Catalyst Center on AWS
 Note |
Cisco DNA Center has been rebranded as Cisco Catalyst Center. During the rebranding process, you will see the former and rebranded names used in different collaterals. However, Cisco DNA Center and Catalyst Center refer to the same product. |
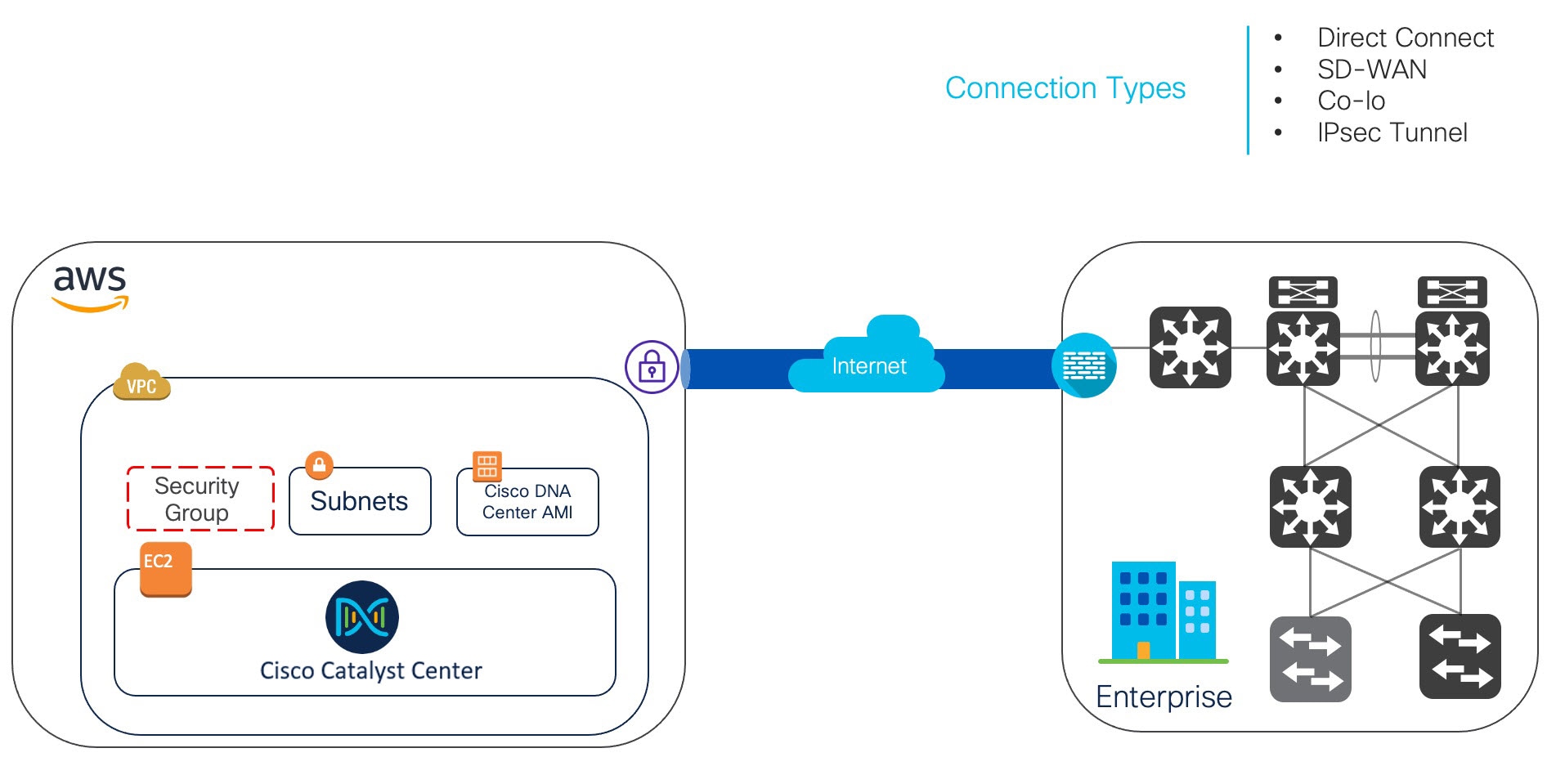
Catalyst Center on AWS
Catalyst Center on Amazon Web Services (AWS) is a deployment model that
-
provides the full functionality of a Catalyst Center appliance deployment
-
runs in your AWS cloud environment, and
-
manages your network from the cloud.
Catalyst Center offers centralized, intuitive management that makes it fast and easy to design, provision, and apply policies across your network environment. The Catalyst Center user interface provides end-to-end network visibility and uses network insights to optimize network performance and deliver the best user and application experience.
Catalyst Center on AWS topology

 Feedback
Feedback