |
Unsent Queue High Watermark |
Highest flow control unsent queue size at ACSMGR level. |
Unsent Queue Low Watermark |
Lowest flow control unsent queue size at ACSMGR level. |
Content Filtering |
Indicates whether content filtering is enabled or disabled for the ACS. |
Dynamic Content Filtering |
Indicates whether dynamic content filtering is enabled or disabled for the ACS. |
URL Blacklisting |
Indicates whether URL blacklisting is enabled or disabled for the ACS. |
URL Blacklisting Match Method |
Method to look up the URLs in the URL blacklisting database. |
Content Filtering Match Method |
Method to look up the URLs in the category-based content filtering database. |
Interpretation of Charging Rulebase Name |
Charging rulebase configured for the ACS. |
Selected Charging Rulebase Name for AVP |
Charging rulebase name for attribute value pair (AVP) configured for the ACS. |
Viewing Content Filtering Categories
To view content filtering categories in logical inventory:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services >ACS >Content Filtering Categories.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services >ACS >Content Filtering Categories.
Prime Network Vision displays the list of content filtering categories configured under the container. You can view the individual content filtering category details from the table on the right pane or by choosing Logical Inventory > local > Mobile > Active Charging Services > ACS >Content Filtering Categories > Content Filtering Category.
Table 26-70 describes the details available for each content filtering category.
Table 26-70 Content Filtering Categories in Logical Inventory
|
|
|
Policy ID |
ID of the content filtering policy. |
Failure Action |
Action to take for the content filtering analysis result. |
EDR File |
The EDR file name. |
Content Category |
Name of the content filtering category. |
Content Insert |
Content string to insert in place of the message returned from prohibited or restricted site or content server. |
Content Priority |
Precedence of the category in the content filtering policy. |
Content Failure Action |
Action to take for the indicated result of the content filtering analysis, which could be one of the following: • allow allow • content-insert content-insert • discard discard • redirect URL redirect URL • terminate flow terminate flow • www-reply-code-and-terminate-flow www-reply-code-and-terminate-flow |
Content Redirect |
Content string to redirect the subscriber to a specified URL. |
Content Reply Code |
Reply code to terminate flow. |
EDR File Format |
Predefined EDR file format. |
Viewing Credit Control Properties
In a prepaid environment, the subscribers pay for a service prior to using it. While the subscriber is using the service, credit is deducted from subscriber's account until it is exhausted or the call ends. In prepaid charging, ECS performs the metering function. Credits are deducted in real time from an account balance or quota. A fixed quota is reserved from the account balance and given to the system by a prepaid rating and charging server, which interfaces with an external billing system platform. The system deducts volume from the quota according to the traffic analysis rules. When the subscriber's quota gets to the threshold level specified by the prepaid rating and charging server, system sends a new access request message to the server and server updates the subscriber's quota. The charging server is also updated at the end of the call.
ECS supports the following credit control applications for prepaid charging:
• RADIUS Credit Control Application—RADIUS is used as the interface between ECS and the prepaid charging server.
RADIUS Credit Control Application—RADIUS is used as the interface between ECS and the prepaid charging server.
• Diameter Credit Control Application—The Diameter Credit Control Application (DCCA) is used to implement real-time credit control for a variety of services, such as networks access, messaging services, and download services.
Diameter Credit Control Application—The Diameter Credit Control Application (DCCA) is used to implement real-time credit control for a variety of services, such as networks access, messaging services, and download services.
To view credit control properties in logical inventory:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services >ACS > Credit Control.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services >ACS > Credit Control.
Prime Network Vision displays the list of credit control groups configured under the container. You can view the individual credit control group details from the table on the right pane or by choosing Logical Inventory > local > Mobile > Active Charging Services > ACS > Credit Control > Credit Control Group.
You can also view the following details by clicking the respective node under the credit control group:
• Diameter
Diameter
• Failure Handling
Failure Handling
• Pending Traffic Treatment
Pending Traffic Treatment
• Quota
Quota
• Server Unreachable Failure Handling
Server Unreachable Failure Handling
Table 26-71 describes the details available for each credit control group.
Table 26-71 Credit Control Properties in Logical Inventory
|
|
|
Group |
Name of the credit control group for the subscriber. |
Mode |
Prepaid charging application mode, which could be Diameter or Radius. |
APN Name to be Included |
Type of APN name sent in the credit control application (CCA) message. |
Trigger Type |
Condition based on which credit reauthorization is triggered from the server. |
Diameter MSCC Final Unit Action Terminate |
Indicates whether to terminate a PDP session immediately when the Final-Unit-Action (FUA) in a particular multi service credit control (MSCC) is set as Terminate and the quota is exhausted for that service, or to terminate the session after all MSCCs (categories) have used their available quota. |
Diameter Peer Select table |
Peer |
Primary hostname. |
Realm |
Realm for the primary host. |
Secondary Peer |
Secondary hostname. |
Secondary Realm |
Realm for the secondary host. |
IMSI Range Mode |
Mode of peer selection based on IMSI prefix or suffix. |
IMSI Start Value |
Starting value of the IMSI range for peer selection. |
IMSI End Value |
Ending value of the IMSI range for peer selection. |
Diameter |
End Point Name |
Name of the diameter endpoint. |
End Point Realm |
Realm of the diameter endpoint. |
Pending Timeout |
Maximum time to wait for response from a diameter peer. |
Session Failover |
Indicates whether diameter session failover is enabled or not. |
Dictionary |
Diameter credit control dictionary for the ACS. |
Failure Handling |
Initial Request |
Failure handling behavior, if failure takes place during initial session establishment. Value could be continue, retry-and-terminate, and terminate. |
Update Request |
Failure handling behavior, if failure takes place during update request. Value could be continue, retry-and-terminate, and terminate. |
Terminate Request |
Failure handling behavior, if failure takes place during terminate request. Value could be continue, retry-and-terminate, and terminate. |
Pending Traffic Treatment |
Trigger |
Indicates whether to allow or drop a trigger while waiting for the credit information from the server. Value could be pass or drop. |
Forced Reauth |
Indicates whether to allow or drop reauthorization while waiting for the credit information from the server. Value could be pass or drop. |
NoQuota |
Indicates whether to allow or drop traffic, if there is no quota present. Value could be pass, drop, or buffer. |
Quota Exhausted |
Indicates whether to allow or drop traffic, if quota is exhausted. Value could be pass, drop, or buffer. |
Validity Expired |
Indicates whether to allow or drop traffic, if quota validity is expired. Value could be pass or drop. |
Quota |
Request Trigger |
Action taken on the packet that triggers the credit control application to request quota. Value could be exclude-packet-causing-trigger or include-packet-causing-trigger. |
Holding Time |
Duration for which ECS can hold the quota before returning to the credit control server. |
Validity Time |
Lifetime for which subscriber quota retrieved from the billing server is valid. |
Time Threshold |
Time threshold limit for subscriber quota in the prepaid credit control service. |
Units Threshold |
Unit threshold limit for subscriber quota in the prepaid credit control service. |
Volume Threshold |
Volume threshold limit for subscriber quota in the prepaid credit control service. |
Server Unreachable Failure Handling |
Initial Request |
Failure handling behavior if server is unreachable during initial session establishment. Value could be continue or terminate. |
Update Request |
Failure handling behavior if server is unreachable during update request. Value could be continue or terminate. |
Viewing Charging Action Properties
Charging Action is an action taken on the incoming data packets once the data packets are treated by the routing and charging rule components. User can configure independent actions such as allow, forward, and block traffic, and bind these actions with other routing and charging rule components.
To view charging action properties in logical inventory:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services >ACS > Charging Action.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services >ACS > Charging Action.
Prime Network Vision displays the list of charging actions configured under the container as shown. You can view the individual charging action details from the table on the right pane or by choosing Logical Inventory > local > Mobile > Active Charging Services > ACS > Charging Action > Charging Action.
You can also view the following details by clicking the respective node under the Charging Action node:
• Allocation Retention Priority
Allocation Retention Priority
• Bandwidth
Bandwidth
• Flow Action
Flow Action
• QoS
QoS
• Video
Video
• Billing Action
Billing Action
Table 26-72 describes the details available for each charging action record.
Table 26-72 Charging Action Properties in Logical Inventory
|
|
|
Name |
Name of the charging action. |
Content ID |
Content ID to use in the generated billing records as well the AVP used by the credit control application. |
Service ID |
Configured service ID used to associate the charging action in rule definitions configuration. |
Charging EDR Name |
Name of the EDR format for the billing action in the ACS. |
EGCDRs |
Indicates whether eG-CDRs must be generated when the subscriber session ends or an interim trigger condition occurs. |
Rf |
Indicates whether Rf accounting is enabled or not. |
UDRs |
Indicates whether UDRs must be generated based on the UDR format declared in the rule base. |
Flow Idle Timeout |
Maximum duration a flow can remain idle after which the system automatically terminates the flow. |
Limit for Flow Type State |
Indicates whether the limit for flow type is configured or not. |
Limit for Flow Type Value |
Maximum number of flows of a particular type. |
Limit for Flow Type Action |
Action to be taken, if the number of flows exceeds the maximum limit. |
IP Type of Service |
IP Type of Service (ToS) octets used in the charging action. |
Retransmission Count |
Indicates whether to count the number of packet retransmissions when the charging action is applied on the incoming data packets. |
Content Filtering |
Indicates whether content filtering must be applied on the incoming packets or not. |
Credit Control |
Indicates whether to apply credit control or not. |
Credit Rating Group |
Coupon ID used in prepaid charging as rating group. |
Charge Volume |
Method used for charge volume calculation based on the protocol and packet. |
Next Hop Forwarding Address |
Next hop forwarding address for a charging action. |
VLAN ID |
VLAN ID configured for the subscriber |
Flow Mapping Idle Timeout |
Maximum duration, in seconds, a flow can remain idle after which the system automatically terminates the flow. |
Allocation Retention Priority |
Priority Level |
Priority value that indicates whether to accept or reject a request for establishment or modification of a bearer in a limited resource condition. |
Priority Vulnerability Indicator |
Defines whether an active bearer can be preempted by a preemption-capable high priority bearer. |
Priority Capability Indicator |
Defines whether the bearer request can preempt the resources from the Low Priority Pre-empatable Active Bearers. |
Bandwidth |
Bandwidth ID |
The bandwidth policy ID for the ACS. |
Uplink |
Indicates whether uplink flow limit is configured for the subscriber or not. |
Downlink |
Indicates whether downlink flow limit is configured for the subscriber or not. |
Charging Action Bandwidth Direction |
Direction |
Direction of the packet flow: Uplink or Downlink |
Peak Data Rate |
Peak data rate configured for the uplink or downlink packet flow. |
Peak Burst Size |
Peak burst size allowed for the uplink or downlink packets. |
Committed Data Rate |
Committed data rate for the uplink or downlink packet flow. |
Committed Burst Size |
Committed burst size allowed for the uplink or downlink packets. |
Exceed Action |
Action to take on packets that exceed committed data rate but do not violate the peak data rate. |
Violate Action |
Action to take on packets that exceed both committed and peak data rates. |
Bandwidth Limiting ID |
Identifier for bandwidth limiting. |
Flow Action |
Redirect URL |
Indicates whether packets matched to the rule definition must be redirected to a specified URL or not. |
Clear Quota Retry Timer |
Indicates whether to reset the CCA quota retry timer for a specific subscriber upon redirection of data packets. |
Conditional Redirect |
Indicates whether packets matching to a configured user agent must be conditionally redirected to a specified URL. |
Discard |
Discards packets associated with the charging action. |
Random Drop |
Indicates whether to degrade voice quality and specify the time interval in seconds at which the voice packets will be dropped. |
Readdress |
Redirects unknown gateway traffic based on the destination IP address of the packets to known or trusted gateways. |
Terminate Flow |
Indicates whether to terminate the flow by terminating the TCP connection gracefully between the subscriber and external server. |
Terminate Session |
Indicates whether to terminate the session. |
QoS |
Traffic Class |
QoS traffic class for the charging action, which could be background, conversational, interactive, or streaming. |
Class Identifier |
The QCI value. |
Video |
Bit Rate |
Bits per second, at which the TCP video flow must be paced during video pacing. |
CAE Readdressing |
Indicates whether Content Adaptation Engine (CAE) readdressing is enabled, allowing video traffic to be fetched from the CAEs in the CAE group. |
Transrating |
Indicates whether transrating is enabled or not. Transrating is a mobile video feature that reduces the encoded bit rates by adjusting video encoding. |
Target Rate Reduction |
Percentage of the input bit rate of a video flow. |
Billing Action |
EDR |
Name of the EDR format for the billing action in the ACS. |
EGCDR |
Indicates whether eG-CDRs must be generated when the subscriber session ends or an interim trigger condition occurs. |
Rf |
Indicates whether Rf accounting is enabled or not. |
UDRs |
Indicates whether UDRs must be generated based on the UDR format declared in the rule base. |
Radius Accounting Record |
Indicates whether radius accounting is enabled or not. |
Viewing Rule Definitions
Rule definitions are user-defined expressions, based on protocol fields and protocol states, which define what actions to take when specific field values are true. Each rule definition configuration consists of multiple expressions applicable to any of the fields or states supported by the respective analyzers.
Rule definitions are of the following types:
• Routing—Used to route packets to content analyzers. Routing rule definitions determine which content analyzer to route the packet to when the protocol fields and/or protocol states in the rule definition expression are true. Up to 256 rule definitions can be configured for routing.
Routing—Used to route packets to content analyzers. Routing rule definitions determine which content analyzer to route the packet to when the protocol fields and/or protocol states in the rule definition expression are true. Up to 256 rule definitions can be configured for routing.
• Charging—Used to specify what action to take based on the analysis done by the content analyzers. Actions can include redirection, charge value, and billing record emission. Up to 2048 charging rule definitions can be configured in the system.
Charging—Used to specify what action to take based on the analysis done by the content analyzers. Actions can include redirection, charge value, and billing record emission. Up to 2048 charging rule definitions can be configured in the system.
• Post-processing—Used for post-processing purposes. Enables processing of packets even if the rule matching for them has been disabled.
Post-processing—Used for post-processing purposes. Enables processing of packets even if the rule matching for them has been disabled.
• TPO—Used for Traffic Performance Optimization (TPO) in-line service match-rule and match advertisement features.
TPO—Used for Traffic Performance Optimization (TPO) in-line service match-rule and match advertisement features.
To view rule definitions in logical inventory:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Rule Definitions.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Rule Definitions.
Prime Network Vision displays the list of rule definitions configured under the container. You can view the individual rule definition details from the table on the right pane or by choosing Logical Inventory > local > Mobile > Active Charging Services >ACS > Rule Definitions > Rule Definition.
Table 26-73 describes the details available for each rule definition.
