Zero Touch Provisioning concepts
The ZTP allows you to ship factory-fresh devices to a branch office or remote location and provision them when physically installed. Local operators can cable these devices to the network without installing an image or the need to fully configure them. To use ZTP, you first establish an entry for each device in the DHCP server and in ZTP. You can then activate ZTP processing by connecting the device to the network and powering it on or reloading it. The device will download and apply a software image and configurations to the device automatically (you can also apply configurations only). When configured, ZTP onboards the new device to the Cisco Crosswork device inventory. You can then use other Crosswork Network Controller functionalities to monitor and manage the device.
ZTP uses the following basic terms and concepts:
-
Evaluation License Countdown : You can use ZTP to onboard devices without licenses for 90 days. After this evaluation period expires, you cannot use ZTP to onboard new devices until you purchase and install a license bundle with enough capacity to cover all prior devices onboarded using ZTP, as well as your projected future needs.
-
Image file : A binary software image file, used to install the network operating system on a device. For Cisco devices, these files are the supported versions of Cisco IOS images. Software image installation is an optional part of ZTP processing. When configured to do so, the ZTP process downloads the image from the Crosswork Network Controller to the device, and the device installs it. If you must also install SMUs, ZTP can install them as part of configuration processing in Classic and Secure ZTP (SMUs are not supported in PnP ZTP).
-
Configuration handling method : A Secure ZTP user option. It allows you to specify whether you want to merge a new configuration into the existing device configuration or to overwrite it.
-
Credential profile : Collections of passwords and community strings that are used to access devices via SNMP, SSH, HTTP, and other network protocols. Crosswork Network Controller uses credential profiles to access your devices, automating device access. All credential profiles store passwords and community strings in encrypted format.
-
Bootfile name : The explicit path to and name of a software image that is stored in the ZTP repository. For each device you plan to onboard using ZTP, specify the bootfile name as part of the device configuration in DHCP.
-
HTTPS/TLS : Hypertext Transport Protocol Secure (HTTPS) is a secure form of the HTTP protocol. It wraps an encrypted layer around HTTP. This layer is the Transport Layer Security (TLS) (formerly Secure Sockets Layer, or SSL).
-
iPXE : The open-source boot firmware iPXE is the popular implementation of the Preboot eXecution Environment (PXE) client firmware and boot loader. iPXE allows devices without built-in PXE support to boot from the network. The iPXE boot process is a normal part of Classic ZTP processing.
-
UUID : The Universal Unique Identifier (UUID) identifies a device when it is onboarded.
-
Image ID : The image ID uniquely identifies an image file that you have uploaded to Crosswork Network Controller. You use the image ID of the software image file in the DHCP bootfile URL with Classic and Secure ZTP.
-
ZTP asset : ZTP requires access to several types of files and information in order to onboard new devices. We refer to these files and information collectively as "ZTP assets." You load these assets as part of the ZTP setup, before initiating ZTP processing.
-
ZTP profile : Crosswork Network Controller storage construct that combines (normally) one image and one configuration into a single unit. Crosswork Network Controller uses ZTP profiles to automate imaging and configuration processes. Using ZTP profiles is optional, but we recommended them. They are an easy way to organize ZTP images and configurations around device families, classes, and roles, and help maintain consistency.
-
ZTP repository : The location where the Crosswork Network Controller stores image and configuration files.
Types of ZTP processes
-
Secure ZTP : A secure process to download and apply software images and configuration files to devices. It uses secure transport protocols and certificates to verify devices and perform downloads, which makes it more suitable for use over public networks.
-
Classic ZTP : A process to download and apply software and configuration files to devices. It uses iPXE firmware and HTTP to boot the device and perform downloads. As it does not use secure communications, it is not suitable for use over public networks.
-
PnP ZTP : A secure process to download and apply software images and configuration files to Cisco IOS-XE devices. It uses Cisco Plug and Play (Cisco PnP) to verify devices and perform downloads over a secure, encrypted channel. It offers much the same level of security as Secure ZTP, but only for Cisco IOS-XE devices.
