Scenario
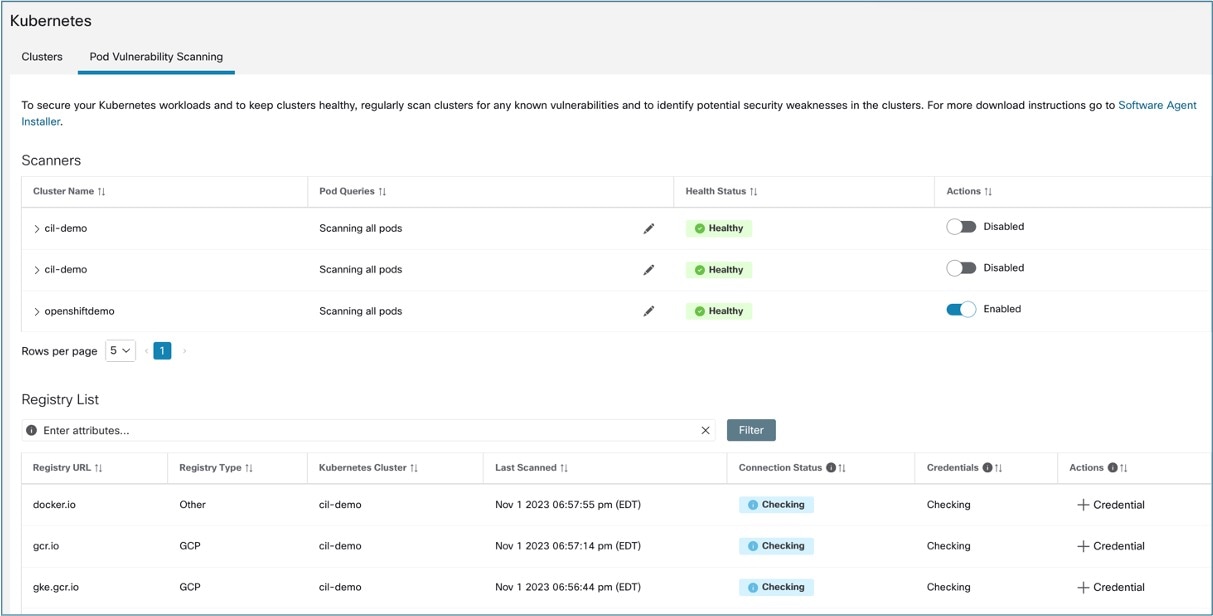
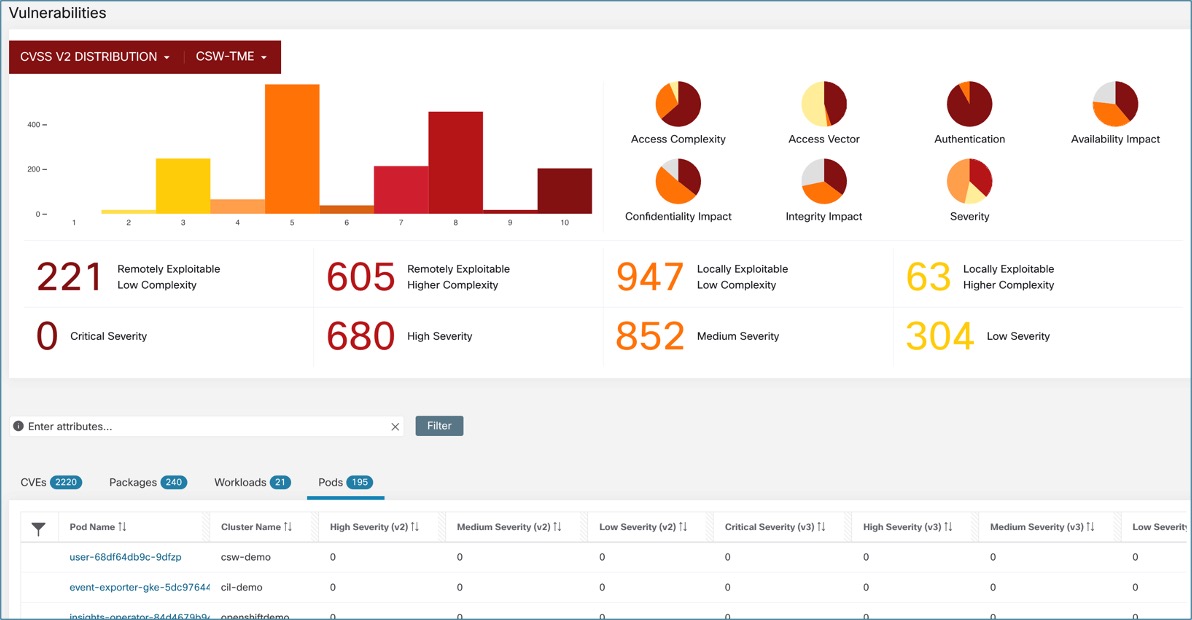
A security analyst and a DevOps engineer collaborate to manage vulnerabilities in a Kubernetes cluster using the Secure Workload scanner pod.
Is this use case for you?
The target audience for this scenario includes DevOps engineers, Security analysts, and Cloud and Network security engineers responsible for ensuring the security of containerized applications throughout the development lifecycle. This involves continuously monitoring and securing containerized environments to detect potential threats and vulnerabilities.
 Feedback
Feedback