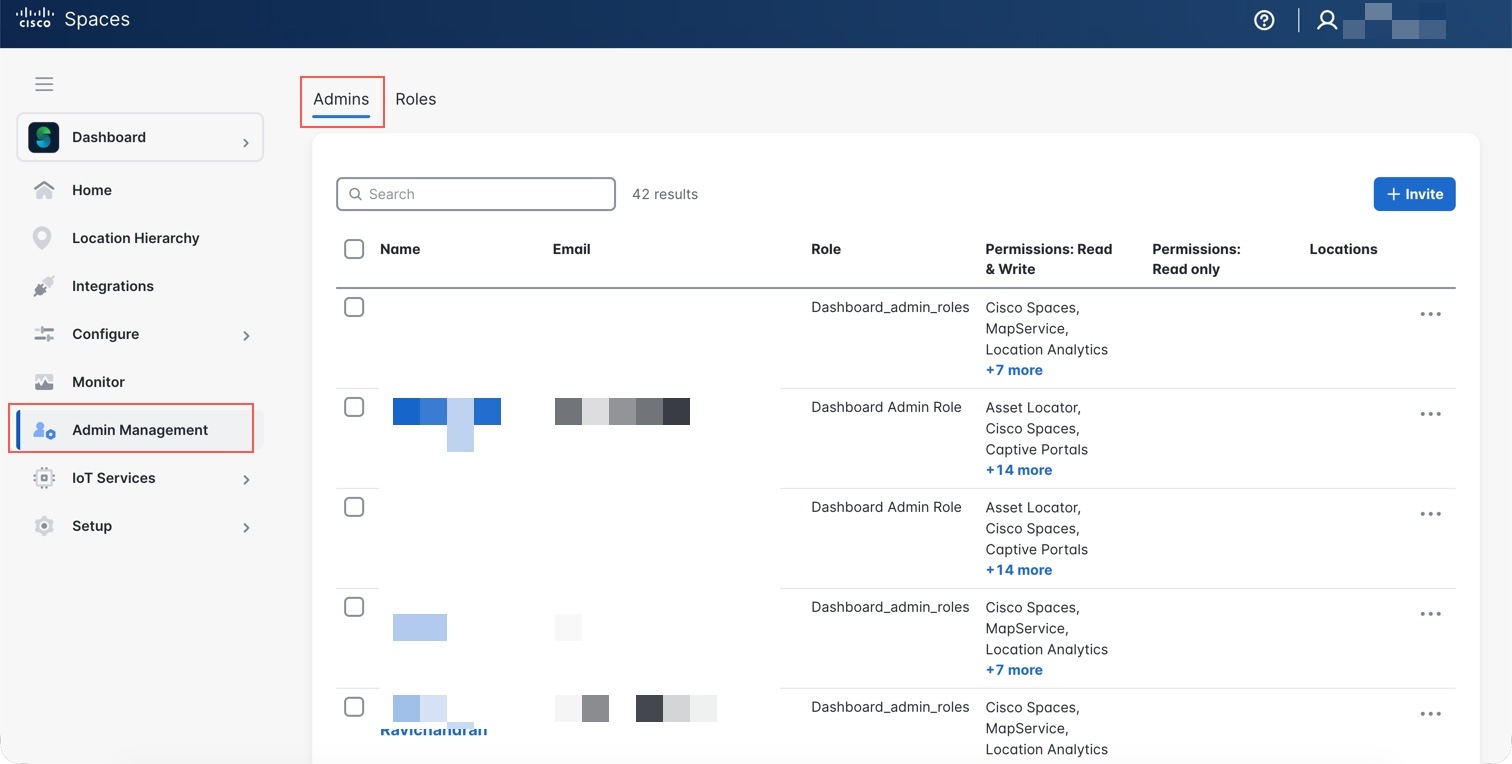
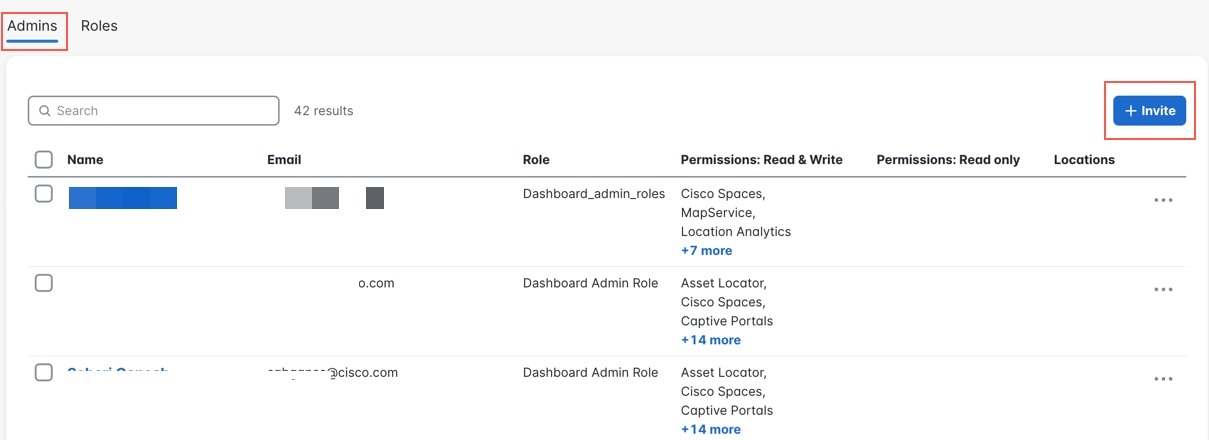
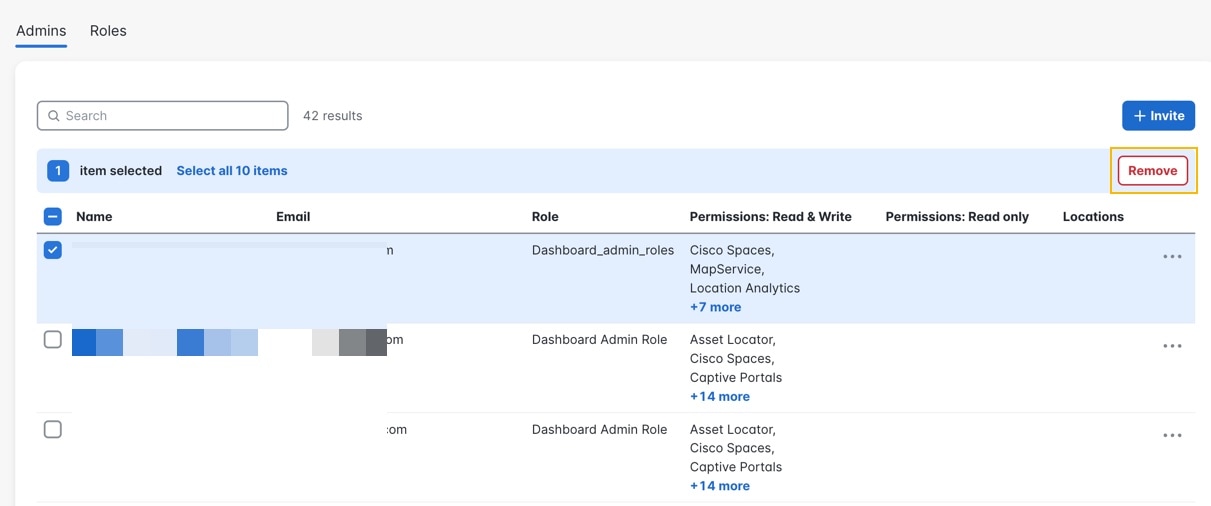
Manage Dashboard Administrators and Permissions
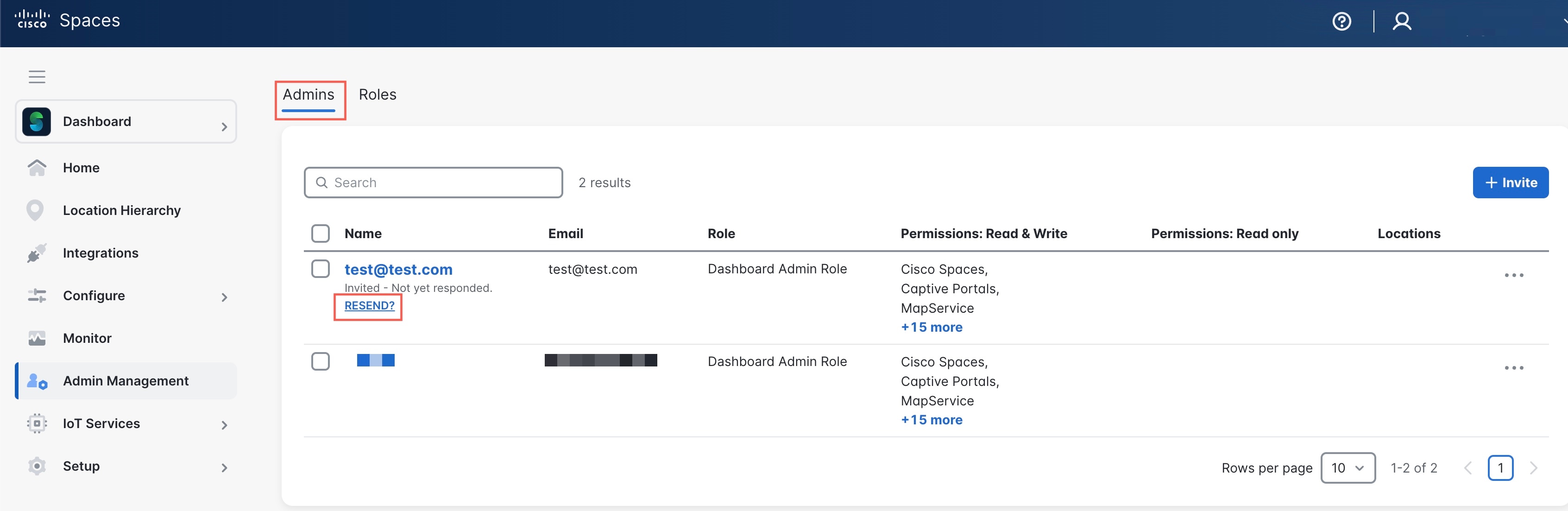
