Field Notice: FN74345 - Cisco On-Premises Calling Products: Impact on Secure Communication Due to Upcoming Changes to TLS certificates Issued by Public Certificate Authorities with Client Authentication EKU, Starting May 2026 - Workaround Provided
Available Languages
Notice
THIS FIELD NOTICE IS PROVIDED ON AN "AS IS" BASIS AND DOES NOT IMPLY ANY KIND OF GUARANTEE OR WARRANTY, INCLUDING THE WARRANTY OF MERCHANTABILITY. YOUR USE OF THE INFORMATION ON THE FIELD NOTICE OR MATERIALS LINKED FROM THE FIELD NOTICE IS AT YOUR OWN RISK. CISCO RESERVES THE RIGHT TO CHANGE OR UPDATE THIS FIELD NOTICE AT ANY TIME.
Products Affected
| Affected Software Product | Affected Release | Affected Release Number | Comments |
|---|---|---|---|
| Emergency Responder | - | All releases are affected. | |
| Unified Communications Manager | - | All releases are affected including Session Management Edition | |
| Unified Communications Manager IM and Presence Service | - | All releases are affected. | |
| Unity Connection | - | All releases are affected. |
Defect Information
| Defect ID | Headline |
| CSCws03463 | Support for separate server and client Certificate for CUC |
| CSCws02424 | Support for Separate Server and Client Certificate Support for CUCM |
| CSCws03437 | Support for Separate Server and Client Certificate Support for IM&P |
| CSCws03022 | Support for separate server and client Certificate for CER |
Problem Description
Effective March 2027, the Chrome Root Program Policy will restrict root certificate authority (CA) certificates that are included in the Chrome Root Store, phasing out multi-purpose roots to align all public-key infrastructure (PKI) hierarchies to serve only TLS server authentication use cases.
This constraint includes root CAs that assert an Extended Key Usage (EKU) only for server authentication (id-kp-serverAuth). As a result, certificates issued by a public root CA with only Server Authentication EKU will not be valid for client authentication in mutual TLS (mTLS) setups.
Note: The effective date of the Chrome Root Program Policy is subject to change. For the most up-to-date information, see the Chrome Root Program Policy.
Background
To meet the Chrome Root Program Policy requirement, effective March 2027, public root CAs that are part of Chrome Root Store will be restricted to Server Authentication EKU only, effectively sunsetting the Client Authentication EKU from the store. As a response, public CA servers will stop issuing Client Authentication EKU certifications before March 2027. This date might change, and timelines will be decided by the CAs.
Certificates must include only Server Authentication EKU to maintain trust from the Google Chrome browser. Including the Client Authentication EKU in these certificates will be prohibited.
Although certain public root CAs continue to issue certificates containing the Client Authentication EKU, they will eventually be removed from the Chrome Root Store.
Certificates that are used for mTLS connections in Cisco Unified Communication devices are expected to include both Server and Client Authentication EKUs. Customers could choose to have these certificates from public CA providers.
Server Authentication EKU-only certificates that are provided by public root CAs can break certificate validity, leading to potential authentication issues in Cisco Unified Communication devices and affecting proper functionality.
For more details, see the Chrome Root Program Policy.
Problem Symptom
Cisco on-premises calling products can be affected by potential authentication issues and impacted functionality due to broken certificate validity that is caused by using Server Authentication-only certificates provided by public root CAs.
The following list shows examples of certificates that are used for mTLS connections in these Cisco on-premises calling products:
- Unified Communication Manager/Session Management Edition (Unified CM/Unified CM SME): Tomcat, TVS, Call Manager, and IPSec
- Unified Communication Manager IM & Presence Service (Unified CM IM&P), formerly Cisco Unified Presence (CUP): cup-xmpp-s2s
- Emergency Responder: Tomcat
- Unity Connection: Tomcat
The following list shows examples of certificates that are used for different mTLS connections:
- Tomcat: Connections with external servers like Lightweight Directory Access Protocol (LDAP), filebeat, logslash server, and SIP Oauth over MRA
- Call Manager: SIP Trunk connections and internode/intercluster connections
- TVS: Online-CAPF (Certificate Authority Proxy Function) connection
- IPSec: IPSec connections with other Cisco Unified CM nodes and Gateways
- CUP: Secure SIP connections with Cisco Unified CM and third party clients
- CUP-XMPP-S2S: Extensible Messaging and Presence Protocol (XMPP) federation
Workaround/Solution
Before considering workaround and solution options, audit current certificates. Prepare an inventory of all public TLS certificates to identify which certificates contain the Client Authentication EKU.
