Overview
Describes the workflow of MACsec encryption, covering link establishment, peer authentication, connectivity association formation, key server selection, and the secure exchange of encrypted data frames.
MACsec is a Layer 2 IEEE 802.1AE standard that secures data on physical media by encrypting packets between two MACsec routers.
Summary
The key components involved in MACsec encryption are:
-
MACsec routers: Devices that implement the MACsec standard to encrypt and decrypt traffic.
-
MACsec Key Agreement (MKA) protocol: Manages the exchange of session keys and encryption keys.
-
Pre-shared Key (PSK): A shared secret used for mutual peer authentication.
-
Secure Association Key (SAK): The actual encryption key used for data encryption.
-
MACsec frame format: The structure of encrypted packets, including SecTAG, Secure Data, and ICV.
Workflow
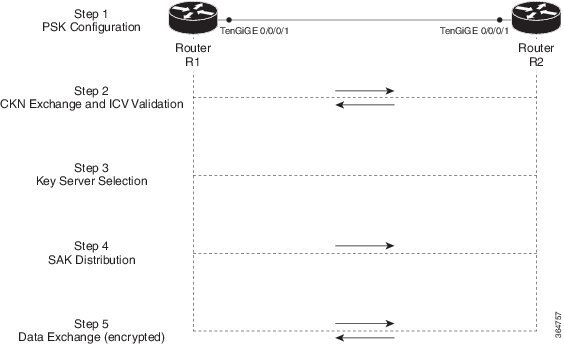
These stages describe how MACsec encryption works:
-
Link establishment and peer authentication: When two MACsec routers first connect, they establish a peer relationship. Both devices perform mutual authentication using a pre-shared key (PSK).
-
Connectivity association formation: After successful peer authentication, the routers create a connectivity association. They exchange a secure connectivity association key name (CKN) and validate the media key agreement (MKA) integrity check value (ICV) using the connectivity association key (CAK).
-
Key server selection: The routers select a key server based on their configured priorities.
Rules that apply to key server selection include:
-
Lower numerical values of key server priority and SCI receive the highest preference.
-
A lower priority value increases the preference for the router to become the key server, while the other router functions as a key client. If no value is configured, the default value of 16 is taken to be the key server priority value for the router.
-
Each router selects a peer advertising the highest preference as its key server if peer has not selected another router as its key server or is not willing to function as the key server.
-
If two routers tie for the highest preference, a router with the highest priority SCI becomes the key server (KS).
-
-
Security association and SAK distribution: The selected key server generates and distributes the secure association key (SAK). Each secure channel relies on a series of overlapping security associations (SA), with each SA utilizing a new SAK.
-
Encrypted data exchange: Once the routers distribute the SAKs and establish security associations, they begin exchanging encrypted data. The data frames include a MACsec header with a SecTAG (for SAK identification and replay protection), the secure data (the encrypted payload), and an ICV (for integrity checking). Once assembled, both devices transmit the encrypted data.
Result
The MACsec process secures data on physical media, making it impossible for data to be compromised at higher layers. It provides data integrity checks, data encryption, and replay protection. This enhances the overall security of the network.