Wired dynamic PVLANs
A wired dynamic PVLAN is a network isolation feature that
-
uses a private VLAN with AAA authorization to isolate clients and provide Zero-Trust
-
blocks peer-to-peer communication within a subnet or VLAN, and
-
assigns a single wired data client per port interface to ensure point-to-point blocking.
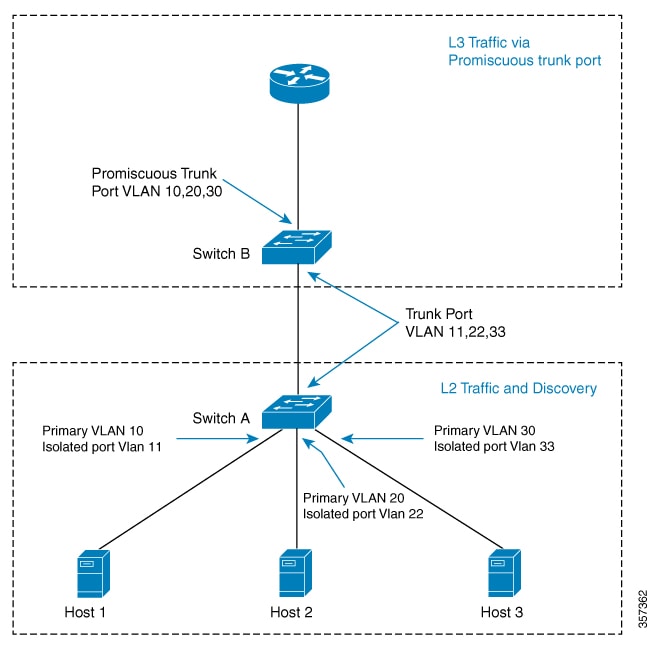
PVLAN isolation and client communication
Hosts connected to Switch A can communicate only with the promiscuous trunk port on the switch. The PVLAN can be extended to span across multiple switches by adding intermediate switches. If there is a switch (Switch C) between Switch A and Switch B, layer 2 trunk ports need to be configured on the intermediate links. In the case of a community VLAN, packets can be seen on other hosts within the same community VLAN.
When a host is connected to a switch port with a cable, it is placed into an isolated PVLAN where it cannot discover any other hosts. The host is then authenticated by the RADIUS server. If the port is placed in closed mode and is not authenticated, only Extensible Authentication Protocol over LAN (EAPoL) packets are allowed. Once the port is authenticated, it is placed into an isolated VLAN dynamically.
When the host first authenticates with the RADIUS server, it sends the name of a dynamic interface template to be applied to the host's port. This interface template contains the configurations to enable the PVLAN primary and secondary VLANs on the port. With the template applied to the host, the switchport mode changes, causing the port to flap from access mode to PVLAN mode.
 Note |
Traffic from multiple clients on the same interface will not be blocked. |
 Note |
The interface template with the same name as referred by AAA Authorization needs to be configured on the switch. |
When the interface template is applied, the port will physically go down for a time period set by the sticky timer and come up again. When the RADIUS server sends the interface template a second time, it is ignored as the conversion has been completed. The port is then assigned to a PVLAN which keeps it isolated. The host completes authorization and comes up to ready state.
Configuring sticky timer for interface template
Configure the keep time for which the interface template information is retained before it is removed from the port using the access-session interface-template sticky timertime command.
PVLAN isolation compared to private rooms
PVLAN isolation is similar to placing each client in a private room, where they cannot see or communicate with other clients except through a central access point.
 Feedback
Feedback