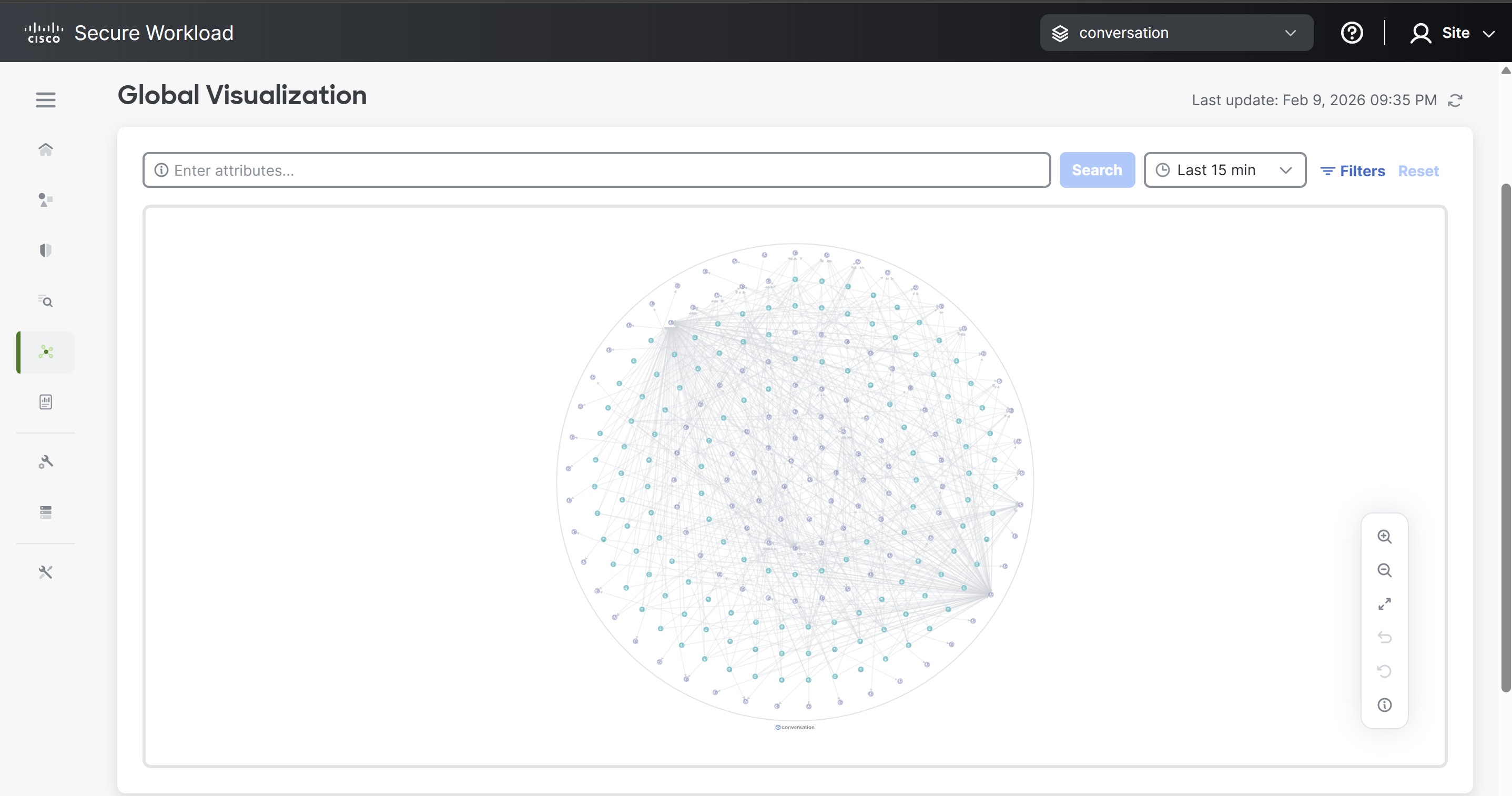
Introduction to Global Visualization
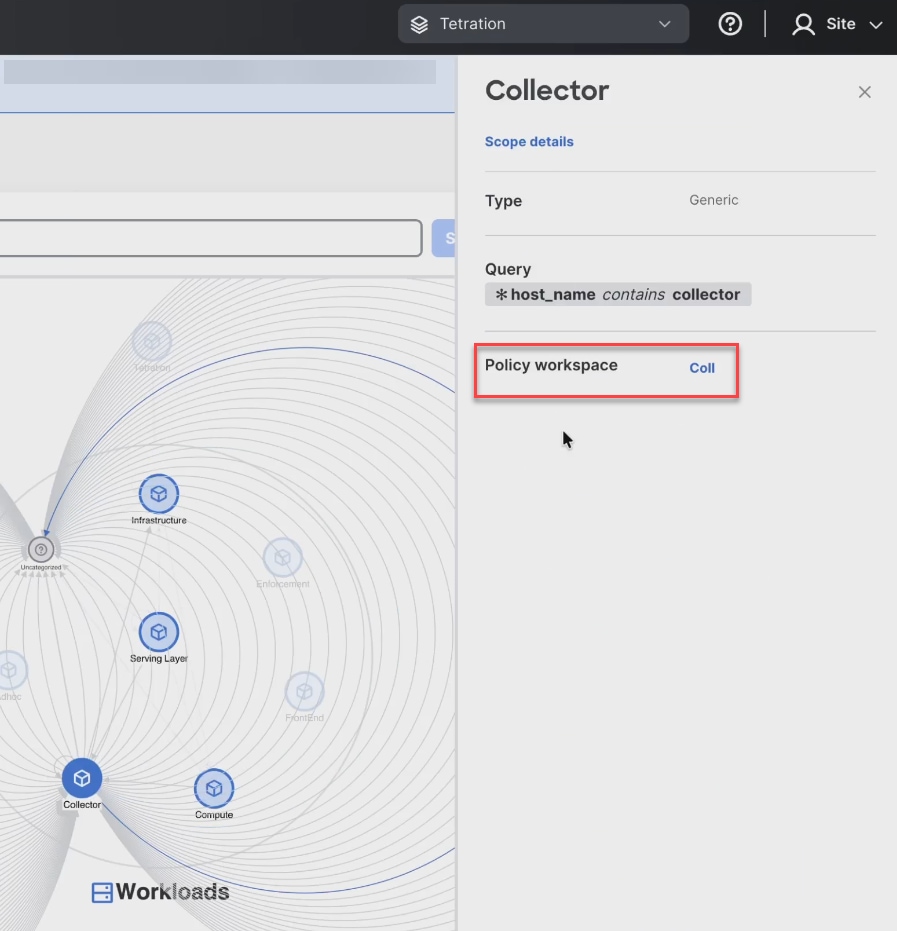
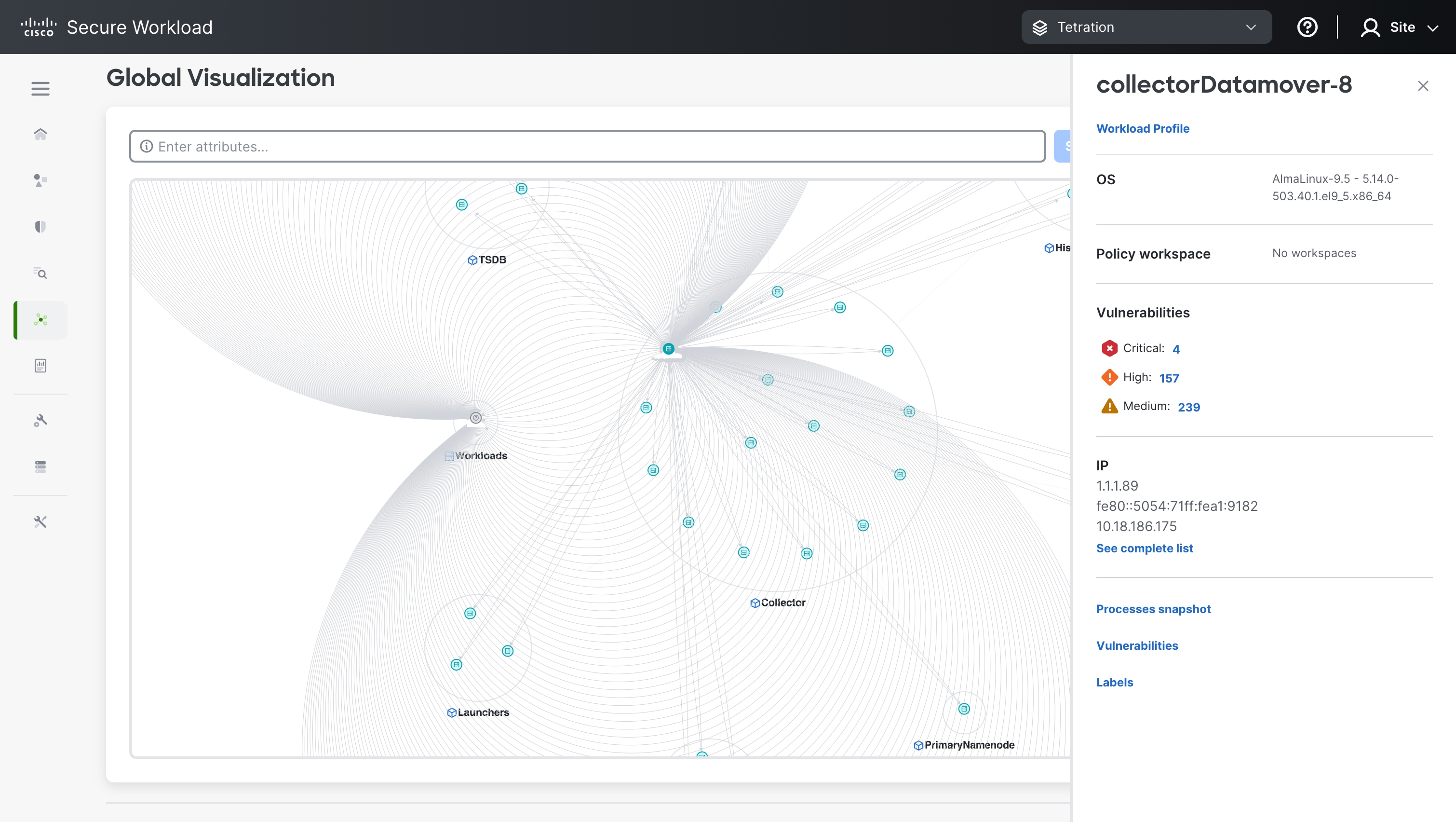
Cisco Secure Workload's microsegmentation solution includes Global Visualization, a tool that helps organisations to gain near real-time network visibility, segmentation of the network, discover vulnerabilities, and improve their security posture.