Table 26-73 Rule Definition Group Properties in Logical Inventory
|
|
|
Name |
Name of the rule definition group. |
Application Type |
Purpose of the rule definition, which could be charging, routing, post-processing, or Traffic Performance Optimization (TPO). |
Copy Packet To Log |
Indicates whether to copy every packet that matches the rule to a log file. |
Tethered Flow Check |
Indicates whether tethered flow check if enabled or not. Tethering detection flow check feature enables detection of subscriber data traffic flow originating from PC devices tethered to mobile smart phones, and also provides effective reporting to enable service providers take business decisions on how to manage such usage and to bill subscribers accordingly. |
Multiline OR |
Indicates whether to apply the OR operator to all lines in a rule definition. This allows a single rule definition to specify multiple URL expressions. |
|
|
Protocol |
The protocol that this rule definition is applied on. |
Fields |
Particular protocol field, which is applied on the data packets for inspection. Value could be, host, payload, or domain. |
Operator |
Logical operator that indicates how to logically match the value in the field analyzed based on the data type. |
Value |
Value of a particular protocol in a rule definition which has to be applied on the incoming data packets for inspection. |
Viewing Rule Definition Groups
A rule definition group enables grouping the rule definitions into categories. A rule definition group may contain optimizable rule definitions. Whether a group is optimized or not is decided on whether all the rule definitions in the group can be optimized. When a new rule definition is added, it is checked if it is included in any rule definition group and whether it needs to be optimized or not.
To view rule definition groups in logical inventory:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Group of Rule Definitions.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Group of Rule Definitions.
Prime Network Vision displays the list of rule definition groups configured under the container. You can view the individual rule definition group details from the table on the right pane or by choosing Logical Inventory > local > Mobile > Active Charging Services >ACS > Group of Rule Definitions > Rule Definition Group.
Table 26-74 describes the details available for each rule definition group.
Table 26-74 Rule Definition Group Properties in Logical Inventory
|
|
|
Name |
Name of the rule definition group. |
Application Type |
Purpose of the rule definition group, which could be charging, routing, content filtering, post-processing, or Traffic Performance Optimization (TPO). |
Dynamic Command Content Filtering Policy ID |
Content filtering policy ID to add or remove dynamic commands from the rule definition group. |
Rule Definition Group Commands
The following commands can be launched from the inventory by right-clicking a rule definition group and choosing Commands > Configuration or Commands > Show. Before executing any commands, you can preview them and view the results. If desired, you can also schedule the commands. To find out if a device supports these commands, see the Cisco Prime Network 3.10 Supported Cisco VNEs.
Note  You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
Table 26-75 Rule Definition Group Commands
|
|
|
Inputs Required and Notes
|
Configuration |
Delete Group of RuleDefs |
Click Execute Now to delete the rule definition group. |
Show |
Show Group of RuleDefs |
Click Execute Now to display the group of rule definitions. |
Viewing Rule Base for the Charging Action
A rule base is a collection of rule definitions and their associated billing policy. The rule base determines the action to be taken when a rule is matched. A maximum of 512 rule bases can be specified in the ECS service. It is possible to define a rule definition with different actions.
Rule bases can also be used to apply the same rule definitions for several subscribers, which eliminate the need to have unique rule definition for each subscriber. We can set priority, default bandwidth policy, type of billing for subscriber sessions, for a rule definition/ group of rule definitions in the rule base. Additionally we can configure content based billing and firewall/NAT constituent to rule base.
To view a rule base in logical inventory:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Rulebase Container.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Rulebase Container.
Prime Network Vision displays the list of rule bases configured under the container. You can view the individual rule base details from the table on the right pane or by choosing Logical Inventory > local > Mobile > Active Charging Services >ACS > Rulebase Container > Rule Base.
Table 26-76 describes the details available for each rule base record.
Table 26-76 Rule Base Properties in Logical Inventory
|
|
|
Rulebase Name |
Name of the rule base. |
Flow Any Error Charging Action |
Charging action to be used for packets dropped due to any error conditions after data session is created. |
Limit for Total Flows |
Maximum number of simultaneous uplink and downlink packet flows. |
Limit for TCP Flows |
Maximum number simultaneous TCP packet flows per subscriber or APN allowed for a rulebase. |
Limit for Non TCP Flows |
Maximum number simultaneous non-TCP packet flows per subscriber or APN allowed for a rulebase. |
Charging Rule Optimization |
Internal optimization level to use, for improved performance, when evaluating each instance of the action. |
QoS Renegotiation Timeout |
Timeout value after which QoS renegotiation is performed. |
RTP Dynamic Routing |
Indicates whether the Real Time Streaming Protocol (RTSP) and SDP analyzers are enabled to detect the start/stop of RTP (a Transport Protocol for Real-Time Applications) and RTP Control Protocol (RCP) flows. |
Ignore Port Number In Application Header |
Indicates whether to consider or ignore the port number embedded in the application. |
Delayed Charging |
Indicates how to charge for the control traffic associated with an application. |
XHeader Certificate Name |
Name of the encryption certificate to be used for x-header encryption. |
XHeader Reencryption Period |
Indicates how often to regenerate the encryption key for x-header encryption. |
Default Bandwidth Policy |
Name of the default bandwidth policy per subscriber. |
P2P Dynamic Routing |
Indicates whether P2P analyzer is enabled to detect the P2P applications flow configured in ACS. |
Fair Usage Waiver Percentage |
Waiver percent on top of the average available memory credits per session for the Fair Usage feature of active charging. |
URL Blacklisting Action |
Configured URL blacklisting action to take when the URL matches ones of the blacklisted URLs. |
URL Blacklisting Content ID |
Specific content ID for which URL blacklisting is enabled in the rulebase. |
Charging Action Priorities tab |
Charging rule definitions and their priorities in the rulebase. |
Routing Action Priorities tab |
Routing actions and their priorities in the rulebase. |
Post Processing Action Priorities |
Post-processing actions and their priorities in the rulebase. |
Viewing Bandwidth Policies
Bandwidth policies are helpful in applying rate limit to potentially bandwidth intensive and service disruptive applications. Using this policy, the operator can police and prioritize subscribers' traffic to ensure that no single or group of subscribers' traffic negatively impacts another subscribers' traffic. Each policy will be identified by a unique ID, which will be associated to a particular group. Bandwidth policies are used to control the direction (uplink/downlink) of bandwidth, peak data rate, and peak burst size, and the actions that need to be taken on violation, if the bandwidth exceeds the burst size and data rate.
To view bandwidth policy in logical inventory:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Bandwidth Policy Container.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Bandwidth Policy Container.
Prime Network Vision displays the list of bandwidth policies configured under the container. You can view the individual bandwidth policy details from the table on the right pane or by choosing Logical Inventory > local > Mobile > Active Charging Services > ACS > Bandwidth Policy Container > Bandwidth Policy.
Table 26-77 describes the details available for each bandwidth policy.
Table 26-77 Bandwidth Policy Properties in Logical Inventory
|
|
|
Name |
Name of the bandwidth policy configured. |
Total Bandwidth ID Configured |
Total number of bandwidth IDs configured. |
Total Group Limit Configured |
Total number of bandwidth group limits configured. |
Flow Limit for Bandwidth ID and Group ID Associations and Group ID tables |
Holds all bandwidth IDs and group IDs of the bandwidth policy. |
Viewing Fair Usage Properties
To view fair usage properties configured for the ACS:
Step 1  Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory.
Step 2  In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Fair Usage.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Fair Usage.
Prime Network Vision displays the details on the content pane.
Table 26-78 describes the fair usage properties.
Table 26-78 Fair Usage Properties in Logical Inventory
|
|
|
CPU Threshold Percent |
Percentage of system CPU resources that the dynamic inline transrating feature is allowed to use. |
Threshold Percent |
Percentage of system resources that the dynamic inline transrating feature is allowed to use. |
Deactivate Margin Percent |
Fair usage deactivate margin, below which monitor action is disabled. |
ACS Commands
The following commands can be launched from the inventory by right-clicking an ACS and choosing Commands > Configuration or Commands > Show. Before executing any commands, you can preview them and view the results. If desired, you can also schedule the commands. To find out if a device supports these commands, see the Cisco Prime Network 3.10 Supported Cisco VNEs.
Note  You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
Note  In the GUI, parameters that are displayed in bold text are mandatory.
In the GUI, parameters that are displayed in bold text are mandatory.
Table 26-79 lists the Active Charging Services configuration commands.
Table 26-79 Active Charging Services Configuration Commands
|
|
|
|
Create Ruledef |
Expand Active Charging Services node > right-click ACS service > Commands > Configuration |
Rule definitions (Ruledefs) are user-defined expressions, based on protocol fields and/or protocol-states, which define what actions to take when specific field values are true. Use this command to create a new rule definition for the selected ACS service. |
Create group of Ruledefs |
Expand Active Charging Services node > right-click ACS service > Commands > Configuration |
Group-of-Ruledefs enable grouping ruledefs into categories. When a group-of-ruledefs is configured in a rulebase, if any of the ruledefs within the group matches, the specified charging-action is performed, any more action instances are not. Use this command to create a new group of rule definitions for the selected ACS service. |
Create Rulebase |
Expand Active Charging Services node > right-click ACS service > Commands > Configuration |
A rulebase is a collection of ruledefs and their associated billing policy. The rulebase determines the action to be taken when a rule is matched. Use this command to create a new rule base for the selected ACS service. |
Modify Active Charging Service Delete Active Charging Service |
Expand Active Charging Services node > right-click ACS service > Commands > Configuration |
Use these commands to modify/delete an Active Charging service created for the selected context. |
Create Access Ruledef Delete Access Ruledef |
Expand Active Charging Services node > right-click ACS service > Commands > Configuration > Access Ruledef |
Use these commands to create/delete an access rule definition for the selected ACS service. |
Show Access Ruledef |
Expand Active Charging Services node > right-click ACS service > Commands > Show |
Use this command to view and confirm the access rule definitions configured for the service. |
Create Host Pool Modify Host Pool Delete Host Pool |
Expand Active Charging Services node > right-click ACS service > Commands > Configuration > Host Pool |
Host pools allow operators to group a set of host or IP addresses that share similar characteristics together. Access rule definitions (ruledefs) can be configured with host pools. Up to ten sets of IP addresses can be configured in each host pool. Use these commands to create/modify/delete a host pool for the selected ACS service. |
Create Charging Action |
Expand Active Charging Services node > right-click ACS service > Commands > Configuration |
Charging Action is an action taken on the incoming data packets once the data packets are treated by the routing and charging rule components. You can configure independent actions such as allow, forward, and block traffic, and bind these actions with other routing and charging rule components. Use this command to configure a charging action for a service. |
Modify charging Action Delete Charging Action |
Expand Active Charging Services node > ACS service > Charging Actions > right-click an charging action > Commands > Configuration |
Use these commands to modify/delete a charging action for a service. |
Show Charging Action |
Expand Active Charging Services node > right-click ACS service > Commands > Show |
Use this command to view and confirm the charging action configuration details. |
Configuring and Viewing Mobile Technologies
The following commands can be used to configure and view mobile technologies under a particular context in the Prime Network Vision. These commands can be launched from the logical inventory by choosing the Context > Commands > Configuration or Context > Commands > Show. Before executing any command, you can preview them and view the results. If desired, you can also schedule the commands. To find out if a device supports these commands, see the Cisco Prime Network 3.10 Supported Cisco VNEs.
Note  You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
|
|
|
|
Create AAA Group |
Context > Commands > Configuration |
AAA refers to Authentication, Authorization, and Accounting, which is a security architecture for distributed systems that determines the access given to users for specific services and the amount of resources they have used. Use this command to create a new AAA group. |
Create APN |
APN is the access point name that is configured in the GGSN configurations. Use this command to create a new APN service. |
Create Active Charging Service |
Enhanced Charging Service (ECS), also known as Active Charging Service (ACS), is an in-line service, which is integrated within the platform and provides mobile operators the ability to offer tiered, detailed, and itemized billing to subscribers. Use this command to create a new ACS service. |
Create EGTP |
Evolved GPRS Tunneling Protocol (EGTP) formulates the primary bearer plane protocol within an LTE / EPC architecture. It provides support for tunnel management including handover procedures within and across LTE networks. Use this command to create an EGTP service. |
Create GGSN |
Context > Commands > Configuration |
Gateway GPRS Support Node (GGSM) is the gateway between the GPRS wireless data network and other external packet data networks such as radio networks, IP networks, or private networks. GGSN provides network access to external hosts wishing to communicate with mobile subscribers (MS). Use this command to create a GGSN service. |
Create GTPP |
GPRS Tunneling Protocol Prime (GTPP) is used for communicating accounting messages to CGs. Use this command to create a GTPP service. |
Create GTPU |
GTPU carries user data within the GPRS core network and between the radio access network and the core network. The user data transported can be packets in any of IPv4, IPv6, or PPP formats. Use this command to create a GTPU service. |
Create IP Pool |
An IP pool is a sequential range of IP addresses within a certain network. Use this command to create an IP Pool. |
Create P-GW |
PDN Gateway (P-GW) is the node that terminates the SGi interface towards the PDN. If a UE is accessing multiple PDNs, there may be more than one P-GW for that UE. Use this command to create a P-GW. |
Create QCI-QOS Mapping |
The QoS Class Index (QCI) to QoS mapping configuration mode is used to map QCIs to enforceable QoS parameters. Use this command to create a QCI-QOS Mapping. |
Create S-GW |
A Serving Gateway (S-GW) acts as a demarcation point between the Radio Access Network (RAN) and core network, and manages user plane mobility. Use this command to create a S-GW. |
Create VRF |
Virtual routing and forwarding (VRF) is a technology included in IP (Internet Protocol) network routers that allows multiple instances of a routing table to exist in a router and work simultaneously. Use this command to create a VRF. |
Delete Context |
Use this command to delete a context under the Logical Inventory node. |
Modify License |
Use this command to modify the license information. |
Create DHCP |
Context > Commands > Configuration > DHCP |
DHCP is used to automate host configuration by assigning IP addresses, delegating prefixes (in IPv6), and providing extensive configuration information to network computers. Use this command to create a DHCP service. |
Delete DHCP |
Use this command to delete a DHCP service. |
Modify DHCP |
Use this command to modify the configuration details of a DHCP service. |
Create HA SPI List |
Context > Commands > Configuration > HA SPI List |
Use this command to create the Security Parameter Index (SPI) between the HA service and the FA. |
Delete HA SPI List |
Use this command to delete the HA SPI List. |
Modify HA SPI List |
Use this command to modify the HA SPI List configuration details. |
Create HA Service |
Context > Commands > Configuration > HA Service |
Use this command to create a new Home Agent service. |
Delete HA Service |
Use this command to delete a HA Service. |
Modify HA Service |
Use this command to modify the configuration details of a HA service. |
Create Network Requested PDP Context |
Context > Commands > Configuration > PDP Context |
Packet Data Protocol (PDP) context is the connection or link between a mobile device and a network server that allows them to communicate with each other. A PDP context lasts only for the duration of a specific connection. Use this command to create a network requested PDP context. |
Delete Network Requested PDP Context |
Use this command to delete a network requested PDP context. |
Create Proxy DNS |
Context > Commands > Configuration > Proxy DNS |
The proxy DNS listens for incoming DNS requests on the local interface and resolves remote hosts using an external PHP script, through http proxy requests. Use this command to create a proxy DNS. |
Delete Proxy DNS |
Use this command to delete a proxy DNS. |
Modify Proxy DNS |
Use this command to modify the proxy DNS configuration details. |
Create Route Access List |
Context > Commands > Configuration > Route Map and Route Access List |
Access lists are a set of rules, organized in a rule table and are used to filter and identify traffic. Use this command to create a new access list. |
Create Route Map |
Route maps are similar to access lists; they both have criteria for matching the details of certain packets and an action of permitting or denying those packets. Unlike access lists, though, route maps can add to each "match" criterion a "set" criterion that actually changes the packet in a specified manner, or changes route information in a specified manner. Use this command to create a route map. |
Delete Route Access List |
Use this command to delete a route access list. |
Delete Route Map |
Use this command to delete a route map. |
Modify Route Access List |
Use this command to modify a route access list. |
Modify Route Map |
Use this command to modify a route map. |
Create Subscribers |
Context > Commands > Configuration > Subscriber |
Use this command to create a new subscriber. |
Delete Subscriber |
Use this command to delete a subscriber. |
Modify Subscriber |
Use this command to modify subscriber details. |
Show APN |
Context > Commands > Show |
Use this command to view and confirm the APN configuration details. |
Show DHCP |
Use this command to view and confirm the DHCP configuration details. |
Show EGTP |
Use this command to view and confirm the EGTP configuration details. |
Show HA SPI List |
Use this command to view and confirm the HA SPI List details. |
Show HA Service |
Use this command to view and confirm the home agent service details. |
Show IP Pool |
Use this command to view and confirm the IP Pool configuration details. |
Show License |
Use this command to view and confirm the License details. |
Show Route Access List |
Use this command to view and confirm the Access list details. |
Show Route Map |
Use this command to view and confirm the Route Map details. |
Show Subscriber |
Use this command to view and confirm the Subscriber details. |
Create Policy Accounting |
Right-click on context > Commands > Configuration > Policy Accounting |
Use this command to create a new accounting policy. |
Modify Policy Accounting Delete Policy Accounting |
Right-click on context > Commands > Configuration > Policy Accounting |
Use these commands to modify/delete an accounting policy. |
![]() User Roles Required to Work with Mobile Technologies
User Roles Required to Work with Mobile Technologies ![]() GPRS/UMTS Networks - An Overview
GPRS/UMTS Networks - An Overview ![]() Working With GPRS/UMTS Network TechnologiesLTE Networks - An Overview
Working With GPRS/UMTS Network TechnologiesLTE Networks - An Overview ![]() Working with LTE Network Technologies
Working with LTE Network Technologies ![]() Viewing Operator Policies, APN Remaps, and APN Profiles
Viewing Operator Policies, APN Remaps, and APN Profiles ![]() Working with Active Charging Service
Working with Active Charging Service ![]() Configuring and Viewing Mobile Technologies
Configuring and Viewing Mobile Technologies ![]() For GUI-based tasks (tasks that do not affect elements), authorization is based on the default permission that is assigned to your user account.