Certificates and ownership
-
Owner Certificate : The Certificate Authority (CA)-signed end-entity certificate for your organization, which binds a public key to your organization. You install Owner Certificates on your devices as part of Secure ZTP processing.
-
Ownership Voucher : The Ownership Voucher is used to identify the owner of the device by verifying the Owner Certificate that is stored in the device. Cisco supplies Ownership Vouchers in response to requests from your organization. For information on how to get the Ownership Vouchers from Cisco, see Ownership voucher requirements .
-
SUDI : The Secure Unique Device Identifier (SUDI) is a certificate with an associated key pair. The SUDI contains the device's product identifier and serial number. Cisco inserts the SUDI and key pair in the device hardware Trust Anchor module (TAm) during manufacturing, giving the device an immutable identity. During Secure ZTP processing, the back-end system challenges the device to validate its identity. The router responds using its SUDI-based identity. This exchange, and the TAm encryption services, permit the back-end system to provide encrypted image and configuration files. Only the validated router can open these encrypted files, ensuring confidentiality in transit over public networks.
-
SUDI Root CA certificates : A root authority certificate for SUDIs, issued and signed by a Certificate Authority (CA), used to authenticate subordinate SUDI certificates.
Cisco Plug and Play (Cisco PnP)
Cisco Plug and Play: Cisco's proprietary ZTP, bundled in most IOS software images. Cisco PnP uses a software PnP agent and a PnP server to distribute images and configurations to devices. To ensure that communications are secure, the server and agent communicate using HTTPS.
-
Cisco PnP agent : A software agent embedded in Cisco IOS-XE devices. Whenever a device that supports the PnP agent powers up for the first time without a startup configuration file, the agent tries to find a Cisco PnP server. The agent can use various means to discover the server's IP address, including DHCP and DNS.
-
Cisco PnP server : A central server for managing and distributing software images and configurations to Cisco PnP-enabled devices. ZTP has an embedded PnP server, which is configured to communicate with PnP agents using HTTPS.
Configuration file
-
A file used to set the operating parameters of the newly imaged or re-imaged device. Depending on the ZTP mode you plan to use, the file may be a Python script, Linux shell script, or a sequence of Cisco IOS CLI commands stored as ASCII text (not all of these are supported in all ZTP modes). The ZTP process downloads the configuration file to the newly imaged device, which then executes it. The ZTP process requires a single configuration file. The secure ZTP process supports up to three different configuration files, which are applied during onboarding in the following order:
-
Pre-configuration: A preconfiguration file is a file used to set the initial operating parameters of a newly imaged or re-imaged device. The preconfiguration file is essential for automating the setup process, allowing the device to be configured without manual intervention.
-
Day-zero: A day-zero file is a configuration file that is used to set up a newly imaged or re-imaged device right from the start, often referred to as "day zero." The day-zero file is crucial for automating the initial configuration process, enabling the device to be operational without manual setup.
-
Post-configuration: A post-configuration file is used to apply additional settings and configurations to a device after the initial setup has been completed. This file can include advanced configurations, updates, or custom scripts that further refine the device's operation. The post-configuration file ensures that the device meets specific operational requirements and is fully optimized for its intended use.
The pre-configuration and post-configuration may have references to the day-zero configuration file, which indicates that the pre and post- configuration files require the UUID from the day-zero file.
-
License consumption for ZTP onboarding
The ZTP licensing follows a consumption-based model with licenses that are sold in blocks. To regain the ability to onboard devices using ZTP, you must install a license block that covers both the number of devices you onboarded during the trial period as well as the new devices you expect to onboard with ZTP in the future. For example: If you onboard 10 devices during the trial and then install a license bundle for 10 devices on day 91, you have no licenses that are left to use, and must install at least one more license block before onboarding another device. You can add more license blocks as needed. Operators should monitor license consumption to avoid running out of licenses unexpectedly. To see how many licenses you have used and are still available, check Cisco Smart Licensing site .
Your onboarded ZTP devices are always associated with either:
-
A serial number, or
-
For IOS-XR devices: The values of the Option 82 location ID attributes (remote ID and circuit ID).
