Wired guest access
Wired guest access is a network feature that
-
enables guest users of an enterprise network that supports both wired and wireless access to connect to the guest access network
-
allows wired guest clients to connect from designated and configured wired Ethernet ports for guest access after they complete the configured authentication methods, and
-
directs wired session guests to a wireless guest controller in a demilitarized zone (DMZ) through a Control And Provisioning of Wireless Access Points (CAPWAP) tunnel.
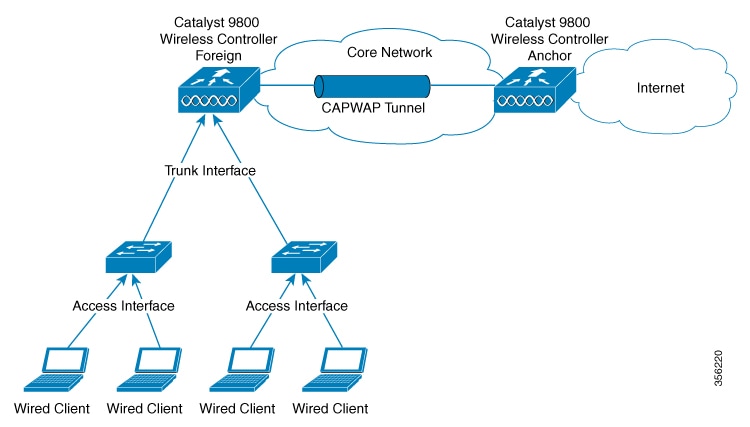
Wired guest access configuration and architecture
Wired guest access can be configured in a dual-controller configuration that uses both an anchor controller and a foreign controller. A dual-controller configuration isolates wired guest access traffic from the enterprise user traffic.
The wired session guests are provided open or web-authenticated access from the wireless controller.
IPv6 Router Advertisement forwarding for wired guests
-
Guest Anchor Controller: Guest anchor controller forwards the RA packets, from the receiving VLAN, to all the foreign controllers using the mobility data tunnel. The RA packets are tagged with the anchor VLAN to ensure the message is forwarded to the correct clients using the foreign controller data path.
-
Guest Foreign Controller: Guest foreign controller forwards the received RAs from the guest anchor to the wired ports on which the wired guest clients are connected. To forward the RAs to the intended clients, the guest foreign controller keeps a track of the wired guest clients–per interface, access VLANs, and anchor VLANs.
Wired clients get the IPv6 based connectivity when they receive the IPv6 Router Advertisement (RA) message. The IPv6 router sends these RA messages and it contains information such as IPv6 prefix and router link-local address.
These RA messages are sent as Unicast or Multicast messages. The Unicast RA messages are routed as same as the client directed traffic. The Multicast RA messages are forwarded to all the clients present in the intended VLAN. RA message forwarding is enabled by default and requires no specific configuration.
Supported features
Supported features include:
-
Cisco Catalyst 9800 Series Wireless Controllers-Anchor
-
Cisco AireOS Wireless Controllers-Anchor
-
Cisco Catalyst 9800 Series Wireless Controllers-Foreign
-
Cisco AireOS Wireless Controllers-Foreign
-
Dual controller solution (foreign + anchor) and access switch
-
Trunk Ports
-
Open Authentication
-
Local Web Authentication
-
Scale max 2k clients and 5 guest-LANs (5 VLANs max)
-
Client IPv6 support
-
Idle Timeout and Session Timeout
-
Accounting on Foreign
-
Manageability (SNMP/Yang/WebUI)
-
QoS Rate-Limiting and MQC Policies (Upstream at foreign, Upstream, and Downstream at the anchor)
-
QoS support with AireOS Anchor setup
-
Stateful Switch Over (SSO)
-
Port Channel support on Anchor and Foreign with no restrictions to the controller's role.
-
Access Port on Foreign
-
Cisco Umbrella (not supported in AireOS Anchor)
-
ACL support at anchor
-
Fully Qualified Domain Name (FQDN) URL filtering is supported at Anchor controller.
-
IP theft detection
-
Sleeping Client
Local web authentication options:
-
Local Web Authentication (web consent)

Note
In AireOS, this is referred to as web pass-through.
-
Local Web Authentication + ISE (External Web Authentication).
-
LWA (local web authentication), with a username and a password.
-
Web consent (LWA + consent), that is with a username, a password and the check box of acceptance.
To configure Web Authentication, see Web-based Authentication section of the Cisco Catalyst 9800 Series Wireless Controller Software Configuration Guide.
 Note |
Statistics computation not supported. |
 Note |
QoS rate-limiting supports bps rate-limiting, pps rate-limiting is not supported. |
 Feedback
Feedback