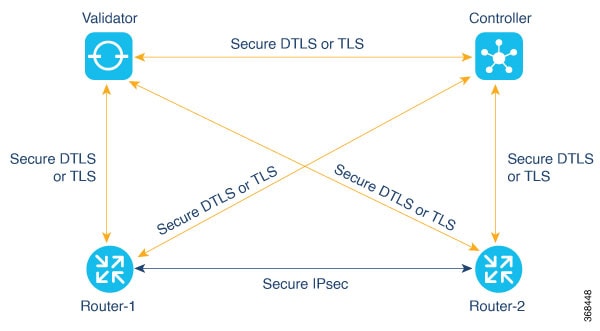
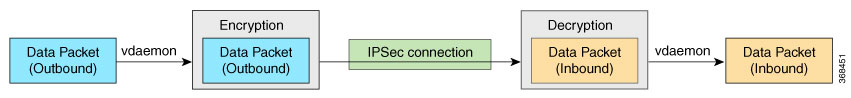
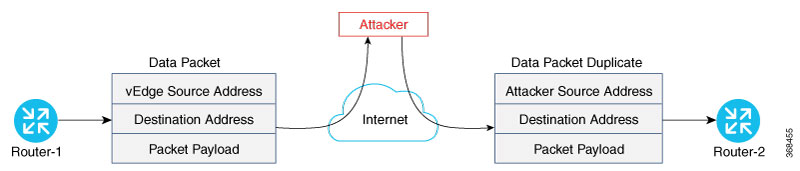
During the bringup of the overlay, the Cisco Catalyst SD-WAN Controller establishes the information for edge routers to send data to each other. However before a pair of routers can exchange data
traffic, they establish an IPsec connection between them, which they use as a secure communications channel. Since the Cisco Catalyst SD-WAN Controller has authenticated the devices, the devices do not further authenticate each other.
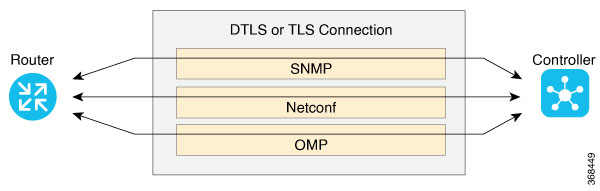
Control plane communications have allowed the edge device to have enough information to establish IPsec tunnels. Edge devices
simply send data through the tunnels. There is no additional authentication step.
In a traditional IPsec environment, key exchange is handled by the Internet Key Exchange (IKE) protocol. IKE first sets up
secure communications channels between devices and then establishes security associations (SAs) between each pair of devices
that want to exchange data. IKE uses a Diffie-Hellman key exchange algorithm to generate a shared key that encrypts further
IKE communication. To establish SAs, each device (n) exchanges keys with every other device in the network and creates per-pair
keys, generating a unique key for each remote device. This scheme means that in a fully meshed network, each device has to
manage n2 key exchanges and (n-1) keys. As an example, in a 1,000-node network, 1,000,000 key exchanges are required to authenticate
the devices, and each node is responsible for maintaining and managing 999 keys.
The discussion in the previous paragraph points out why an IKE-style key exchange does not scale as network size increases
and why IKE could be a bottleneck in starting and in maintaining data exchange on a large network:
-
The handshaking required to set up the communications channels is both time consuming and resource intensive.
-
The processing required for the key exchange, especially in larger networks, can strain network resources and can take a long
time.
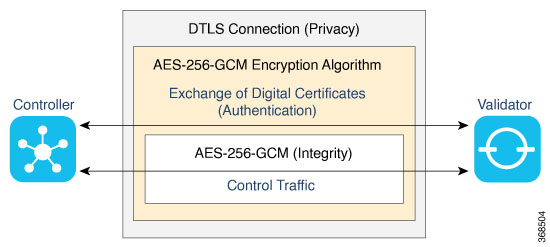
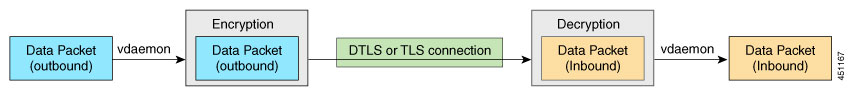
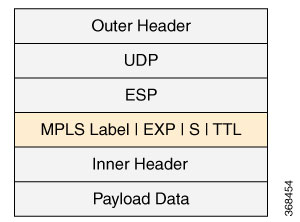
The Cisco Catalyst SD-WAN implementation of data plane authentication and encryption establishes SAs between each pair of devices that want to exchange
data, but it dispenses with IKE altogether. Instead, to provide a scalable solution to data plane key exchange, the Cisco Catalyst SD-WAN solution takes advantage of the fact that the DTLS control plane connections in the Cisco Catalyst SD-WAN overlay network are known to be secure. Because the Cisco Catalyst SD-WAN control plane establishes authenticated, encrypted, and tamperproof connections, there is no need in the data plane to set
up secure communications channels to perform data plane authentication.