Serial numbers and location IDs form an "allowed" list. ZTP uses this list when deciding to onboard a device and assign it a license. If you delete an onboarded ZTP device from inventory, and then onboard it again later, use the same serial number or location ID. If you use a different serial number or location ID, you may consume an extra license. The current release provides no workaround for this scenario. In any case, you can't have two different ZTP devices with the same serial number or location ID active at the same time.
Platform support for ZTP
For the most accurate and up-to-date list of hardware and software versions that Classic ZTP, Secure ZTP, and PNP ZTP supports, refer to the Cisco Crosswork Network Controller Essentials Supported Devices.
 Important |
ZTP does not support third-party devices. |
Requirements for provisioning third-party devices with secure ZTP
Secure ZTP supports provisioning for third-party devices only if the third-party devices:
-
Are 100 percent compliant with the Secure ZTP RFC 8572.
-
Match the Cisco format guidelines for serial numbers in device certificates and ownership vouchers.
Guidelines for third-party device certificates and ownership vouchers
Secure ZTP processing for any device starts with a successful HTTPS/TLS handshake between the device and Crosswork Network Controller. After the handshake, Secure ZTP must extract a serial number from the device certificate. Secure ZTP then validates the extracted serial number against its internal "allowed" list of serial numbers. You create the allowed list by uploading device serial numbers to Cisco Crosswork. A similar serial-number validation step occurs later, when Crosswork uses ownership vouchers to validate downloads.
Unlike Cisco IOS-XR devices, the format of the serial number in third-party vendors' device certificates is not standardized
across vendors. Typically, a third-party vendor's device certificate has a Subject field or section. The Subject contains multiple key-value pairs that the vendor decides upon. One of the keys is usually serialNumber. This key's value contains the actual device serial number as a string, which is preceded by the string SN:. For example:
Let's suppose that the third-party device certificate's Subject section contains the following key and value: serialNumber = PID:NCS-5501 SN:FOC2331R0CW. Secure ZTP will take the value after the SN: string and attempt to match that to one of the serial numbers in the allowed list.
If the third-party vendor's device certificate has a different format, validation failures can occur. The degree of failure
depends on the degree of difference. The vendor certificate may not match this format at all. The certificate's Subject field may not contain a serialNumber key with a value that contains the SN: string. In this case, Secure ZTP processing falls
back to using the whole string value of the serialNumber key (if present) as the device serial number. It will then try to match that value to one in the allowed list of serial numbers.
These two methods – string matching and the fallback – are the only means Secure ZTP has for determining the third-party device's
serial number. If the vendor certificate differs from this expectation, Secure ZTP is unable to validate the device.
Secure ZTP has similar format expectations for ownership vouchers (OVs). Cisco tools generate ownership vouchers with filenames
in the format SerialNumber.vcj, where SerialNumber is the device's serial number.
Secure ZTP extracts the serial number from the filename and then attempts to match it to one in the allowed list. For multivendor support, we assume that third-party vendor tools generate OV files with file names in the same format. If this expectation isn't met, validation fails.
Comparison of ZTP implementation modes
ZTP offers a range of implementation choices and cost versus benefit tradeoffs worth considering in advance. As a best practice, always choose the most secure implementation that is supported by your devices.
-
Classic ZTP is easier to implement than Secure ZTP. It needs no Pinned Domain Certificate (PDC), owner certificates, or ownership vouchers. It’s less subject to processing errors, as device and server verification is less stringent and setup is less complex. It’s your only choice if your Cisco devices run IOS-XR versions earlier than 7.3.1, as Secure and PnP ZTP are not supported on earlier versions of the software. Although Classic ZTP includes a device serial-number check, it remains unsecured at the transport layer. It's not recommended if routes to your remote devices cross a metro or otherwise unsecured network.
-
Use Secure ZTP when:
-
Your ZTP traffic must traverse unsecured public networks.
-
Your Cisco IOS-XR devices support Secure ZTP and are at the required software level.
The additional security that Secure ZTP provides requires a more complex setup than either Classic or PnP ZTP. This complexity can make configuration error-prone if you’re new to the setup tasks. Secure ZTP setup also requires a PDC, owner certificates and ownership vouchers from Cisco.