For GUI-based tasks (tasks that do not affect elements), authorization is based on the default permission that is assigned to your user account. ![]() For element-based tasks (tasks that do affect elements), authorization is based on the default permission that is assigned to your account. That is, whether the element is in one of your assigned scopes and whether you meet the minimum security level for that scope.
For element-based tasks (tasks that do affect elements), authorization is based on the default permission that is assigned to your account. That is, whether the element is in one of your assigned scopes and whether you meet the minimum security level for that scope. ![]() Table 26-1 identifies the tasks that you can perform if a selected element is not in one of your assigned scopes.
Table 26-1 identifies the tasks that you can perform if a selected element is not in one of your assigned scopes. ![]() Table 26-2 identifies the tasks that you can perform if a selected element is in one of your assigned scopes.
Table 26-2 identifies the tasks that you can perform if a selected element is in one of your assigned scopes. 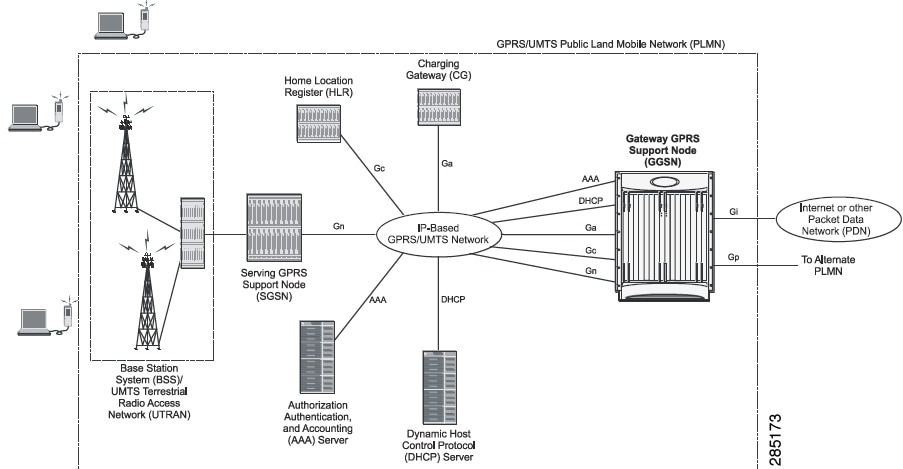
![]() Gateway GPRS support node (GGSN)—A gateway that provides mobile cell phone users access to a Packet Data Network (PDN) or specified private Internet Protocol (IP) networks.
Gateway GPRS support node (GGSN)—A gateway that provides mobile cell phone users access to a Packet Data Network (PDN) or specified private Internet Protocol (IP) networks. ![]() Serving GPRS support node (SGSN)—Connects the radio access network (RAN) to the GPRS/UMTS core and tunnels user sessions to the GGSN. The SGSN sends data to and receives data from mobile stations, and maintains information about the location of a mobile station (MS). The SGSN communicates directly with the MS and the GGSN.
Serving GPRS support node (SGSN)—Connects the radio access network (RAN) to the GPRS/UMTS core and tunnels user sessions to the GGSN. The SGSN sends data to and receives data from mobile stations, and maintains information about the location of a mobile station (MS). The SGSN communicates directly with the MS and the GGSN. 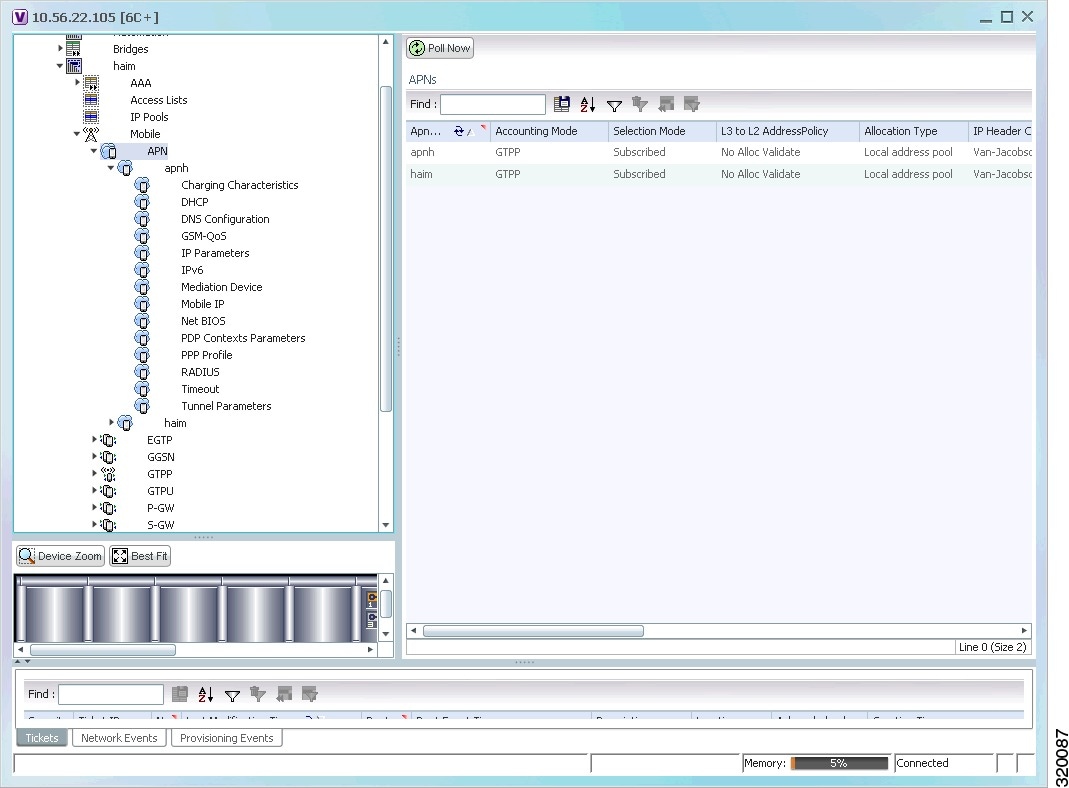
![]() Establish and maintain subscriber Internet Protocol (IP) or Point-to-Point Protocol (PPP) type Packet Data Protocol (PDP) contexts originated by either the mobile or the network.
Establish and maintain subscriber Internet Protocol (IP) or Point-to-Point Protocol (PPP) type Packet Data Protocol (PDP) contexts originated by either the mobile or the network. ![]() Provide charging detail records (CDRs) to the charging gateway ((CG), also known as the Charging Gateway Function (CGF)).
Provide charging detail records (CDRs) to the charging gateway ((CG), also known as the Charging Gateway Function (CGF)). ![]() Route data traffic between the subscriber's Mobile Station (MS) and a PDN such as the Internet or an intranet.
Route data traffic between the subscriber's Mobile Station (MS) and a PDN such as the Internet or an intranet. ![]() Viewing Additional Characteristics of a GGSN
Viewing Additional Characteristics of a GGSN ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > GGSN Container.
In the logical inventory window, choose Logical Inventory > Context > Mobile > GGSN Container. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Mobile > GGSN Container >GGSN.
In the logical inventory window, choose Logical Inventory > Mobile > GGSN Container >GGSN. ![]() Expand the GGSN node. The following list of characteristics configured for the GGSN are displayed:
Expand the GGSN node. The following list of characteristics configured for the GGSN are displayed: ![]() Charging Characteristics
Charging Characteristics ![]() Timers And QoS
Timers And QoS ![]() Choose Charging Characteristics to view the properties on the right pane. See Table 26-5 for more details on the charging characteristics configured for the GGSN.
Choose Charging Characteristics to view the properties on the right pane. See Table 26-5 for more details on the charging characteristics configured for the GGSN. ![]() Under the GGSN node, choose Timers and QoS to view the properties on the right pane. See Table 26-6 for more details on the Timers and QoS parameters configured for the GGSN.
Under the GGSN node, choose Timers and QoS to view the properties on the right pane. See Table 26-6 for more details on the Timers and QoS parameters configured for the GGSN. 
![]() You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > GTPU Container.
In the logical inventory window, choose Logical Inventory > Context > Mobile > GTPU Container. 
![]() You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time. ![]() Extensive parameter configuration flexibility for the APN.
Extensive parameter configuration flexibility for the APN. ![]() Extensive QoS support.
Extensive QoS support. ![]() Virtual APNs to allow differentiated services within a single APN. The APN that is supplied by the mobile station is evaluated by the GGSN in conjunction with multiple configurable parameters. Then the GGSN selects an APN configuration based on the supplied APN and those configurable parameters.
Virtual APNs to allow differentiated services within a single APN. The APN that is supplied by the mobile station is evaluated by the GGSN in conjunction with multiple configurable parameters. Then the GGSN selects an APN configuration based on the supplied APN and those configurable parameters. ![]() Traffic policing that governs the subscriber traffic flow if it violates or exceeds configured peak or committed data rates. The traffic policing attributes represent a QoS data rate limit configuration for both uplink and downlink directions.
Traffic policing that governs the subscriber traffic flow if it violates or exceeds configured peak or committed data rates. The traffic policing attributes represent a QoS data rate limit configuration for both uplink and downlink directions. ![]() Accounting—Various parameters regarding accounting possibilities, such as, charging characteristics, accounting mode (RADIUS server-based accounting, GTPP-based accounting, and so on.)
Accounting—Various parameters regarding accounting possibilities, such as, charging characteristics, accounting mode (RADIUS server-based accounting, GTPP-based accounting, and so on.) ![]() Authentication—Various parameters regarding authentication, such as, protocols used, like, Challenge Handshake Authentication Protocol (CHAP), Password Authentication Protocol (PAP), or none, default username/password, server group to use, and limit for number of PDP contexts.
Authentication—Various parameters regarding authentication, such as, protocols used, like, Challenge Handshake Authentication Protocol (CHAP), Password Authentication Protocol (PAP), or none, default username/password, server group to use, and limit for number of PDP contexts. ![]() Enhanced Charging—Name of rulebase to use, which holds the enhanced charging configuration (for example, eG-CDR variations, charging rules, prepaid/postpaid options, etc.).
Enhanced Charging—Name of rulebase to use, which holds the enhanced charging configuration (for example, eG-CDR variations, charging rules, prepaid/postpaid options, etc.). ![]() IP: Method for IP address allocation (e.g., local allocation by GGSN, Mobile IP, Dynamic Host Control Protocol (DHCP), DHCP relay, etc.). IP address ranges, with or without overlapping ranges across APNs.
IP: Method for IP address allocation (e.g., local allocation by GGSN, Mobile IP, Dynamic Host Control Protocol (DHCP), DHCP relay, etc.). IP address ranges, with or without overlapping ranges across APNs. ![]() Tunneling: PPP may be tunneled with L2TP. IPv4 may be tunneled with GRE, IP-in-IP or L2TP. Load-balancing across multiple tunnels. IPv6 is tunneled in IPv4. Additional tunneling techniques, such as, IPsec and VLAN tagging may be selected by the APN, but are configured in the GGSN independently from the APN.
Tunneling: PPP may be tunneled with L2TP. IPv4 may be tunneled with GRE, IP-in-IP or L2TP. Load-balancing across multiple tunnels. IPv6 is tunneled in IPv4. Additional tunneling techniques, such as, IPsec and VLAN tagging may be selected by the APN, but are configured in the GGSN independently from the APN. ![]() QoS: IPv4 header ToS handling. Traffic rate limits for different 3GPP traffic classes. Mapping of R98 QoS attributes to work around particular handset defections. Dynamic QoS renegotiation (described elsewhere).
