About this Document
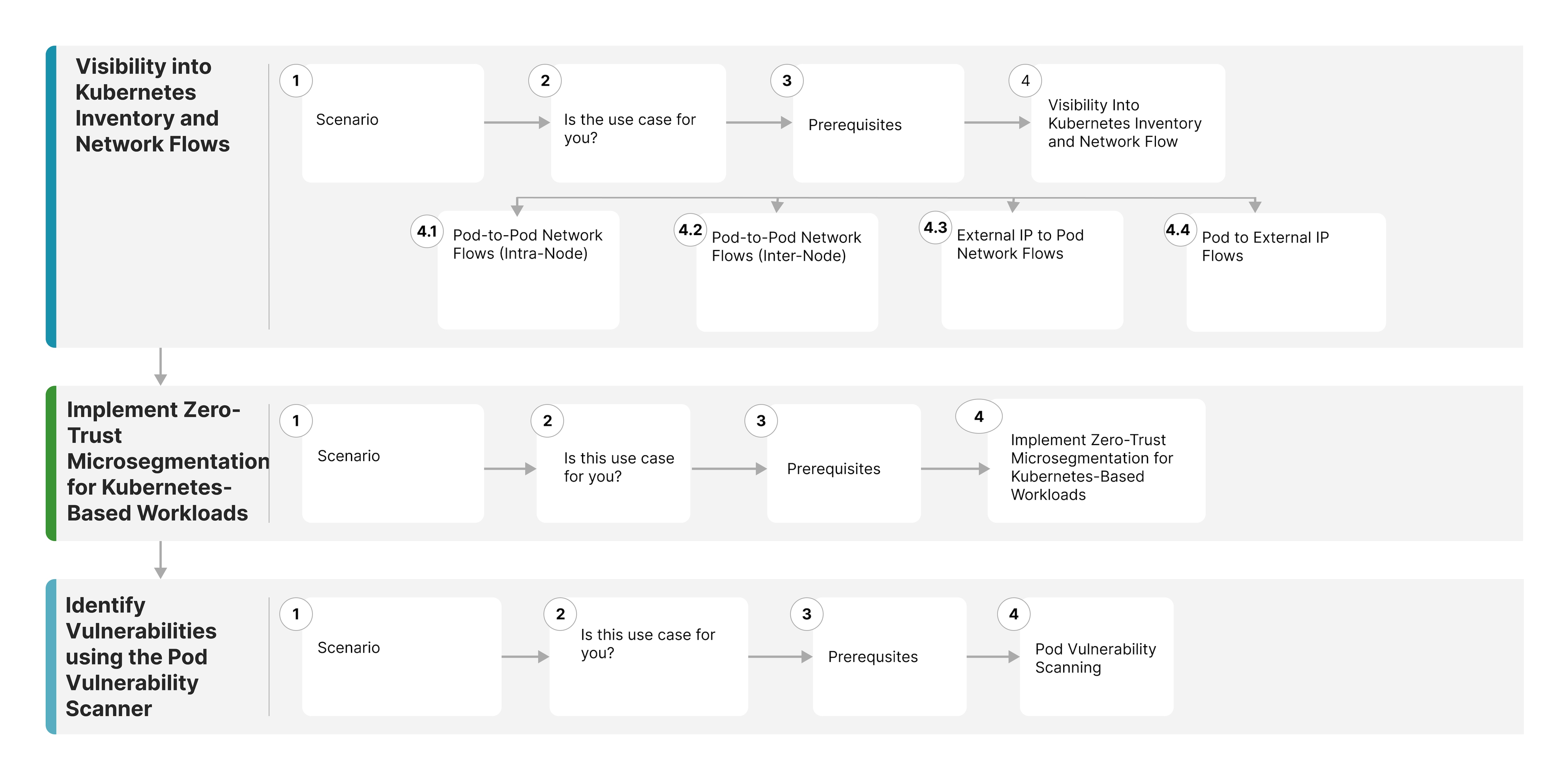
This document details the primary use cases on Kubernetes security supported by Cisco Secure Workload.
The approaches in the document do not encompass all potential network requirements; rather, they serve as models for structuring your network. You can incorporate and modify features to better align with your specific needs. Additionally, the document assumes you are familiar with Cisco Secure Workload solution.
For more information, see Cisco Secure Workload Documentation.
 Feedback
Feedback