Consider using Secure ZTP if your devices are from third-party manufacturers; Classic and PnP ZTP don't support third-party hardware. Third-party devices and their software must be 100 percent compliant with RFCs 8572 and 8366 . Device certificates for third-party devices must contain the device serial number. Third-party ownership vouchers must be in a format that uses the device serial number as the filename. Cisco doesn't guarantee Secure ZTP compatibility with all third-party devices. For more details on third-party device support, see Platform support for ZTP.
Secure ZTP offers more flexibility with compatible devices because it offers pre-configuration, day-zero, and post-configuration script execution capability. While both Classic and Secure ZTP modes can chain configuration files, Classic ZTP's ability to execute additional scripts is limited to the support for script execution allowed on specific devices. PnP ZTP can only execute CLI commands, which don't allow for script execution.
-
-
Use PnP ZTP when you want a secure provisioning setup for Cisco IOS-XE devices that support the Cisco PnP protocol. PnP ZTP is less complicated to set up than Secure ZTP, but only slightly more complicated than Classic ZTP.
-
Use ZTP With imaged devices when you do not have to specify a software image when using any of the ZTP modes. This feature allows you the option of shipping to your remote location one or more devices on which you have already installed a software image. Later, connect to these devices and trigger the ZTP processing remotely. You can then apply:
-
A configuration file
-
One or more images or SMUs, with more configurations.
In all cases, the result is to onboard the device. Once onboarded to Crosswork Network Controller, you want to avoid using ZTP to configure the device again. See Options for reconfiguring onboarded ZTP devices for details.
-
Methods for ensuring consistency:
-
Organize your configurations : Keep your configurations as consistent as possible across devices. Start by ensuring that all devices from the same device family and with similar roles have the same or similar basic configurations.
-
Define the role that a device plays depends on your organization, its operational practices, and the complexity of your network environment. For example: Suppose that your organization is a financial services enterprise. It has three types of branches: Sidewalk ATMs, retail branches open during standard business hours, and private trading offices. You could define three sets of basic profiles covering all the devices at each type of branch. You can map your configuration files to each of these profiles.
-
Develop basic script configurations for similar types of devices, then use the script logic to call, or chain, other scripts for devices with special roles. If you’re using Classic ZTP, the script is in the specified configuration file. To extend our example, that script would apply a common configuration, then download and apply other scripts depending on the branch type. If using Secure ZTP, you have even more flexibility, as you can specify pre-configuration and post-configuration scripts in addition to the day-zero configuration script.
ZTP processing logic
When initiated by a device reset or reload, the ZTP process proceeds automatically. Crosswork Network Controller also updates the Devices window with status messages showing the state that each device reaches as it is processed. When a device has reached the Onboarded state, there are additional steps to perform that are beyond the scope of ZTP processing (see, for example, Update ZTP device information).
The scripts used to configure the devices must include notifications of state changes in order for Crosswork Network Controller to accurately report progress as shown in the diagrams. To see examples of these calls, select , then click Download sample script (XR). For information on the sample configuration file, see the Download the sample configuration file section in Prepare and Load Configuration Files.
ZTP processing differs depending on the Classic ZTP, Secure ZTP, or PnP ZTP implementation. The details on each step of ZTP processing for each ZTP mode are explained in these sections:
Classic ZTP processing
The following illustration shows the process logic that Classic ZTP uses to provision and onboard devices. The device state transitions are represented by blocks in the shades of green, positioned on the left side of the illustration.