QoS: IPv4 header ToS handling. Traffic rate limits for different 3GPP traffic classes. Mapping of R98 QoS attributes to work around particular handset defections. Dynamic QoS renegotiation (described elsewhere). ![]() Viewing Additional Characteristics of an APN
Viewing Additional Characteristics of an APN ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory >Context > Mobile > APN Container >APN.
In the logical inventory window, choose Logical Inventory >Context > Mobile > APN Container >APN. ![]() To view additional details configured for the APN, use the following tabs:
To view additional details configured for the APN, use the following tabs: ![]() Virtual APNs—A virtual APN is a non-physical entity that represents an access point that does not itself provide direct access to a real target network. A virtual APN can be used to consolidate access to multiple, physical target networks through a single access point.
Virtual APNs—A virtual APN is a non-physical entity that represents an access point that does not itself provide direct access to a real target network. A virtual APN can be used to consolidate access to multiple, physical target networks through a single access point. ![]() QCI to DSCP Mapping—Shows the mapping between QoS Class Indices (QCI) to Differentiated Services Code Point (DSCP).
QCI to DSCP Mapping—Shows the mapping between QoS Class Indices (QCI) to Differentiated Services Code Point (DSCP). ![]() QCI & ARP DSCP Mapping—Shows the mapping between QCI and Allocation/Retention Priority (ARP) to DSCP.
QCI & ARP DSCP Mapping—Shows the mapping between QCI and Allocation/Retention Priority (ARP) to DSCP. ![]() QoS Downlink Traffic Policing—Shows the attributes that represent QoS data rate limit configuration for downlink direction within the APN profile.
QoS Downlink Traffic Policing—Shows the attributes that represent QoS data rate limit configuration for downlink direction within the APN profile. ![]() QoS Uplink Traffic Policing—Shows the attributes that represent QoS data rate limit configuration for uplink direction within the APN profile.
QoS Uplink Traffic Policing—Shows the attributes that represent QoS data rate limit configuration for uplink direction within the APN profile. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > APN Container >APN.
In the logical inventory window, choose Logical Inventory > Context > Mobile > APN Container >APN. ![]() Expand the APN node. The following list of characteristics configured for the APN are displayed:
Expand the APN node. The following list of characteristics configured for the APN are displayed: ![]() Charging Characteristics—Charging characteristics configured on the APN for different subscribers.
Charging Characteristics—Charging characteristics configured on the APN for different subscribers. ![]() DHCP—Dynamic Host Control Protocol (DHCP) parameter configured, if the APN supports dynamic address assignment for PDP contexts.
DHCP—Dynamic Host Control Protocol (DHCP) parameter configured, if the APN supports dynamic address assignment for PDP contexts. ![]() GSM-QoS—Represents the negotiated QoS attribute reliability class based on the configuration provided for service data unit (SDU) error ratio and residual bit error rate (BER) attributes in the APN.
GSM-QoS—Represents the negotiated QoS attribute reliability class based on the configuration provided for service data unit (SDU) error ratio and residual bit error rate (BER) attributes in the APN. ![]() IP Parameters—Represents the APN parameters related to IP.
IP Parameters—Represents the APN parameters related to IP. ![]() IPv6—Represents IPv6 configurations and related services for the APN.
IPv6—Represents IPv6 configurations and related services for the APN. ![]() Mediation Device—Represents the mediation device used by the APN for communication with the subscriber.
Mediation Device—Represents the mediation device used by the APN for communication with the subscriber. ![]() Mobile IP—Represents mobile IP configuration of the APN.
Mobile IP—Represents mobile IP configuration of the APN. ![]() Net BIOS—Represents the NetBIOS server configuration used by the APN.
Net BIOS—Represents the NetBIOS server configuration used by the APN. ![]() PDP Contexts Parameters—Represents the PDP contexts supported by the APN.
PDP Contexts Parameters—Represents the PDP contexts supported by the APN. ![]() PPP Profile—Represents the PPP profile used by the APN.
PPP Profile—Represents the PPP profile used by the APN. ![]() RADIUS—Represents the APN parameters related to communication with the RADIUS server.
RADIUS—Represents the APN parameters related to communication with the RADIUS server. ![]() Timeout—Represents the timeout parameters of the APN.
Timeout—Represents the timeout parameters of the APN. ![]() Tunnel Parameters—Represents the parameters configured for tunneling between the GGSN and an external gateway for the APN.
Tunnel Parameters—Represents the parameters configured for tunneling between the GGSN and an external gateway for the APN. ![]() DNS Configuration—Represents the Domain Name System (DNS) settings configured on the APN.
DNS Configuration—Represents the Domain Name System (DNS) settings configured on the APN. ![]() Click each of one of these characteristics to view its properties on the right pane. See Table 26-12 for more details on the properties of each characteristics configured for the APN.
Click each of one of these characteristics to view its properties on the right pane. See Table 26-12 for more details on the properties of each characteristics configured for the APN. 
![]() You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time. ![]() Transfers CDRs between the Charging Data Function (CDF) and CGF.
Transfers CDRs between the Charging Data Function (CDF) and CGF. ![]() Redirects CDRs to another CGF.
Redirects CDRs to another CGF. ![]() Advertises to peers about its CDR transfer capability; for example, after a period of service down time.
Advertises to peers about its CDR transfer capability; for example, after a period of service down time. ![]() Prevents duplicate CDRs that might arise during redundancy operations. The CDR duplication prevention function is carried out by marking potentially duplicated CDR packets, and delegating the final duplicate deletion task to a CGF or the billing domain, instead of handling the possible duplicates solely by GTPP messaging.
Prevents duplicate CDRs that might arise during redundancy operations. The CDR duplication prevention function is carried out by marking potentially duplicated CDR packets, and delegating the final duplicate deletion task to a CGF or the billing domain, instead of handling the possible duplicates solely by GTPP messaging. ![]() Viewing Additional Characteristics of a GTPP
Viewing Additional Characteristics of a GTPP ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > GTPP Container.
In the logical inventory window, choose Logical Inventory > Context > Mobile > GTPP Container. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > GTPP Container >GTPP.
In the logical inventory window, choose Logical Inventory > Context > Mobile > GTPP Container >GTPP. ![]() Expand the GTPP node. The following list of characteristics configured for the GGSN are displayed:
Expand the GTPP node. The following list of characteristics configured for the GGSN are displayed: ![]() Accounting Server Failure Detection—Attributes of the CGF accounting server within the GTPP server group.
Accounting Server Failure Detection—Attributes of the CGF accounting server within the GTPP server group. ![]() CDR Attributes Indicator—Indicates whether associated attributes are enabled or disabled for CDR generation.
CDR Attributes Indicator—Indicates whether associated attributes are enabled or disabled for CDR generation. ![]() CDR Triggers—Attributes that trigger CDR generation.
CDR Triggers—Attributes that trigger CDR generation. ![]() Charging Agent— IP address and port of the system interface within the current context used to communicate with the CGF or the GTPP Storage Server (GSS).
Charging Agent— IP address and port of the system interface within the current context used to communicate with the CGF or the GTPP Storage Server (GSS). ![]() EGCDR Data Generation Configuration—Attributes that represent the GTPP eG-CDR data generation configuration.
EGCDR Data Generation Configuration—Attributes that represent the GTPP eG-CDR data generation configuration. ![]() Local Storage—Storage server information, if CDR storage mode is Local.
Local Storage—Storage server information, if CDR storage mode is Local. ![]() MBMS CDR Triggers—Attributes that trigger the MBMS CDR generation.
MBMS CDR Triggers—Attributes that trigger the MBMS CDR generation. ![]() Storage Server—Configuration information for the GTPP backup storage server.
Storage Server—Configuration information for the GTPP backup storage server. ![]() Click each of one of these characteristics to view its properties on the right pane. See Table 26-15 for more details on the properties of each characteristics configured for the GTPP.
Click each of one of these characteristics to view its properties on the right pane. See Table 26-15 for more details on the properties of each characteristics configured for the GTPP. 
![]() You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > EGTP Container.
In the logical inventory window, choose Logical Inventory > Context > Mobile > EGTP Container. 
![]() You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time. ![]() Increased downlink and uplink peak data rates
Increased downlink and uplink peak data rates ![]() Scalable bandwidth
Scalable bandwidth ![]() Improved spectral efficiency
Improved spectral efficiency ![]() All IP network
All IP network 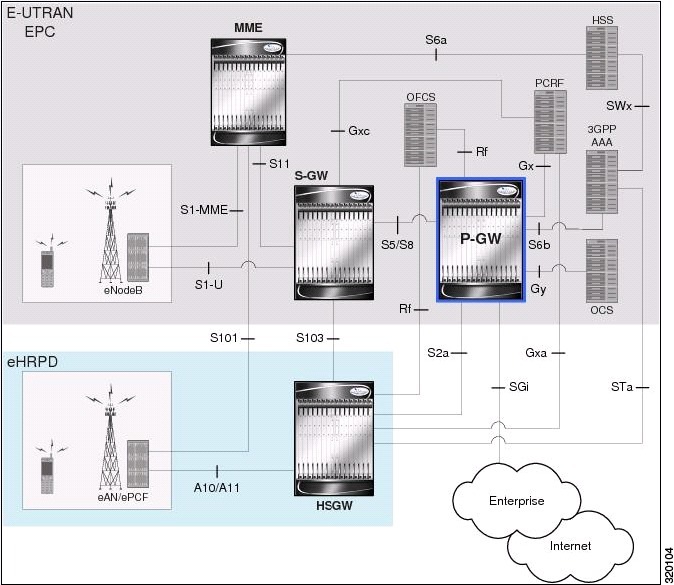
![]() Viewing the Layer 2 Tunnel Access Concentrator Configurations
Viewing the Layer 2 Tunnel Access Concentrator Configurations ![]() Monitoring the HRPD Serving Gateway
Monitoring the HRPD Serving Gateway ![]() Viewing the HSGW Configuration
Viewing the HSGW Configuration ![]() Monitoring Evolved Packet Data Gateway (ePDG)
Monitoring Evolved Packet Data Gateway (ePDG) ![]() Monitoring Packet Data Serving Node
Monitoring Packet Data Serving Node ![]() Viewing the Local Mobility Anchor Configuration
Viewing the Local Mobility Anchor Configuration ![]() Higher capacity—For a UE with one PDN connection that is passing through standalone S-GW and P-GW services consumes 2 license units because both S-GW and P-GW services account for it separately. SAE-GW as a single node consumes only one license unit for the same, thus increasing the capacity.
Higher capacity—For a UE with one PDN connection that is passing through standalone S-GW and P-GW services consumes 2 license units because both S-GW and P-GW services account for it separately. SAE-GW as a single node consumes only one license unit for the same, thus increasing the capacity. ![]() Cohesive configuration—Configuration and management of SAE-GW as a node is simpler to follow and logical to explain.
Cohesive configuration—Configuration and management of SAE-GW as a node is simpler to follow and logical to explain. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > SAE-GW Container.
In the logical inventory window, choose Logical Inventory > Context > Mobile > SAE-GW Container. ![]() Integration of multiple core network functions in a single node
Integration of multiple core network functions in a single node ![]() Multiple instances of P-GW can enable call localization and local breakout
Multiple instances of P-GW can enable call localization and local breakout ![]() High performance across all parameters like, signaling, throughput, density, and latency
High performance across all parameters like, signaling, throughput, density, and latency ![]() Integrated in-line services
Integrated in-line services ![]() Support for enhanced content charging, content filtering with blacklisting, dynamic network-based traffic optimization, application detection and optimization, stateful firewall, NAT translation, and lawful intercept
Support for enhanced content charging, content filtering with blacklisting, dynamic network-based traffic optimization, application detection and optimization, stateful firewall, NAT translation, and lawful intercept ![]() High-availability helps to ensure subscriber satisfaction
High-availability helps to ensure subscriber satisfaction ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > P-GW Container.
In the logical inventory window, choose Logical Inventory > Context > Mobile > P-GW Container. ![]() If the P-GW is associated with PLMNs, you can view the details of the PLMNs on clicking the specified P-GW.
If the P-GW is associated with PLMNs, you can view the details of the PLMNs on clicking the specified P-GW. 
![]() You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > S-GW Container.
In the logical inventory window, choose Logical Inventory > Context > Mobile > S-GW Container. ![]() If the S-GW is associated with PLMNs, you can view the PLMN entries on clicking the specified S-GW.
If the S-GW is associated with PLMNs, you can view the PLMN entries on clicking the specified S-GW. 
![]() You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time. 
![]() QCI-QoS mapping is applicable only for the `local' context in the logical inventory.
QCI-QoS mapping is applicable only for the `local' context in the logical inventory. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > local > Mobile > QCI-QoS Mapping.
In the logical inventory window, choose Logical Inventory > local > Mobile > QCI-QoS Mapping. 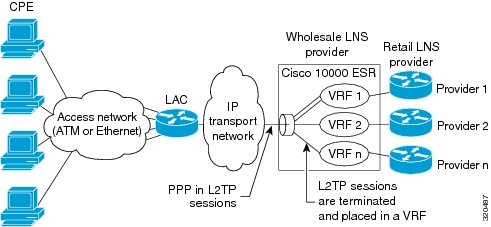
![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > LAC. The list of LAC services configured in Prime Network is displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > LAC. The list of LAC services configured in Prime Network is displayed in the content pane. ![]() From the LAC node, choose an LAC service. The LAC service details are displayed in the content pane as shown in Figure 26-5.
