Overview
A certificate is an electronic document that identifies an entity such as a person, server, or company and links it to a public key. When a certificate is created, both a public key and a matching private key are generated. In the TLS protocol, the public key encrypts data, while the private key decrypts it.
Certificates are signed by an issuer, often a Certificate Authority (CA), which acts as a "parent" certificate. This process can also be self-signed. In a TLS exchange, a trust chain of certificates verifies the issuer's validity. This chain includes three types of entities: a self-signed root CA certificate, possibly several intermediate CA certificates, and an end-entity certificate. Intermediate certificates connect the server certificates to the root CA, adding security. Starting with the root certificate's private key, each certificate in the chain signs and issues the next one, ending with the end-entity certificate used for server or client authentication. See X.509 Certificates and HTTPS
Certificates in Crosswork Network Controller
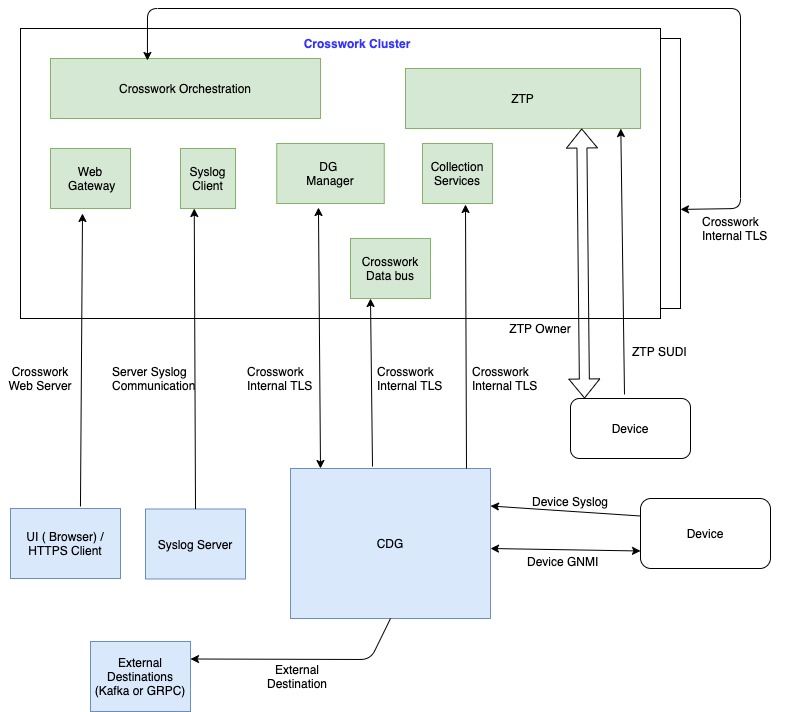
