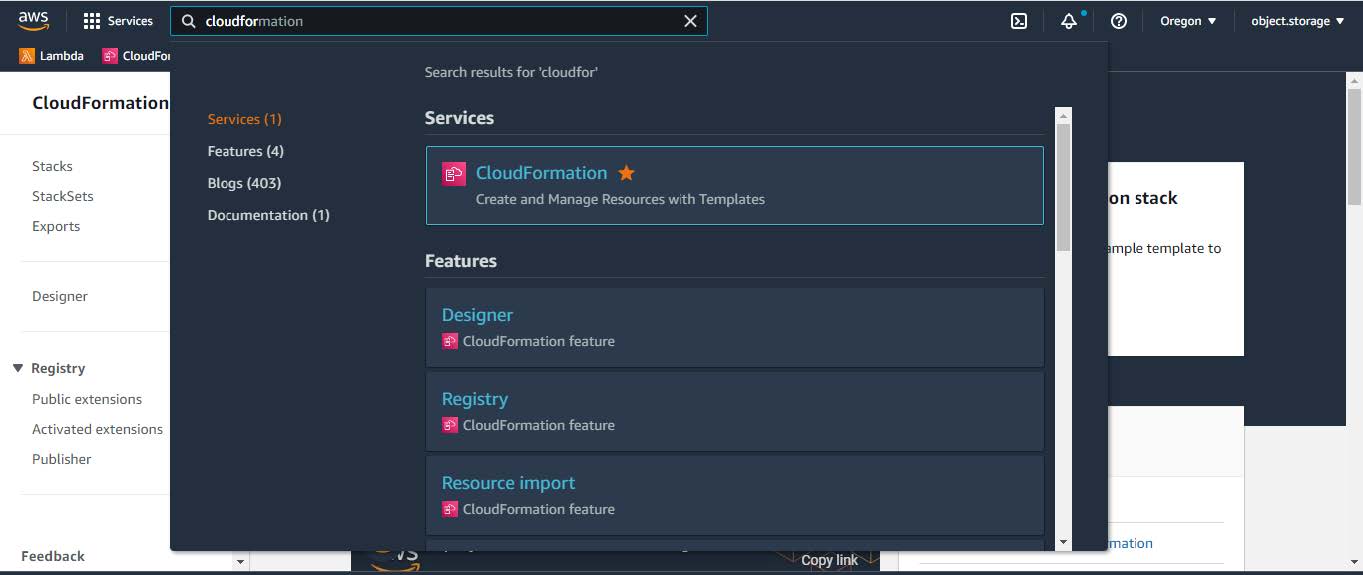
Manual deployment using AWS CloudFormation
This chapter explains how to manually deploy the Catalyst Center AMI on your AWS account using AWS CloudFormation. You will create the AWS infrastructure, establish a VPN tunnel, and deploy Catalyst Center.
This deployment method is an option for those who
-
are familiar with AWS administration, and
-
have existing VPCs.


 Feedback
Feedback