From the LAC node, choose an LAC service. The LAC service details are displayed in the content pane as shown in Figure 26-5. 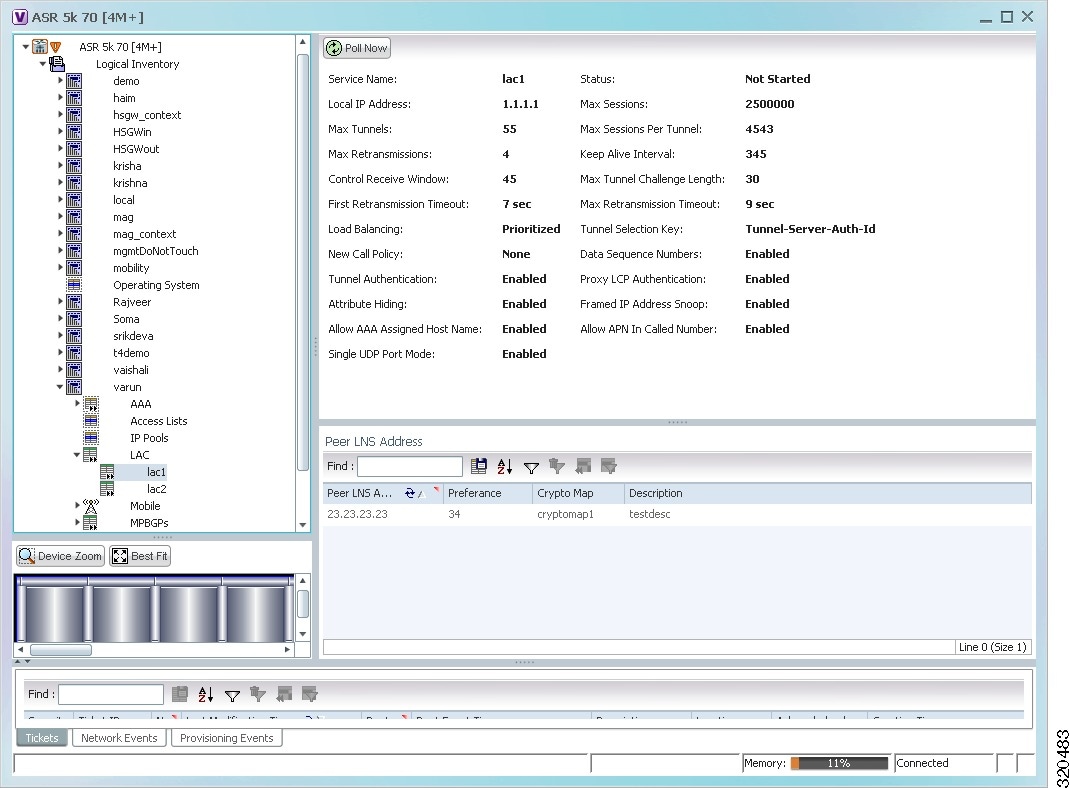
![]() Mobility anchoring for inter-eAN handoffs
Mobility anchoring for inter-eAN handoffs ![]() Transport level packet marking in the uplink and the downlink. For example, setting the DiffServ Code Point, based on the QCI of the associated EPS bearer
Transport level packet marking in the uplink and the downlink. For example, setting the DiffServ Code Point, based on the QCI of the associated EPS bearer ![]() Uplink and downlink charging per UE, PDN, and QCI
Uplink and downlink charging per UE, PDN, and QCI ![]() Downlink bearer binding based on policy information
Downlink bearer binding based on policy information ![]() Uplink bearer binding verification with packet dropping of UL traffic that does not comply with established uplink policy
Uplink bearer binding verification with packet dropping of UL traffic that does not comply with established uplink policy ![]() MAG functions for S2a mobility (i.e., Network-based mobility based on PMIPv6)
MAG functions for S2a mobility (i.e., Network-based mobility based on PMIPv6) ![]() Support for IPv4 and IPv6 address assignment
Support for IPv4 and IPv6 address assignment ![]() EAP Authenticator function
EAP Authenticator function ![]() Policy enforcement functions defined for the Gxa interface
Policy enforcement functions defined for the Gxa interface ![]() Robust Header Compression (RoHC)
Robust Header Compression (RoHC) ![]() Support for VSNCP and VSNP with UE
Support for VSNCP and VSNP with UE ![]() Support for packet-based or HDLC-like framing on auxiliary connections
Support for packet-based or HDLC-like framing on auxiliary connections ![]() IPv6 SLACC, generating RAs responding to RSs
IPv6 SLACC, generating RAs responding to RSs 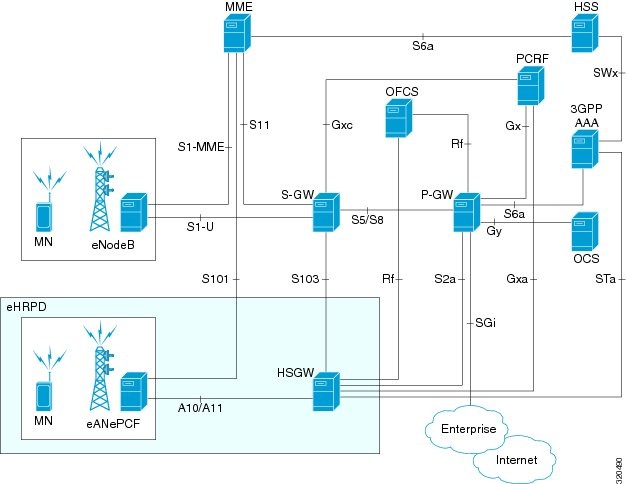
![]() Authentication
Authentication ![]() IP Address Allocation
IP Address Allocation ![]() Quality of Service
Quality of Service ![]() AAA, Policy and Charging
AAA, Policy and Charging ![]() EAP over PPP
EAP over PPP ![]() UE and HSGW negotiates EAP as the authentication protocol during LCP
UE and HSGW negotiates EAP as the authentication protocol during LCP ![]() HSGW is the EAP authenticator
HSGW is the EAP authenticator ![]() EAP-AKA' (trusted non-3GPP access procedure) as specified in TS 33.402
EAP-AKA' (trusted non-3GPP access procedure) as specified in TS 33.402 ![]() EAP is performed between UE and 3GPP AAA over PPP/STa
EAP is performed between UE and 3GPP AAA over PPP/STa ![]() Support for IPv4 and IPv6 addressing
Support for IPv4 and IPv6 addressing ![]() Types of PDNs - IPv4, IPv6 or IPv4v6
Types of PDNs - IPv4, IPv6 or IPv4v6 ![]() IPv6 addressing
IPv6 addressing ![]() Interface Identifier assigned during initial attach and used by UE to generate it's link local address
Interface Identifier assigned during initial attach and used by UE to generate it's link local address ![]() HSGW sends the assigned /64 bit prefix in RA to the UE
HSGW sends the assigned /64 bit prefix in RA to the UE ![]() Configure the 128-bits IPv6 address using IPv6 SLAAC (RFC 4862)
Configure the 128-bits IPv6 address using IPv6 SLAAC (RFC 4862) ![]() Optional IPv6 parameter configuration via stateless DHCPv6(Not supported)
Optional IPv6 parameter configuration via stateless DHCPv6(Not supported) ![]() IPv4 address
IPv4 address ![]() IPv4 address allocation during attach
IPv4 address allocation during attach ![]() Deferred address allocation using DHCPv4(Not supported)
Deferred address allocation using DHCPv4(Not supported) ![]() Option IPv4 parameter configuration via stateless DHCPv4(Not supported)
Option IPv4 parameter configuration via stateless DHCPv4(Not supported) ![]() HRPD Profile ID to QCI Mapping
HRPD Profile ID to QCI Mapping ![]() DSCP Marking
DSCP Marking ![]() UE Initiated Dedicated Bearer Resource Establishment
UE Initiated Dedicated Bearer Resource Establishment ![]() QCI to DSCP Mapping
QCI to DSCP Mapping ![]() EAP Authentication (STa)
EAP Authentication (STa) ![]() Rf Diameter Accounting
Rf Diameter Accounting ![]() AAA Server Groups
AAA Server Groups ![]() Dynamic Policy and Charging: Gxa Reference Interface
Dynamic Policy and Charging: Gxa Reference Interface ![]() Intelligent Traffic Control
Intelligent Traffic Control ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > HSGW. The list of HSGW services configured in Prime Network are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > HSGW. The list of HSGW services configured in Prime Network are displayed in the content pane. ![]() From the HSGW node, choose a HSGW service. The HSGW service details are displayed in the content pane as shown in Figure 26-7.
From the HSGW node, choose a HSGW service. The HSGW service details are displayed in the content pane as shown in Figure 26-7. 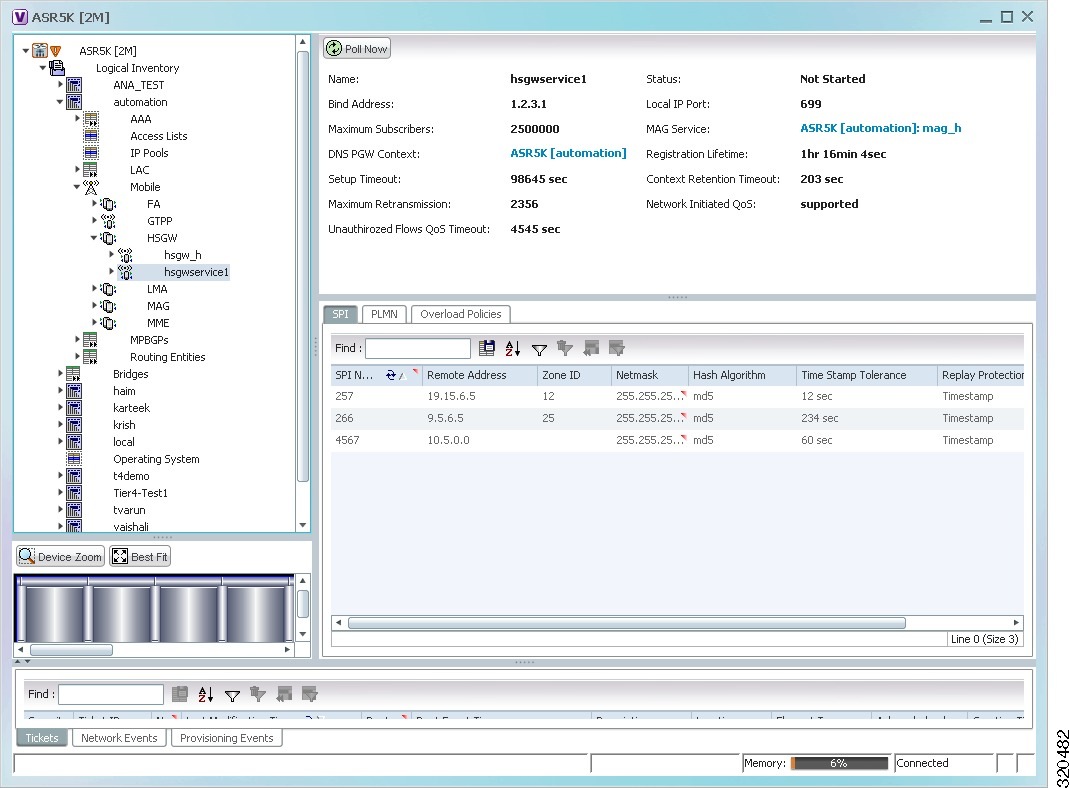
![]() A10/A11 Properties—The A10/A11 interface (also known as R-P interface for RAN-to-PDSN) supports the A10 protocol for user data transport between the PCF and PDSN, and the A11 protocol for the associated signaling. A11 signaling messages are also used for passing accounting related and other information from the PCF to the PDSN. The A10/A11 interfaces support mobility between PCFs under the same PDSN.
A10/A11 Properties—The A10/A11 interface (also known as R-P interface for RAN-to-PDSN) supports the A10 protocol for user data transport between the PCF and PDSN, and the A11 protocol for the associated signaling. A11 signaling messages are also used for passing accounting related and other information from the PCF to the PDSN. The A10/A11 interfaces support mobility between PCFs under the same PDSN. ![]() GRE Parameters—Generic Routing Encapsulation (GRE) is a tunneling protocol developed by Cisco Systems that can encapsulate a wide variety of network layer protocols inside virtual point-to-point links over an Internet Protocol internetwork.
GRE Parameters—Generic Routing Encapsulation (GRE) is a tunneling protocol developed by Cisco Systems that can encapsulate a wide variety of network layer protocols inside virtual point-to-point links over an Internet Protocol internetwork. ![]() IP Source Violation—IP source violations occur when the PDSN receives packets from a subscriber where the source address is not the same as the address given to the subscriber, and hence get discarded.
IP Source Violation—IP source violations occur when the PDSN receives packets from a subscriber where the source address is not the same as the address given to the subscriber, and hence get discarded. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > HSGW > HSGW service > A10/A11 Properties. The configuration details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > HSGW > HSGW service > A10/A11 Properties. The configuration details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > HSGW > HSGW service > GRE Parameters. The relevant details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > HSGW > HSGW service > GRE Parameters. The relevant details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > HSGW > HSGW service > IP Source Violation. The configuration details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > HSGW > HSGW service > IP Source Violation. The configuration details are displayed in the content pane. 
![]() You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time. 
![]() In the GUI, parameters that are displayed in bold text are mandatory.
In the GUI, parameters that are displayed in bold text are mandatory. ![]() Obtains an IP address from a Local Mobility Anchor (LMA) and assigns it to an MN
Obtains an IP address from a Local Mobility Anchor (LMA) and assigns it to an MN ![]() Retains the IP address of an MN when the MN roams across MAGs
Retains the IP address of an MN when the MN roams across MAGs ![]() Tunnels traffic from an MN to LMA
Tunnels traffic from an MN to LMA ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > MAG > MAG service. The configuration details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > MAG > MAG service. The configuration details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > local > Mobile > Profile > Profile-QCI Mapping > Profile-QCI Mapping. The mapping details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > local > Mobile > Profile > Profile-QCI Mapping > Profile-QCI Mapping. The mapping details are displayed in the content pane. 
![]() You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time. 
![]() In the GUI, parameters that are displayed in bold text are mandatory.
In the GUI, parameters that are displayed in bold text are mandatory. 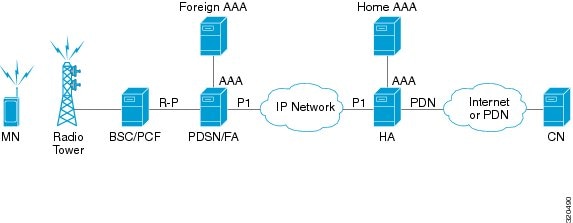
![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent. The list of home agent services configured in Prime Network are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent. The list of home agent services configured in Prime Network are displayed in the content pane. ![]() From the Home Agent node, choose a home agent service. The home agent service details are displayed in the content pane as shown in Figure 26-9.
