- Auto Anchor SSID between Wireless LAN Controllers acting as MC
- Enabling Central Web Authentication on ISE
- Configuring Auto Anchor and Mobility Groups on Wireless Services
- Configuring Wireless Multicast on Wireless LAN Controllers
- Converged Access Consolidated Quick Reference Templates for Wireless LAN
- Converged Access Controller AP Join Issue Troubleshoot with Traces
- Converged Access Controllers MAC Address Entry for Network Mobility Service Protocol
- Configuration Example: Converged Access Management through Prime Infrastructure with SNMP v2 and v3
- Converged Access Path Maximum Transmission Unit Discovery
- Third-Party Certificate Installation on Converged Access Wireless LAN Controllers
- Configuration Example: Converged Access for WLC EAP-FAST with Internal RADIUS Server
- Converged Access and WLC Local EAP Authentication Configuration Example
- Configuration Example: Custom Web Authentication with Local Authentication
- Dynamic VLAN Assignment with Converged Access and ACS 5.2 Configuration Example
- Configuration Example: External RADIUS Server EAP Authentication
- External Web Authentication on Converged Access
- Installing Wireless Services
- Local Web Authentication with External RADIUS Authentication
- Local Web Authentication on Converged Access
- PEAP Authentication with Microsoft NPS Configuration
- QoS on Converged Access Controllers and Lightweight Access Points
- Configuration Example: TACACS Administrator Access to Converged Access Wireless LAN Controllers
- Configuration Example: Unified Access WLC Guest Anchor with Converged Access
- VideoStream Troubleshooting
- Custom Web Authentication Locally Hosted on WLC or an External Server
- Wireless Converged Access Chromecast Configuration Example
- Web Passthrough Configuration Example
- Configuration Examples: WPA2-PSK and Open Authentication
Configuration Examples: WPA2-PSK and Open Authentication
- Prerequisites
- WPA2 PSK and Open Authentication
- Verifying WPA2-PSK and Open Authentication Configuration
- Troubleshooting WPA2-PSK and Open Authentication Configuration Issues
Prerequisites
Supported Platforms and Releases
 Note | The information in this document is based on the devices used in a specific lab environment. The devices used in this document started with a default configuration. If your network is live, make sure that you understand the potential impact of the commands. |
WPA2 PSK and Open Authentication
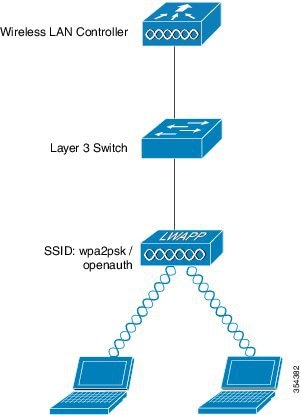
The following figure displays the network diagram for WPA2 PSK and Open Authentication:
- Configuring WPA2-PSK Configuration using CLI
- Configuring WPA2-PSK Configuration using GUI
- Configuring Open Authentication using CLI
- Configuring Open Authentication using GUI
Configuring WPA2-PSK Configuration using CLI
The following example describes the procedure to configure DHCP snooping for the VLANs that are used for the clients. In this example, VLAN20 is used for clients and the pool is configured on the same WLC.
ip device tracking ip dhcp snooping vlan 12,20,30,40 ip dhcp snooping ! ip dhcp pool vlan20 network 192.0.2.0 255.255.255.0 default-router 192.0.2.1 interface Vlan20 ip address 192.0.2.1 255.255.255.0 interface TenGigabitEthernet1/0/1 switchport trunk native vlan 12 switchport mode trunk ip dhcp relay information trusted ip dhcp snooping trust wlan wpa2psk 1 wpa2psk client vlan 20 no security wpa akm dot1x security wpa akm psk set-key ascii 0 Cisco123 no shutdown
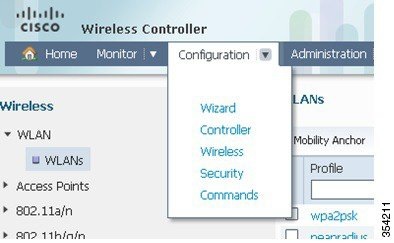
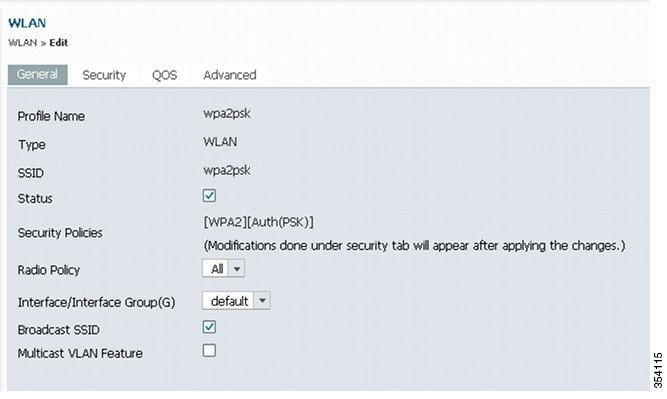
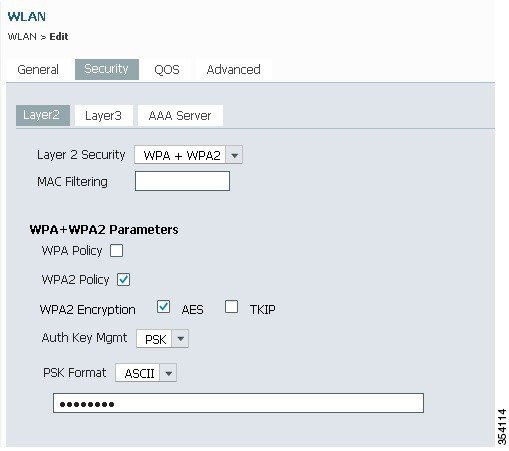
Configuring WPA2-PSK Configuration using GUI
Perform the following steps to configure a WPA2 PSK on the WLC GUI:
Configuring Open Authentication using CLI
The following example describes how to configure DHCP snooping for the VLANs that are used for clients. In the following example, VLAN20 is used for clients and the pool is configured on the same WLC.
