Routing policy enforcement
Routing policy enforcement is a feature that
-
requires configuring inbound and outbound policies for external BGP (eBGP) neighbors
-
prevents accidental route acceptance or advertisement, and
-
provides an added security measure against configuration omission errors.
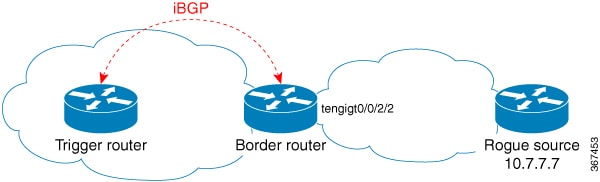
Routing policy enforcement behavior
If you do not configure a policy, BGP does not accept any routes from the neighbor, nor does it advertise any routes to it. This enforcement affects only eBGP neighbors, which are neighbors in a different autonomous system than this router. For internal BGP (iBGP) neighbors, which are neighbors in the same autonomous system, BGP accepts or advertises all routes if there is no policy.
Configure routing policy enforcement
Configure BGP routing filtering by applying a route policy.
This task outlines the steps to create and apply a route policy to filter BGP routes, ensuring that only desired routes are accepted or advertised.
Procedure
|
Step 1 |
Create a route policy and define its filtering logic. Example: |
|
Step 2 |
Configures a neighbor IP address as a BGP peer and apply the route policy to inbound or outbound routes for the neighbor. Example: |
BGP routes are filtered according to the defined route policy.

 Feedback
Feedback