From the Home Agent node, choose a home agent service. The home agent service details are displayed in the content pane as shown in Figure 26-9. 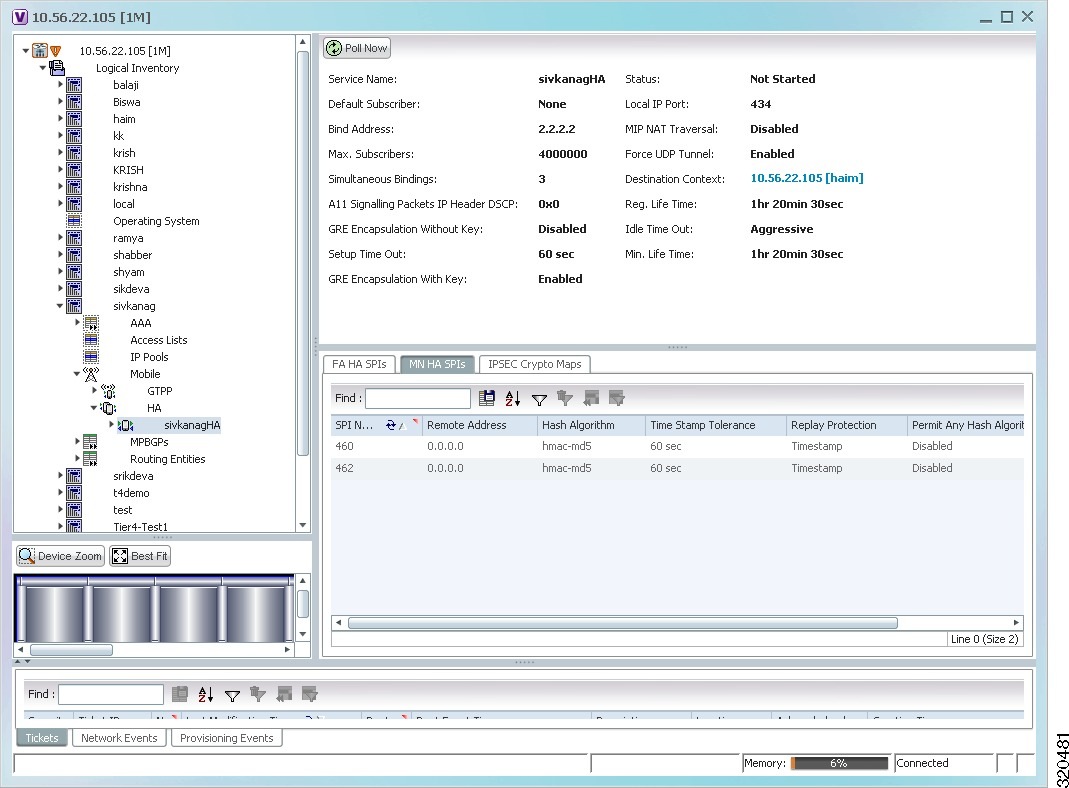
![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent > Home agent service > AAA. The AAA configuration details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent > Home agent service > AAA. The AAA configuration details are displayed in the content pane. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent > Home agent service > GRE. The GRE configuration details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent > Home agent service > GRE. The GRE configuration details are displayed in the content pane. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent > Home agent service > Policy. The Policy configuration details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent > Home agent service > Policy. The Policy configuration details are displayed in the content pane. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent > Home agent service > Registration Revocation. The configuration details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > Home Agent > Home agent service > Registration Revocation. The configuration details are displayed in the content pane. 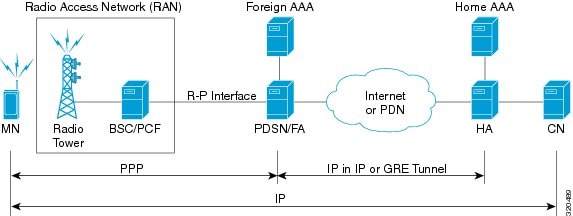
![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > FA. The list of Foreign agents configured in Prime Network are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > FA. The list of Foreign agents configured in Prime Network are displayed in the content pane. ![]() From the FA node, choose a FA service. The FA service details are displayed in the content pane as shown in Figure 26-11.
From the FA node, choose a FA service. The FA service details are displayed in the content pane as shown in Figure 26-11. 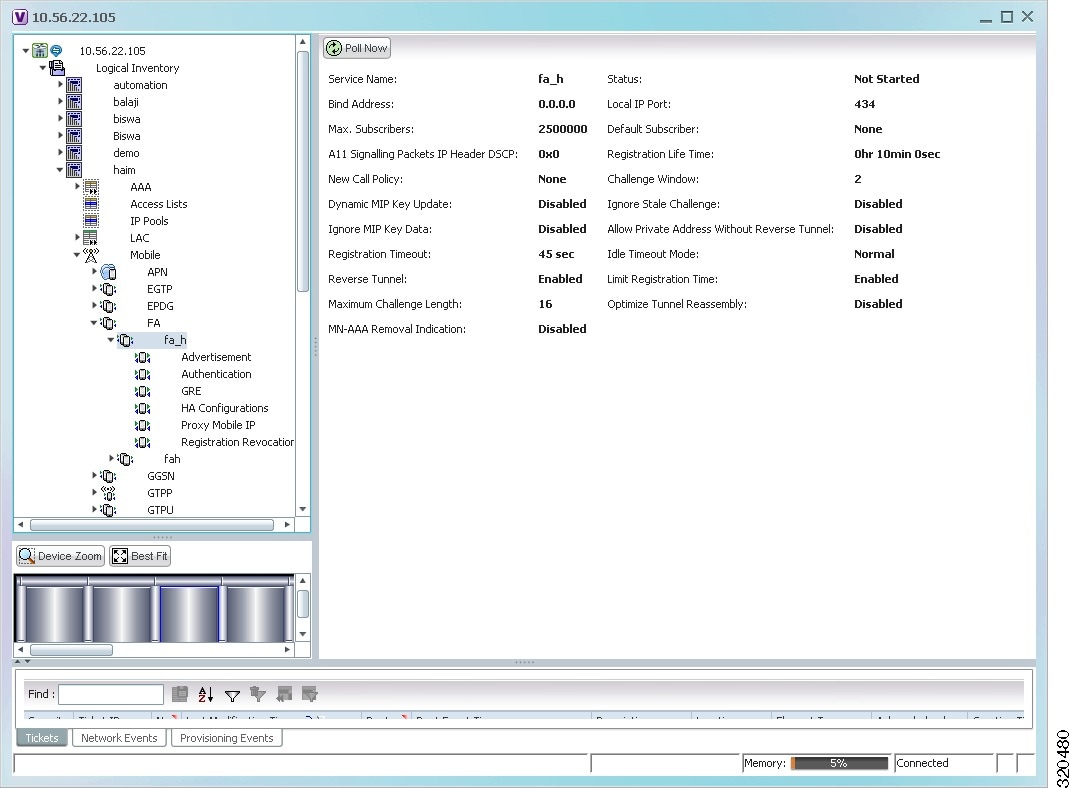
![]() Advertisement—Foreign agents advertise their presence on their attached links by periodically multicasting or broadcasting messages called agent advertisements. Mobile nodes listen to these advertisements and determine if they are connected to their home link or foreign link. Rather than waiting for agent advertisements, an MN can also send an agent solicitation. This solicitation forces any agents on the link to immediately send an agent advertisement.
Advertisement—Foreign agents advertise their presence on their attached links by periodically multicasting or broadcasting messages called agent advertisements. Mobile nodes listen to these advertisements and determine if they are connected to their home link or foreign link. Rather than waiting for agent advertisements, an MN can also send an agent solicitation. This solicitation forces any agents on the link to immediately send an agent advertisement. ![]() Authentication—Authentication verifies users before they are allowed access to the network and network services.
Authentication—Authentication verifies users before they are allowed access to the network and network services. ![]() GRE—Generic routing encapsulation (GRE) is a tunneling protocol used by Mobile IP. The GRE tunnel interface creates a virtual point-to-point link between two routers at remote points over an IP internetwork. If the GRE for Cisco Mobile Networks feature is enabled, the mobile router will request GRE encapsulation in the registration request only if the FA advertises that it is capable of GRE encapsulation (the G bit is set in the advertisement). If the registration request is successful, packets will be tunneled using GRE encapsulation. If the GRE for Cisco Mobile Networks feature is enabled and the mobile router is using collocated care-of address (CCoA), the mobile router will attempt to register with the HA using GRE encapsulation. If the registration request is successful, packets will be tunneled using GRE encapsulation.
GRE—Generic routing encapsulation (GRE) is a tunneling protocol used by Mobile IP. The GRE tunnel interface creates a virtual point-to-point link between two routers at remote points over an IP internetwork. If the GRE for Cisco Mobile Networks feature is enabled, the mobile router will request GRE encapsulation in the registration request only if the FA advertises that it is capable of GRE encapsulation (the G bit is set in the advertisement). If the registration request is successful, packets will be tunneled using GRE encapsulation. If the GRE for Cisco Mobile Networks feature is enabled and the mobile router is using collocated care-of address (CCoA), the mobile router will attempt to register with the HA using GRE encapsulation. If the registration request is successful, packets will be tunneled using GRE encapsulation. ![]() HA Configurations—Once the mobile node roams to a new network, it must register with the home agent as being away from home. Its registration is sent by way of the Foreign Agent (FA), the router providing service on the foreign network. A security association between the home agent (HA) and the foreign agent (FA) is mandatory.
HA Configurations—Once the mobile node roams to a new network, it must register with the home agent as being away from home. Its registration is sent by way of the Foreign Agent (FA), the router providing service on the foreign network. A security association between the home agent (HA) and the foreign agent (FA) is mandatory. ![]() Proxy Mobile IP—Proxy Mobile IP supports Mobile IP for wireless nodes without requiring specialized software for those devices. The wireless access point acts as a proxy on behalf of wireless clients that are not aware of the fact that they have roamed onto a different Layer 3 network. The access point handles the IRDP communications to the foreign agent and handles registrations to the home agent.
Proxy Mobile IP—Proxy Mobile IP supports Mobile IP for wireless nodes without requiring specialized software for those devices. The wireless access point acts as a proxy on behalf of wireless clients that are not aware of the fact that they have roamed onto a different Layer 3 network. The access point handles the IRDP communications to the foreign agent and handles registrations to the home agent. ![]() Registration Revocation—Registration Revocation is a method by which a mobility agent (one that provides Mobile IP services to a mobile node) can notify the other mobility agent of the termination of a registration due to administrative reasons or MIP handoff. When a mobile changes its point of attachment (FA), or needs to terminate the session administratively, the HA sends a registration revocation message to the old FA. The old FA tears down the session and sends a registration revocation acknowledgement message to the HA. Additionally, if the PDSN/FA needs to terminate the session administratively, the FA sends a registration revocation message to the HA. The HA deletes the binding for the mobile, and sends a registration revocation acknowledgement to FA.
Registration Revocation—Registration Revocation is a method by which a mobility agent (one that provides Mobile IP services to a mobile node) can notify the other mobility agent of the termination of a registration due to administrative reasons or MIP handoff. When a mobile changes its point of attachment (FA), or needs to terminate the session administratively, the HA sends a registration revocation message to the old FA. The old FA tears down the session and sends a registration revocation acknowledgement message to the HA. Additionally, if the PDSN/FA needs to terminate the session administratively, the FA sends a registration revocation message to the HA. The HA deletes the binding for the mobile, and sends a registration revocation acknowledgement to FA. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > Advertisement. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > Advertisement. The details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > Authentication. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > Authentication. The details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > GRE. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > GRE. The details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > HA. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > HA. The details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > Proxy Mobile IP. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > Proxy Mobile IP. The details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > Registration Revocation. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > FA > FA service > Registration Revocation. The details are displayed in the content pane. 
![]() You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time. 
![]() In the GUI, parameters that are displayed in bold text are mandatory.
In the GUI, parameters that are displayed in bold text are mandatory. ![]() General Packet Radio Service (GPRS). See GPRS/UMTS Networks - An Overview.
General Packet Radio Service (GPRS). See GPRS/UMTS Networks - An Overview. ![]() Global System for Mobile communication (GSM)
Global System for Mobile communication (GSM) ![]() Universal Mobile Telecommunication System (UMTS). See GPRS/UMTS Networks - An Overview.
Universal Mobile Telecommunication System (UMTS). See GPRS/UMTS Networks - An Overview. ![]() Worldwide Interoperability for Microwave Access (WiMAX)
Worldwide Interoperability for Microwave Access (WiMAX) ![]() CDMA2000
CDMA2000 ![]() Wireless local area network (WLAN)
Wireless local area network (WLAN) ![]() Fixed networks
Fixed networks 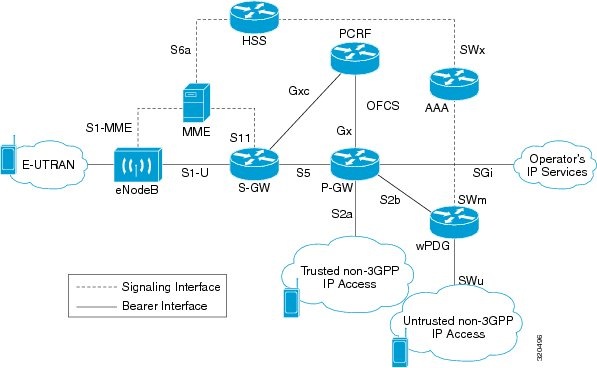
![]() RFC 2401, Security Architecture for the Internet Protocol
RFC 2401, Security Architecture for the Internet Protocol ![]() RFC 2402, IP Authentication Header (AH)
RFC 2402, IP Authentication Header (AH) ![]() RFC 2406, IP Encapsulating Security Payload (ESP)
RFC 2406, IP Encapsulating Security Payload (ESP) ![]() RFC 2409, The Internet Key Exchange (IKE)
RFC 2409, The Internet Key Exchange (IKE) ![]() RFC-3193, Securing L2TP using IPSEC, November 2001
RFC-3193, Securing L2TP using IPSEC, November 2001 ![]() PDN Access: Subscriber IP traffic is routed over an IPSec tunnel from the system to a secure gateway on the packet data network (PDN) as determined by access control list (ACL) criteria.
PDN Access: Subscriber IP traffic is routed over an IPSec tunnel from the system to a secure gateway on the packet data network (PDN) as determined by access control list (ACL) criteria. ![]() Mobile IP: Mobile IP control signals and subscriber data is encapsulated in IPSec tunnels that are established between foreign agents (FAs) and home agents (HAs) over the Pi interfaces.
Mobile IP: Mobile IP control signals and subscriber data is encapsulated in IPSec tunnels that are established between foreign agents (FAs) and home agents (HAs) over the Pi interfaces. ![]() Crypto template—Used to define the IKEv2 and IPSec policies. In other words, it includes IKEv2 and IPSec parameters for keepalive, lifetime, NAT-T and cryptographic and authentication algorithms.
Crypto template—Used to define the IKEv2 and IPSec policies. In other words, it includes IKEv2 and IPSec parameters for keepalive, lifetime, NAT-T and cryptographic and authentication algorithms. ![]() EAP Profile—Defines the EAP authentication method and associated parameters.
EAP Profile—Defines the EAP authentication method and associated parameters. ![]() Transform Set—Define the negotiable algorithms for IKE SAs (Security Associations) and Child SAs to enable calls to connect to the ePDG.
Transform Set—Define the negotiable algorithms for IKE SAs (Security Associations) and Child SAs to enable calls to connect to the ePDG. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Security Association > Crypto Template. The list of crypto templates are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Security Association > Crypto Template. The list of crypto templates are displayed in the content pane. ![]() In the Crypto Template node, choose the crypto template. The template details are displayed in the content pane. Figure 26-13 displays the crytpo template details.