This chapter explains the different permission levels within the dashboard and how to manage administrative users. Administrative users can log in to the dashboard to view and/or administer apps, locations, devices, and role-based access within the account.
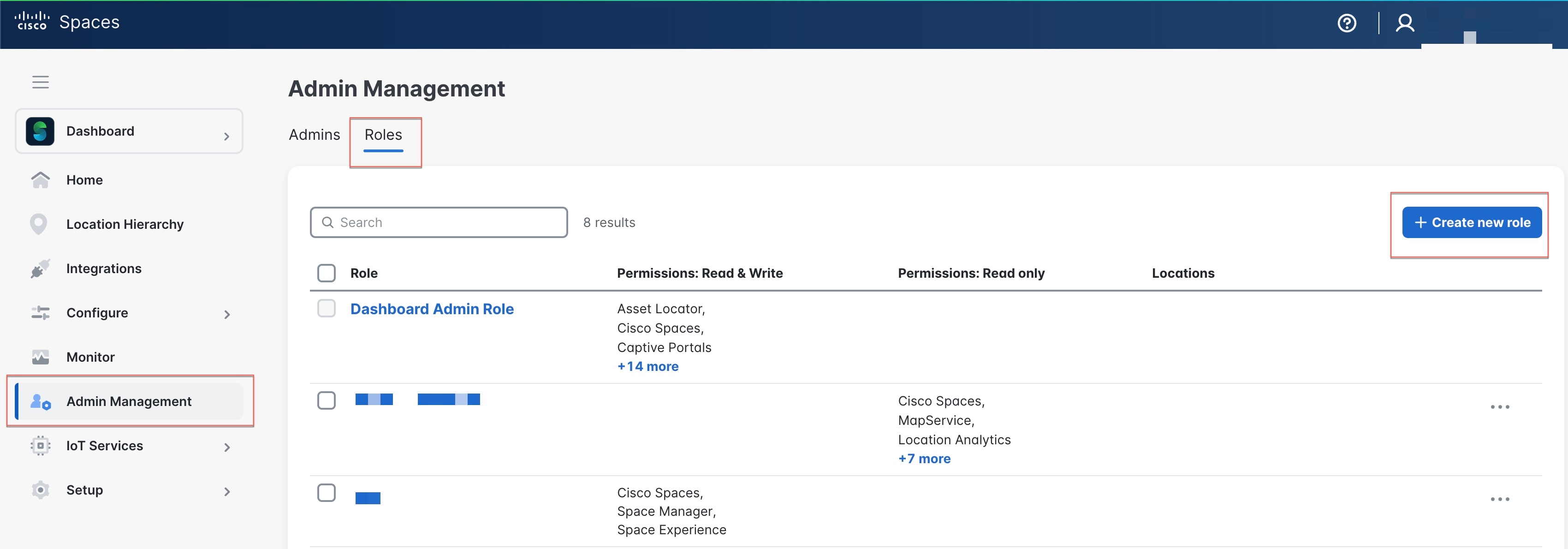
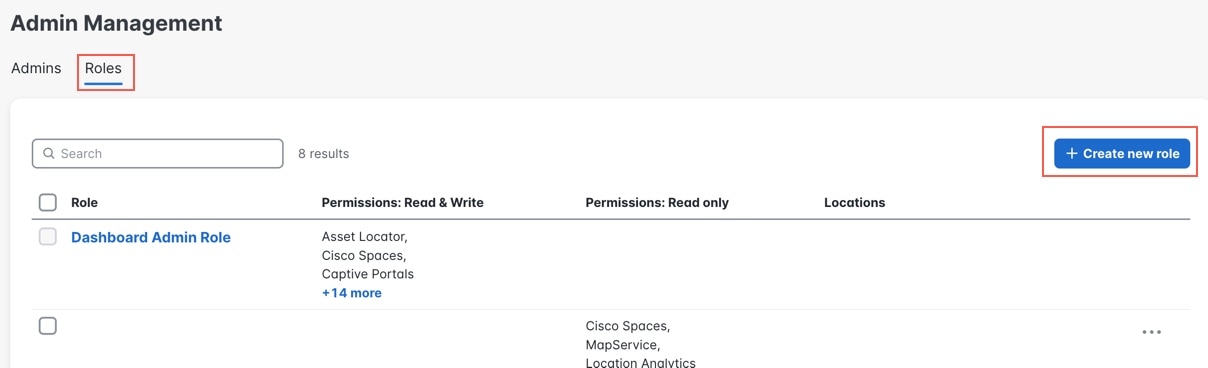
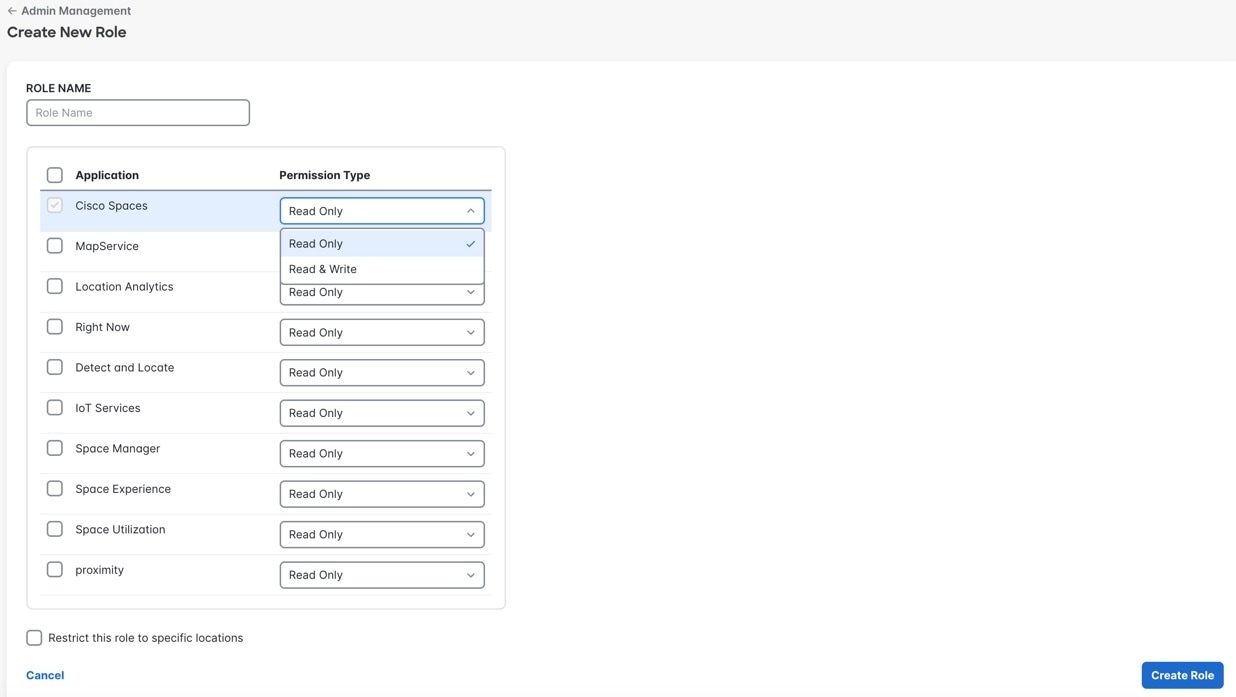