ip device tracking ip dhcp snooping vlan 12,20,30,40 ip dhcp snooping ! ip dhcp pool vlan20 network 192.0.2.0 255.255.255.0 default-router 20.20.20.1 interface Vlan20 ip address 192.0.2.1 255.255.255.0 interface TenGigabitEthernet1/0/1 switchport trunk native vlan 12 switchport mode trunk ip dhcp relay information trusted ip dhcp snooping trust wlan open 5 open client vlan VLAN0020 no security wpa no security wpa akm dot1x no security wpa wpa2 no security wpa wpa2 ciphers aes session-timeout 1800 no shutdown
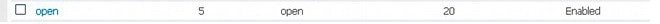
Configuring Open Authentication using GUI
Perform the following steps to configure an open authentication in the WLC GUI:
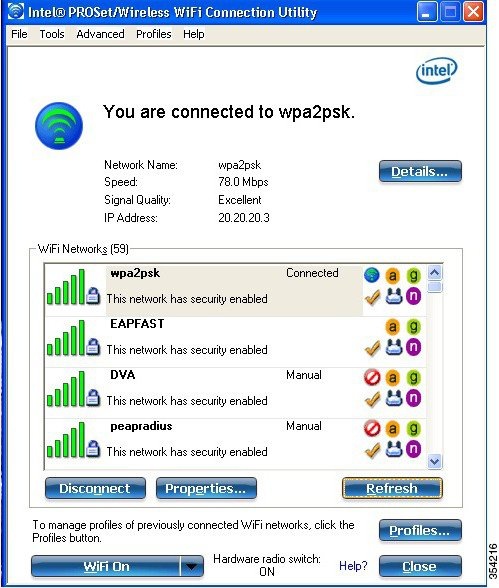
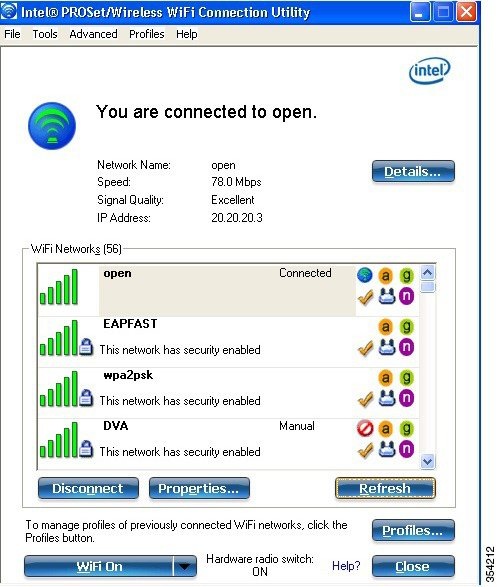
Verifying WPA2-PSK and Open Authentication Configuration
Perform the following to verify the WPA2-PSK and Open Authentication configuration:
Troubleshooting WPA2-PSK and Open Authentication Configuration Issues
debug client mac XXXX.XXXX.XXXX
Device# show debugging
dot11/state debugging is on
pem/events debugging is on
client/mac-addr debugging is on
dot11/detail debugging is on
mac/ filters[string 0021.5c8c.c761] debugging is on
dot11/error debugging is on
dot11/mobile debugging is on
pem/state debugging is on
set trace group-wireless-client filter mac XXXX.XXXX.XXXX
set trace wcm-dot1x event filter mac XXXX.XXXX.XXXX
set trace wcm-dot1x aaa filter mac XXXX.XXXX.XXXX
set trace aaa wireless events filter mac XXXX.XXXX.XXXX
set trace access-session core sm filter mac XXXX.XXXX.XXXX
set trace access-session method dot1x filter XXXX.XXXX.XXXX
*Sep 1 05:55:01.321: 0021.5C8C.C761 Association received from mobile on AP
C8F9.F983.4260 1 wcm: i.D^Iw for client
*Sep 1 05:55:01.321: 0021.5C8C.C761 qos upstream policy is unknown and
downstream policy is unknown 1 wcm: r client
*Sep 1 05:55:01.321: 0021.5C8C.C761 apChanged 0 wlanChanged 1 mscb ipAddr
20.20.20.3, apf RadiusOverride 0x0, numIPv6Addr=0 1 wcm: nJ^Iwy_status 0
attr len^G$8\227v^K
*Sep 1 05:55:01.321: 0021.5C8C.C761 Applying WLAN policy on MSCB. 1 wcm:
ipAddr 20.20.20.3, apf RadiusOverride 0x0, numIPv6Addr=0
*Sep 1 05:55:01.321: 0021.5C8C.C761 Scheduling deletion of Mobile Station: 1
wcm: (callerId: 50) in 1 seconds
*Sep 1 05:55:01.321: 0021.5C8C.C761 Disconnecting client due to switch of
WLANs from 6(wep) to 5(open) 1 wcm:
*Sep 1 05:55:02.193: 0021.5C8C.C761 apfMsExpireCallback (apf_ms.c: 1 wcm: 664)
Expiring Mobile!
