- Auto Anchor SSID between Wireless LAN Controllers acting as MC
- Enabling Central Web Authentication on ISE
- Configuring Auto Anchor and Mobility Groups on Wireless Services
- Configuring Wireless Multicast on Wireless LAN Controllers
- Converged Access Consolidated Quick Reference Templates for Wireless LAN
- Converged Access Controller AP Join Issue Troubleshoot with Traces
- Converged Access Controllers MAC Address Entry for Network Mobility Service Protocol
- Configuration Example: Converged Access Management through Prime Infrastructure with SNMP v2 and v3
- Converged Access Path Maximum Transmission Unit Discovery
- Third-Party Certificate Installation on Converged Access Wireless LAN Controllers
- Configuration Example: Converged Access for WLC EAP-FAST with Internal RADIUS Server
- Converged Access and WLC Local EAP Authentication Configuration Example
- Configuration Example: Custom Web Authentication with Local Authentication
- Dynamic VLAN Assignment with Converged Access and ACS 5.2 Configuration Example
- Configuration Example: External RADIUS Server EAP Authentication
- External Web Authentication on Converged Access
- Installing Wireless Services
- Local Web Authentication with External RADIUS Authentication
- Local Web Authentication on Converged Access
- PEAP Authentication with Microsoft NPS Configuration
- QoS on Converged Access Controllers and Lightweight Access Points
- Configuration Example: TACACS Administrator Access to Converged Access Wireless LAN Controllers
- Configuration Example: Unified Access WLC Guest Anchor with Converged Access
- VideoStream Troubleshooting
- Custom Web Authentication Locally Hosted on WLC or an External Server
- Wireless Converged Access Chromecast Configuration Example
- Web Passthrough Configuration Example
- Configuration Examples: WPA2-PSK and Open Authentication
Enabling Central Web Authentication on ISE
The document describes the procedure to enable Central Web Authentication (CWA) on Identity Services Engine (ISE).
- Enabling CWA on ISE through Global Configuration Commands
- Enabling External Policy Server using Dynamic Authorization Commands
- Configuring WLAN Commands
- Authentication Flow on ISE
Enabling CWA on ISE through Global Configuration Commands
Use the following commands to enable CWA on ISE to work with Converged Access controllers:
|
Command or Action |
Description/Purpose/Example |
|
show run aaa |
Displays the Authorization, Authentication, and Accounting (AAA) related configurations. |
|
aaa authentication login ext_ise group rad_ise |
Defines the 'exe ise' login method list which points to the ISE server 'rad_ise'. |
|
aaa authorization network cwa_mac group rad_ise |
The authorization method 'cwa_mac' is the mac filter list name which is called under the WLAN configuration. It points to the ISE server 'rad_ise' for authorization. |
|
radius server ise address ipv4 192.0.2.1 auth-port 1812 acct-port 1813 key Cisco123 |
Displays the RADIUS server definition for the 'ise' server. |
|
aaa group server radius rad_ise server name ise |
The 'rad_ise' AAA group server points to the server 'ise'. |
|
aaa server radius dynamic-author client 192.0.2.1 server-key Cisco123 auth-type any |
Required for Change of Authorization (CoA). For more information on CoA, refer to Dynamic Authorization Commands. |
Enabling External Policy Server using Dynamic Authorization Commands
Use the following dynamic authorization commands to enable an external policy server to dynamically send updates to a device:
| Command or Action | Description/Purpose/Example |
|
radius-server attribute 31 send nas -port-detail mac-only Or, radius-server attribute 31 send nas-port-detail |
Sends the calling station ID for MAC.
