Configure SNMP using CLI
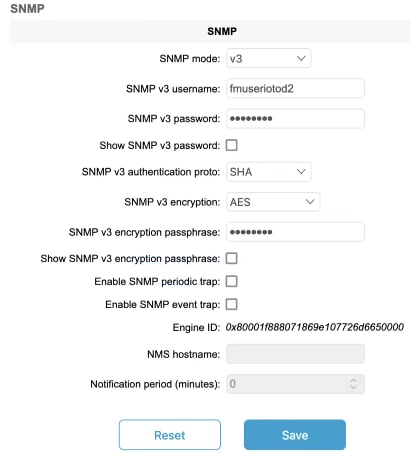
URWB software for network management functionalities uses SNMP applications. The SNMP implementation supports queries (solicited) and traps (unsolicited). If you enable SNMP traps, specify the server address to which the monitoring information is sent.
 Note |
The same SNMP configuration must be set for all gateways in the network. |
Before you begin
All parameters of SNMP are required to be configured before enabling SNMP feature using the snmp enabled command.
Procedure
|
Step 1 |
Configure the SNMP v2 parameters using these commands: |
|
Step 2 |
Configure the SNMP v3 parameters using these commands: |




 Feedback
Feedback