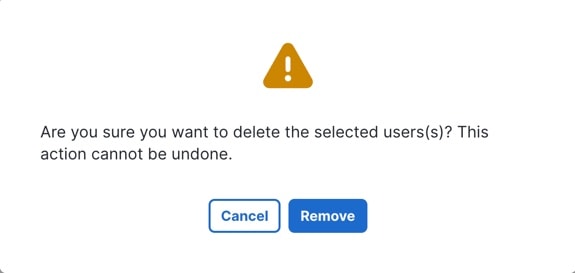
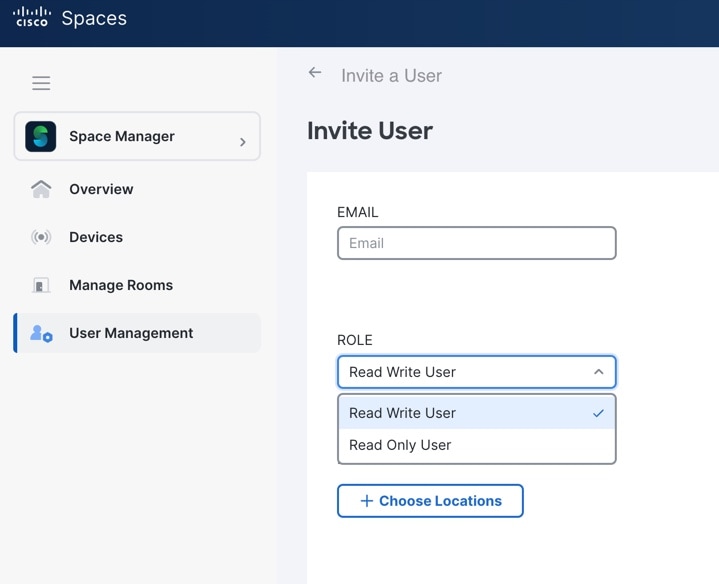
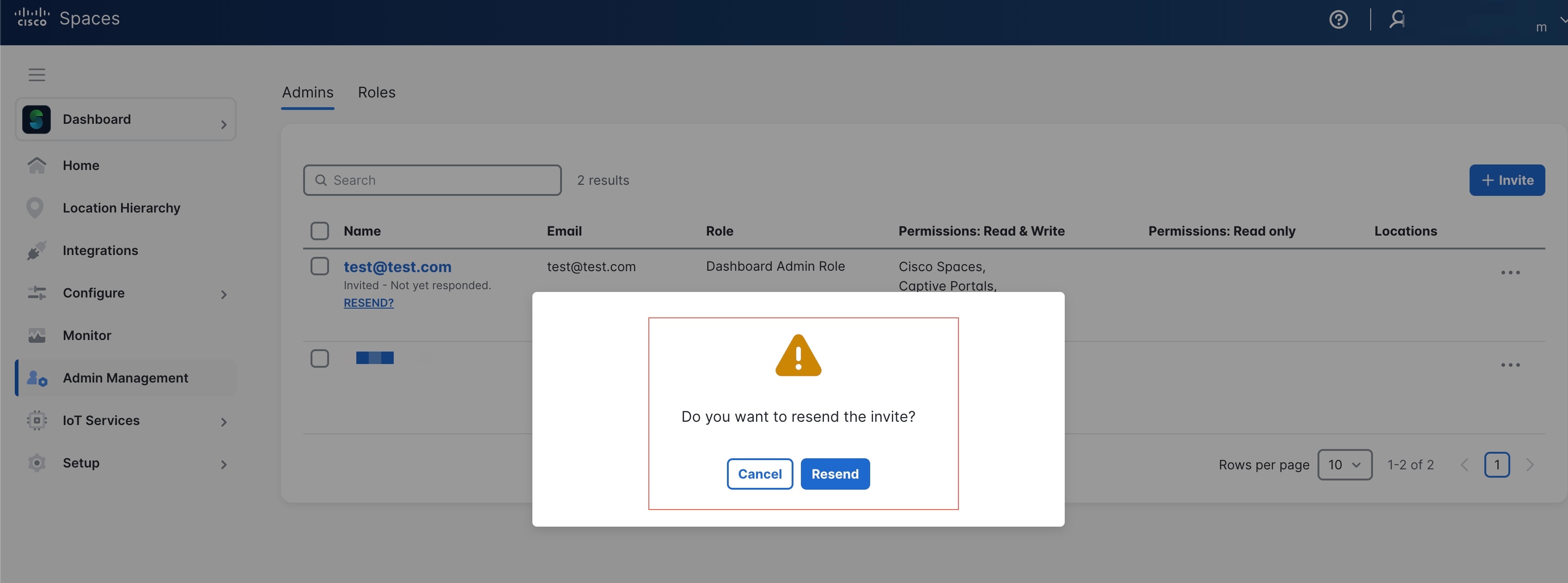
Admin Management
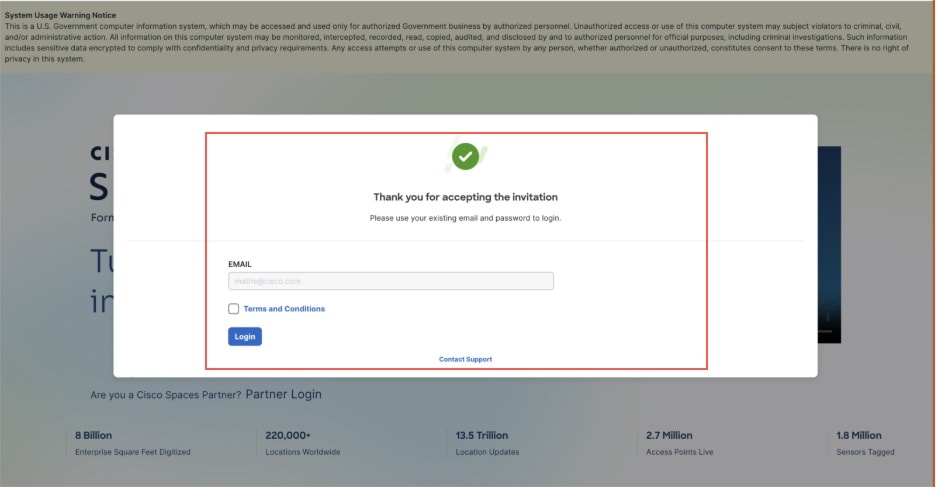
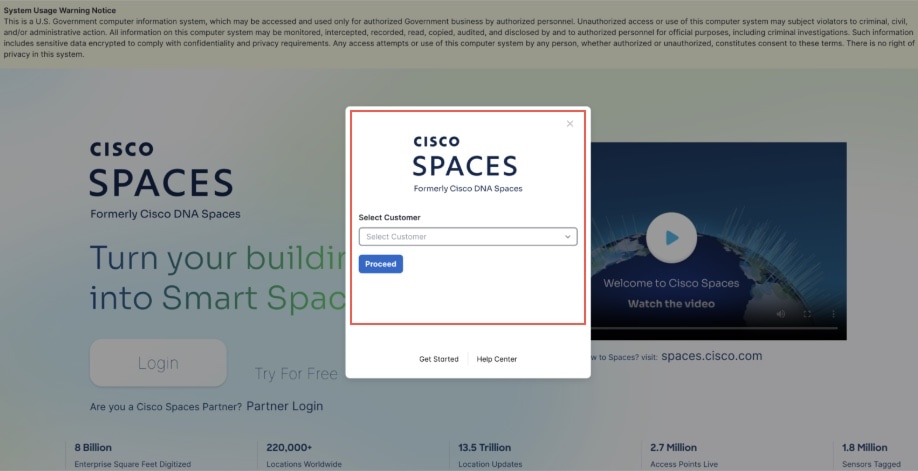