In the Crypto Template node, choose the crypto template. The template details are displayed in the content pane. Figure 26-13 displays the crytpo template details. 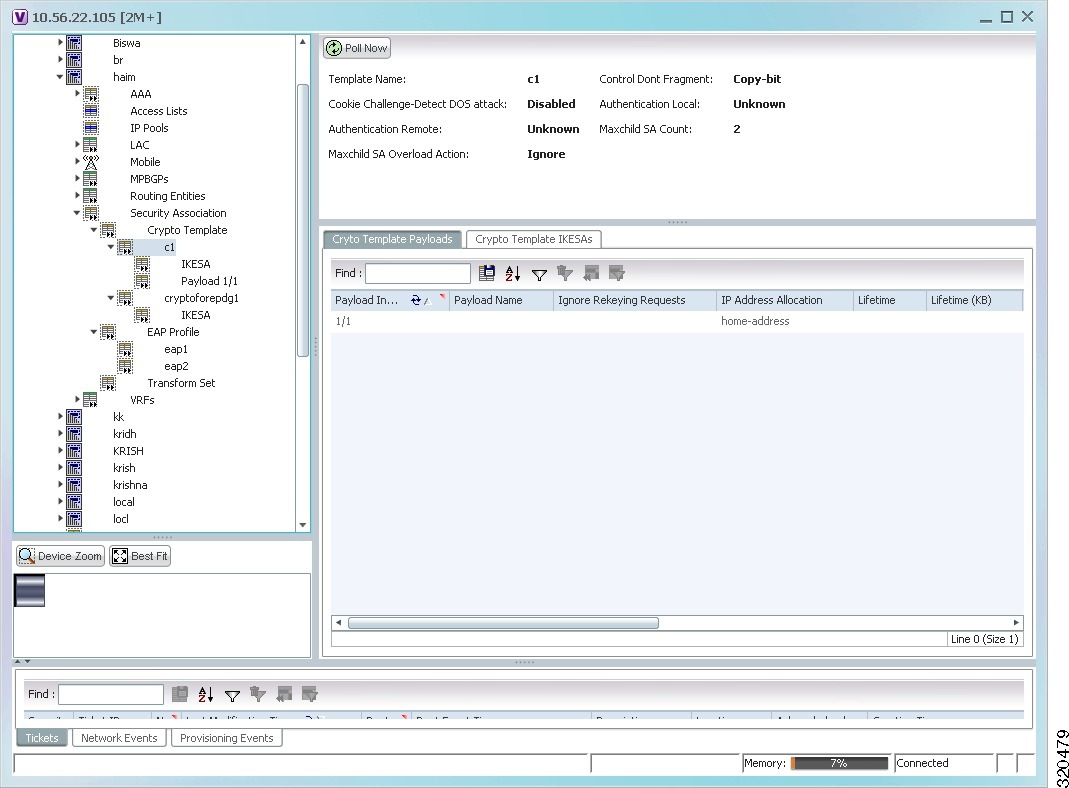
![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Security Association > EAP Profile. The list of profiles are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Security Association > EAP Profile. The list of profiles are displayed in the content pane. ![]() In the EAP Profile node, choose the profile. The profile details are displayed in the content pane.
In the EAP Profile node, choose the profile. The profile details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Security Association > Transform Set > IKEv2 IPSec Transform Set or IKEv2 Transform set. The list of profiles are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Security Association > Transform Set > IKEv2 IPSec Transform Set or IKEv2 Transform set. The list of profiles are displayed in the content pane. ![]() In the IKEv2 IPSec Transform Set or IKEv2 Transform set node, choose the transform set. The relevant details are displayed in the content pane.
In the IKEv2 IPSec Transform Set or IKEv2 Transform set node, choose the transform set. The relevant details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > EPDG. The list of EPDG services configured in Prime Network are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > EPDG. The list of EPDG services configured in Prime Network are displayed in the content pane. ![]() From the EPDG node, choose an EPDG service. The EPDG service details are displayed in the content pane.
From the EPDG node, choose an EPDG service. The EPDG service details are displayed in the content pane. 
![]() You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time. 
![]() In the GUI, parameters that are displayed in bold text are mandatory.
In the GUI, parameters that are displayed in bold text are mandatory. ![]() Simple IP—In this protocol, the mobile user is assigned an IP address dynamically. The user can use this IP address within a defined geographical area, which is lost when the user moves out of the area. If the user moves out of the designated area, they must register with the service provider again to obtain a new IP address. Figure 26-14 depicts the working of this protocol.
Simple IP—In this protocol, the mobile user is assigned an IP address dynamically. The user can use this IP address within a defined geographical area, which is lost when the user moves out of the area. If the user moves out of the designated area, they must register with the service provider again to obtain a new IP address. Figure 26-14 depicts the working of this protocol. 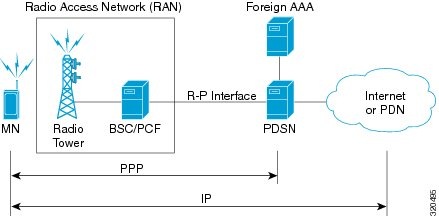
![]() Mobile IP—In this protocol, the mobile user is assigned a static or dynamic IP address, which is basically the "home address" assigned by the user's Home Agent (HA). Even if the user moves out of the home network, the IP address does not change or is not lost. This enables the user to use applications that require seamless mobility such as transferring files. How does this work? The Mobile IP protocol provides a network-layer solution that allows mobile nodes to receive IP packets from their home network even when they are connected to a visitor network. The PDSN in the visitor's network performs as a Foreign Agent (FA), which assigns a Care-of-Address (CoA) to the mobile node and establishes a virtual session with the mobile node's HA. IP packets are encapsulated into IP tunnels and transported between the FA, HA and mobile node. Figure 26-15 depicts the working of this protocol.
Mobile IP—In this protocol, the mobile user is assigned a static or dynamic IP address, which is basically the "home address" assigned by the user's Home Agent (HA). Even if the user moves out of the home network, the IP address does not change or is not lost. This enables the user to use applications that require seamless mobility such as transferring files. How does this work? The Mobile IP protocol provides a network-layer solution that allows mobile nodes to receive IP packets from their home network even when they are connected to a visitor network. The PDSN in the visitor's network performs as a Foreign Agent (FA), which assigns a Care-of-Address (CoA) to the mobile node and establishes a virtual session with the mobile node's HA. IP packets are encapsulated into IP tunnels and transported between the FA, HA and mobile node. Figure 26-15 depicts the working of this protocol. 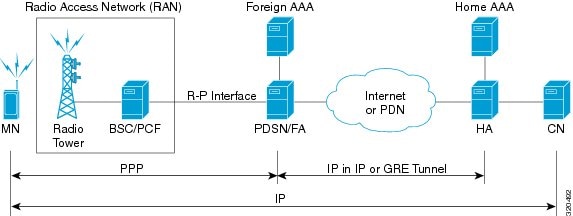
![]() Proxy Mobile IP—This protocol provides a mobility solution for subscribers whose mobile nodes do not support the Mobile IP protocol. On behalf of the mobile node, PDSN proxies the Mobile IP tunnel with the HA. In turn, the service provider or the home agent assigns an IP address to the subscriber. This IP address does not change or is not lost even if the user moves out of the home network.
Proxy Mobile IP—This protocol provides a mobility solution for subscribers whose mobile nodes do not support the Mobile IP protocol. On behalf of the mobile node, PDSN proxies the Mobile IP tunnel with the HA. In turn, the service provider or the home agent assigns an IP address to the subscriber. This IP address does not change or is not lost even if the user moves out of the home network. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN. The list of PDSN services configured in Prime Network are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN. The list of PDSN services configured in Prime Network are displayed in the content pane. ![]() From the PDSN node, choose a PDSN service. The PDSN service details are displayed in the content pane as shown in Figure 26-16.
From the PDSN node, choose a PDSN service. The PDSN service details are displayed in the content pane as shown in Figure 26-16. 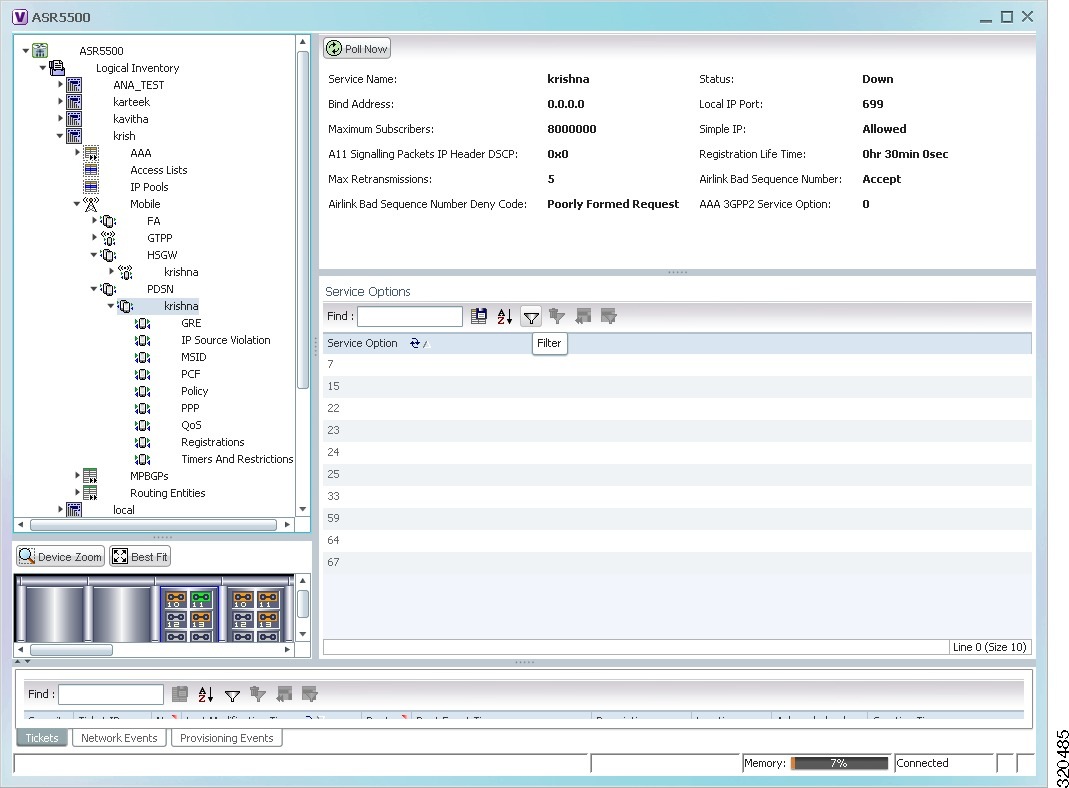
![]() GRE
GRE ![]() IP Source Violation
IP Source Violation ![]() MSID
MSID ![]() PCF
PCF ![]() Policy
Policy ![]() PPP
PPP ![]() QoS
QoS ![]() Registrations
Registrations ![]() Timers and Restrictions
Timers and Restrictions ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > GRE. The GRE details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > GRE. The GRE details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > IP Source Violation. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > IP Source Violation. The details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > MSID. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > MSID. The details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > PCF. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > PCF. The details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > Policy. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > Policy. The details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > PPP. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > PPP. The details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > QoS. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > QoS. The details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > Registrations. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > Registrations. The details are displayed in the content pane. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > Timers and Restrictions. The details are displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > PDSN > PDSN service > Timers and Restrictions. The details are displayed in the content pane. 
![]() You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time. 
![]() In the GUI, parameters that are displayed in bold text are mandatory.
In the GUI, parameters that are displayed in bold text are mandatory. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > Context > Mobile > LMA. The list of LMA services configured in Prime Network is displayed in the content pane.
In the logical inventory window, choose Logical Inventory > Context > Mobile > LMA. The list of LMA services configured in Prime Network is displayed in the content pane. ![]() From the LMA node, choose an LMA service. The LMA service details are displayed in the content pane as shown in Figure 26-17.
From the LMA node, choose an LMA service. The LMA service details are displayed in the content pane as shown in Figure 26-17. 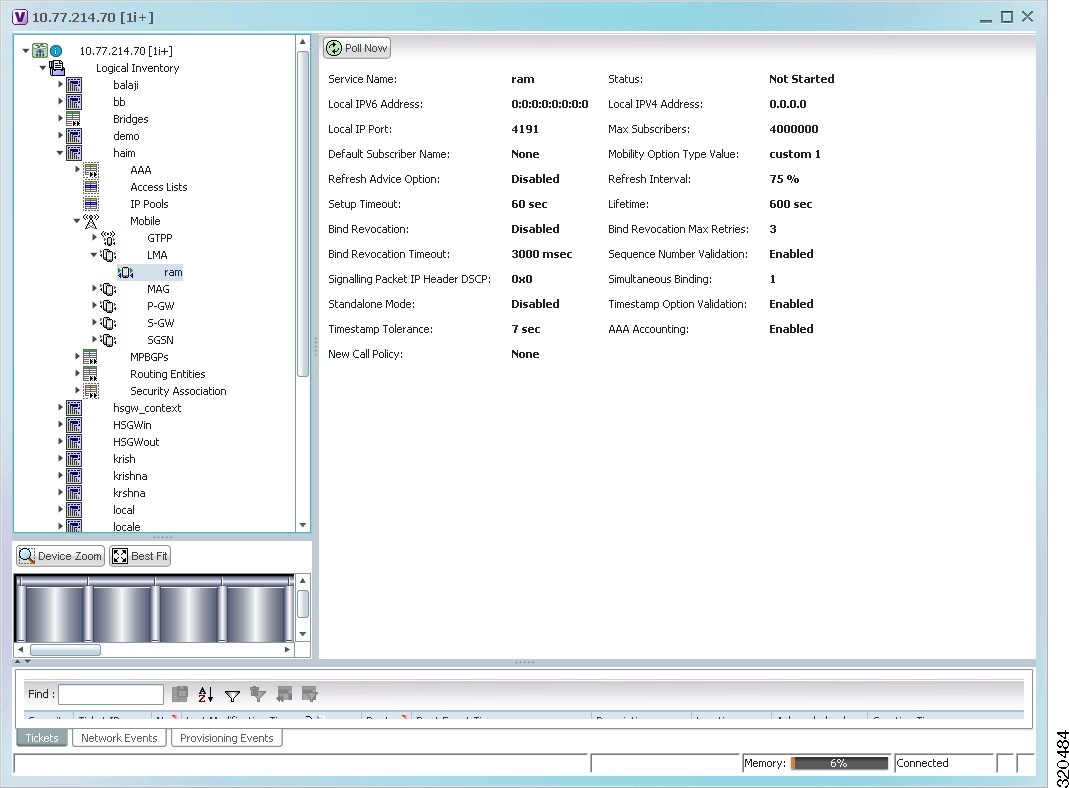

![]() Operator policies and APN profiles are applicable only for the `local' context in the logical inventory.
Operator policies and APN profiles are applicable only for the `local' context in the logical inventory. ![]() Call-control profiles
Call-control profiles ![]() IMEI profiles (SGSN only)
IMEI profiles (SGSN only) ![]() APN profiles
APN profiles ![]() APN remap tables
APN remap tables ![]() Operator policies
Operator policies ![]() IMSI ranges
IMSI ranges ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > local > Mobile > Policy > Operator Policies
In the logical inventory window, choose Logical Inventory > local > Mobile > Policy > Operator Policies ![]() An APN is provided in the activation request that does not match with any of the subscribed APNs; either a different APN was entered or the APN could have been misspelled. In such situations, the SGSN rejects the activation request. It is possible to correct the APN, creating a valid name so that the activation request is not rejected.