Key features
-
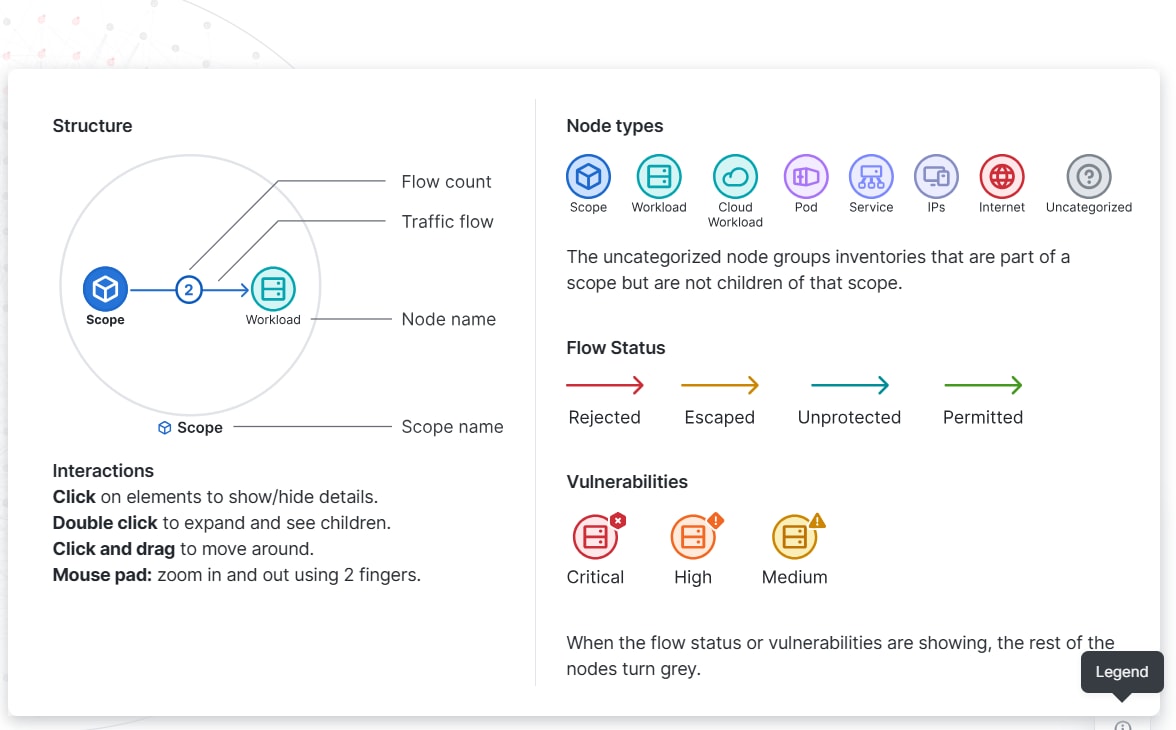
Represents a vast amount of data in a compact space and avoids node-edge overlap.
-
Node sizes expand or contract for scopes that have more inventory, more concentrated connections, or critical nodes that have large amount of inventory.
-
Highlights traffic flows and makes it simple to identify patterns or anomalies at a glance.
-
Visualization access is now managed through Role-Based Access Control (RBAC), ensuring that users can only view data and dashboards aligned with their assigned roles and permissions.
-
Users with respective access can view the scope tree.
For a visual presentation of real-time network visibility, see this video: Global Visualization for Near Real-time Traffic Flow Analysis



 Feedback
Feedback