Feature history for route leaking between VPNs
This table describes the developments of this feature, by release.
|
Feature Name |
Release Information |
Description |
|---|---|---|
|
Route leaking between global VRF and service VPNs |
Cisco IOS XE Catalyst SD-WAN Release 17.3.1a Cisco vManage Release 20.3.1 |
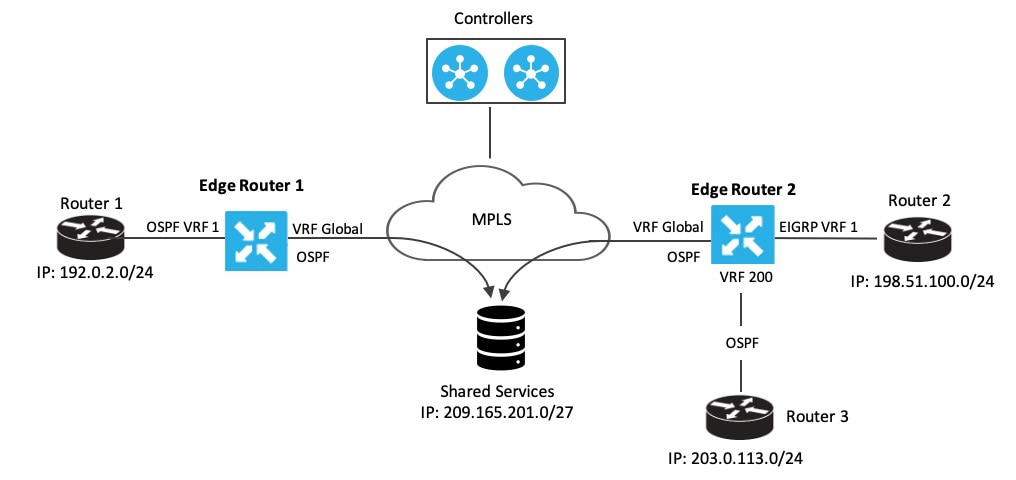
Route leaking enables you to leak routes bidirectionally between the global VRF and service VPNs. The feature allows service sharing and is beneficial in migration use cases because it allows bypassing hubs and provides migrated branches direct access to non-migrated branches. |
|
Redistribution of replicated BGP routes to OSPF, EIGRP protocols |
Cisco IOS XE Catalyst SD-WAN Release 17.5.1a Cisco vManage Release 20.5.1 |
This feature allows you to leak or replicate BGP routes between the global VRF and service VPNs, then redistribute the leaked BGP routes. The redistribution of the leaked routes to the EIGRP and OSPF protocols occurs after replicating the BGP routes into the corresponding VRF. |
|
Redistribution of replicated routes to BGP, OSPF, and EIGRP Protocols |
Cisco IOS XE Catalyst SD-WAN Release 17.6.1a Cisco vManage Release 20.6.1 |
This feature allows you to configure:
|
|
Route leaking between inter-service VPNs |
Cisco IOS XE Catalyst SD-WAN Release 17.9.1a Cisco vManage Release 20.9.1 |
With this feature, you can leak routes between the service VPNs at the same edge device. Route leaking feature allows redistribution of replicated routes between the inter-service VPN for Connected, Static, BGP, OSPF, and EIGRP on Cisco IOS XE Catalyst SD-WANs. |

 Feedback
Feedback