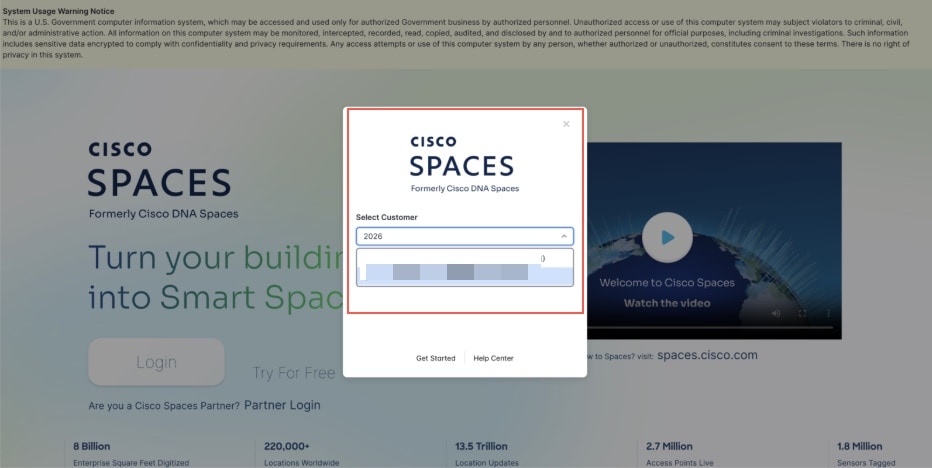
When you onboard to Cisco Spaces as a new user, the Cisco Spaces Support team will assist you in setting up your account details and fulfilling the