Key packages
A key package is a Cryptographic Message Syntax (CMS [RFC5652]) that must be digitally signed with private keys of the customer's Ownership Certificate (OC). Key packages can be used to
-
add one or more keys to the router
-
delete one or more keys from the router, and
-
revoke one or more keys from the router.
|
Feature Name |
Release Information |
Feature Description |
|---|---|---|
|
Key package enhancements |
Release 26.1.1 |
Introduced in this release on: Fixed Systems (8200 [ASIC: Q100, Q200, P100], 8700 [ASIC: P100, K100], 8010 [ASIC: A100]); Centralized Systems (8600 [ASIC:Q200]) ; Modular Systems (8800 [LC ASIC: Q100, Q200, P100]) This feature introduces you to the version 3 key package. With the version 3 key package, you can create, validate, sign a key package before the key package is provisioned on the router. Unlike the reserved customer consent token name, CUS-CT, used in version 1 and version 2 key packages, you can now use any name for the customer consent token that you include in the key package. However, to enable the customer consent token workflow, execute the consent-token customer command after the key package installation. |
A key package provides a secure mechanism to install owner or third-party public keys (GPG or X.509) on the router.
Key package versions and IOS XR releases
You can create key packages using the GitHub script for different key package versions. These key packages can be installed on the router based on the supported IOS XR releases.
|
Key package version |
IOS XR release |
Purpose |
|---|---|---|
|
Cisco IOS XR Release 7.6.x, Cisco IOS XR Release 7.7.x |
With key-pkg-ver1, you can perform the following operations:
The key request in the key package supports ADD, DELETE, or REVOKE action. |
|
|
Cisco IOS XR Release 7.8.x – Cisco IOS XR Release 25.4.x |
With key-pkg-ver2, you can perform the following operations:
The key request in the key package supports ADD, DELETE, or REVOKE action. |
|
|
Cisco IOS XR Release 26.1.1 and later |
With key-pkg-ver3, you can perform the following operations:
Key requests do not include action (add, delete, revoke). |
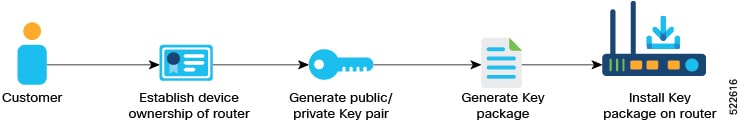
Prerequisites for key packages
Ensure that the following prerequisites are met before installing key packages on the router:
-
Device ownership should be established.
-
The router must be up and running.
-
Any uncommitted install operations should not be in progress.
Restrictions for key packages
-
Key packages to add, remove, revoke or unrevoke customer or Cisco keys must have a timestamp.
-
Key packages must be processed based on the timestamp order. Key packages with a timestamp earlier than that of a processed key package are rejected.
-
A key package to remove a key fails if there are any installed packages signed with this key.
 Feedback
Feedback