*Sep 1 05:55:02.193: 0021.5C8C.C761 apfMsExpireMobileStation (apf_ms.c: 1 wcm:
6953) Changing state for mobile 0021.5C8C.C761 on AP C8F9.F983.4260 from
Associated to Disassociated
*Sep 1 05:55:02.193: 0021.5C8C.C761 Sent Deauthenticate to mobile on BSSID
C8F9.F983.4260 slot 1(caller apf_ms.c: 1 wcm: 7036)
*Sep 1 05:55:02.193: 0021.5C8C.C761 apfMsExpireMobileStation (apf_ms.c: 1 wcm:
7092) Changing state for mobile 0021.5C8C.C761 on AP C8F9.F983.4260 from
Disassociated to Idle
*Sep 1 05:55:02.193: 0021.5C8C.C761 20.20.20.3 RUN (20) Deleted mobile LWAPP
rule on AP [ C8F9.F983.4260 ] 1 wcm: 5C8C.C761 on AP C8F9.F983.4260 from
Disassociated to Idle
*Sep 1 05:55:02.193: 0021.5C8C.C761 20.20.20.3 RUN (20) FastSSID for the
client [ C8F9.F983.4260 ] NOTENABLED 1 wcm: C.C761 on AP C8F9.F983.4260
from Disassociated to Idle
*Sep 1 05:55:02.193: 0021.5C8C.C761 Incrementing the Reassociation Count 1 for
client (of interface VLAN0020) 1 wcm: D
*Sep 1 05:55:02.193: 0021.5C8C.C761 Clearing Address 20.20.20.3 on mobile 1
wcm: for client (of interface VLAN0020)
*Sep 1 05:55:02.193: PEM recv processing msg Del SCB(4) 1 wcm: 0.20.3 on
mobile
*Sep 1 05:55:02.193: 0021.5C8C.C761 20.20.20.3 RUN (20) Skipping TMP rule
add 1 wcm: lient (of interface VLAN0020)
*Sep 1 05:55:02.193: 0021.5C8C.C761 20.20.20.3 RUN (20) Change state to
DHCP_REQD (7) last state RUN (20) 1 wcm:
*Sep 1 05:55:02.193: 0021.5C8C.C761 WCDB_CHANGE: 1 wcm: Client 1 m_vlan 20
Radio iif id 0xbfcdc00000003a bssid iif id 0x8959800000004a, bssid
C8F9.F983.4260
*Sep 1 05:55:02.193: 0021.5C8C.C761 WCDB_AUTH: 1 wcm: Adding opt82 len 0
*Sep 1 05:55:02.193: 0021.5C8C.C761 WCDB_CHANGE: 1 wcm: Suppressing SPI
(client pending deletion) pemstate 7 state LEARN_IP(2) vlan 20 client_id
0xac70800000004b mob=Local(1) ackflag 2 dropd 0, delete 1
*Sep 1 05:55:02.193: 0021.5C8C.C761 Sending SPI spi_epm_epm_terminate_session
successfull 1 wcm: pemstate 7 state LEARN_IP(2) vlan 20 client_id
0xac70800000004b mob=Local(1) ackflag 2 dropd 0, delete 1
*Sep 1 05:55:02.194: 0021.5C8C.C761 Sending SPI spi_epm_epm_terminate_session
successfull 1 wcm: pemstate 7 state LEARN_IP(2) vlan 20 client_id
0xac70800000004b mob=Local(1) ackflag 2 dropd 0, delete 1
*Sep 1 05:55:02.194: 0021.5C8C.C761 Deleting wireless client; Reason code 0,
Preset 1, AAA cause 1 1 wcm: 7 state LEARN_IP(2) vlan 20 client_id
0xac70800000004b mob=Local(1) ackflag 2 dropd 0, delete 1
*Sep 1 05:55:02.194: 0021.5C8C.C761 WCDB_DEL: 1 wcm: Successfully sent
*Sep 1 05:55:02.194: 0021.5C8C.C761 Expiring mobile state delete 1 wcm: on
code 0, Preset 1, AAA cause 1
*Sep 1 05:55:02.194: 0021.5C8C.C761 0.0.0.0 DHCP_REQD (7) Handling pemDelScb
Event skipping delete 1 wcm: state LEARN_IP(2) vlan 20 client_id
0xac70800000004b mob=Local(1) ackflag 2 dropd 0, delete 1
*Sep 1 05:55:02.197: 0021.5C8C.C761 WCDB SPI response msg handler client code
1 mob state 1 1 wcm: g delete
*Sep 1 05:55:02.197: 0021.5C8C.C761 apfProcessWcdbClientDelete: 1 wcm: Delete
ACK from WCDB.
