Mobility
Mobility, or roaming, is the ability of a wireless LAN client to maintain a seamless and secure connection while moving from one access point to another with minimal latency.
-
enables uninterrupted connectivity as clients move between access points,
-
relies on controllers to manage client information, including MAC and IP addresses, security context, quality of service (QoS), wireless LAN (WLAN), and associated access point, and
-
ensures secure and efficient data forwarding and traffic management for wireless clients.
Definitions of mobility-related terms
Key mobility terms in wireless LANs include point of attachment, point of presence, and station.
-
Point of Attachment: the location in the network where a station data path is first processed when it enters the network.
-
Point of Presence: the point in the network where a station is advertised.
-
Station: a device that connects to and requests service from a network.
Intracontroller roaming
A intracontroller roaming is a wireless network mobility process that
-
enables a wireless client to move its association from one access point to another within the same controller
-
allows the controller to update the client database with the new access point association, and
-
maintains or reestablishes the security context and client associations to support uninterrupted connectivity.
Additional information
When a client roams between access points managed by the same controller, the controller simply updates the client database to reflect the client’s new association. If required, the controller creates new security contexts and reestablishes associations to maintain connectivity.
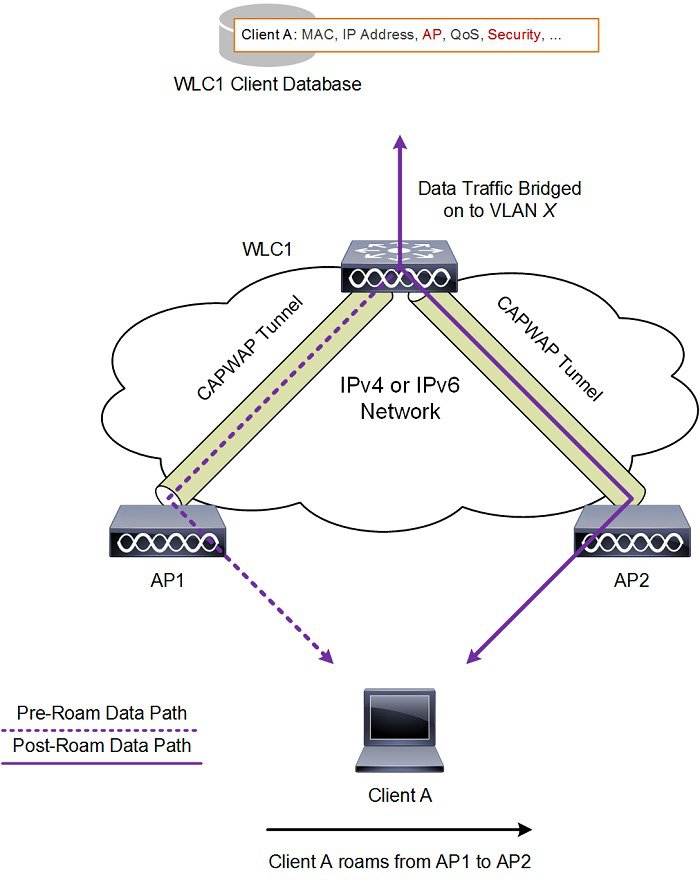
Intracontroller roaming example
A user walking through a building with multiple access points connected to one wireless LAN controller experiences no interruption in service because intracontroller roaming automatically updates the client’s association information as the device connects to new access points.
Intercontroller roaming
An intercontroller roaming event is a wireless mobility process that provides the following functions:
-
occurs when a client moves from an access point managed by one controller to an access point managed by another controller
-
exchanges mobility messages between the new and original controllers to update the client database entry, and
-
maintains the user network experience, making the handover transparent to the user.
-
Mobility messages: specialized communications between controllers that coordinate the handover and update the client database during a roaming event.
-
Client database entry: the information each controller stores about a connected client, such as security context, session details, and access point association.
Expanded explanation
When a client device joins an access point managed by a new controller, the new controller exchanges mobility messages with the previous controller.
These messages transfer the client session information and database entry from the original controller to the new controller. The system establishes new security contexts and associations as needed.
The system updates the client database entry to reflect the new access point and controller location. This process occurs in the background and appears seamless to the user.