Workaround
Administrators can choose from one of the following workaround options.
Option 1: Switch to public root CAs that provide combined EKU certificates.
Some public root CAs, such as DigiCert and IdenTrust, issue certificates with combined EKU types (server and client certificates) from an alternative root, which may not be included in the Chrome Root Store. Coordinate with the CA provider to check the availability of such certificates, and, before deploying them, ensure that both the server presenting the certificate and the clients consuming it trust the corresponding root CA.
This approach alleviates the need to upgrade server software to mitigate sunsetting of Client Authentication EKU that is enforced by the Chrome Root Program Policy.
The following table, which shows examples of public root CAs and EKU types, is not an exhaustive list and is for illustrative purposes only.
CA Vendor EKU Type Root CA Issuing/Sub CA IdenTrust clientAuth + serverAuth IdenTrust Public Sector Root CA 1 IdenTrust Public Sector Server CA 1 IdenTrust clientAuth IdenTrust Public Sector Root CA 1 TrustID RSA ClientAuth CA 2 IdenTrust serverAuth (browser trusted) IdenTrust Commercial Root CA 1 HydrantID Server CA O1 DigiCert clientAuth + serverAuth DigiCert Assured ID Root G2 DigiCert Assured ID CA G2 DigiCert clientAuth DigiCert Assured ID Root G2 DigiCert Assured ID Client CA G2 DigiCert serverAuth (browser trusted) DigiCert Global Root G2 DigiCert Global G2 TLS RSA SHA256 Option 2: Renew current certificates to extend validity.
Certificates that were issued by public root CAs before the sunsetting of Client Authentication EKU and that have both Server and Client Authentication EKU will continue to be honored until their term expires. However, it is best to renew combined EKU certificates before policy sunsetting occurs.
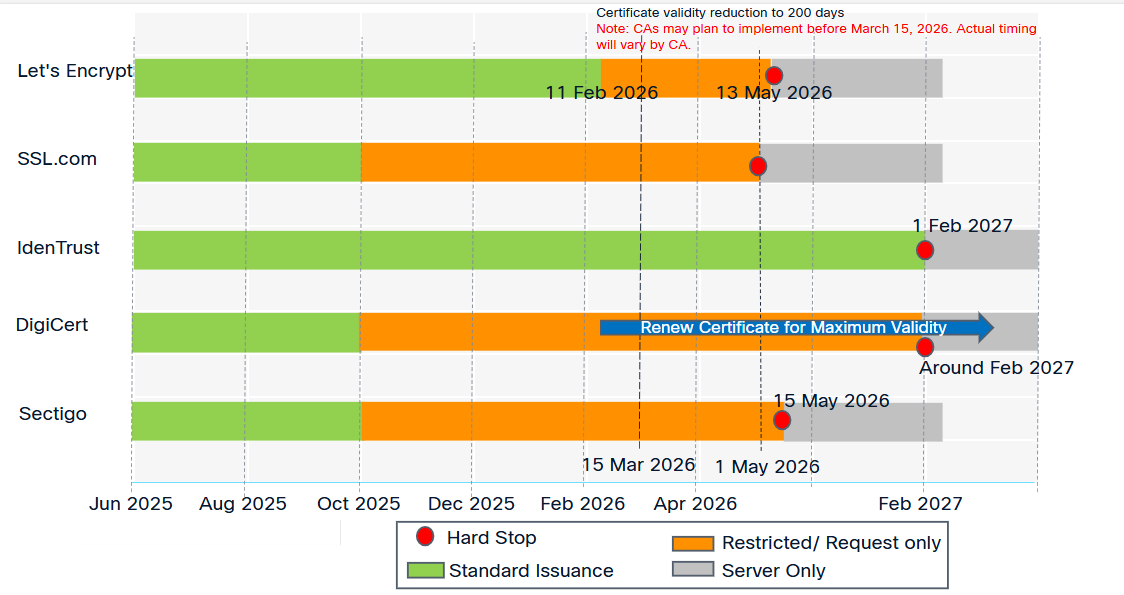
To maximize certificate validity, renew certificates before March 15, 2026, when public CAs will reduce maximum validity to 200 days. Note that CA policies vary. Some may implement this change earlier, reducing validity to 200 and 100 days. Work with CA providers to find the appropriate date and path.