Crosswork Network Controller uses the TLS protocol for secure communication between devices and components. TLS utilizes X.509 certificates to authenticate devices and encrypt data, ensuring its integrity. The system employs a combination of generated certificates and those uploaded by clients. Uploaded certificates might be purchased from Certificate Authorities or be self-signed. For instance, the system's VM-hosted web server and the client browser interface use th system-generated X.509 certificates exchanged over TLS for secure communication
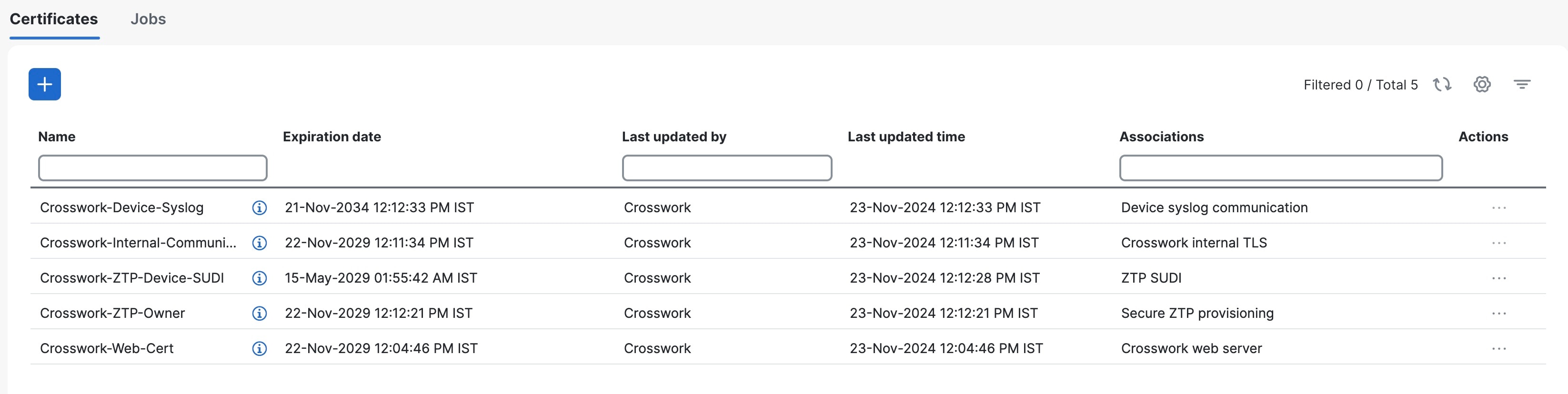
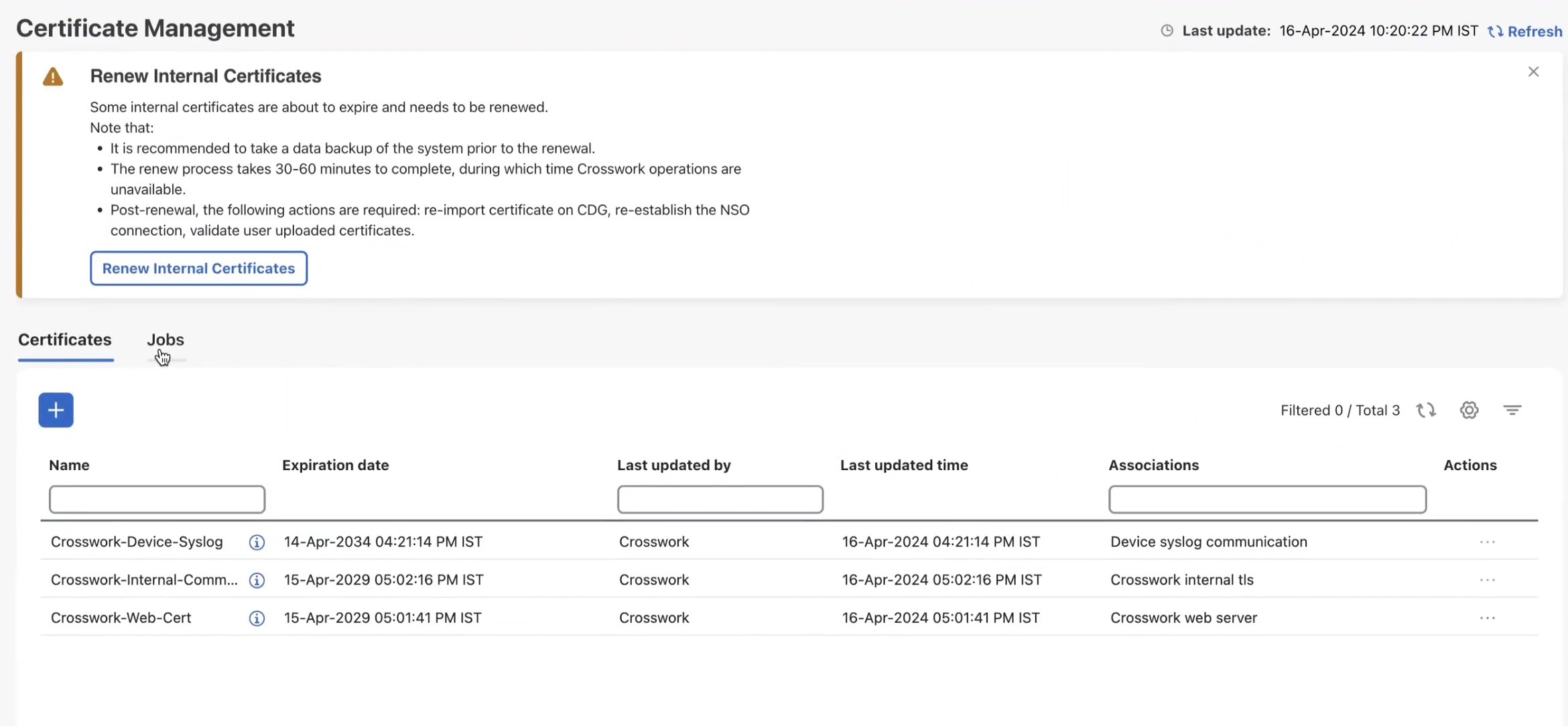
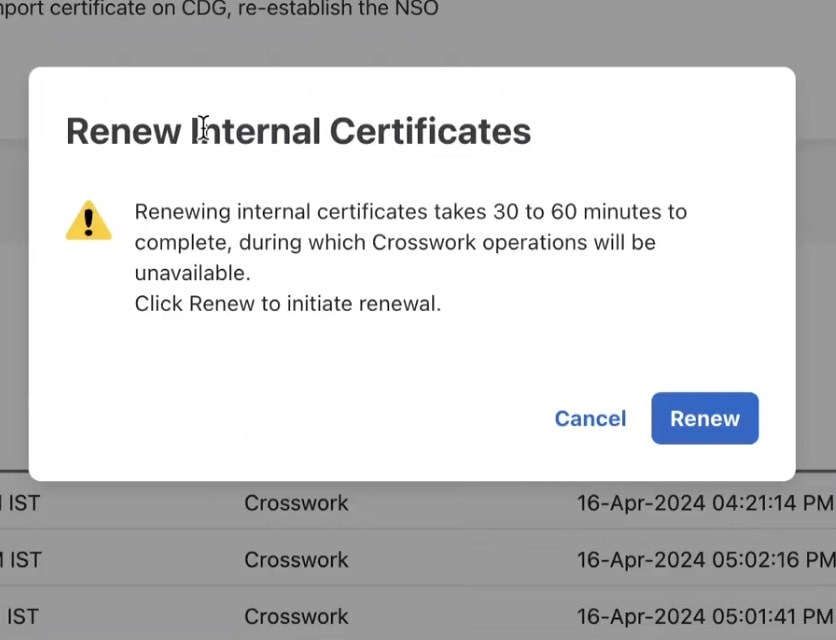
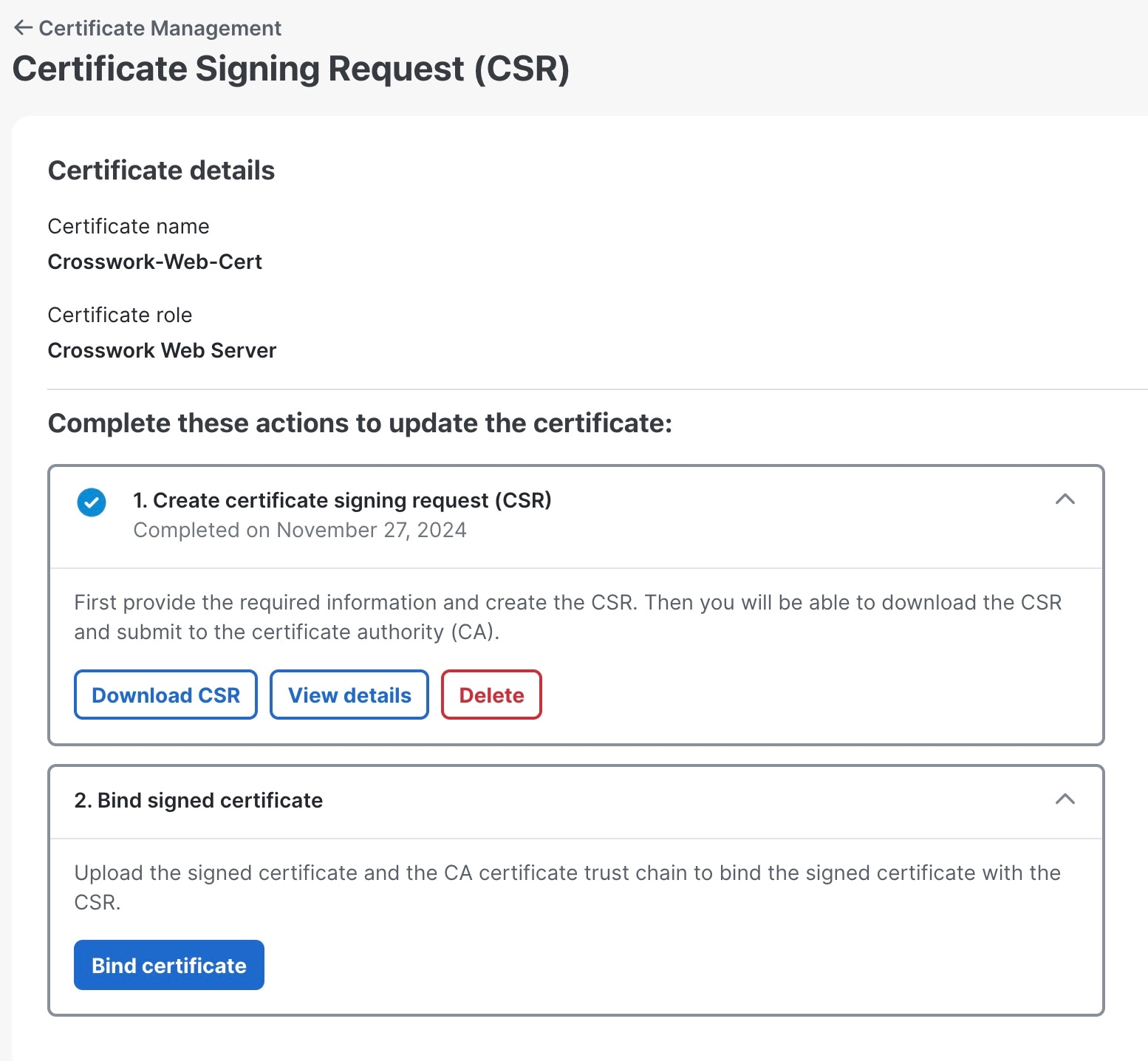
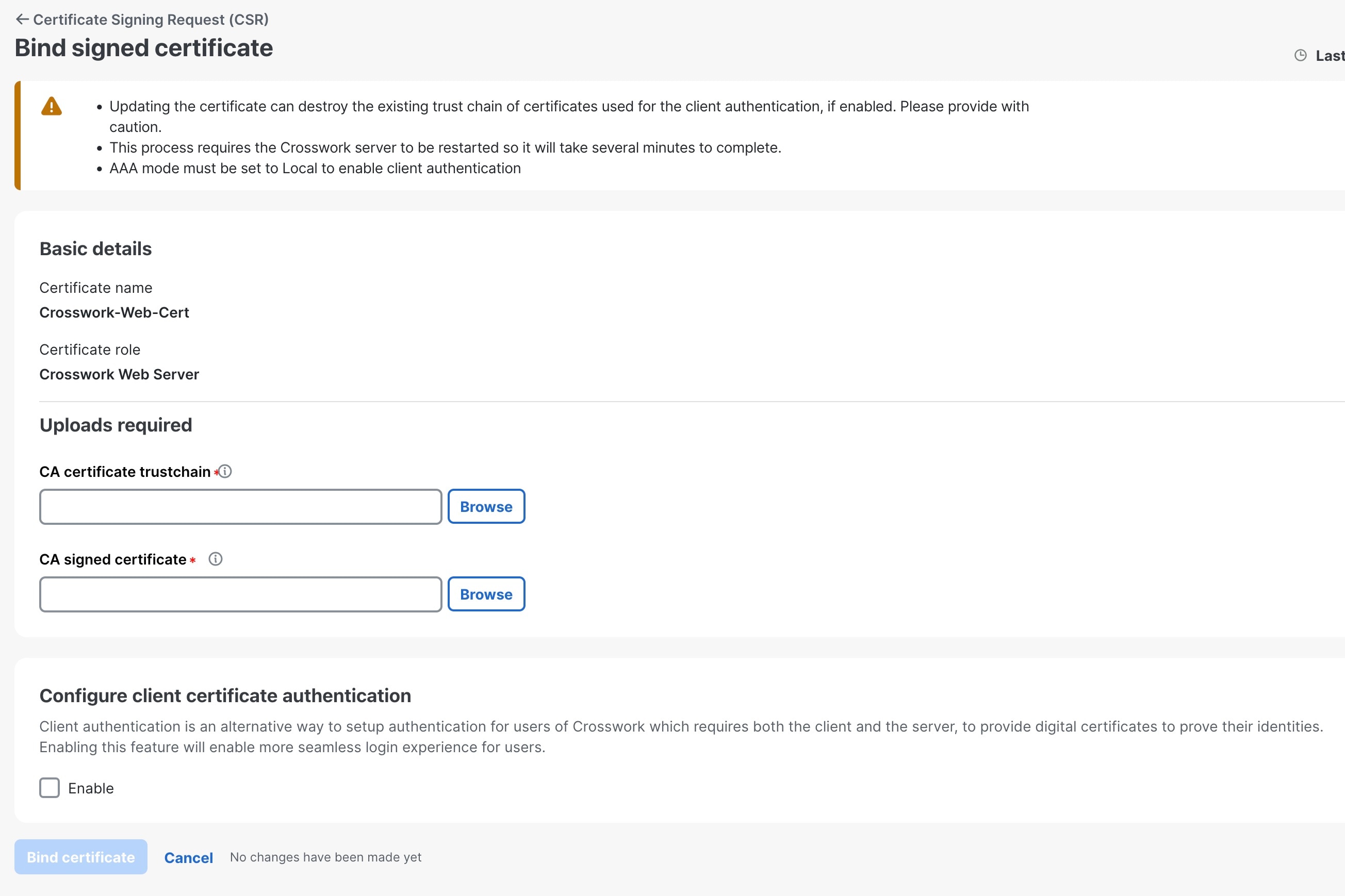
The Crosswork Cert Manager is a proxy for multiple microservices and services within the distributed framework and manages all the Crosswork certificates. The Certificate Management UI () allows you to view, upload, and modify certificates. The following figure displays the default certificates provided by Cisco Crosswork.

 Feedback
Feedback