*Sep 1 05:55:02.197: 0021.5C8C.C761 WCDB_DELACK: 1 wcm: wcdbAckRecvdFlag
updated
*Sep 1 05:55:02.197: 0021.5C8C.C761 WCDB_DELACK: 1 wcm: Client IIF Id dealloc
SUCCESS w/ 0xac70800000004b.
*Sep 1 05:55:02.197: 0021.5C8C.C761 Invoked platform delete and cleared handle
1 wcm: w/ 0xac70800000004b.
*Sep 1 05:55:02.197: 0021.5C8C.C761 Deleting mobile on AP C8F9.F983.4260 (1)
1 wcm: w/ 0xac70800000004b.
*Sep 1 05:55:02.197: 0021.5C8C.C761 Unlinked and freed mscb 1 wcm:
8F9.F983.4260 (1)
*Sep 1 05:55:02.197: WCDB_IIF: 1 wcm: Ack Message ID: 0xac70800000004b code
1003
*Sep 1 05:55:02.379: 0021.5C8C.C761 Adding mobile on LWAPP AP C8F9.F983.4260
(1) 1 wcm: xac7080000.D^Iwb.
*Sep 1 05:55:02.379: 0021.5C8C.C761 Creating WL station entry for client -
rc 0 1 wcm:
*Sep 1 05:55:02.379: 0021.5C8C.C761 Association received from mobile on AP
C8F9.F983.4260 1 wcm: 0.D^Iwb.
*Sep 1 05:55:02.379: 0021.5C8C.C761 qos upstream policy is unknown and
downstream policy is unknown 1 wcm:
*Sep 1 05:55:02.379: 0021.5C8C.C761 apChanged 0 wlanChanged 0 mscb ipAddr
0.0.0.0, apf RadiusOverride 0x0, numIPv6Addr=0 1 wcm: \2105HnJ^Iwlient_id
0xac708000^G$8\227v^K
*Sep 1 05:55:02.379: 0021.5C8C.C761 Applying WLAN policy on MSCB. 1 wcm:
ipAddr 0.0.0.0, apf RadiusOverride 0x0, numIPv6Addr=0
*Sep 1 05:55:02.379: 0021.5C8C.C761 Applying WLAN ACL policies to client 1
wcm: 0.0.0.0, apf RadiusOverride 0x0, numIPv6Addr=0
*Sep 1 05:55:02.379: 0021.5C8C.C761 No Interface ACL used for Wireless client
in WCM(NGWC) 1 wcm: usOverride 0x0, numIPv6Addr=0
*Sep 1 05:55:02.379: 0021.5C8C.C761 Applying site-specific IPv6 override for
station 0021.5C8C.C761 - vapId 5, site 'default-group', interface
'VLAN0020' 1 wcm:
*Sep 1 05:55:02.379: 0021.5C8C.C761 Applying local bridging Interface Policy
for station 0021.5C8C.C761 - vlan 20, interface 'VLAN0020' 1 wcm: erface
'VLAN0020'
*Sep 1 05:55:02.379: 0021.5C8C.C761 STA - rates (8): 1 wcm:
140 18 152 36 176 72 96 108 0 0 0 0 0 0 0 0
*Sep 1 05:55:02.379: 0021.5C8C.C761 new capwap_wtp_iif_id b6818000000038,
sm capwap_wtp_iif_id 0 1 wcm: 8C.C761 - vlan 20, interface 'VLAN0020'
*Sep 1 05:55:02.379: 0021.5C8C.C761 WCDB_ADD: 1 wcm: Radio IIFID
0xbfcdc00000003a, BSSID IIF Id 0xbb30c000000046, COS 4
*Sep 1 05:55:02.379: Load Balancer: 1 wcm: Success, Resource allocated are:
Active Switch number: 1, Active Asic number : 0, Reserve Switch number 0
Reserve Asic number 0. AP Asic num 0
*Sep 1 05:55:02.379: 0021.5C8C.C761 WCDB_ADD: 1 wcm: Anchor Sw 1, Doppler 0
*Sep 1 05:55:02.380: 0021.5C8C.C761 WCDB_ALLOCATE: 1 wcm: Client IIF Id alloc
SUCCESS w/ client 8e7bc00000004d (state 0).
*Sep 1 05:55:02.380: 0021.5C8C.C761 iifid Clearing Ack flag 1 wcm: F Id alloc
SUCCESS w/ client 8e7bc00000004d (state 0).
