Our security architecture comprises multiple, layered security options and controls. You can deploy these security features
to meet your individual security requirements. You can combine these features to achieve a robust security posture against
attacks.
The contact center enterprise solutions include some servers that run on a Windows OS and others that run on the Linux-based
Cisco Voice OS (VOS). The security architecture leverages the resources of the OS on which a particular server runs.
On a Windows OS, the Unified CCE servers leverage the Windows Firewall, Windows NT LAN Manager version 2 (NTLMv2), Windows
Hardening Policies, and Active Directory. These servers include:
The Cisco VOS platform is a closed, appliance-based model which runs within a Linux (shell) OS architecture. The servers that
run on VOS include:
-
Cisco Finesse
-
Cisco Unified Intelligence Center
-
Virtual Voice Browser
-
Unified Communications Manager
-
Cisco Unity Connection
-
Cisco Identity Service
-
Live Data
-
Customer Collaboration Platform
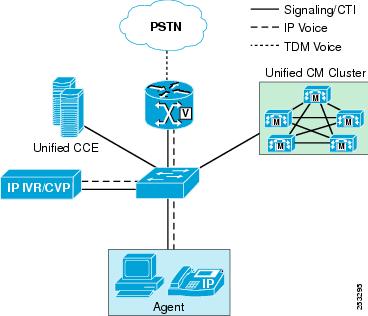
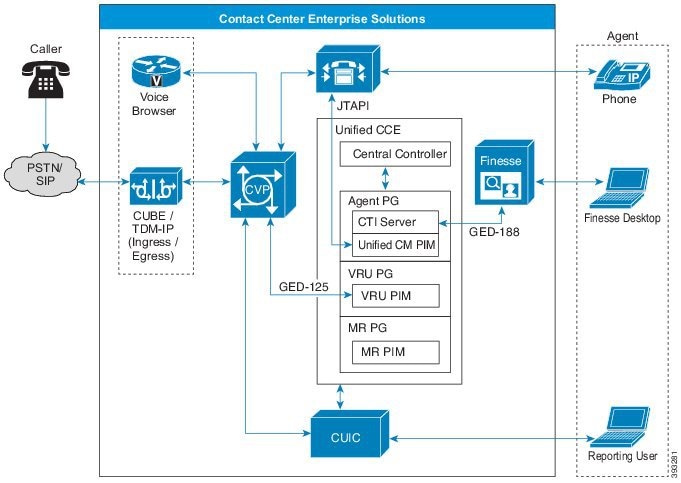
This figure shows the core elements of a Unified CCE instance:
Application endpoints, like desktops and phones, involve Computer Telephony Interface (CTI), JTAPI, and any TAPI applications.
These endpoints are secured by leveraging TLS and SRTP. The solution also uses a Certificate Trust List (CTL) which you create
that establishes signaling authentication between Client and Server.
Network Security Architecture
The contact center enterprise solution offers a flexible network security model. There are many areas on the network where,
based on your unique needs and compliance requirements, you can apply security to the solution. These include Firewalls, Access
Control Lists (ACLs), private network addressing, Network Address Translation (NAT), setting up a DMZ, SRTP, and Internet
Protocol Security (IPsec).
You can secure in-flight data by deploying IPsec. IPsec is an Internet layer 3 framework of open standards that are designed
to ensure private, secure communications over Internet Protocol (IP) networks. The use of cryptographic security services
and policies provides security. IPsec helps defend against:
-
Network-based attacks from untrusted computers that can result in the denial-of-service of applications, services, or the
network
-
Data corruption
-
Data theft
-
User-credential theft
-
Network security attacks (IP Spoofing, DNS hijacking) against critical servers, other computers, and the network
You can deploy IPsec in two modes in your contact center enterprise solution. LAN or WAN network endpoints support either
transport mode or tunnel mode deployments. Contact Center nodes (such as Peripheral Gateways, Routers, and Loggers) support
only transport mode IPsec.
You secure voice traffic in your solution by applying encryption directly to the Real-Time Transport Protocol (RTP) which
delivers audio and video streaming. RTP streams do not terminate within the core contact center enterprise solution. Adjunct
devices, such as Unified CM and voice gateways, supply the media termination within the solution.
Secure Real-Time Transport Protocol (SRTP) is the method that secures the voice and video traffic.
Unified CCE web servers use Microsoft Internet Information Services (IIS) for web server responses and Apache Tomcat for the
client authentication. Communication between Web servers and web-based users is trusted and encrypted using HTTPS and Transport
Layer Security (TLS) protocols.
The servers that make up the contact center enterprise solution reside in a protected data center. They are not typically
exposed to open internet traffic. These servers sit behind a firewall or DMZ. The only exceptions are Microsoft Active Directory
Domain Controllers, Customer Collaboration Platform servers, and the Email and Chat web servers which reside inside a DMZ.
This guide focuses primarily on the premises-based deployment of our solutions. Cisco also offers cloud-based contact center
applications, such as the Customer Journey Platform. We are thorough in ensuring compliance with international standards
requirements for cloud data handling. Cisco has completed Binding Corporate Rules with the EU, the EU-US Privacy Shield, and
the APEC agreements for cloud data handling and cross-border transfers. The Cisco Trust Center website provides details of
these protections: https://www.cisco.com/c/en/us/about/trust-center.html.


 Feedback
Feedback