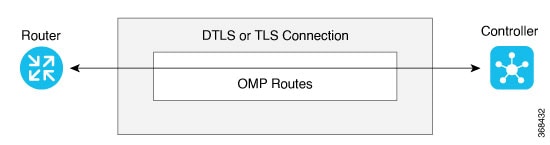
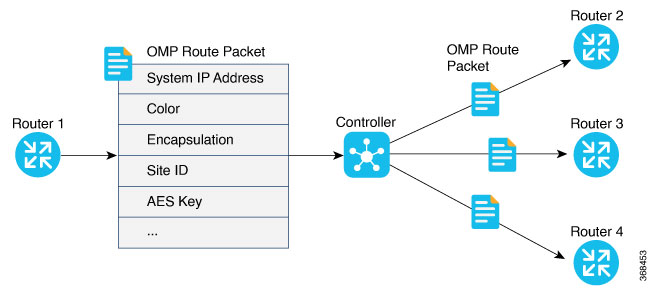
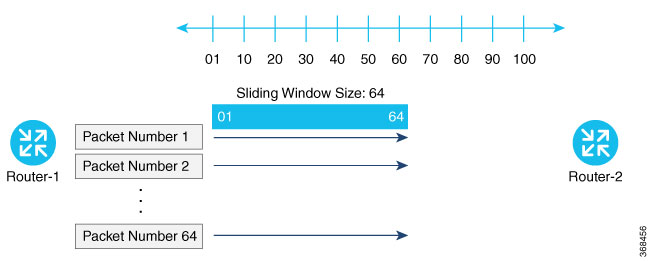
In the Cisco Catalyst SD-WAN network for unicast traffic, data plane encryption is done by AES-256-GCM, a symmetric-key algorithm that uses the same key
to encrypt outgoing packets and to decrypt incoming packets. Each router periodically generates an AES key for its data path
(specifically, one key per TLOC) and transmits this key to the Cisco SD-WAN Controller in OMP route packets, which are similar to IP route updates. These packets contain information that the Cisco SD-WAN Controller uses to determine the network topology, including the router's TLOC (a tuple of the system IP address and traffic color)
and AES key. The Cisco SD-WAN Controller then places these OMP route packets into reachability advertisements that it sends to the other routers in the network. In
this way, the AES keys for all the routers are distributed across the network. Even though the key exchange is symmetric,
the routers use it in an asymmetric fashion. The result is a simple and scalable key exchange process that uses the Cisco Catalyst SD-WAN Controller.
In Cisco SD-WAN Release 19.2.x and Cisco IOS XE SD-WAN Release 16.12.x onwards, Cisco Catalyst SD-WAN supports IPSec pairwise keys that provide additional security. When IPSec pairwise keys are used, the edge router generates
public and private Diffie-Hellman components and sends the public value to the Cisco SD-WAN Controller for distribution to all other edge devices. For more information, see IPsec Pairwise Keys
If control policies configured on a Cisco SD-WAN Controller limit the communications channels between network devices, the reachability advertisements sent by the Cisco SD-WAN Controller contain information only for the routers that they are allowed to exchange data with. So, a router learns the keys only for
those routers that they are allowed to communicate with.
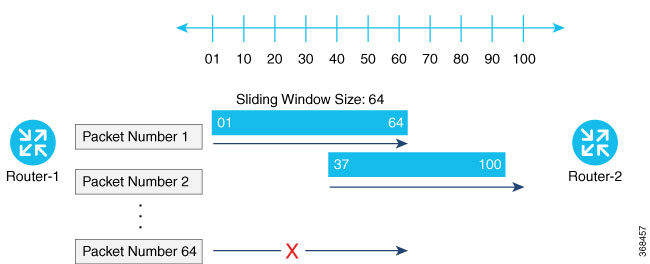
To further strengthen data plane authentication and encryption, routers regenerate their AES keys aggressively (by default,
every 24 hours). Also, the key regeneration mechanism ensures that no data traffic is dropped when keys change.
In the Cisco Catalyst SD-WAN overlay network, the liveness of SAs between router peers is tracked by monitoring BFD packets, which are periodically exchanged
over the IPsec connection between the peers. IPsec relays the connection status to the Cisco SD-WAN Controllers. If data connectivity between two peers is lost, the exchange of BFD packets stops, and from this, the Cisco SD-WAN Controller learns that the connection has been lost.
The IPsec software has no explicit SA idle timeout, which specifies the time to wait before deleting SAs associated with
inactive peers. Instead, an SA remains active as long as the IPsec connection between two routers is up, as determined by
the periodic exchange of BFD packets between them. Also, the frequency with which SA keys are regenerated obviates the need
to implement an implicit SA idle timeout.
In summary, the Cisco Catalyst SD-WAN data plane authentication offers the following improvements over IKE:
-
Because only n +1 keypaths are required rather than the n2 required by IKE, the Cisco Catalyst SD-WAN solution scales better as the network grows large.
-
Keys are generated and refreshed locally, and key exchange is performed over a secure control plane.
 Feedback
Feedback