|
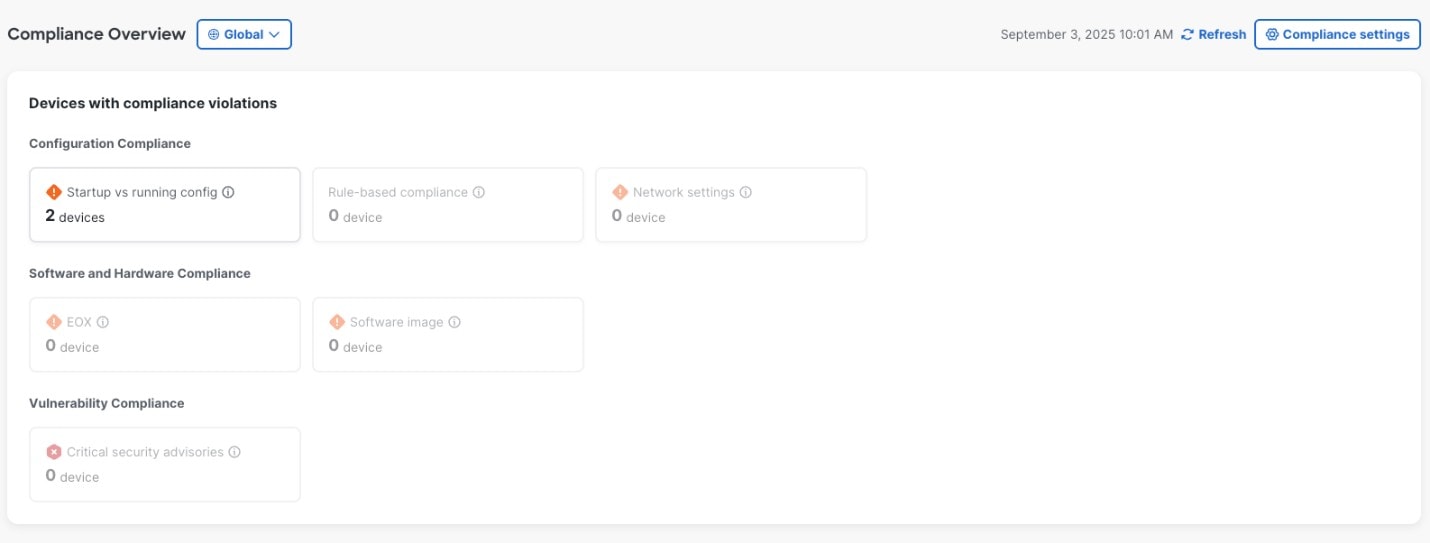
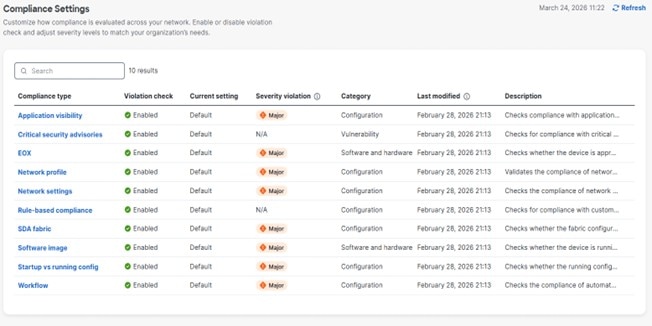
Configuration compliance
|
|
Network Profile
|
Catalyst Center allows you to define its intent configuration using network profiles and push the intent to the device. If any violations
are found at any time due to changes in-band, out-of-band or triggered by another catalyst center service, this check identifies, assesses, and flags it off. The violations are shown
to the user under Network Profiles in the compliance summary window.
|
Note
|
Network profile compliance is applicable for routers, switches, and wireless controllers.
|
|
-
Non-compliant: The device is not running the intent configuration of the profile.
-
Compliant: While applying a network profile to the device, the device configurations that are pushed through Catalyst Center are actively running on the device.
-
Error: The compliance could not compute the status because of an underlying error. For details, see the error log.
|
|
Network Settings
|
Catalyst Center allows you to define its intent configuration settings using network settings and to push the intent to the device. If any
violations are found at any time due to out-of-band or any other changes, the compliance check identifies, assesses, and flags
it off.