*Sep 1 05:55:02.380: 0021.5C8C.C761 WCDB_ADD: 1 wcm: Adding opt82 len 0
*Sep 1 05:55:02.380: 0021.5C8C.C761 WCDB_ADD: 1 wcm: Cleaering Ack flag
*Sep 1 05:55:02.380: 0021.5C8C.C761 WCDB_ADD: 1 wcm: ssid open bssid
C8F9.F983.4260 vlan 20 auth=ASSOCIATION(0) wlan(ap-group/global) 5/5
client 0 assoc 1 mob=Unassoc(0) radio 1 m_vlan 20 ip 0.0.0.0 src
0xb6818000000038 dst 0x0 cid 0x8e7bc00000004d glob rsc id 14dhcpsrv
0.0.0.0 ty
*Sep 1 05:55:02.380: 0021.5C8C.C761 WCDB_ADD: 1 wcm: mscb iifid
0x8e7bc00000004d msinfo iifid 0x0
*Sep 1 05:55:02.380: 0021.5C8C.C761 0.0.0.0 START (0) Initializing policy 1
wcm: info iifid 0x0
*Sep 1 05:55:02.380: 0021.5C8C.C761 0.0.0.0 START (0) Change state to
AUTHCHECK (2) last state AUTHCHECK (2) 1 wcm: -group/global) 5/5 client 0
assoc 1 mob=Unassoc(0) radio 1 m_vlan 20 ip 0.0.0.0 src 0xb6818000000038
dst 0x0 cid 0x8e7bc00000004d glob rsc id 14dhcpsrv 0.0.0.0 ty
*Sep 1 05:55:02.380: 0021.5C8C.C761 0.0.0.0 AUTHCHECK (2) Change state to
L2AUTHCOMPLETE (4) last state L2AUTHCOMPLETE (4) 1 wcm: 5/5 client 0 assoc
1 mob=Unassoc(0) radio 1 m_vlan 20 ip 0.0.0.0 src 0xb6818000000038 dst 0x0
cid 0x8e7bc00000004d glob rsc id 14dhcpsrv 0.0.0.0 ty
*Sep 1 05:55:02.380: 0021.5C8C.C761 WCDB_CHANGE: 1 wcm: Client 1 m_vlan 20
Radio iif id 0xbfcdc00000003a bssid iif id 0xbb30c000000046, bssid
C8F9.F983.4260
*Sep 1 05:55:02.380: 0021.5C8C.C761 WCDB_AUTH: 1 wcm: Adding opt82 len 0
*Sep 1 05:55:02.380: 0021.5C8C.C761 WCDB_LLM: 1 wcm: NoRun Prev Mob 0, Curr
Mob 0 llmReq 1, return False
*Sep 1 05:55:02.380: 0021.5C8C.C761 auth state 1 mob state 0 setWme 0 wme 1
roam_sent 0 1 wcm: rn False
*Sep 1 05:55:02.380: 0021.5C8C.C761 WCDB_CHANGE: 1 wcm: auth=L2_AUTH(1) vlan
20 radio 1 client_id 0x8e7bc00000004d mobility=Unassoc(0) src_int
0xb6818000000038 dst_int 0x0 ackflag 0 reassoc_client 0 llm_notif 0 ip
0.0.0.0 ip_learn_type UNKNOWN
*Sep 1 05:55:02.380: 0021.5C8C.C761 WCDB_CHANGE: 1 wcm: In L2 auth but l2ack
waiting lfag not set,so set
*Sep 1 05:55:02.380: 0021.5C8C.C761 0.0.0.0 L2AUTHCOMPLETE (4) DHCP Not
required on AP C8F9.F983.4260 vapId 5 apVapId 5for this client 1 wcm:
6818000000038 dst_int 0x0 ackflag 0 reassoc_client 0 llm_notif 0 i$=6v.0.0.0
it^_Dv^\7HnP6v^D6Hl5Ht^_Dv$6H8^ r^D6H>&5v8^ r^D6H>&5v^D6Ht^M^Lw^\7H8^ r
*Sep 1 05:55:02.380: WCDB_IIF: 1 wcm: Ack Message ID: 0x8e7bc00000004d code
1001
*Sep 1 05:55:02.380: 0021.5C8C.C761 Not Using WMM Compliance code qosCap 00 1
wcm: quired on AP C8F9.F983.4260 vapId 5 apVapId 5for this client
*Sep 1 05:55:02.380: 0021.5C8C.C761 0.0.0.0 L2AUTHCOMPLETE (4) Plumbed
mobile LWAPP rule on AP C8F9.F983.4260 vapId 5 apVapId 5 1 wcm: client
*Sep 1 05:55:02.380: 0021.5C8C.C761 0.0.0.0 L2AUTHCOMPLETE (4) Change state
to DHCP_REQD (7) last state DHCP_REQD (7) 1 wcm: apVapId 5
*Sep 1 05:55:02.380: 0021.5C8C.C761 WCDB_CHANGE: 1 wcm: Client 1 m_vlan 20
Radio iif id 0xbfcdc00000003a bssid iif id 0xbb30c000000046, bssid
C8F9.F983.4260
*Sep 1 05:55:02.380: 0021.5C8C.C761 WCDB_AUTH: 1 wcm: Adding opt82 len 0
*Sep 1 05:55:02.380: 0021.5C8C.C761 WCDB_CHANGE: 1 wcm: Suppressing SPI
(Mobility state not known) pemstate 7 state LEARN_IP(2) vlan 20 client_id
0x8e7bc00000004d mob=Unassoc(0) ackflag 1 dropd 0
*Sep 1 05:55:02.380: 0021.5C8C.C761 Incrementing the Reassociation Count 1 for
