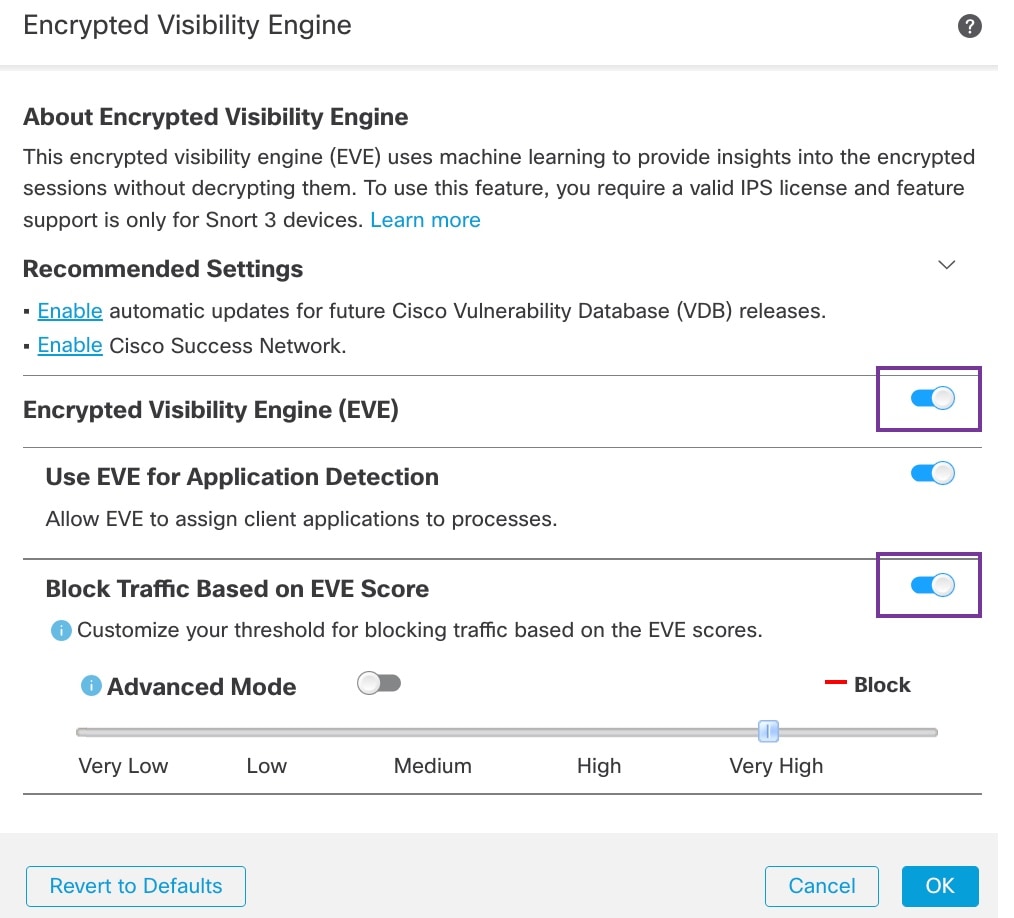
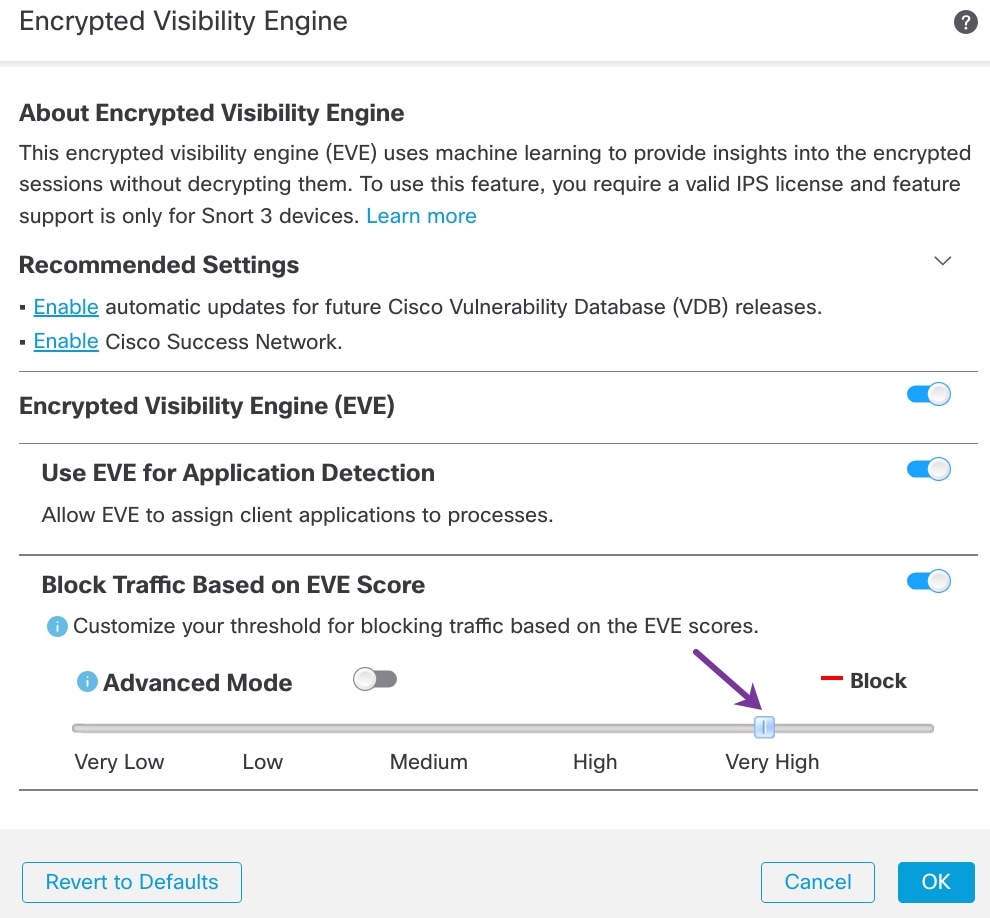
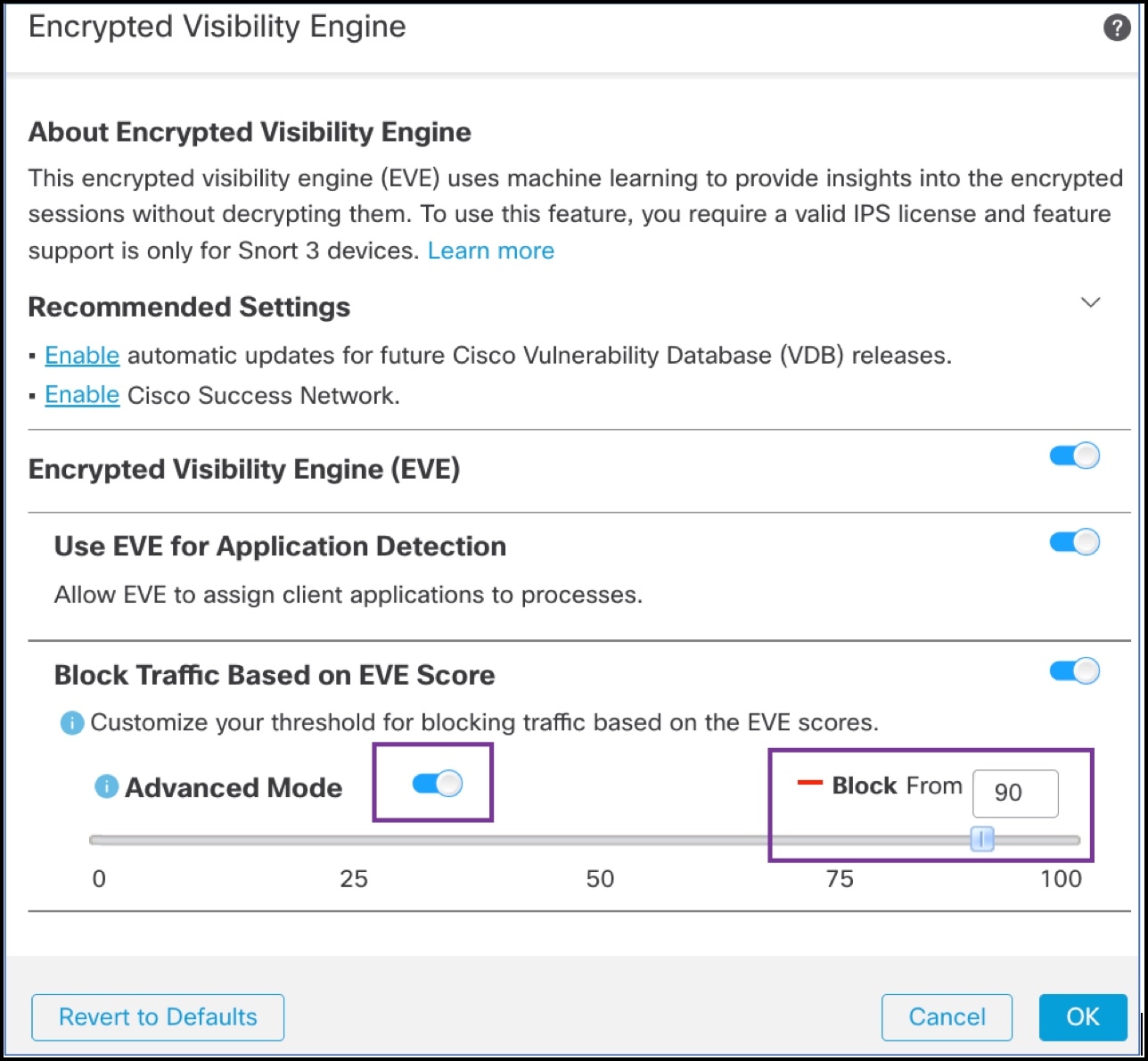
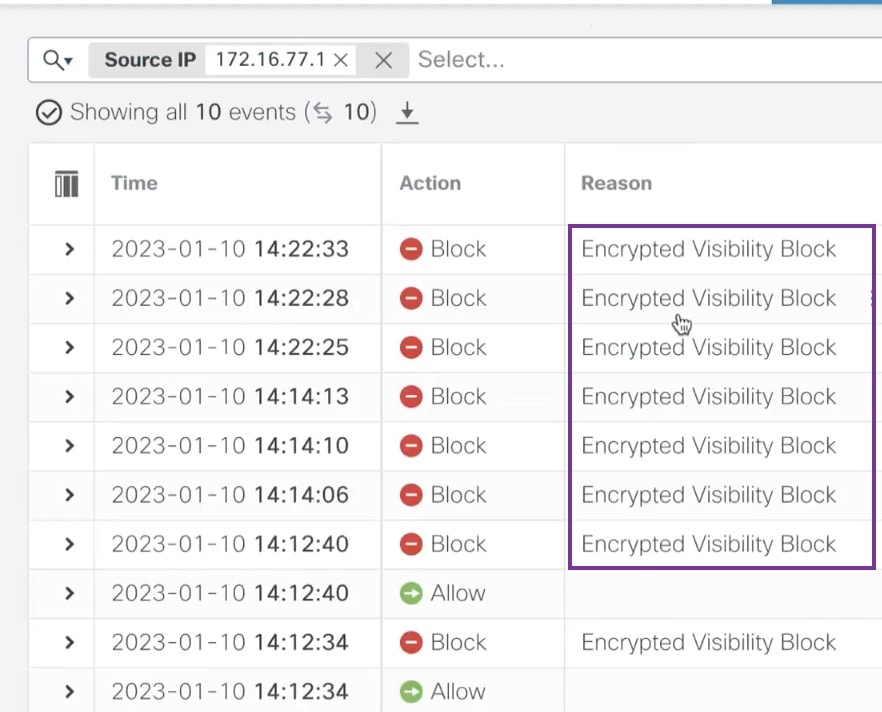
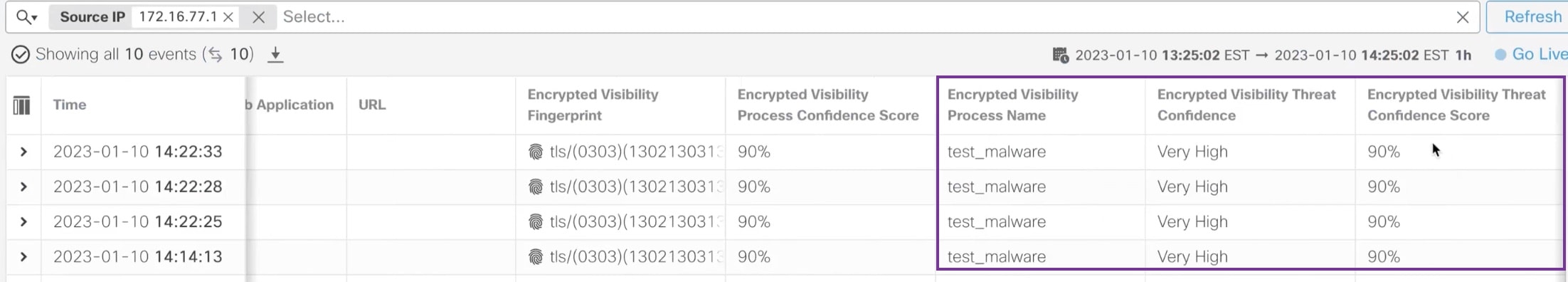
Overview of Encrypted Visibility Engine
The encrypted visibility engine (EVE) is used to provide more visibility into the encrypted sessions without the need to decrypt them. These insights into encrypted sessions are obtained by Cisco's open-source library that is packaged in Cisco's vulnerability database (VDB). The library fingerprints and analyzes incoming encrypted sessions and matches it against a set of known fingerprints. This database of known fingerprints is also available in the Cisco VDB.
 Note |
The encrypted visibility engine feature is supported only on Firewall Management Center-managed devices running Snort 3. This feature is not supported on Snort 2 devices and Firewall Device Manager-managed devices. |
Some of the important features of EVE are the following:
-
You can take access control policy actions on the traffic using information derived from EVE.
-
The VDB included in Cisco Secure Firewall has the ability to assign applications to some processes detected by EVE with a high confidence value. Alternatively, you can create custom application detectors to:
-
Map EVE-detected processes to new user-defined applications.
-
Override the built-in value of process confidence that is used to assign applications to EVE-detected processes.
See the Configuring Custom Application Detectors and Specifying EVE Process Assignments sections in the Application Detection chapter of the Cisco Secure Firewall Management Center Device Configuration Guide.
-
-
EVE can detect the operating system type and version of the client that created a Client Hello packet in the encrypted traffic.
-
EVE supports fingerprinting and analysis of Quick UDP Internet Connections (QUIC) traffic too. The server name from the Client Hello packet is displayed in the URL field of the Connection Events page.
 Attention |
To use EVE on Firewall Management Center, you must have a valid Threat license on your device. In the absence of a Threat license, the policy displays a warning and deployment is not allowed. |
 Note |
|


 Feedback
Feedback