Ensure that the local addresses specified in static and dynamic NAT rules do not overlap.
Recommendations for NAT configuration
-
Ensure that the local addresses specified in static and dynamic NAT rules do not overlap. If overlap is possible, configure
the ACL associated with the dynamic rule to exclude the corresponding addresses used by the static rule. Similarly, ensure
there is no overlap between the global addresses.
-
Do not employ loose filtering such as
permit ip any any
in an ACL associated with a NAT rule to avoid packets translation.
-
Do not share an address pool across multiple NAT rules.
-
Do not define the same inside global address in both static NAT configuration and dynamic pool configuration.
-
Carefully evaluate the impact before modifying the default timeout values associated with NAT. Small timeout values could
result in high CPU usage.
-
Avoid manually clearing NAT translation entries unless absolutely necessary. Manually clearing translation entries could result
in the disruption of active application sessions.
-
Use dedicated interface(s) for NAT traffic when Application-Level Gateway (ALG) protocols are in use as they are punted to
CPU. For all other types of traffic that does not require NAT translation, use different interface(s).
Types of NAT
You can configure NAT such that it advertises only a single address for your entire network to the outside world. The configuration
effectively hides the internal network from the world, giving you some additional security.
The types of NAT include:
-
Static address translation (static NAT): Allows one-to-one mapping between local and global addresses.
-
Dynamic address translation (dynamic NAT): Maps unregistered IP addresses to registered IP addresses from a pool of registered
IP addresses.
-
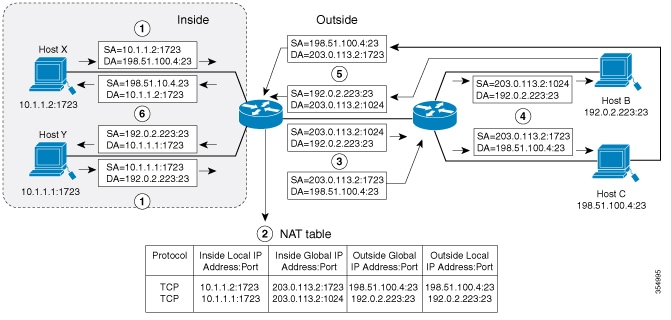
Overloading or Port Address Translation (PAT): Maps multiple unregistered IP addresses to a single registered IP address (many
to one) using different Layer 4 ports. This method is also known as Port Address Translation (PAT). By using overloading,
thousands of users can be connected to the Internet by using only one real global IP address.
Benefits of NAT
NAT provide these advantages for your network:
-
IP address conservation: NAT maps internal addresses to a small range of registered Class C addresses to resolve IP address
scarcity.
-
Enhanced security: NAT hides internal IP addresses—including already registered internal addresses—from external entities
to prevent direct attacks on internal hosts.
-
Addressing flexibility: You can expand internal Class A addressing, which is drawn from the reserve pool of the Internet Assigned
Numbers Authority (IANA), without changing addresses at the LAN or internet interface.
-
Simplified configuration: You can implement NAT on a few exit devices without changing other devices in the network.
-
Device compatibility: NAT is designed for use on a variety of devices for IP address simplification and conservation.
IP address depletion resolution: NAT allows organizations with existing networks to access the internet without acquiring
registered IP addresses for every host. Sites that do not yet possess Network Information Center (NIC)-registered IP addresses
must acquire IP addresses. If a site has more than 254 clients, NAT resolves the scarcity of Class B addresses by mapping
internal addresses to available Class C addresses.
Network security: NAT secures the network by hiding internal client addresses—including registered internal addresses—from
external entities. This prevents hackers from identifying and attacking specific internal hosts.
Implementation flexibility: Cisco software performs NAT selectively or dynamically. This allows you to use RFC 1918 addresses
or registered addresses and select specific internal hosts for translation. You can configure NAT on a few exit devices without
modifying other devices in the network.
Connecting to the internet with limited global IP addresses
Use NAT to enable internet connectivity when only a few of your hosts have globally unique IP addresses.
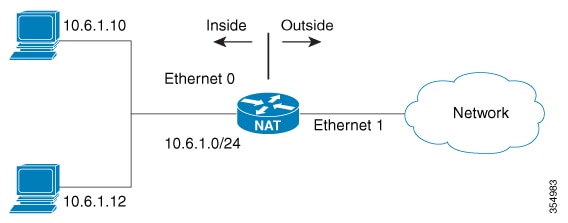
Configure NAT on the border device between your internal network and the internet. NAT translates your internal addresses
to globally unique IP addresses before forwarding packets to the internet.
This approach works when few internal hosts communicate externally at the same time. NAT translates only active connection
addresses and reuses these global addresses as needed.

Note
|
Translate internal addresses using NAT instead of changing them manually, which reduces configuration effort.
|
Use cases for network address translations
You can use network address translations in the following scenarios:
-
Internet connectivity: When only a few hosts in your internal network require a globally unique IP address to communicate
with the internet simultaneously.
-
Network renumbering: When you need to change internal addresses but prefer to translate them using NAT rather than manually
reconfiguring every host.
-
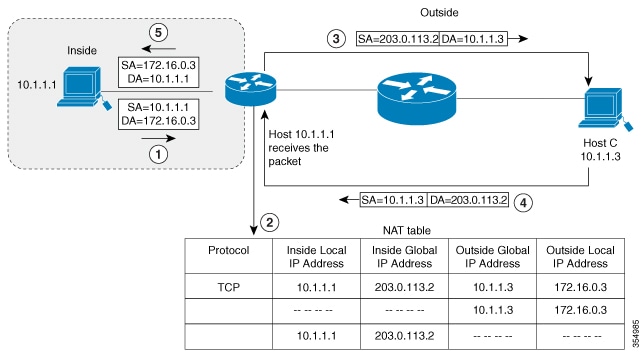
Overlapping networks: When you connect two networks that use the same private IP address space (such as 10.1.1.x) and need
to translate the addresses to ensure connectivity.
Static and dynamic translations
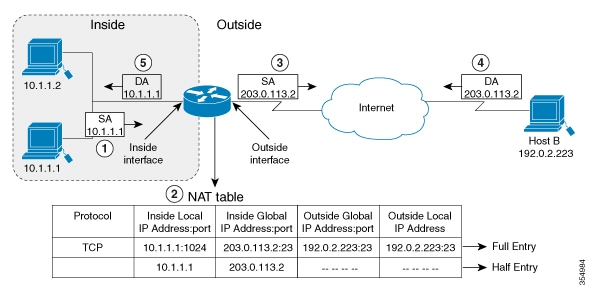
This table contrasts the two primary methods of source address translation.
Table 1. Static and dynamic translations
| Static translation |
Dynamic translation |
| Establishes a permanent one-to-one mapping between an inside local address and an inside global address. |
Establishes a temporary mapping between an inside local address and a pool of global addresses at run-time. |
| Used when an internal host (such as a mail server) must be accessible from the outside using a fixed address. |
Used when multiple users on a private network need to access the internet periodically. |
| The mapping is manually configured and does not time out. |
The mapping is created dynamically and is released back to the pool after a period of inactivity. |

 Feedback
Feedback