Overview
Describes the workflow for establishing secure point-to-point MACsec links by leveraging external QKD networks for automated, quantum-safe key exchange between peer routers.
Point-to-point MACsec encryption establishes secure communication between peer router interfaces by leveraging an external quantum key distribution (QKD) network for key exchange. This approach ensures secure and automated key management.
Summary
The key components involved in the process are:
-
Router: Initiates the MACsec link creation and communicates with the QKD device using SKIP.
-
Peer router: The other end of the MACsec link, which also communicates with its QKD device.
-
SKIP: The protocol a router uses to establish secure encryption.
-
External QKD device network: A network of Quantum Key Distribution devices responsible for securely sharing MACsec encryption keys.
-
QKD device: A specific device within the QKD network that generates key pairs (key ID and key) and shares them.
-
Key ID: A unique string that identifies the shared secret (key).
-
Key (shared secret): The actual MACsec encryption key.
Workflow
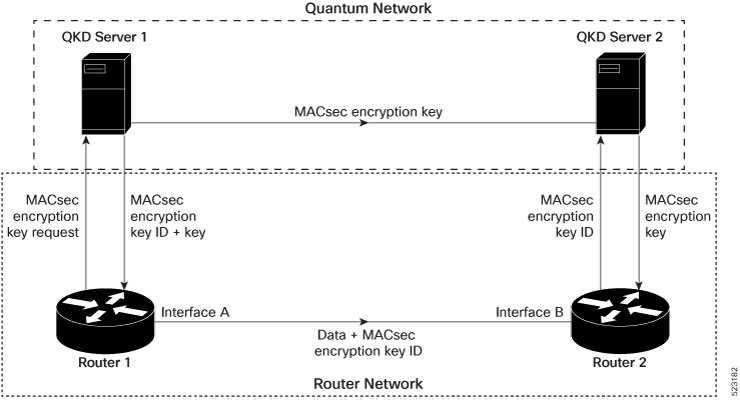
The process involves the following stages:
-
Link creation request: A router needs to create a MACsec link between its interface and a peer router's interface.
-
Key request to QKD: The router contacts its external QKD device and requests the encryption key.
-
Key pair generation: The external QKD device generates a key pair. This pair comprises a unique key ID and the encryption key.
-
Key distribution to initiating router: The QKD device shares both the generated key ID and the key with the initiating router.
-
Key ID sharing with peer: The initiating router shares only the key ID with its peer router.
-
Key retrieval by peer: The peer router uses the received key ID to retrieve the corresponding encryption key from its own QKD device.
-
Secure link establishment: Both routers now possess the same MACsec encryption key, enabling them to establish the secure point-to-point MACsec link.
Result
Quantum networks securely communicate encryption keys. This enables robust and automated secure communication links between peer router interfaces. Routers do not directly exchange sensitive encryption keys.