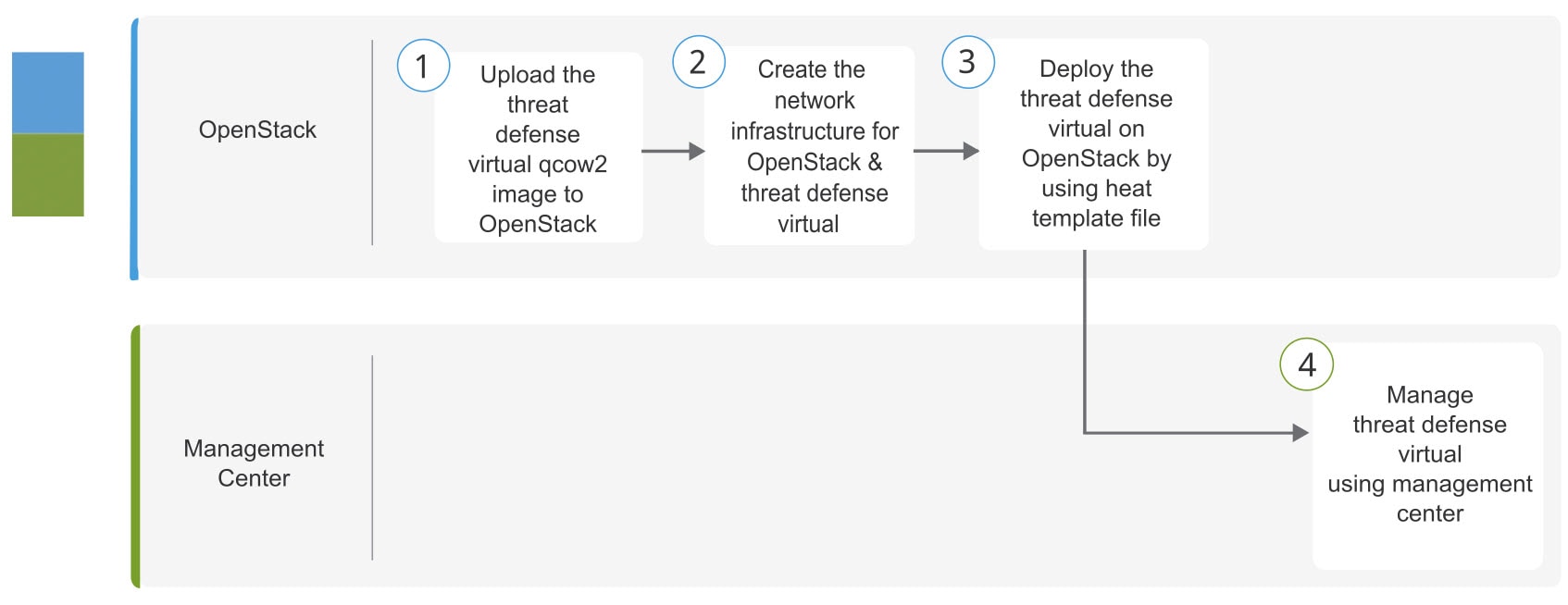
Overview
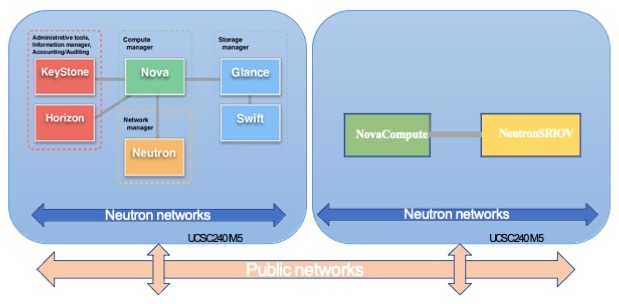
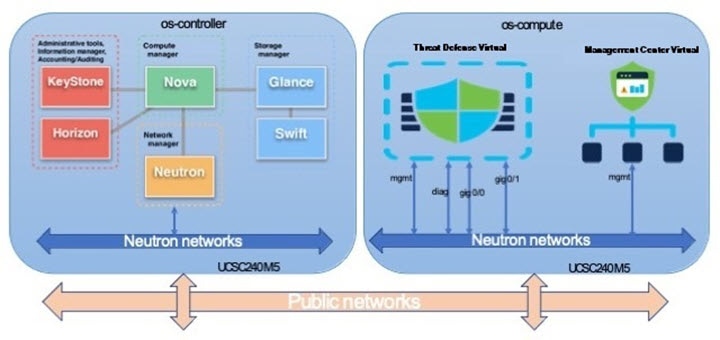
This guide describes how to deploy the Firewall Threat Defense Virtual in an OpenStack environment. OpenStack is a free open standard cloud computing platform, mostly deployed as infrastructure-as-a-service (IaaS) in both public and private clouds where virtual servers and other resources are made available to users.
This deployment uses a KVM hypervisor to manage virtual resources. KVM is a full virtualization solution for Linux on x86 hardware containing virtualization extensions (such as Intel VT). It consists of a loadable kernel module, kvm.ko, that provides the core virtualization infrastructure and a processor specific module, such as kvm-intel.ko.
You can run multiple virtual machines running unmodified OS images using KVM. Each virtual machine has private virtualized hardware: a network card, disk, graphics adapter, and so forth.
Because devices are already supported on the KVM hypervisor, no additional kernel packages or drivers are needed to enable OpenStack support.
 Note |
Firewall Threat Defense Virtual on OpenStack can be installed on any optimized multi-node environment. |

 Feedback
Feedback