 Note |
Clients configured with 802.1X or Wi-Fi Protected Access (WPA) security complete full authentication to comply with IEEE standards. |
 Important |
Intersubnet roaming is not supported for Software-Defined Access (SDA). |
Intercontroller roaming examples
A user with a mobile device walks from one building to another on a campus network. The device switches from an access point managed by Controller A to one managed by Controller B. The client remains connected and active while the controllers complete the roaming event.
The figure shows intercontroller roaming, which occurs when wireless LAN interfaces on controllers are on the same IP subnet.

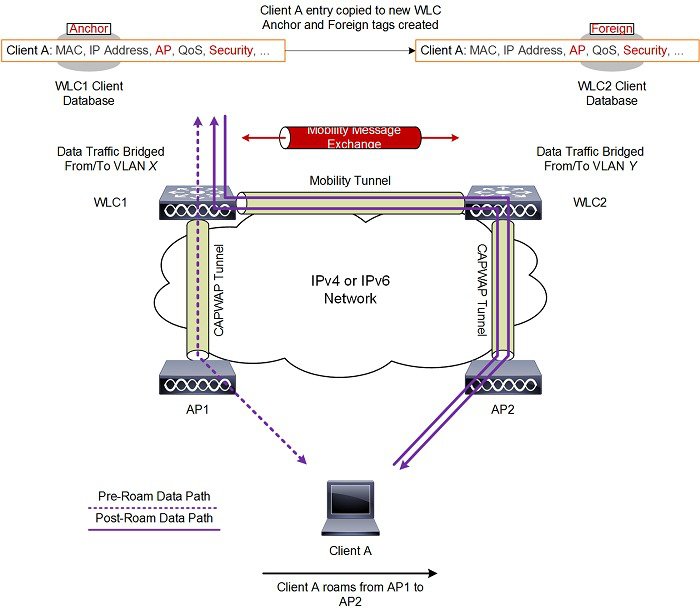
Intersubnet roaming
An intersubnet roaming event is a wireless network mobility process that provides the following functions:
-
allows wireless clients to move seamlessly between controllers on different IP subnets
-
keeps the original client IP address after roaming
-
uses anchor and foreign controller roles to maintain and track the client session across controllers
-
Anchor controller: the original controller where the client is first authenticated and where session anchoring remains, maintaining the primary client database entry.
-
Foreign controller: the new controller to which the client connects after roaming, which receives a copy of the client database entry marked as a foreign entry.
Expanded explanation
Intersubnet roaming is similar to intercontroller roaming because controllers exchange mobility messages when a client roams. Instead of transferring the client database entry to the new controller, the original controller marks the client with an anchor entry in its client database.
The system then copies the database entry to the new controller and marks it as a foreign entry. This process keeps the roam transparent to the wireless client and preserves the original IP address.
WLANs on both the anchor and foreign controllers must provide the same network access privileges.
Ensure that source-based routing and source-based firewalls are not configured. If they are present, clients may experience network connectivity issues after the handoff.
Additional reference information
In static anchor setups that use controllers and a RADIUS server, the following applies:
-
If AAA override dynamically assigns VLAN and QoS, the foreign controller updates the anchor controller with the correct VLAN after Layer 2 authentication (802.1X).
-
For Layer 3 RADIUS authentication, the anchor controller sends authentication requests.
 Note |
The Cisco Catalyst 9800 Series Wireless Controller mobility tunnel is a CAPWAP tunnel with a control path (UDP 16666) and a data path (UDP 16667). The control path uses DTLS encryption by default. You can enable DTLS on the data path when you add the mobility peer. The supported DTLS version is 1.2. |
Intersubnet roaming example
This figure shows intersubnet roaming, which occurs when wireless LAN interfaces on controllers are located on different IP subnets.