Note: Some public CAs have stopped issuing combined EKU certificates and may not provide one by default. To generate a certificate with a combined EKU, work with public CAs, which may provide special profiles.
Upgrade servers after the solution mentioned in this field notice is available.
The following image shows the Client Authentication EKU depreciation timeline, which is subject to change. For the most recent information, check with the specific CA.
To manage certificates for Cisco Collaboration products, see the steps in the following guides:
- Cisco Unified Communication Manager Certificate Regeneration
- Cisco Emergency Responder 15 Certificate Management
- Cisco Emergency Responder 14 Certificate Management
- Cisco Unity Connection 15 Security Administration
- Cisco Unity Connection 14 Security Administration
Option 3: Evaluate and Migrate to Alternatives
Evaluate the feasibility of transitioning to a private PKI and then set up a private CA to issue single certificates with combined EKUs.
Before issuing or deploying a certificate, ensure that both the server presenting the certificate and all clients consuming it trust the corresponding root CA. Using this approach will alleviate the need to upgrade server software to mitigate sunsetting of Client Authentication EKU that is enforced by the Chrome Root Program Policy.
Solution
The following product enhancements will be implemented in the fixed release that is described in the table in this section:
- Segregation of client and server certificates: This will enable support for two separate certificates on the same interface, such as Tomcat server certificates (with Server Authentication EKU) and Tomcat client certificate (with Client Authentication EKU) to facilitate mTLS connections. Customers must arrange for Client Authentication EKU certificates from either private PKI or alternate root CAs.
- Options for administrators to disable Client Authentication EKU checks: This will allow on-premises calling products to ignore EKU from remote peers (client) that are requesting a connection with Server Authentication EKU-only certificate. This option will also allow on-premises calling products to (re)use the Server Authentication EKU-only certificate as a client certificate. Note: The remote peer will also have to support a similar Ignore Client Authentication EKU model.
To segregate server and client certificates or to use the Ignore EKU option, upgrade to a fixed release as shown in the following table:
| Product | Affected Release | Fixed Release |
|---|---|---|
| Emergency Responder Unified CM Unified CM IM&P Unified CM SME Unity Connection Unity Connection Survivable Remote Site Voicemail (SRSV) |
14 14 SU1 14 SU2 14 SU3 14 SU4 15 15 SU1 15 SU2 15 SU3a 15 SU4 |
15 SU5 (future release Q4CY26) |
Additional Information
The following field notices address other Cisco Collaboration products that are affected by this issue:
For more information about this issue, see the following:
- Public CA certificate changes impacting Dedicated Instance
- Blog: Changes to TLS clientAuth Certificates - Ensuring You’re Not Impacted
- Certificate EKU Changes: Actions Cisco On-premises Collaboration Customers MUST TAKE NOW
Revision History
| Version | Description | Section | Date |
| 1.2 | Added blog and article links for more details. Updated information about the dates when the Chrome Root Program Policy is scheduled to go into effect. | Problem Description, Background, Workaround/Solution, Additional Information | 2026-MAR-25 |
| 1.1 | Updated information to explain that public CA servers will stop issuing Client Authentication EKU certifications from May 2026. | Background | 2026-FEB-03 |
| 1.0 | Initial Release | — | 2026-JAN-30 |
For More Information
For further assistance or for more information about this field notice, contact the Cisco Technical Assistance Center (TAC) using one of the following methods:
Receive Email Notification About New Field Notices
To receive email updates about Field Notices (reliability and safety issues), Security Advisories (network security issues), and end-of-life announcements for specific Cisco products, set up a profile in My Notifications.
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
This Document Applies to These Products
- Emergency Responder 14
- Emergency Responder 15
- Unified Communications Manager (CallManager)
- Unified Communications Manager IM and Presence Service 15
- Unified Communications Manager IM and Presence Service Version 14
- Unified Communications Manager Version 14
- Unified Communications Manager Version 15
- Unity Connection Version 14
- Unity Connection Version 15
Unleash the Power of TAC's Virtual Assistance
 Feedback
Feedback