802.1x supplicant and authenticator switches with network edge access topology
An 802.1x supplicant and authenticator switch with network edge access topology is a LAN access control solution that
-
uses the 802.1x standard1 to authenticate clients before granting access to LAN services
-
extends identity and authentication outside the wiring closet using Network Edge Access Topology (NEAT), and
-
supports secure connectivity and trunk configuration for devices connected through layer 2 ports.
1: The 802.1x standard defines a client-server-based access control and authentication protocol that prevents unauthorized clients from connecting to a LAN through publicly accessible ports unless they are properly authenticated.
Network edge access topology features
The NEAT feature allows any device to authenticate on the port, propagating client MAC and VLAN information between supplicant and authenticator switches using CISP. NEAT and CISP are supported only on layer 2 ports, not on layer 3 ports. NEAT can be configured on Cisco Catalyst IE9300 Rugged series Switches.
-
802.1x switch supplicant: Configure a switch to act as a supplicant to another switch using the 802.1x supplicant feature. This is useful when a switch is outside a wiring closet and connected to an upstream switch through a trunk port. The supplicant switch authenticates with the upstream switch for secure connectivity. After successful authentication, the port mode changes from access to trunk in the authenticator switch. On the supplicant switch, manually configure the trunk when enabling CISP.
-
If the access VLAN is configured on the authenticator switch, it becomes the native VLAN for the trunk port after successful authentication.
When connecting a supplicant switch to an authenticator switch with BPDU guard enabled, the authenticator port may be error-disabled if it receives STP BPDU packets before authentication. You can control traffic exiting the supplicant port during authentication. Entering the dot1x supplicant controlled transient global configuration command temporarily blocks the supplicant port during authentication to prevent the authenticator port from shutting down before authentication completes. If authentication fails, the supplicant port opens. Entering the no dot1x supplicant controlled transient global configuration command opens the supplicant port during authentication, which is the default behavior.
Use the dot1x supplicant controlled transient command on a supplicant switch when BPDU guard is enabled on the authenticator switch port with the spanning-tree bpduguard enable interface configuration command.
 Note |
If you globally enable BPDU guard on the authenticator switch by using the spanning-tree portfast bpduguard default global configuration command, entering the dot1x supplicant controlled transient command on the supplicant switch does not prevent the BPDU violation. |
You can enable MDA or multiauth mode on the authenticator switch interface that connects to one or more supplicant switches. Multihost mode is not supported on the authenticator switch interface.
When you reboot an authenticator switch with single-host mode enabled on the interface, the interface may move to err-disabled state before authentication. To recover from err-disabled state, flap the authenticator port to activate the interface again and initiate authentication.
Use the dot1x supplicant force-multicast global configuration command on the supplicant switch for NEAT to work in all host modes.
-
Host authorization: Ensures that only traffic from authorized hosts connecting to the switch with supplicant is allowed on the network. The switches use CISP to send the MAC addresses connecting to the supplicant switch to the authenticator switch.
-
Auto enablement: Automatically enables trunk configuration on the authenticator switch, allowing user traffic from multiple VLANs coming from supplicant switches. Configure the cisco-av-pair as device-traffic-class=switch at the ISE. (You can configure this under the group or the user settings.)
Figure 1. Authenticator and supplicant switch using CISP 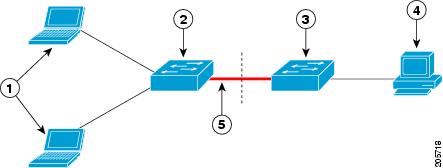
|
1 |
Workstations (clients) |
|
2 |
Supplicant switch (outside wiring closet) |
|
3 |
Authenticator switch |
|
4 |
Cisco ISE |
|
5 |
Trunk port |
 Note |
The switchport nonegotiate command is not supported on supplicant and authenticator switches with NEAT. This command should not be configured at the supplicant side of the topology. If configured on the authenticator side, the internal macros automatically remove this command from the port. |
For more information about 802.1x, including configuration information, see Configuring IEEE 802.1x Port-Based Authentication.
 Feedback
Feedback