Managing Meraki with Security Cloud Control
Meraki MX is an enterprise security and software-defined wide-area-network (SD-WAN) next-generation firewall appliance designed for distributed deployments. The Meraki dashboard manages Meraki MX remotely. You can use Security Cloud Control (formerly Cisco Defense Orchestrator) to manage Layer 3 network rules for Meraki MX devices. For more information, refer to Meraki Next-Gen Firewall Technologies and Meraki product.
After you onboard a Meraki device to Security Cloud Control, Security Cloud Control communicates with the Meraki dashboard to manage that device. Security Cloud Control does not communicate directly with the MX device.
Security Cloud Control securely transfers configuration requests to the Meraki dashboard which then applies the new configuration to the device. For more information, refer to How Does Security Cloud Control Communicate With Meraki.
Security Cloud Control provides tools to optimize your Meraki environment by detecting problems with objects and policies and suggesting possible fixes or alternative options. This applies to policies that are associated with both devices and templates. Use Security Cloud Control to:
-
Simultaneously manage policies on one or more Meraki devices.
-
Monitor and manage Meraki policies or templates along with your FTD and ASA devices in a comprehensive environment.
-
Use a Meraki template to manage multiple networks.
-
Customize access rules by using objects that are compatible with other supported platforms, such as FTD and ASA devices.
Onboard Meraki MX Devices
Before onboarding a device to Security Cloud Control, you must create an account with the Meraki dashboard and onboard your device or template to the dashboard. To generate an API token and communicate with Security Cloud Control, your organization must have an account in the Meraki dashboard.
You can onboard a Meraki MX device or a Meraki template to Security Cloud Control.
Handle Meraki MX log in credentials and permissions through the Security Cloud Control console. Without the correct credentials or permissions, Security Cloud Control cannot communicate with the Meraki device.
For more information, refer to Updating Meraki MX Credentials and Generate and Retrieve Meraki API Key.
Meraki Layer 3 Rules and Security Cloud Control
At this time, Security Cloud Control supports Layer 3 firewall rules only. Layer 3 rules let you manage policy at the network layer of the OSI model. For more information, refer to Using Layer 3 Firewall Rules.
You can create Layer 3 outbound rules in the Meraki dashboard. When you onboard a device into Security Cloud Control, Security Cloud Control reads the Layer 3 rules that you have defined in the Meraki dashboard. You can then manage these rules in Security Cloud Control in the same way as you manage FTD or ASA rules. For more information, refer to Manage Meraki Access Control Policy.
Objects
You can optimize your new access control policy with objects. The Meraki dashboard uses protocols and groups of IP addresses or IP address ranges. In contrast, Security Cloud Control uses a variety of objects to manage rules. To understand how Security Cloud Control transfers Meraki protocols into objects, refer to Objects Associated with Meraki Devices. You can create these objects in Security Cloud Control, and they are translated into IP groups in the Meraki dashboard:
You can create Layer 3 outbound rules in the Meraki dashboard. Security Cloud Control reads in the Layer 3 rules you have defined in the Meraki dashboard when you onboard a device into Security Cloud Control. You can then manage these rules just as you would manage FTD or ASA rules in Security Cloud Control. For more information about Meraki access control policy, refer to Manage Meraki Access Control Policy.
How Does Security Cloud Control Communicate With Meraki
Deploy From Security Cloud Control to your Meraki Device
Security Cloud Control does not deploy configuration changes directly to a Meraki MX device; deployment is a multistep process. The diagram below shows the deployment process.
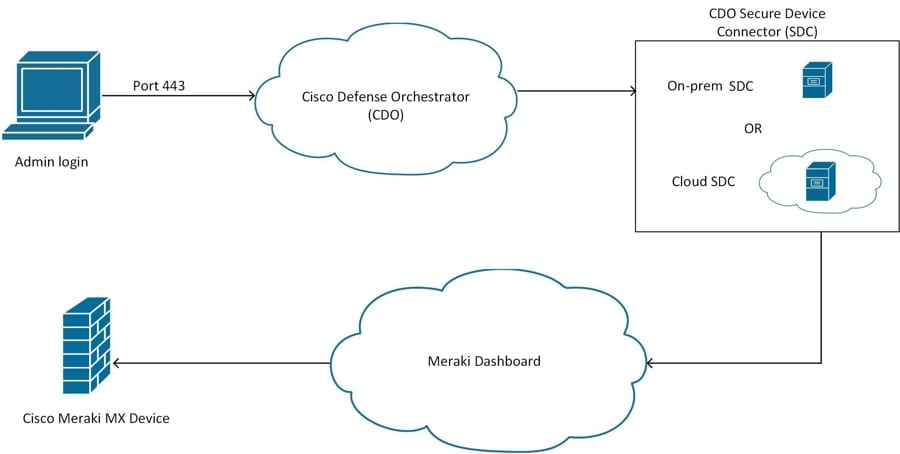
Configuration changes that you make in Security Cloud Control for a Meraki MX device are staged in Security Cloud Control until you deploy them. When you deploy the configuration changes, Security Cloud Control forwards them to the Meraki dashboard, which implements them on the Meraki MX device. Security Cloud Control manages firewall policies while Meraki dashboard manages the network the policies are applied to. Both operations affect the way the Meraki MX device manages and processes network traffic.
Some customers with older tenants may connect the Meraki MX device to Security Cloud Control through an SDC. If you are one of those customers, you can continue to use this method or you can remove the SDC by onboarding your Meraki MX again or updating the connection credentials. You do not need an SDC to connect Security Cloud Control to Meraki MX.
One difference between Security Cloud Control and the Meraki dashboard is the use of objects. For rules that are created on the Meraki dashboard, Security Cloud Control takes Meraki IP address groups or IP address ranges and turns them into objects that can be attached or associated to rules and the device policy. When you deploy objects that are created in Security Cloud Control to Meraki appliances, the Meraki dashboard translates those objects back into IP address groups or ranges. Objects in Security Cloud Control are unique and versatile because they are compatible with other device platforms. If you have other devices onboarded in Security Cloud Control, you may be able to create a single object for all your devices. For more information about objects associated with Meraki devices, refer to Objects Associated with Meraki Devices.
 Feedback
Feedback