initial-onboarding requirements. The Cisco Spaces Support team is responsible for creating the new account, generating the tenant ID, assigning the account number, and provisioning the appropriate license type.
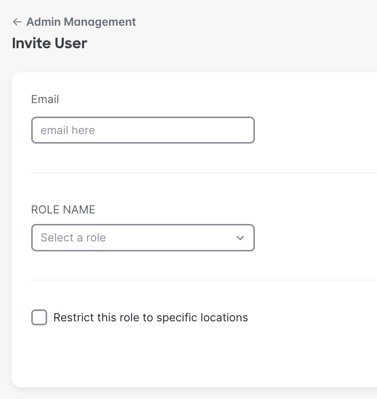
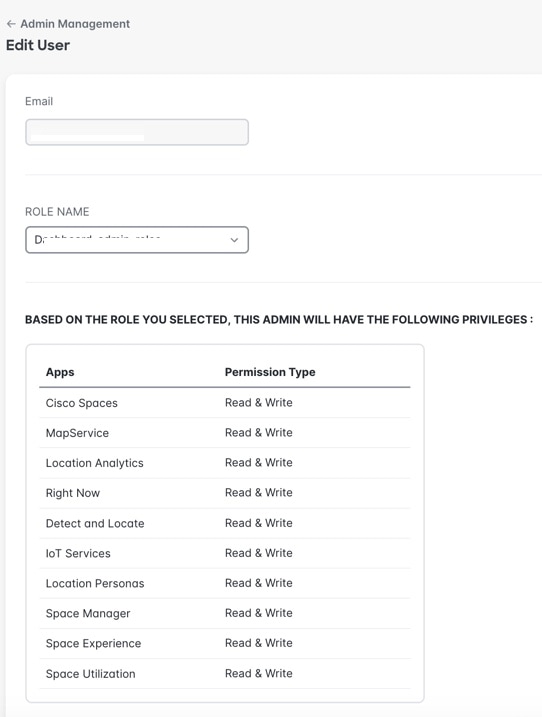
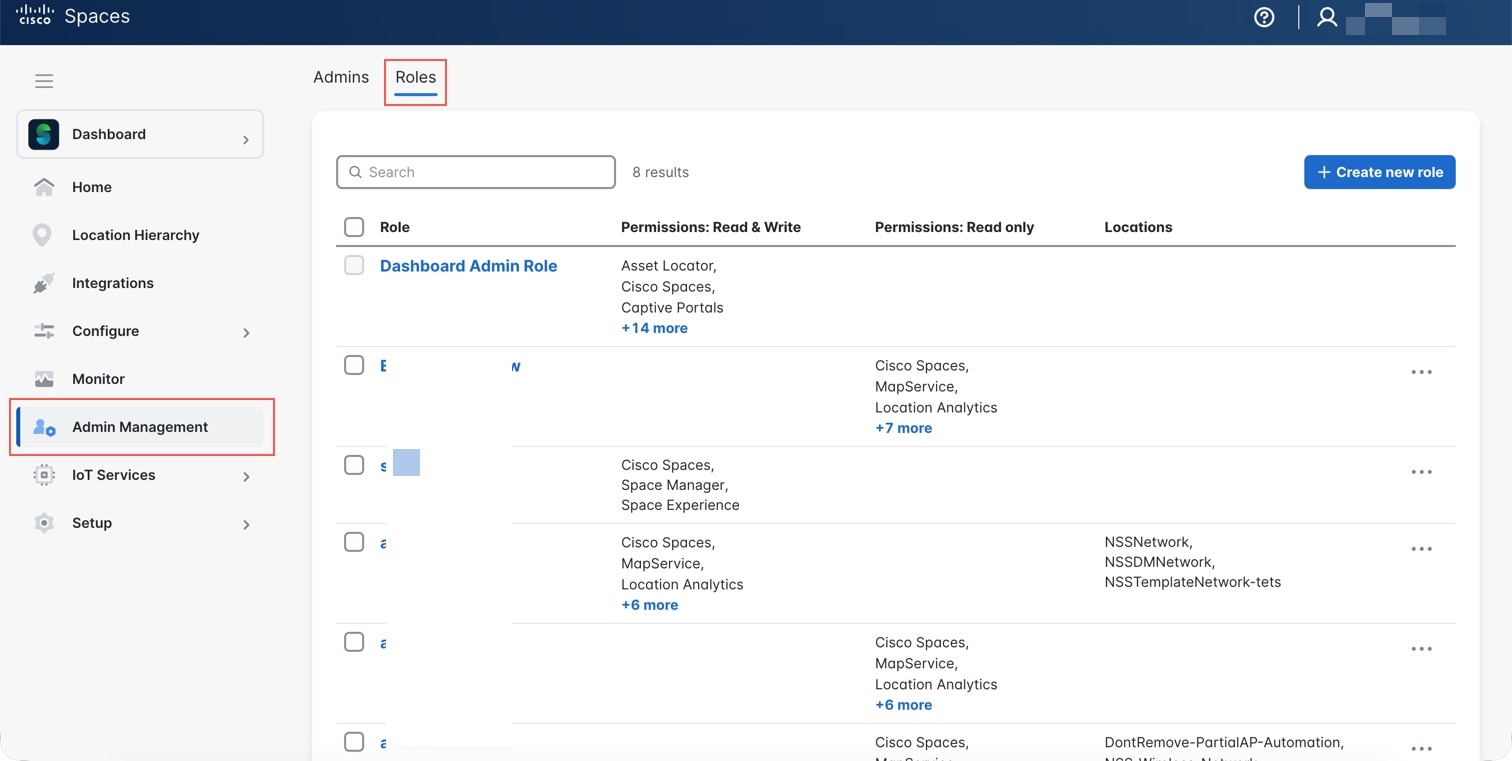
When a new account is created, a Default Admin Role (Dashboard Admin Role) is automatically provisioned.
This role is assigned to the user email configured during account creation. The Default Admin Role is the top-level admin role for user and role management.


 Feedback
Feedback