Provisioning Cisco-signed consent tokens
Summary
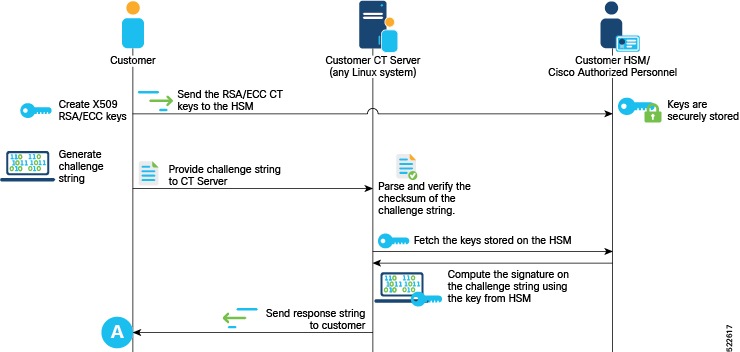
Consent tokens use a challenge-response process. The challenge string generated on the router is valid for a defined time interval. The response string for this challenge must be provided within this time interval to authenticate the user to perform the restricted action.
If you use Cisco's consent token workflow, you need to contact Cisco TAC for every request to enable or disable certain privileged operations.
Workflow
These are the stages used in provisioning a Cisco-signed consent token:
-
Generate the challenge string on the router.
This produces a challenge string containing the device ID, a nonce, and the requested action. Here, <feature> can be any supported security feature, namely, secure-ztp, lawful-intercept, factory-reset, and so on.Router# request consent-token generate-challenge <feature> - Submit the challenge string to a Cisco TAC engineer. Cisco verifies that the requester is the legitimate device owner and is authorized to perform the requested action. If verified, the TAC engineer provides a signed response string.
-
Paste the response string provided by the TAC engineer when prompted, to install the signed response on the router.
The router validates the signature and confirms that the device ID and nonce match its own records. If valid, the requested feature is enabled or disabled.Router# request consent-token accept-response
 Feedback
Feedback