client (of interface VLAN0020) 1 wcm: EARN_IP(2) vlan 20 client_id
0x8e7bc00000004d mob=Unassoc(0) ackflag 1 dropd 0
*Sep 1 05:55:02.380: 0021.5C8C.C761 apfPemAddUser2 (apf_policy.c: 1 wcm: 161)
Changing state for mobile 0021.5C8C.C761 on AP C8F9.F983.4260 from Idle
to Associated
*Sep 1 05:55:02.380: 0021.5C8C.C761 Scheduling deletion of Mobile Station: 1
wcm: (callerId: 49) in 1800 seconds
*Sep 1 05:55:02.380: 0021.5C8C.C761 Ms Timeout = 1800, Session Timeout = 1800
1 wcm: llerId: 49) in 1800 seconds
*Sep 1 05:55:02.381: 0021.5C8C.C761 Sending Assoc Response to station on BSSID
C8F9.F983.4260 (status 0) ApVapId 5 Slot 1 1 wcm: .F983.4260 from Idle to
Associated
*Sep 1 05:55:02.381: 0021.5C8C.C761 apfProcessAssocReq (apf_80211.c: 1 wcm:
5260) Changing state for mobile 0021.5C8C.C761 on AP C8F9.F983.4260
from Associated to Associated
*Sep 1 05:55:02.381: 0021.5C8C.C761 0.0.0.0 DHCP_REQD (7) pemAdvanceState2:
1 wcm: MOBILITY-INCOMPLETE with state 7.
*Sep 1 05:55:02.381: 0021.5C8C.C761 0.0.0.0 DHCP_REQD (7) pemAdvanceState2:
1 wcm: MOBILITY-INCOMPLETE with state 7.
*Sep 1 05:55:02.381: 0021.5C8C.C761 0.0.0.0 DHCP_REQD (7) pemAdvanceState2:
1 wcm: MOBILITY-COMPLETE with state 7.
*Sep 1 05:55:02.381: 0021.5C8C.C761 0.0.0.0 DHCP_REQD (7) State Update from
Mobility-Incomplete to Mobility-Complete, mobility role=Local, client
state=APF_MS_STATE_ASSOCIATED 1 wcm: 1 dropd 0
*Sep 1 05:55:02.381: 0021.5C8C.C761 0.0.0.0 DHCP_REQD (7) pemAdvanceState2
3611, Adding TMP rule 1 wcm: o Mobility-Complete, mobility role=Local,
client state=APF_MS_STATE_ASSOCIATED
*Sep 1 05:55:02.381: 0021.5C8C.C761 0.0.0.0 DHCP_REQD (7) Adding Fast Path
rule on AP C8F9.F983.4260 , slot 1 802.1P = 0 1 wcm: role=Local, client
state=APF_MS_STATE_ASSOCIATED
*Sep 1 05:55:02.381: 0021.5C8C.C761 0.0.0.0 DHCP_REQD (7) Successfully
plumbed mobile rule 1 wcm: F9.F983.4260 , slot 1 802.1P = 0^M
*Sep 1 05:55:02.381: 0021.5C8C.C761 WCDB_CHANGE: 1 wcm: Client 1 m_vlan 20
Radio iif id 0xbfcdc00000003a bssid iif id 0xbb30c000000046, bssid
C8F9.F983.4260
*Sep 1 05:55:02.381: 0021.5C8C.C761 WCDB_AUTH: 1 wcm: Adding opt82 len 0
*Sep 1 05:55:02.381: 0021.5C8C.C761 WCDB_LLM: 1 wcm: NoRun Prev Mob 0, Curr
Mob 1 llmReq 1, return False
*Sep 1 05:55:02.381: 0021.5C8C.C761 WCDB_CHANGE: 1 wcm: Suppressing SPI (ACK
message not recvd) pemstate 7 state LEARN_IP(2) vlan 20 client_id
0x8e7bc00000004d mob=Local(1) ackflag 1 dropd 1
*Sep 1 05:55:02.381: 0021.5C8C.C761 Error updating wcdb on mobility complete
1 wcm: not recvd) pemstate 7 state LEARN_IP(2) vlan 20 client_id
0x8e7bc00000004d mob=Local(1) ackflag 1 dropd 1
*Sep 1 05:55:02.381: PEM recv processing msg Epm spi response(12) 1 wcm:
complete
*Sep 1 05:55:02.381: 0021.5C8C.C761 aaa attribute list length is 79 1 wcm:
complete
*Sep 1 05:55:02.381: 0021.5C8C.C761 Sending SPI spi_epm_epm_session_create
successfull 1 wcm: ) pemstate 7 state LEARN_IP(2) vlan 20 client_id
0x8e7bc00000004d mob=Local(1) ackflag 1 dropd 1
*Sep 1 05:55:02.381: PEM recv processing msg Add SCB(3) 1 wcm:
pm_session_create successfull
*Sep 1 05:55:02.381: 0021.5C8C.C761 0.0.0.0, auth_state 7 mmRole Local !!! 1
wcm: successfull
*Sep 1 05:55:02.381: 0021.5C8C.C761 0.0.0.0, auth_state 7 mmRole Local,