You can view the violations under Policy in the Configuration Compliance window.
|
Note
|
Post UI upgrade, compliance for network settings will get triggered after 6 hours.
|
|
-
Non-compliant: The device is not running the intent configuration.
-
Compliant: The intent configuration that was pushed is actively running on the device.
-
NA (Not Applicable): The device is not configured with network settings, or the device is not assigned to the site.
|
|
Rule-based compliance
|
Catalyst Center allows you to define custom compliance rules using CLI regular expressions. This provides flexibility to check for specific
configuration patterns or values unique to your environment.
|
-
Non-compliant: The device is not running the intent configuration.
-
Compliant: The intent configuration that was pushed is actively running on the device.
-
NA (Not Applicable): The device is not configured with network settings, or the device is not assigned to the site.
|
|
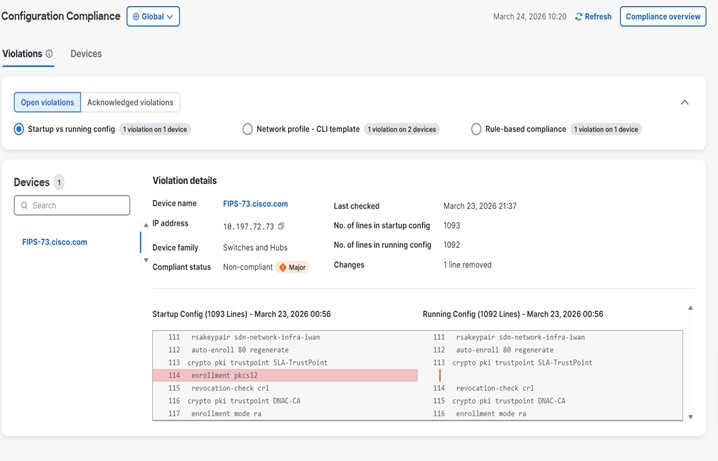
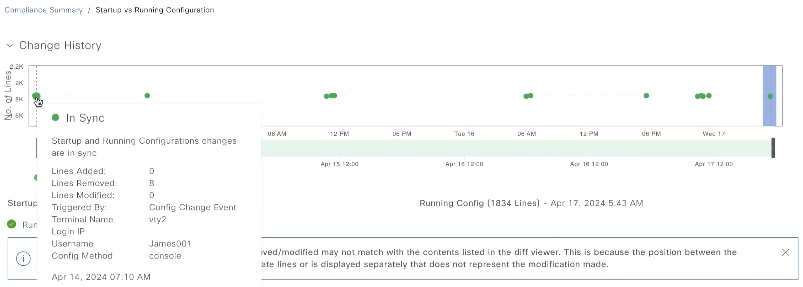
Startup versus Running Configuration
|
This compliance check helps in identifying whether the startup and running configurations of a device are in sync. If the
startup and running configurations of a device are out of sync, compliance is triggered and a detailed report of the out-of-band
changes is displayed. The compliance for startup vs. running configurations is triggered within 2 minutes of any out-of-band
changes.
|
Note
|
Catalyst Center must be configured as a syslog server in the Design > Network Settings > Telemetry > Syslogs window for syslog-based collection to work.
|
|
-
Non-compliant: The startup and running configurations are not the same. In the detailed view, the system shows different startup
vs. running between or running vs. previous running.
-
Compliant: The startup and running configurations are the same.
-
NA (Not Applicable): The device, such as AireOS, is not supported for this compliance type.
|
|
Software and hardware compliance
|
|
Software Image
|
This compliance check helps a network administrator to see if the tagged golden image in Catalyst Center is running on the device. It shows the difference between the golden image and the running image for a device. When there
is a change in the software image, the compliance check is triggered immediately without any delay.
|
-
Non-compliant: The device is not running the tagged golden image of the device family.
-
Compliant: The device is running the tagged golden image of the device family.
-
NA (Not Applicable): The golden image is not available for the selected device family.
|
|
For Fabric Devices:
-
Non-compliant: The device is not running the tagged golden image of the device family, or the current software image version
is not compatible for the network device.
See the Cisco SD-Access Compatibility Matrix for the supported and recommended software image versions for your device.
-
Compliant: The device is running the tagged golden image of the device family, or the current software image version is compatible
with the device.