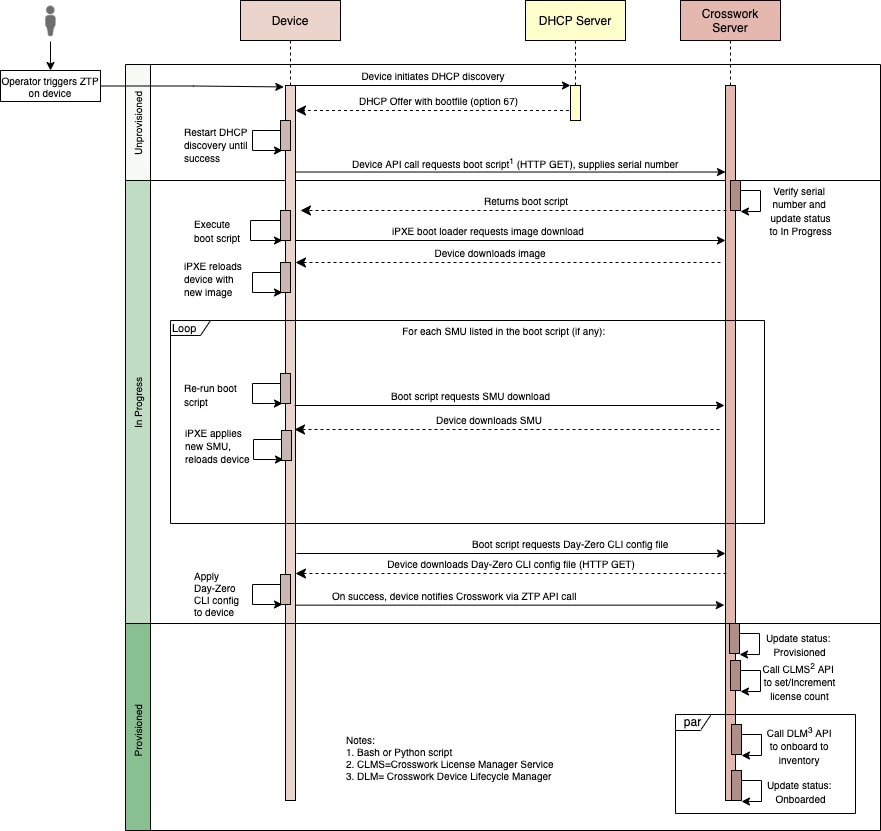
The DHCP server verifies the device identity based on the device serial number, then directs the device to download the boot file and image. Once ZTP images the device, the device downloads the configuration file and executes it.
Secure ZTP processing
The following illustration shows the process logic that Secure ZTP uses to provision and onboard devices. The device state transitions are represented by blocks in the shades of green, positioned on the left side of the illustration.
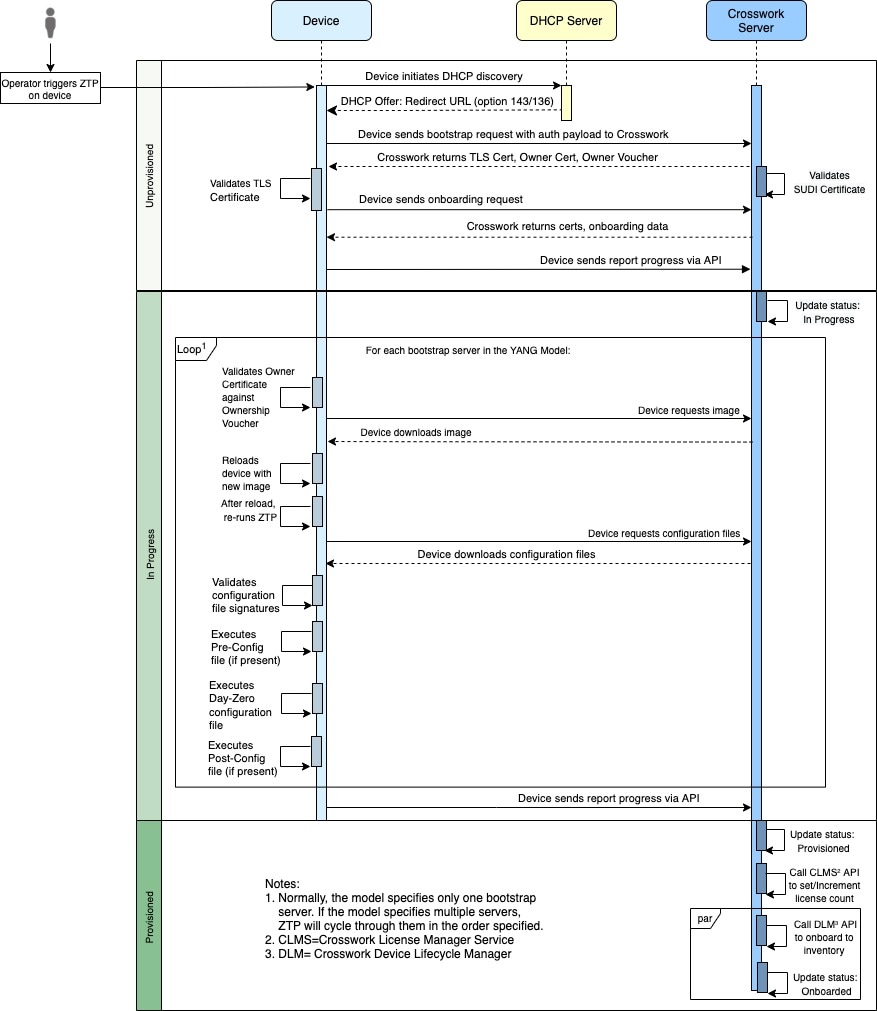
The device and the ZTP bootstrap server authenticate each other using the Secure Unique Device Identifier (SUDI) on the device and server certificates over TLS/HTTPS. Over a secure HTTPS channel, the bootstrap server lets the device download-signed image and configuration artifacts. These artifacts must adhere to the RFC 8572 YANG schema. When the device installs the new image (if any) and reloads, the device downloads configuration scripts and executes them.
PnP ZTP processing
The following illustration shows the process logic that PnP ZTP uses to provision and onboard devices. The device state transitions are represented by blocks in the shades of green, positioned on the left side of the illustration.
