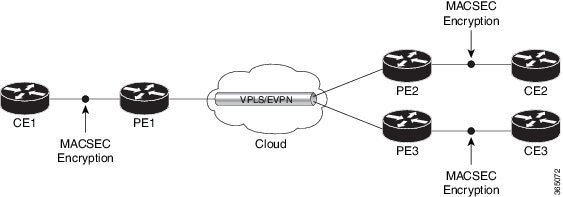
The MACsec service configuration is applied to the host-facing interface of a CE router.
Guidelines for MACsec Interface Configuration
-
Configure different keychains for primary and fallback PSKs.
-
We do not recommend to update both primary and fallback PSKs simultaneously, because fallback PSK is intended to recover MACsec
session on primary key mismatch.
-
When using MACsec, we recommend you adjust the maximum transmission unit (MTU) of an interface to accommodate the MACsec overhead.
Configuring MTU value on an interface allows protocols to do MTU negotiation including MACsec overhead. For instance, if the
default MTU is 1514 bytes, configure the MTU to 1546 bytes (1514 + 32).
-
The minimum MTU for IS-IS protocol on the MACsec interface is 1546 bytes.
-
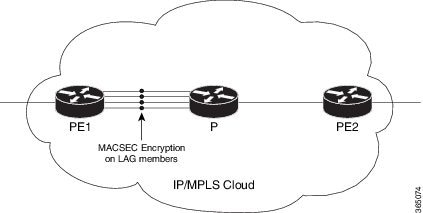
To enable MACsec on bundles:
-
Enable MACsec on all bundle members.
-
We recommend configuring the maximum possible MTU on the bundle interface.
-
The MTU configurations must account for the maximum packet size of the protocols running on the bundle interface and 32 bytes
of MACsec overhead.
-
For IS-IS protocol running on the bundle interface, hello-padding must be disabled.

Tip
|
You can programmatically view the MACsec configuration using the openconfig-macsec.yang OpenConfig data model. To get started with using data models, see
Programmability Configuration Guide for Cisco 8000 Series Routers.
|
MACsec PSK Configuration on an Interface
Router#configure
Router(config)#interface hundredGigE 0/1/0/10
Router(config-if)# macsec psk-keychain kc policy mp-SF
To enable MACsec PSK on a physical interface without the MACsec policy, use this command:
Router(config-if)#macsec psk-keychain script_kc
MACsec Fallback PSK Configuration on an Interface
It is optional to configure a fallback PSK. If a fallback PSK is configured, the fallback PSK along with the primary PSK ensures
that the session remains active even if the primary PSK is mismatched, or there is no active key for the primary PSK.
Router(config-if)#macsec psk-keychain kc fallback-psk-keychain fallback_kc policy mp-SF
Router(config-if)#commit
Verification
Before the introduction of active fallback functionality:
Router# show macsec mka session detail
NODE: node0_1_CPU0
MKA Detailed Status for MKA Session
===================================
Status: Secured - Secured MKA Session with MACsec
Local Tx-SCI : 7872.5d1a.e7d4/0001
Local Tx-SSCI : 1
Interface MAC Address : 7872.5d1a.e7d4
MKA Port Identifier : 1
Interface Name : Hu0/1/0/10
CAK Name (CKN) : 1234
CA Authentication Mode : PRIMARY-PSK
Keychain : kc
Member Identifier (MI) : C12A70FEE1212B835BDDDCBA
Message Number (MN) : 395
Authenticator : NO
Key Server : NO
MKA Cipher Suite : AES-128-CMAC
Configured MACSec Cipher Suite : GCM-AES-XPN-128
Latest SAK Status : Rx & Tx
Latest SAK AN : 0
Latest SAK KI (KN) : 018E2F0D63FF2ED6A5BF270E00000001 (1)
Old SAK Status : FIRST-SAK
Old SAK AN : 0
Old SAK KI (KN) : FIRST-SAK (0)
SAK Transmit Wait Time : 0s (Not waiting for any peers to respond)
SAK Retire Time : 0s (No Old SAK to retire)
Time to SAK Rekey : NA
Time to exit suspension : NA
MKA Policy Name : mp-SF
Key Server Priority : 16
Delay Protection : FALSE
Replay Window Size : 64
Include ICV Indicator : FALSE
Confidentiality Offset : 30
Algorithm Agility : 80C201
SAK Cipher Suite : 0080C20001000003 (GCM-AES-XPN-128)
MACsec Capability : 3 (MACsec Integrity, Confidentiality, & Offset)
MACsec Desired : YES
# of MACsec Capable Live Peers : 1
# of MACsec Capable Live Peers Responded : 0
Live Peer List:
-------------------------------------------------------------------------------
MI MN Rx-SCI SSCI KS-Priority
-------------------------------------------------------------------------------
018E2F0D63FF2ED6A5BF270E 86 008a.962d.7400/0001 2 16
Potential Peer List:
-------------------------------------------------------------------------------
MI MN Rx-SCI SSCI KS-Priority
-------------------------------------------------------------------------------
Peers Status:
Last Tx MKPDU : 2019 Oct 08 07:39:56.905
Peer Count : 1
RxSCI : 008A962D74000001
MI : 018E2F0D63FF2ED6A5BF270E
Peer CAK : Match
Latest Rx MKPDU : 2019 Oct 08 07:39:57.363
With the introduction of active fallback functionality:
The following is a snippet from the sample output that displays entry for active fallback PSK as well. The secured primary
session output part is truncated here, which is exactly same as the output given above.
