Support for SGT Propagation with Cisco TrustSec Integration
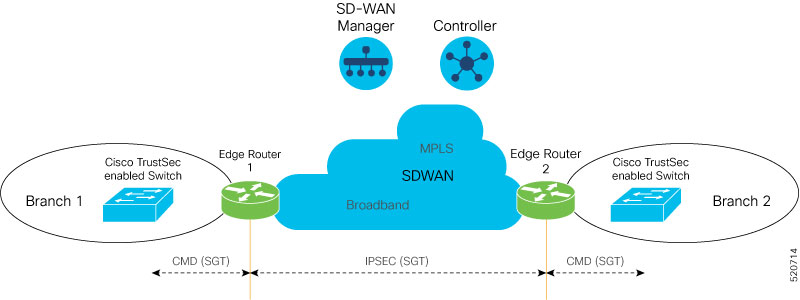
Cisco TrustSec is an end-to-end network infrastructure that provides a scalable architecture for the enforcement of role-based access control, identity-aware networking, and data confidentiality to secure the network and its resources. Cisco TrustSec uses Security Group Tag (SGT) to represent user and device groups. The switches, routers, and firewalls inspect these tags and enforce SGT-based traffic policies.
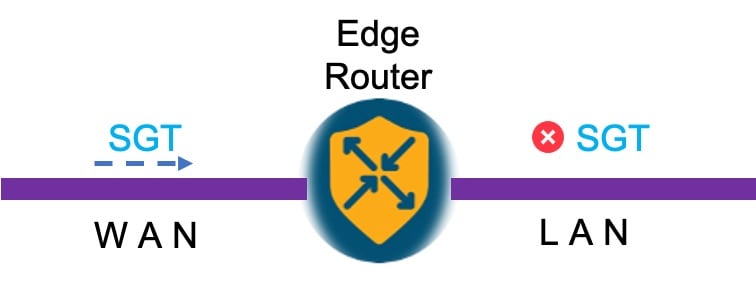
Cisco TrustSec is defined in three phases—classification, propagation, and enforcement. After traffic is classified, the SGT is propagated from where classification took place, to where enforcement action is invoked. This process is called propagation. Cisco TrustSec offers two types of SGT propagation, Inline tagging and Security Group Tag Exchange Protocol (SXP).
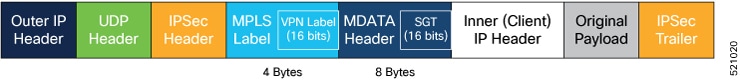
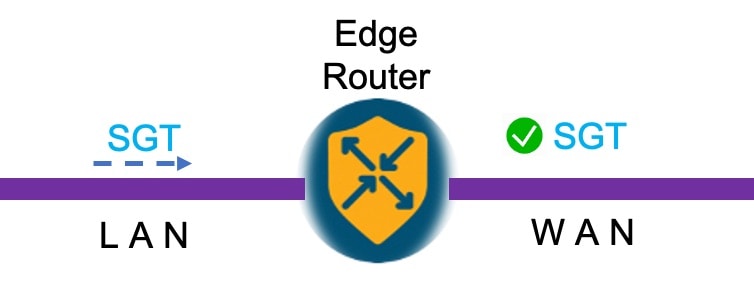
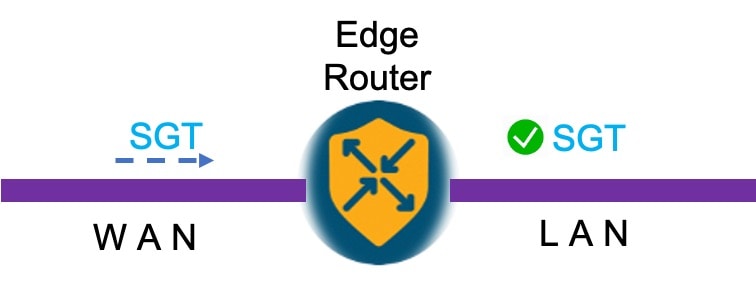
With inline tagging, a special Ethernet frame is used to propagate these SGTs between network hops where the policies are enforced based on the SGT policy. After the introduction of this feature, Cisco IOS XE Catalyst SD-WAN devices support propagation of SGT. See Configure SGT Inline Tagging Using Feature Templates
When Inline tagging is not used (or not possible), an SXP protocol can be used to dynamically exchange IP address binding to SGT between Cisco IOS XE Catalyst SD-WAN devices. You can also manually configure IP address to SGT binding, statically, in Cisco SD-WAN Manager. See SGT Propagation Using SXP
Enforcement of SGT is achieved using Security Group Access Control Lists (SGACL) where policies can be dynamically or statically configured and applied to the egress traffic on the network. See SGT Enforcement
Benefits of Cisco TrustSec
-
Provides secure access to network services and applications based on user and device identity.
-
Applies policies across the network using tags instead of IP addresses.
-
Enforces policies easily. SGT propagation simplifies network access and security operations with software-defined segmentation.
-
Scales fast and enforces policies consistently across the network. SGT propagation helps streamline security policy management across domains.
-
Reduces risk and segments devices without redesigning the network. You can easily manage access to enterprise resources and restrict lateral movement of threats with microsegmentation.

 Feedback
Feedback