Sends calling station ID for all operating systems other than MAC. |
|
ip access-list extended ACL-REDIRECT |
This is a url-redirect-acl. To redirect the guest portal, the Identity Services Engine (ISE) returns an AAA override and the redirect URL. The url-redirect-acl is a punt ACL which is a reverse ACL that is used for unified architecture. You need to block access to DHCP, DHCP Server, DNS, DNS server, and ISE server and allow www, 443 port, or the 8443 port as required. The ISE guest portal uses port 8443 and the redirection works with the following ACL: 10 deny udp any eq bootps any 20 deny udp any any eq bootpc 30 deny udp any eq bootpc any 40 deny ip any host 192.0.2.1 50 deny ip any host 192.0.2.2 60 permit tcp any any eq www |
|
mac access-list extended cwa_mac permit anyany |
The access list is defined based on the MAC Authentication Bypass (MAB) rule. |
Related Commands
The following table displays the commands that are associated with dynamic authorization:
|
Command or Action |
Description/Purpose/Example |
|
auth-type (ISO) |
Specifies the server authorization type. |
|
Client |
Specifies a RADIUS client from which a device accepts CoA and disconnects requests. |
|
Default |
Sets the RADIUS application command to default domain and then specifies the username domain options. |
|
Ignore |
Overrides a behavior to ignore the parameters that are specified. |
|
Port |
Specifies a port on which local RADIUS server listens to. |
|
server-key |
Specifies the encryption key shared with the RADIUS clients. |
Configuring WLAN Commands
The following example describes the WLAN configuration:
wlan cwa_guest 11 cwa_guest aaa-override client vlan 263 mac-filtering cwa_mac ----> mac filter pointing to authorization on ISE server nac no security wpa no security wpa akm dot1x no security wpa wpa2 no security wpa wpa2 ciphers aes no shutdown
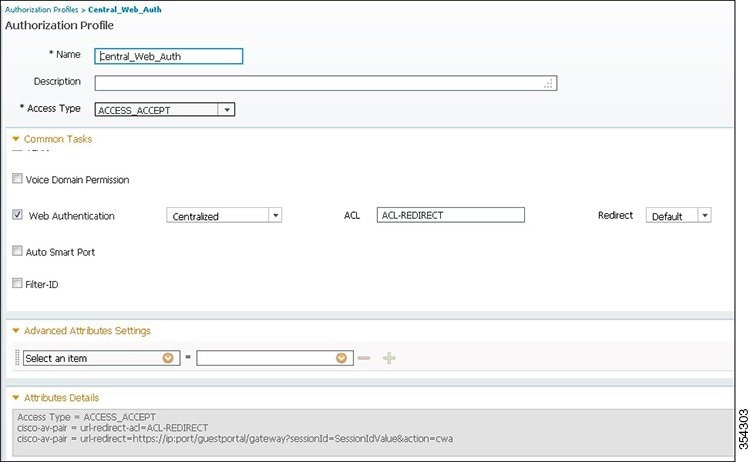
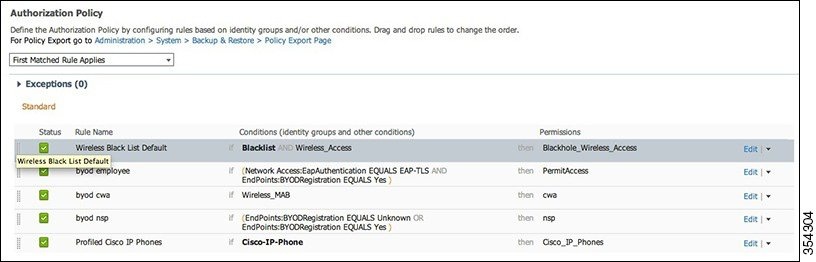
Authentication Flow on ISE
The ISE logs shown in the following figure displays the authentication flow on the ISE:
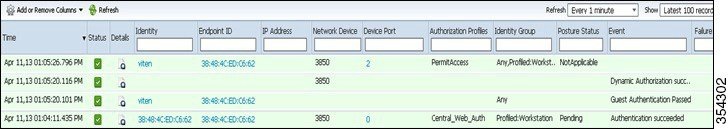
For more information, refer to the 'Information About Mobility' chapter in the Cisco Wireless LAN Controller Configuration Guide, Release 7.4.

 Feedback
Feedback