Router# show macsec mka session detail
NODE: node0_1_CPU0
MKA Detailed Status for MKA Session
===================================
Status: Secured - Secured MKA Session with MACsec
Local Tx-SCI : 0257.3fae.5cda/0001
Local Tx-SSCI : 1
- - - - - - - - - - - - - - - - - -
- - - - - - - - - - - - - - - - - -
- - - - - - - - - - - - - - - - - -
MKA Detailed Status for MKA Session
===================================
Status: Active - Marked Peer as Live (Waiting for SAK generation/distribution)
Local Tx-SCI : 0257.3fae.5cda/0001
Local Tx-SSCI : 1
Interface MAC Address : 0257.3fae.5cda
MKA Port Identifier : 1
Interface Name : Hu0/1/0/0
CAK Name (CKN) : 1111
CA Authentication Mode : FALLBACK-PSK
Keychain : fb1
Member Identifier (MI) : FC53A31E030E385981E0AACE
Message Number (MN) : 178
Authenticator : NO
Key Server : NO
MKA Cipher Suite : AES-256-CMAC
Configured MACSec Cipher Suite : GCM-AES-XPN-256
Key Distribution Mode : SAK
Latest SAK Status : Rx & Tx
Latest SAK AN : 1
Latest SAK KI (KN) : 725FF8F6605A3D428972538F00000001 (1)
Old SAK Status : No Rx, No Tx
Old SAK AN : 0
Old SAK KI (KN) : RETIRED (0)
SAK Transmit Wait Time : 0s (Not waiting for any peers to respond)
SAK Retire Time : 0s (No Old SAK to retire)
Time to SAK Rekey : NA
Time to exit suspension : NA
MKA Policy Name : *DEFAULT POLICY*
Key Server Priority : 16
Delay Protection : FALSE
Replay Window Size : 64
Include ICV Indicator : FALSE
Confidentiality Offset : 0
Algorithm Agility : 80C201
SAK Cipher Suite : 0080C20001000004 (GCM-AES-XPN-256)
MACsec Capability : 3 (MACsec Integrity, Confidentiality, & Offset)
MACsec Desired : YES
# of MACsec Capable Live Peers : 1
# of MACsec Capable Live Peers Responded : 0
Live Peer List:
-------------------------------------------------------------------------------
MI MN Rx-SCI SSCI KS-Priority
-------------------------------------------------------------------------------
6A894FE1E984AD5314F33D21 188 0201.9ab0.85af/0001 0 16
Potential Peer List:
-------------------------------------------------------------------------------
MI MN Rx-SCI SSCI KS-Priority
-------------------------------------------------------------------------------
Peers Status:
Last Tx MKPDU : 2021 Apr 30 14:56:33.797
Peer Count : 1
RxSCI : 02019AB085AF0001
MI : 6A894FE1E984AD5314F33D21
Peer CAK : Match
Latest Rx MKPDU : 2021 Apr 30 14:56:34.638
The following is a sample output of the show macsec mka session interface command. With this command, you can verify whether the interface of the router is peering with its neighbor after MACsec
configuration. The MACsec PSK validation detects inconsistency or mismatch of primary and fallback keys (CAK) being used by
MKA, allowing operators to rectify the mismatch.
Verify whether the MKA session is secured with MACsec on the respective interface. The Status field in the output verifies if the MKA session is secured with MACsec encryption. The output also displays information about
the interface and other MACsec parameters.
