Feature history for BFD protocol
| Feature name | Release information | Description |
|---|---|---|
| BFD Troubleshooting for Cisco Catalyst SD-WAN | Cisco IOS XE Catalyst SD-WAN Release 17.15.1aCisco Catalyst SD-WAN Manager Release 20.15.1 | This feature enables you to troubleshoot BFD protocols using radioactive tracing, check device logs, and use debugging commands to gather detailed information about BFD operations. |
| Automatically Suspend Unstable Cisco Catalyst SD-WAN BFD Sessions | Cisco IOS XE Catalyst SD-WAN Release 17.10.1aCisco vManage Release 20.10.1 | With this feature you can automatically suspend unstable Cisco Catalyst SD-WAN BFD sessions based on flap-cycle thresholds or SLA parameters. It also allows you to monitor all suspended BFD sessions and manually reset them when needed. |
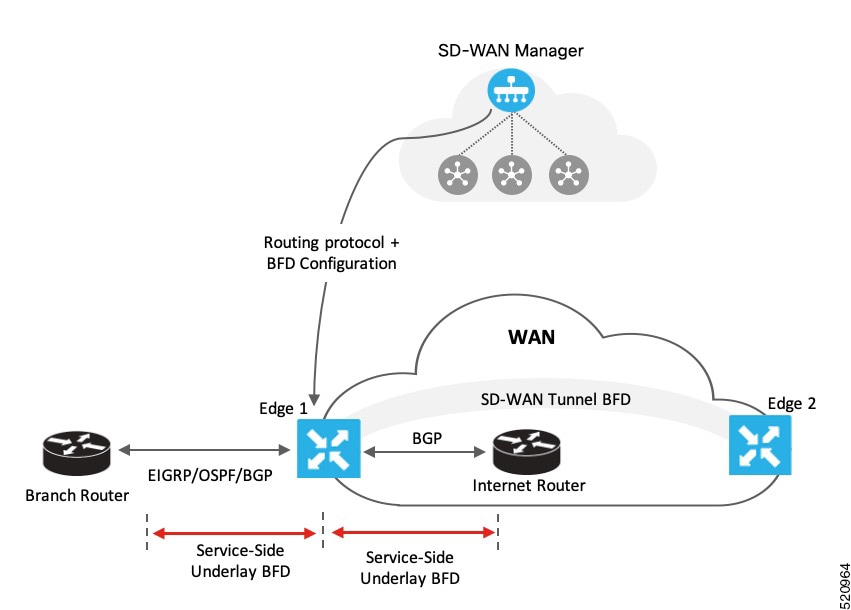
| BFD for Routing Protocols in Cisco Catalyst SD-WAN |
Cisco IOS XE Catalyst SD-WAN Release 17.3.1a Cisco vManage Release 20.3.1 |
This feature extends BFD support to BGP, OSPF, and EIGRP in the Cisco Catalyst SD-WAN solution, allowing BFD to provide a consistent, uniform failure-detection method that quickly identifies forwarding-path failures and enables faster reconvergence. |
 Feedback
Feedback