Application hosting environments
An application hosting environment is a platform that
-
allows Linux applications to manage communication with IOS XR interfaces,
-
establishes packet I/O communication channels with hosted applications, and
-
enables integration of third-party tools, utilities, and operational workflows.
Need for Application Hosting
Over the last decade, there has been a need for a network operating system that supports operational agility and efficiency through seamless integration with existing tool chains. Service providers have been looking for shorter product cycles, agile workflows, and modular software delivery; all of these can be automated efficiently. It does that by providing an environment that simplifies the integration of applications, configuration management tools, and industry-standard zero touch provisioning mechanisms. The IOS XR matches the DevOps style workflows for service providers, and it has an open internal data storage system that can be used to automate the configuration and operation of the device hosting an application.
While we are rapidly moving to virtual environments, there is an increasing need to build applications that are reusable, portable, and scalable. Application hosting gives administrators a platform for leveraging their own tools and utilities. Cisco NCS 540 routers support third-party off-the-shelf applications. An application hosted on a network device can serve a variety of purposes. This ranges from automation, configuration management monitoring, and integration with existing tool chains.
Before an application can be hosted on a device, the following requirements must be met:
-
Suitable build environment to build your application
-
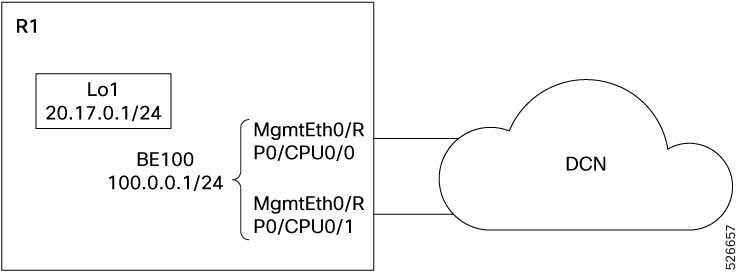
A mechanism to interact with the device and the network outside the device
When network devices are managed by configuration management applications, network administrators are freed of the task of focusing only on the CLI. Because of the abstraction provided by the application, while the application does its job, administrators can now focus on the design, and other higher level tasks.

 Feedback
Feedback