updating wcdb not needed 1 wcm: 7 state LEARN_IP(2) vlan 20 client_id
0x8e7bc00000004d mob=Local(1) ackflag 1 dropd 1
*Sep 1 05:55:02.381: 0021.5C8C.C761 Tclas Plumb needed: 1 wcm: 0
*Sep 1 05:55:02.384: EPM: 1 wcm: Session create resp - client handle
8e7bc00000004d session b8000020
*Sep 1 05:55:02.384: EPM: 1 wcm: Netflow session create resp - client handle
8e7bc00000004d sess b8000020
*Sep 1 05:55:02.384: PEM recv processing msg Epm spi response(12) 1 wcm:
le 8e7bc00000004d sess b8000020
*Sep 1 05:55:02.384: 0021.5C8C.C761 Received session_create_response for
client handle 40105511256850509 1 wcm: LEARN_IP(2) vlan 20 client_id
0x8e7bc00000004d mob=Local(1) ackflag 1 dropd 1
*Sep 1 05:55:02.384: 0021.5C8C.C761 Received session_create_response with EPM
session handle 3087007776 1 wcm:
*Sep 1 05:55:02.384: 0021.5C8C.C761 Send request to EPM 1 wcm: ate_response
with EPM session handle 3087007776
*Sep 1 05:55:02.384: 0021.5C8C.C761 aaa attribute list length is 5 1 wcm: e
with EPM session handle 3087007776
*Sep 1 05:55:02.384: 0021.5C8C.C761 Sending Activate request for session
handle 3087007776 successful 1 wcm: 6
*Sep 1 05:55:02.384: 0021.5C8C.C761 Post-auth policy request sent! Now wait
for post-auth policy ACK from EPM 1 wcm: N_IP(2) vlan 20 client_id
0x8e7bc00000004d mob=Local(1) ackflag 1 dropd 1
*Sep 1 05:55:02.384: 0021.5C8C.C761 WCDB SPI response msg handler client code
0 mob state 0 1 wcm: licy ACK from EPM
*Sep 1 05:55:02.384: 0021.5C8C.C761 WcdbClientUpdate: 1 wcm: L2 Auth ACK from
WCDB
*Sep 1 05:55:02.384: 0021.5C8C.C761 WCDB_L2ACK: 1 wcm: wcdbAckRecvdFlag
updated
*Sep 1 05:55:02.384: 0021.5C8C.C761 WCDB_CHANGE: 1 wcm: Client 1 m_vlan 20
Radio iif id 0xbfcdc00000003a bssid iif id 0xbb30c000000046, bssid
C8F9.F983.4260
*Sep 1 05:55:02.384: 0021.5C8C.C761 WCDB_AUTH: 1 wcm: Adding opt82 len 0
*Sep 1 05:55:02.384: 0021.5C8C.C761 WCDB_LLM: 1 wcm: NoRun Prev Mob 0, Curr
Mob 1 llmReq 1, return False
*Sep 1 05:55:02.385: 0021.5C8C.C761 auth state 2 mob state 1 setWme 0 wme 1
roam_sent 0 1 wcm: rn False
*Sep 1 05:55:02.385: 0021.5C8C.C761 WCDB_CHANGE: 1 wcm: auth=LEARN_IP(2) vlan
20 radio 1 client_id 0x8e7bc00000004d mobility=Local(1) src_int
0xb6818000000038 dst_int 0x0 ackflag 2 reassoc_client 0 llm_notif 0 ip
0.0.0.0 ip_learn_type UNKNOWN
*Sep 1 05:55:02.385: EPM: 1 wcm: Init feature, client handle 8e7bc00000004d
session b8000020 authz ec00000e
*Sep 1 05:55:02.385: EPM: 1 wcm: Activate feature client handle
8e7bc00000004d sess b8000020 authz ec00000e
*Sep 1 05:55:02.385: PEM recv processing msg Epm spi response(12) 1 wcm: 004d
sess b8000020 authz ec00000e
*Sep 1 05:55:02.385: 0021.5C8C.C761 Received activate_features_resp for client
handle 40105511256850509 1 wcm: 004d mobility=Local(1) src_int
0xb6818000000038 dst_int 0x0 ackflag 2 reassoc_client 0 llm_notif 0
ip$=6v0.0.0 ipt^_Dv^\7HnP6v^D6Hl5Ht^_Dv$6H8^ r^D6H>&5v8^
r^D6H>&5v^D6Ht^M^Lw^\7H8^ r
*Sep 1 05:55:02.385: 0021.5C8C.C761 Received activate_features_resp for EPM
session handle 3087007776 1 wcm: 9
*Sep 1 05:55:02.385: EPM: 1 wcm: Policy enforcement - client handle
8e7bc00000004d session 2800000e authz ec00000e
*Sep 1 05:55:02.385: EPM: 1 wcm: Netflow policy enforcement - client handle
8e7bc00000004d sess 2800000e authz ec00000e msg_type 0 policy_status 0 attr
