Cisco ISE network architecture
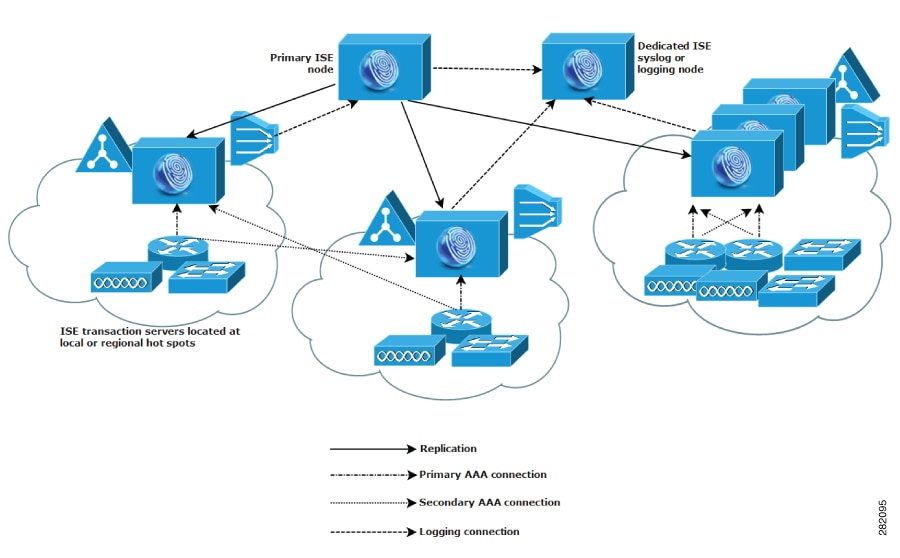
Cisco ISE network architecture integrates specialized nodes and deployment models to deliver comprehensive, scalable network access control and security policy enforcement.
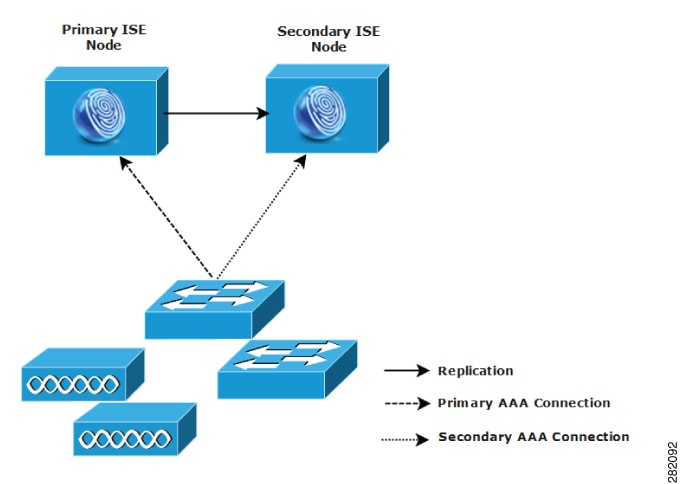
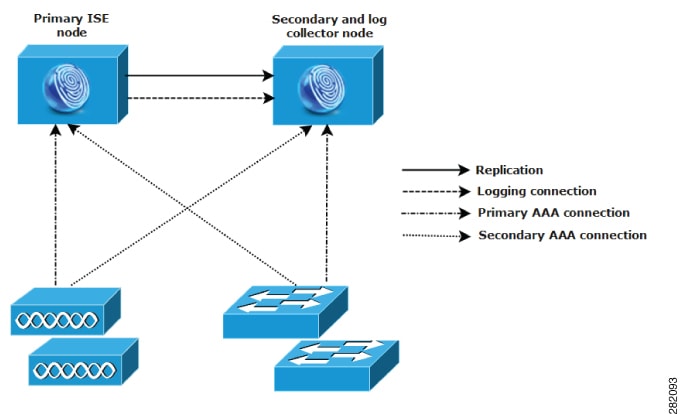
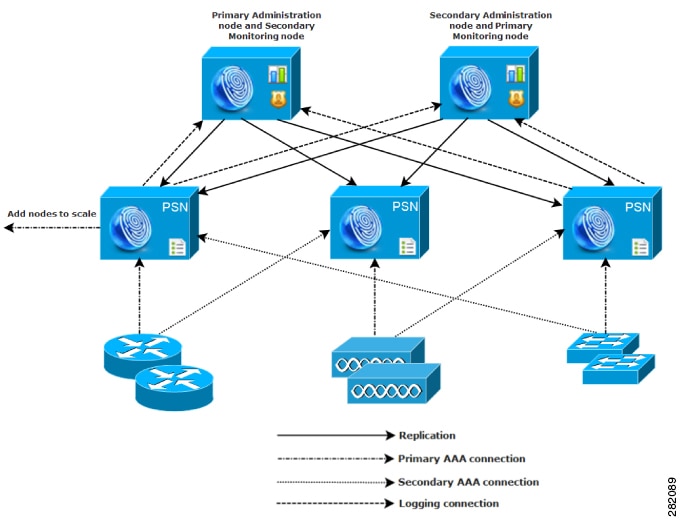
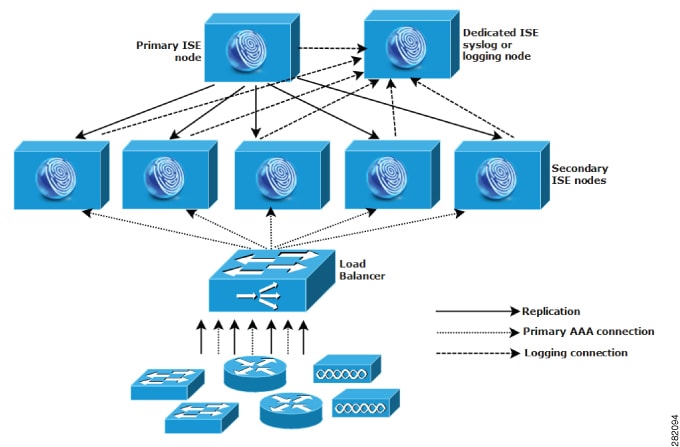
The core components include nodes with specific personas that work together to manage network access and security. It supports various deployment models, including standalone and distributed setups, suited for small to large networks. This architecture ensures scalable, secure, and efficient policy enforcement across wired, wireless, and VPN connections.
Cisco ISE network architecture components
Cisco ISE architecture includes these components:
|
Cisco ISE network components |
Description |
|---|---|
|
Nodes (personas or roles) |
Cisco ISE servers that run one or more roles. A node can run multiple personas. |
|
Network resources |
Infrastructure that controls or provides network access, such as switches, WLCs, VPN devices and so on. |
|
Endpoints |
Users or devices trying to connect to the network, such as laptops, phones, printers, IoTand so on. |
Cisco ISE nodes and personas
A Cisco ISE node can assume any or all of these personas:
| Persona | Role | Use cases |
|---|---|---|
| Administration persona | Manages configuration and system settings | Primary or secondary admin nodes |
| Policy Service persona (PSN) | Makes access-control decisions and enforces policy
The policy information point (PIP) is where external information is communicated to the Policy Service persona. For example, external information might be a Lightweight Directory Access Protocol (LDAP) attribute. |
RADIUS and TACACS+ processing |
| Monitoring persona | Collects logs and reporting data | Troubleshooting, audits, reports |
| pxGrid persona | Shares context with other systems | Integrations with security tools |

 Feedback
Feedback