An APN is provided in the activation request that does not match with any of the subscribed APNs; either a different APN was entered or the APN could have been misspelled. In such situations, the SGSN rejects the activation request. It is possible to correct the APN, creating a valid name so that the activation request is not rejected. ![]() In some cases, an operator might want to force certain devices or users to use a specific APN. For example, a set of mobile users may need to be directed to a specific APN. In such situations, the operator needs to override the selected APN.
In some cases, an operator might want to force certain devices or users to use a specific APN. For example, a set of mobile users may need to be directed to a specific APN. In such situations, the operator needs to override the selected APN. ![]() APN aliasing—Maps incoming APN to a different APN, based on partial string match (MME and SGSN) or matching charging characteristic (SGSN only).
APN aliasing—Maps incoming APN to a different APN, based on partial string match (MME and SGSN) or matching charging characteristic (SGSN only). ![]() Wildcard APN—Allows APN to be provided by the SGSN, when wildcard subscription is present and the user has not requested an APN.
Wildcard APN—Allows APN to be provided by the SGSN, when wildcard subscription is present and the user has not requested an APN. ![]() Default APN—Allows a configured default APN to be used, when the requested APN cannot be used.
Default APN—Allows a configured default APN to be used, when the requested APN cannot be used. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > local > Mobile > > Profile > APN Remaps
In the logical inventory window, choose Logical Inventory > local > Mobile > > Profile > APN Remaps ![]() If a default APN is configured for the remap, click the Default APN node under the APN remap. You can view the following details on the content pane.
If a default APN is configured for the remap, click the Default APN node under the APN remap. You can view the following details on the content pane. ![]() Enable or disable a direct tunnel (DT) per APN (SGSN).
Enable or disable a direct tunnel (DT) per APN (SGSN). ![]() Define charging characters for calls associated with a specific APN.
Define charging characters for calls associated with a specific APN. ![]() Identify a specific GGSN to be used for calls associated with a specific APN (SGSN).
Identify a specific GGSN to be used for calls associated with a specific APN (SGSN). ![]() Define various quality of service (QoS) parameters to be applied to calls associated with a specific APN.
Define various quality of service (QoS) parameters to be applied to calls associated with a specific APN. ![]() Restrict or allow PDP context activation on the basis of access type for calls associated with a specific APN.
Restrict or allow PDP context activation on the basis of access type for calls associated with a specific APN. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > local > Mobile > Profile > APN Profiles.
In the logical inventory window, choose Logical Inventory > local > Mobile > Profile > APN Profiles. ![]() Uplink Traffic Policing Entries/Downlink Traffic Policing Entries
Uplink Traffic Policing Entries/Downlink Traffic Policing Entries ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > local > Mobile > Profile > APN Profiles > APN Profile.
In the logical inventory window, choose Logical Inventory > local > Mobile > Profile > APN Profiles > APN Profile. ![]() Expand the APN Profile node. The following list of characteristics configured for the APN profile are displayed:
Expand the APN Profile node. The following list of characteristics configured for the APN profile are displayed: ![]() PDP Inactivity Actions—Attributes related to PDP data inactivity. Once a data communication is in progress there are cases where this data communication can be inactive after some time, for example, when the user has locked the phone after browsing the internet or when the battery suddenly drains out. In such a case, the SGSN can take a configured action based on this inactivity. The inactivity timeout and the actions that can be taken based on certain conditions are modeled in this configuration.
PDP Inactivity Actions—Attributes related to PDP data inactivity. Once a data communication is in progress there are cases where this data communication can be inactive after some time, for example, when the user has locked the phone after browsing the internet or when the battery suddenly drains out. In such a case, the SGSN can take a configured action based on this inactivity. The inactivity timeout and the actions that can be taken based on certain conditions are modeled in this configuration. ![]() QoS to DSCP Mapping (Downlink) / Qos to DSCP Mapping (Uplink)—Mapping of QoS parameters to DSCP. Configuration of the local values for the traffic class (TC) parameters for QoS configured for the APN.
QoS to DSCP Mapping (Downlink) / Qos to DSCP Mapping (Uplink)—Mapping of QoS parameters to DSCP. Configuration of the local values for the traffic class (TC) parameters for QoS configured for the APN. ![]() PDP Restrictions (UMTS) / PDP Restrictions (GPRS)—Activation restrictions on PDP.
PDP Restrictions (UMTS) / PDP Restrictions (GPRS)—Activation restrictions on PDP. ![]() Click each of one of these characteristics to view its properties on the right pane. See Table 26-68 for more details on the properties of each characteristics configured for the APN profile.
Click each of one of these characteristics to view its properties on the right pane. See Table 26-68 for more details on the properties of each characteristics configured for the APN profile. ![]() Shallow Packet Inspection—Inspection of the Layer 3 (IP header) and Layer 4 (for example, UDP or TCP header) information.
Shallow Packet Inspection—Inspection of the Layer 3 (IP header) and Layer 4 (for example, UDP or TCP header) information. ![]() Deep Packet Inspection—Inspection of Layer 7 and above information. This functionality includes:
Deep Packet Inspection—Inspection of Layer 7 and above information. This functionality includes: ![]() Detection of Uniform Resource Identifier (URI) information at level 7 (example, HTTP)
Detection of Uniform Resource Identifier (URI) information at level 7 (example, HTTP) ![]() Identification of true destination in the case of terminating proxies, where shallow packet inspection only reveals the destination IP address/port number of a terminating proxy
Identification of true destination in the case of terminating proxies, where shallow packet inspection only reveals the destination IP address/port number of a terminating proxy ![]() Routing Ruledefs—Routing ruledefs are used to route packets to content analyzers. Routing ruledefs determine which content analyzer to route the packet to, when the protocol fields and/or protocol states in ruledef expression are true.
Routing Ruledefs—Routing ruledefs are used to route packets to content analyzers. Routing ruledefs determine which content analyzer to route the packet to, when the protocol fields and/or protocol states in ruledef expression are true. ![]() Charging Ruledefs—Charging ruledefs are used to specify what action to take based on the analysis done by the content analyzers. Actions can include redirection, charge value, and billing record emission.
Charging Ruledefs—Charging ruledefs are used to specify what action to take based on the analysis done by the content analyzers. Actions can include redirection, charge value, and billing record emission. ![]() URL Blacklisting—With this solution, all HTTP/WAP URLs in subscriber requests are matched against a database of blacklisted URLs. If there is a match, the flow is discarded, redirected, or terminated as configured. If there is no match, subscribers view the content as they would normally.
URL Blacklisting—With this solution, all HTTP/WAP URLs in subscriber requests are matched against a database of blacklisted URLs. If there is a match, the flow is discarded, redirected, or terminated as configured. If there is no match, subscribers view the content as they would normally. ![]() Category-based Content Filtering
Category-based Content Filtering ![]() Category-based Static Content Filtering—In this method, all HTTP/WAP URLs in subscriber requests are matched against a static URL categorization database. Action is taken based on a URL's category, and the action configured for that category in the subscriber's content filtering policy. Possible actions include permitting, blocking, redirecting, and inserting content.
Category-based Static Content Filtering—In this method, all HTTP/WAP URLs in subscriber requests are matched against a static URL categorization database. Action is taken based on a URL's category, and the action configured for that category in the subscriber's content filtering policy. Possible actions include permitting, blocking, redirecting, and inserting content. ![]() Category-based Static-and-Dynamic Content Filtering—In this method, each URL first undergoes static rating. If the URL cannot be rated by the static database or if the URL static rating categorizes a URL as either Dynamic or Unknown, the requested content is sent for dynamic rating; wherein the requested content is analyzed and categorized. Action is taken based on the category determined by dynamic rating, and the action configured for that category in the subscriber's content filtering policy. Possible actions include permitting, blocking, redirecting, and inserting content.
Category-based Static-and-Dynamic Content Filtering—In this method, each URL first undergoes static rating. If the URL cannot be rated by the static database or if the URL static rating categorizes a URL as either Dynamic or Unknown, the requested content is sent for dynamic rating; wherein the requested content is analyzed and categorized. Action is taken based on the category determined by dynamic rating, and the action configured for that category in the subscriber's content filtering policy. Possible actions include permitting, blocking, redirecting, and inserting content. 
![]() ACS is applicable only for the `local' context in the logical inventory.
ACS is applicable only for the `local' context in the logical inventory. ![]() Viewing Active Charging Services
Viewing Active Charging Services 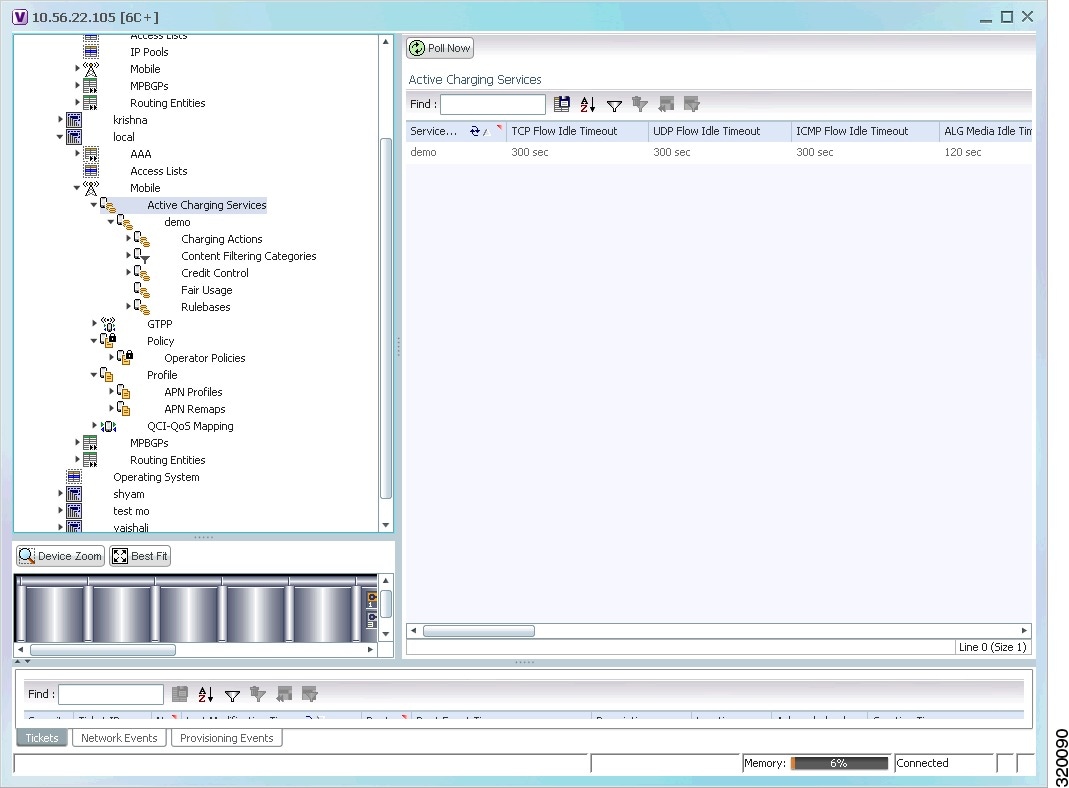
![]() Viewing Content Filtering Categories
Viewing Content Filtering Categories ![]() Viewing Credit Control Properties
Viewing Credit Control Properties ![]() Viewing Charging Action Properties
Viewing Charging Action Properties ![]() Viewing Rule Base for the Charging Action
Viewing Rule Base for the Charging Action ![]() Viewing Fair Usage Properties
Viewing Fair Usage Properties ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services >ACS >Content Filtering Categories.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services >ACS >Content Filtering Categories. ![]() RADIUS Credit Control Application—RADIUS is used as the interface between ECS and the prepaid charging server.
RADIUS Credit Control Application—RADIUS is used as the interface between ECS and the prepaid charging server. ![]() Diameter Credit Control Application—The Diameter Credit Control Application (DCCA) is used to implement real-time credit control for a variety of services, such as networks access, messaging services, and download services.
Diameter Credit Control Application—The Diameter Credit Control Application (DCCA) is used to implement real-time credit control for a variety of services, such as networks access, messaging services, and download services. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services >ACS > Credit Control.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services >ACS > Credit Control. ![]() Server Unreachable Failure Handling
Server Unreachable Failure Handling ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services >ACS > Charging Action.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services >ACS > Charging Action. ![]() Allocation Retention Priority
Allocation Retention Priority ![]() QoS
QoS ![]() Routing—Used to route packets to content analyzers. Routing rule definitions determine which content analyzer to route the packet to when the protocol fields and/or protocol states in the rule definition expression are true. Up to 256 rule definitions can be configured for routing.
Routing—Used to route packets to content analyzers. Routing rule definitions determine which content analyzer to route the packet to when the protocol fields and/or protocol states in the rule definition expression are true. Up to 256 rule definitions can be configured for routing. ![]() Charging—Used to specify what action to take based on the analysis done by the content analyzers. Actions can include redirection, charge value, and billing record emission. Up to 2048 charging rule definitions can be configured in the system.
Charging—Used to specify what action to take based on the analysis done by the content analyzers. Actions can include redirection, charge value, and billing record emission. Up to 2048 charging rule definitions can be configured in the system. ![]() Post-processing—Used for post-processing purposes. Enables processing of packets even if the rule matching for them has been disabled.
Post-processing—Used for post-processing purposes. Enables processing of packets even if the rule matching for them has been disabled. ![]() TPO—Used for Traffic Performance Optimization (TPO) in-line service match-rule and match advertisement features.
TPO—Used for Traffic Performance Optimization (TPO) in-line service match-rule and match advertisement features. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Rule Definitions.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Rule Definitions. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Group of Rule Definitions.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Group of Rule Definitions. 
![]() You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Rulebase Container.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Rulebase Container. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Bandwidth Policy Container.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Bandwidth Policy Container. ![]() Right-click the required device in Prime Network Vision and choose Inventory.
Right-click the required device in Prime Network Vision and choose Inventory. ![]() In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Fair Usage.
In the logical inventory window, choose Logical Inventory > local > Mobile > Active Charging Services > ACS > Fair Usage. 
![]() You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time. 
![]() In the GUI, parameters that are displayed in bold text are mandatory.
In the GUI, parameters that are displayed in bold text are mandatory. 
![]() You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.
You might be prompted to enter your device access credentials while executing a command. Once you have entered them, these credentials will be used for every subsequent execution of a command in the same GUI client session. If you want to change the credentials, click Edit Credentials. The Edit Credentials button will not be available for SNMP commands or if the command is scheduled for a later time.  Feedback
Feedback