len 0
*Sep 1 05:55:02.385: PEM recv processing msg Epm spi response(12) 1 wcm: e
8e7bc00000004d sess 2800000e authz ec00000e msg_type 0 policy_status 0 attr
len 0
*Sep 1 05:55:02.385: 0021.5C8C.C761 Received policy_enforcement_response for
client handle 40105511256850509 1 wcm: 00e msg_type 0 policy_status 0 attr
len 0
*Sep 1 05:55:02.385: 0021.5C8C.C761 Received policy_enforcement_response for
EPM session handle 671088654 1 wcm: 09
*Sep 1 05:55:02.385: 0021.5C8C.C761 Received response for
_EPM_SPI_ACTIVATE_FEATURES request sent for client 1 wcm: 00e msg_type 0
policy_status 0 attr len 0
*Sep 1 05:55:02.385: 0021.5C8C.C761 Received _EPM_SPI_STATUS_SUCCESS for
request sent for client 1 wcm: for client
*Sep 1 05:55:02.385: 0021.5C8C.C761 Post-auth policy ACK recvd from EPM, unset
flag on MSCB 1 wcm: ient
*Sep 1 05:55:02.400: 0021.5C8C.C761 WCDB_IP_BIND: 1 wcm: w/ IPv4 20.20.20.3
ip_learn_type DHCP add_delete 1,options_length 0
*Sep 1 05:55:02.400: 0021.5C8C.C761 WcdbClientUpdate: 1 wcm: IP Binding from
WCDB ip_learn_type 1, add_or_delete 1
*Sep 1 05:55:02.400: 0021.5C8C.C761 IPv4 Addr: 1 wcm: 20:20:20:3
*Sep 1 05:55:02.400: 0021.5C8C.C761 MS got the IP, resetting the Reassociation
Count 0 for client 1 wcm: _delete 1
*Sep 1 05:55:02.400: 0021.5C8C.C761 20.20.20.3 DHCP_REQD (7) Change state to
RUN (20) last state RUN (20) 1 wcm: length 0
*Sep 1 05:55:02.400: 0021.5C8C.C761 WCDB_CHANGE: 1 wcm: Client 1 m_vlan 20
Radio iif id 0xbfcdc00000003a bssid iif id 0xbb30c000000046, bssid
C8F9.F983.4260
*Sep 1 05:55:02.400: 0021.5C8C.C761 WCDB_AUTH: 1 wcm: Adding opt82 len 0
*Sep 1 05:55:02.401: 0021.5C8C.C761 WCDB_LLM: 1 wcm: prev Mob state 1 curr
Mob State 1 llReq flag 0
*Sep 1 05:55:02.401: 0021.5C8C.C761 auth state 4 mob state 1 setWme 0 wme 1
roam_sent 0 1 wcm: g 0
*Sep 1 05:55:02.401: 0021.5C8C.C761 WCDB_CHANGE: 1 wcm: auth=RUN(4) vlan 20
radio 1 client_id 0x8e7bc00000004d mobility=Local(1) src_int
0xb6818000000038 dst_int 0x0 ackflag 2 reassoc_client 0 llm_notif 0 ip
20.20.20.3 ip_learn_type DHCP
*Sep 1 05:55:02.401: 0021.5C8C.C761 20.20.20.3 RUN (20) Reached
PLUMBFASTPATH: 1 wcm: from line 4430
*Sep 1 05:55:02.401: 0021.5C8C.C761 20.20.20.3 RUN (20) Replacing Fast Path
rule on AP C8F9.F983.4260 , slot 1 802.1P = 0
1 wcm: 0xb6818000000038 dst_int 0x0 ackflag 2 reassoc_client 0 llm_notif 0 ip
20.$=6v0.3 ip_lt^_Dv^\7HnP6v^D6Hl5Ht^_Dv$6H8^ r^D6H>&5v8^
r^D6H>&5v^D6Ht^M^Lw^\7H8^ r
*Sep 1 05:55:02.401: 0021.5C8C.C761 20.20.20.3 RUN (20) Successfully plumbed
mobile rule 1 wcm: C8F9.F983.4260 , slot 1 802.1P = 0^M
*Sep 1 05:55:02.401: 0021.5C8C.C761
Sending IPv4 update to Controller 10.105.135.176 1 wcm: e
*Sep 1 05:55:02.401: 0021.5C8C.C761 Assigning Address 20.20.20.3 to mobile 1
wcm: 05.135.176
*Sep 1 05:55:02.401: PEM recv processing msg Add SCB(3) 1 wcm: 20.20.3 to
mobile
*Sep 1 05:55:02.401: 0021.5C8C.C761 20.20.20.3, auth_state 20 mmRole Local !!!
1 wcm: 135.176
*Sep 1 05:55:02.401: 0021.5C8C.C761 20.20.20.3, auth_state 20 mmRole Local,
updating wcdb not needed 1 wcm: 3.4260 , slot 1 802.1P = 0^M
*Sep 1 05:55:02.401: 0021.5C8C.C761 Tclas Plumb needed: 1 wcm: 0
*Sep 1 05:55:20.083: 0021.5C8C.C761
Client stats update: 1 wcm: Time now in sec 1378014920, Last Acct Msg Sent at
1378014902 sec
 Feedback
Feedback