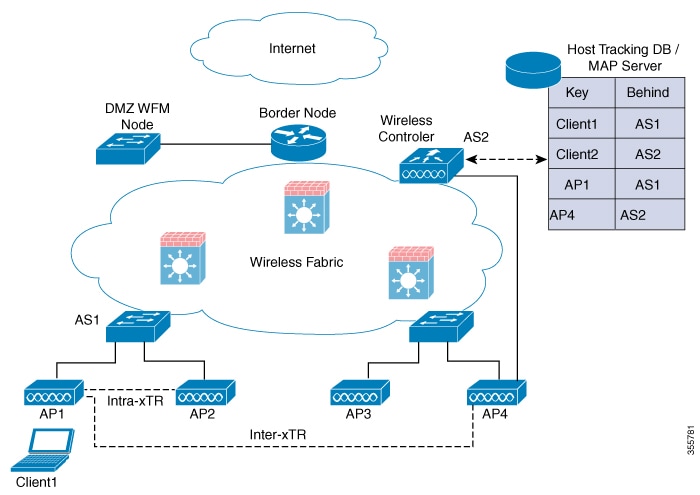
SDA roaming
SDA roaming types keep wireless clients connected as they move across access points in a software-defined access (SDA) network. SDA roaming:
-
keeps wireless clients connected within the fabric as they move across access points
-
supports both intra-xTR events—within the same access switch—and inter-xTR events—across different access switches
-
updates key system tables—local client database, client history table, and map server where applicable—for accurate client location tracking and ongoing connectivity
-
SDA (software-defined access): An architecture that uses centralized control to automate and secure network operations across wired and wireless endpoints.
-
xTR (tunnel router): In SDA, an xTR is an access switch that acts as both an ingress tunnel router and an egress tunnel router. It serves as a fabric edge node responsible for client mobility and traffic tunneling.
Expanded explanation
This section describes the two principal types of SDA roaming events:
-
Intra-xTR roaming happens when your client moves between access points attached to the same access switch (xTR) in an SDA fabric-enabled WLAN. The system updates the local client database and client history table with the new access point information.
-
Inter-xTR roaming happens when your client moves to an access point attached to another access switch (xTR) within the fabric. The system updates the local client database and the map server with the new location (RLOC) to show which switch the client is now using.
 Note |
|
SDA roaming example
When a wireless client roams from Access Point A to Access Point B, both connected to the same access switch, the client experiences an intra-xTR roaming event. Only local tables are updated.
When the client moves from Access Point A to Access Point C on another access switch, the system initiates an inter-xTR roaming event. It updates both the local client database and the central map server with the new location.
The figure shows intra-xTR and inter-xTR roaming. This occurs when the client moves between access points on the same switch or on different switches in a fabric topology.
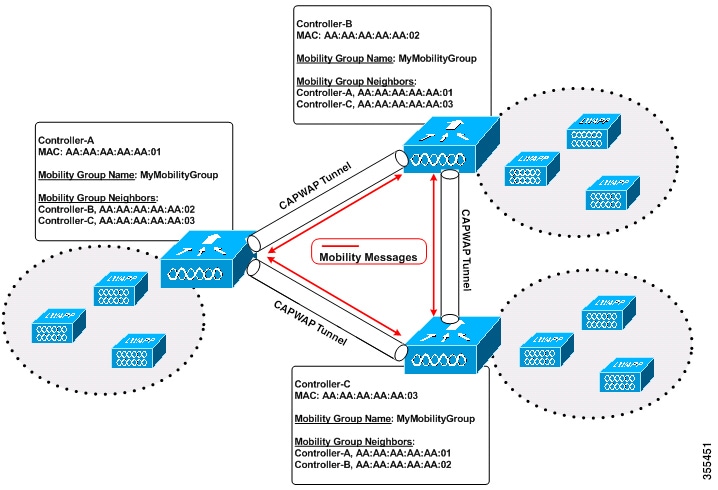
Mobility groups
A mobility group is a wireless controller configuration that
-
defines a set of controllers identified by the same mobility group name
-
enables seamless roaming and state and context sharing for wireless clients, and
-
allows controllers to dynamically forward data traffic and share the list of access points.
By creating a mobility group, multiple controllers in a network dynamically share information and forward data traffic when inter-controller or inter-subnet roaming occurs.
Controllers in the same mobility group share the context and state of client devices and their list of access points. This prevents controllers from identifying access points from other controllers as rogue devices. With this shared information, the network supports inter-controller wireless LAN roaming and controller redundancy.
When an access point (AP) moves from one controller to another, and both controllers are mobility peers, a client associated with controller 1 before the move might remain anchored to controller 1 after the move.
Controller 1 maintains the client entry for a timeout period to support roaming and reassociation scenarios. To prevent a client from remaining anchored to controller 1 after such a move, remove the mobility peer configuration from that controller.
Example of a single mobility group
The figure shows that each controller is configured with a list of the other mobility group members.
Whenever a new client joins a controller, the controller sends a unicast message, or a multicast message if mobility multicast is configured, to all controllers in the mobility group. The controller that previously managed the client passes the client status to the new controller.
 Feedback
Feedback