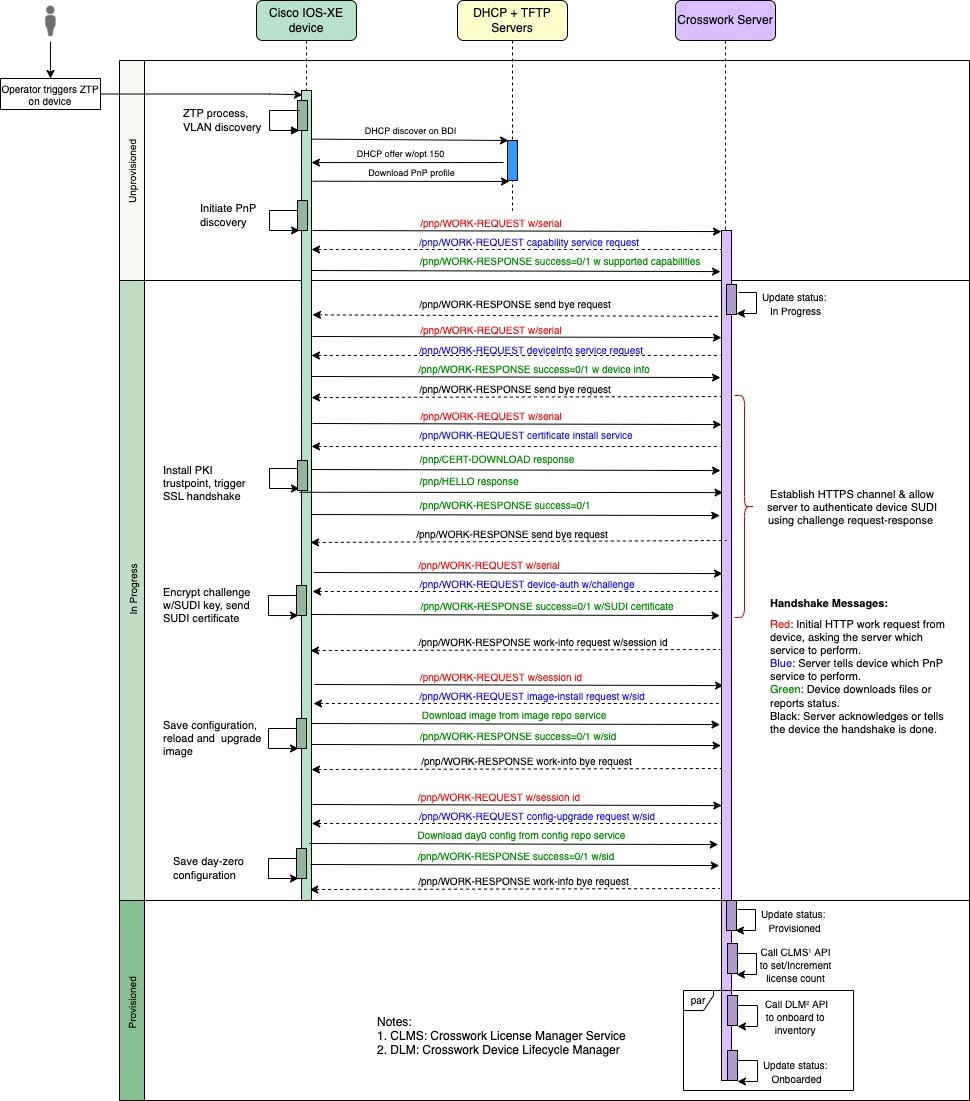
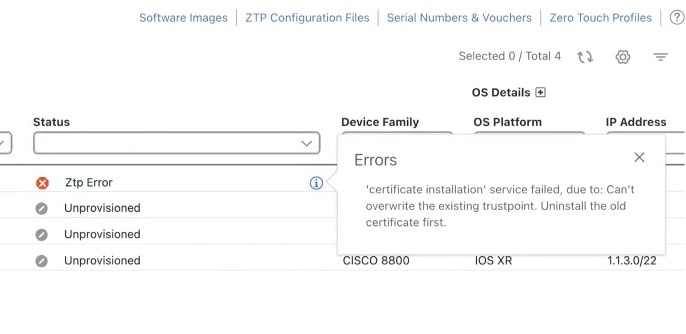
Once an operator triggers PnP ZTP processing, the device performs VLAN discovery and creates a BDI interface, on which DHCP discovery is initiated. The DHCP discovery response provided to the device during DHCP must include Option 150 which directs the device to the TFTP server hosted on the CNC. The device downloads the PnP Profile from the TFTP server without authentication and copies it to the device's running configuration. The PnP Profile is a CLI text file. The profile activates the device's PnP agent and sends work requests to the embedded Crosswork Network Controller PnP server over HTTP on port 30620. The PnP server then validates the device's serial number against Crosswork Network Controller's "allowed" list of serial numbers (previously uploaded to Crosswork Network Controller) and then initiates a PnP capability service request. A successful PnP work response from the device changes the device provisioning status from Unprovisioned to In Progress. Thereafter, the PnP server initiates a series