Router#show macsec mka session interface hundredGigE 0/1/0/10
===============================================================================================
Interface-Name Local-TxSCI #Peers Status Key-Server PSK/EAP CKN
===============================================================================================
Hu0/1/0/10 7872.5d1a.e7d4/0001 1 Secured NO PRIMARY 1234
Hu0/1/0/10 7872.5d1a.e7d4/0001 1 Secured NO FALLBACK 5678
Before the introduction of active fallback functionality:
Router# show macsec mka session interface hundredGigE 0/1/0/10 detail
MKA Detailed Status for MKA Session
===================================
Status: Secured - Secured MKA Session with MACsec
Local Tx-SCI : 7872.5d1a.e7d4/0001
Local Tx-SSCI : 1
Interface MAC Address : 7872.5d1a.e7d4
MKA Port Identifier : 1
Interface Name : Hu0/1/0/10
CAK Name (CKN) : 1234
CA Authentication Mode : PRIMARY-PSK
Keychain : kc
Member Identifier (MI) : C12A70FEE1212B835BDDDCBA
Message Number (MN) : 433
Authenticator : NO
Key Server : NO
MKA Cipher Suite : AES-128-CMAC
Configured MACSec Cipher Suite : GCM-AES-XPN-128
Latest SAK Status : Rx & Tx
Latest SAK AN : 0
Latest SAK KI (KN) : 018E2F0D63FF2ED6A5BF270E00000001 (1)
Old SAK Status : FIRST-SAK
Old SAK AN : 0
Old SAK KI (KN) : FIRST-SAK (0)
SAK Transmit Wait Time : 0s (Not waiting for any peers to respond)
SAK Retire Time : 0s (No Old SAK to retire)
Time to SAK Rekey : NA
Time to exit suspension : NA
MKA Policy Name : mp-SF
Key Server Priority : 16
Delay Protection : FALSE
Replay Window Size : 64
Include ICV Indicator : FALSE
Confidentiality Offset : 30
Algorithm Agility : 80C201
SAK Cipher Suite : 0080C20001000003 (GCM-AES-XPN-128)
MACsec Capability : 3 (MACsec Integrity, Confidentiality, & Offset)
MACsec Desired : YES
# of MACsec Capable Live Peers : 1
# of MACsec Capable Live Peers Responded : 0
Live Peer List:
-------------------------------------------------------------------------------
MI MN Rx-SCI SSCI KS-Priority
-------------------------------------------------------------------------------
018E2F0D63FF2ED6A5BF270E 123 008a.962d.7400/0001 2 16
Potential Peer List:
-------------------------------------------------------------------------------
MI MN Rx-SCI SSCI KS-Priority
-------------------------------------------------------------------------------
Peers Status:
Last Tx MKPDU : 2019 Oct 08 07:41:12.929
Peer Count : 1
RxSCI : 008A962D74000001
MI : 018E2F0D63FF2ED6A5BF270E
Peer CAK : Match
Latest Rx MKPDU : 2019 Oct 08 07:41:11.400
With the introduction of active fallback functionality:
The following is a snippet from the sample output that displays entry for active fallback PSK as well. The secured primary
session output part is truncated here, which is exactly same as the output given above.
Router# show macsec mka session interface hundredGigE 0/1/0/10 detail
MKA Detailed Status for MKA Session
===================================
Status: Secured - Secured MKA Session with MACsec
Local Tx-SCI : 7872.5d1a.e7d4/0001
Local Tx-SSCI : 1
- - - - - - - - - - - - - - - - - -
- - - - - - - - - - - - - - - - - -
- - - - - - - - - - - - - - - - - -
MKA Detailed Status for MKA Session
===================================
Status: Active - Marked Peer as Live (Waiting for SAK generation/distribution)
Local Tx-SCI : 34ed.1b5b.d0d7/0001
Local Tx-SSCI : 1
Interface MAC Address : 34ed.1b5b.d0d7
MKA Port Identifier : 1
Interface Name : Hu0/4/0/27
CAK Name (CKN) : 2222
CA Authentication Mode : FALLBACK-PSK
Keychain : fb1
Member Identifier (MI) : C0978A6B0916C3FC959773FE
Message Number (MN) : 24039
Authenticator : NO
Key Server : NO
MKA Cipher Suite : AES-256-CMAC
Configured MACSec Cipher Suite : GCM-AES-XPN-256
Latest SAK Status : Rx & Tx
Latest SAK AN : 2
Latest SAK KI (KN) : 3D008A7D75DF0A9A35F9E3A900000002 (2)
Old SAK Status : No Rx, No Tx
Old SAK AN : 1
Old SAK KI (KN) : RETIRED (0)
SAK Transmit Wait Time : 0s (Not waiting for any peers to respond)
SAK Retire Time : 0s (No Old SAK to retire)
Time to SAK Rekey : NA
Time to exit suspension : NA
MKA Policy Name : r1
Key Server Priority : 16
Delay Protection : FALSE
Replay Window Size : 64
Include ICV Indicator : FALSE
Confidentiality Offset : 0
Algorithm Agility : 80C201
SAK Cipher Suite : 0080C20001000004 (GCM-AES-XPN-256)
MACsec Capability : 3 (MACsec Integrity, Confidentiality, & Offset)
MACsec Desired : YES
# of MACsec Capable Live Peers : 1
# of MACsec Capable Live Peers Responded : 0
Live Peer List:
-------------------------------------------------------------------------------
MI MN Rx-SCI SSCI KS-Priority
-------------------------------------------------------------------------------
B5ED6849883F34FEE89F74D1 26068 008a.9681.c02c/0001 2 16
Potential Peer List:
-------------------------------------------------------------------------------
MI MN Rx-SCI SSCI KS-Priority
-------------------------------------------------------------------------------
Peers Status:
Last Tx MKPDU : 2021 Apr 28 02:08:03.795
Peer Count : 1
RxSCI : 008A9681C02C0001
MI : B5ED6849883F34FEE89F74D1
Peer CAK : Match
Latest Rx MKPDU : 2021 Apr 28 02:08:02.749


 Feedback
Feedback