-
NA (Not Applicable): The golden image is not available for the selected device family, or the device is not added to a fabric
site.
|
|
For Cisco Switch Stacks: Catalyst Center allows the network administrator to check if the tagged golden image is running on the primary switch and members of switch
stacks.
|
-
Non-compliant: The tagged golden image is not running on the primary switch and member switches.
Also, the device will be non-compliant if golden tagging is not applicable for the device and the member switches are not
running on the image version as that of the primary switch.
-
Compliant: The tagged golden image is running on the primary switch and member switches.
Also, the device will be compliant if no golden tagging is applicable for the device and the member switches are running on
the same image version as that of the primary switch.
-
NA (Not Applicable): The golden image is not applicable for the device, and the device is not a stacked switch.
|
|
EoX - End of Life
|
Catalyst Center allows you to check the compliance status for the hardware, software, and module of EoX devices. You can check the EoX compliance
status from the Compliance Summary > EoX - End of Life tile.
You can also view the EoX status of devices from the Inventory window, under the EoX Status column.
|
Note
|
To enable access to the EoX feature, authorize the CX Cloud Consent to Connect agreement through the Catalyst Center dashboard.
|
|
-
Non-compliant: The device is non-compliant if the last date of support has ended.
-
Compliant: The device is compliant if enough time remains until the last date of support.
-
Compliant with Warning: The device is compliant with warning if the last date of support is nearing.
|
|
Vulnerability compliance
|
|
Critical Security (PSIRT)
|
This compliance check enables a network administrator to check whether the network devices are running without critical security
vulnerabilities.
|
-
Non-compliant: The device has critical advisories. A detailed report displays various other information.
-
Compliant: There are no critical vulnerabilities in the device.
-
NA (Not Applicable): The security advisory scan has not been done by the network administrator in Catalyst Center, or the device is not supported.
|
|
Intent compliance
|
|
Fabric (SDA)
This feature is in beta.
|
Fabric compliance helps to identify fabric intent violations, such as any out-of-band changes for fabric-related configurations.
The fabric compliance status does not participate in determining the overall compliance status of the device, as the feature
is in the beta stage.
|
|
|
SD-Access Unsupported Configuration
This feature is in beta.
|
This compliance check enables you to identify unsupported SD-Access configurations. When a device is added to a fabric site,
the compliance check is triggered immediately.
To view the unsupported SD-Access configurations on a noncompliant device, click Unsupported Configuration. Under the Unsupported Configuration area, unsupported SD-Access configurations are highlighted in red.
|
Note
|
For devices that are not added to a fabric site, this compliance check is not used.
|
|
|
|
Policy Intent Compliance
|
|
Application Visibility
|
Catalyst Center allows you to create an application visibility intent and provision it to a device through CBAR and NBAR. If there is an
intent violation on the device, this check identifies, assesses, and shows the violation as compliant or noncompliant under
the Application Visibility window.
The automatic compliance checks are scheduled to run after 5 hours of receiving traps.
|
|
|
Model Config
|
This compliance check enables the network administrator to check any mismatch from the designed intent of Model Config. The
mismatch is shown under Network Profile in the Compliance Summary window.
|
|
|
CLI Template
|
Catalyst Center allows the network administrator to compare the CLI template with the running configuration of the device. The mismatch in
the configuration is flagged. This mismatch is shown under Network Profile in the Compliance Summary window.
To view the flagged CLI commands:
-
Click the Network Profile tile.
-
From the CLI Deviations area, choose the CLI template for which you want to view the mismatch.
-
The CLI commands are displayed in the Realize Template area, and the flagged commands are highlighted in red.
|
Note
|
Click the View CLI Template Best Practices link to view some of the best practices that must be used in a CLI template to minimize compliance issues.
|
The running configuration for CLI template compliance is taken from the latest archive that is available for the device. Event-based
archive takes at least 2 minutes to update after traps are received. For accurate results, we recommend that you wait at least
2 minutes before running compliance manually after a configuration change.
Catalyst Center must be configured as a syslog server in the Design > Network Settings > Telemetry > Syslogs window for syslog-based collection to work.
|
-
Non-compliant: There is a mismatch between the CLI template and the running configuration of the device.
-
Compliant: There is no mismatch between the CLI template and the running configuration of the device.
|

 Feedback
Feedback