of service requests, including requests for device information, certificate installation, image installation, configuration upgrade, and so on. Each of these service requests involves a four-way handshake between the PnP server and the PnP agent. As part of the certificate-install request, the Crosswork Network Controller PnP server shares its certificate with the device. Successful installation of this trustpoint on the device changes the PnP profile configuration to start using HTTPS and port 30603 on Crosswork Network Controller. Subsequent image and config download requests use HTTPS to secure transactions. There is currently no SUDI certificate authentication support on the device. Once the device downloads and installs a new image (if any) and reloads, the PnP process continues to download CLI configuration files and apply them to device running configuration. The device status is then set to Provisioned and the license count is updated in Crosswork Network Controller. The device status is then set to Onboarded, and the device stops communicating with the PnP server.
 in the same row as
in the same row as 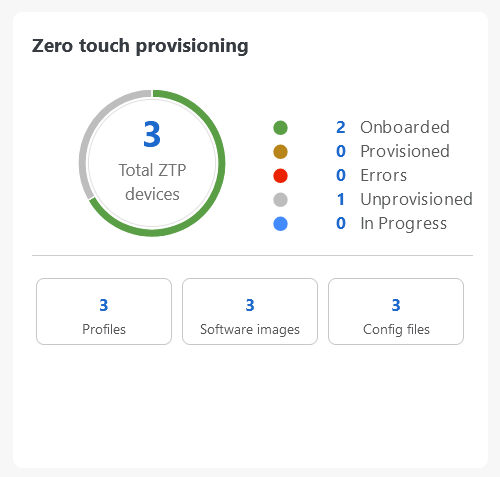

 Feedback
Feedback