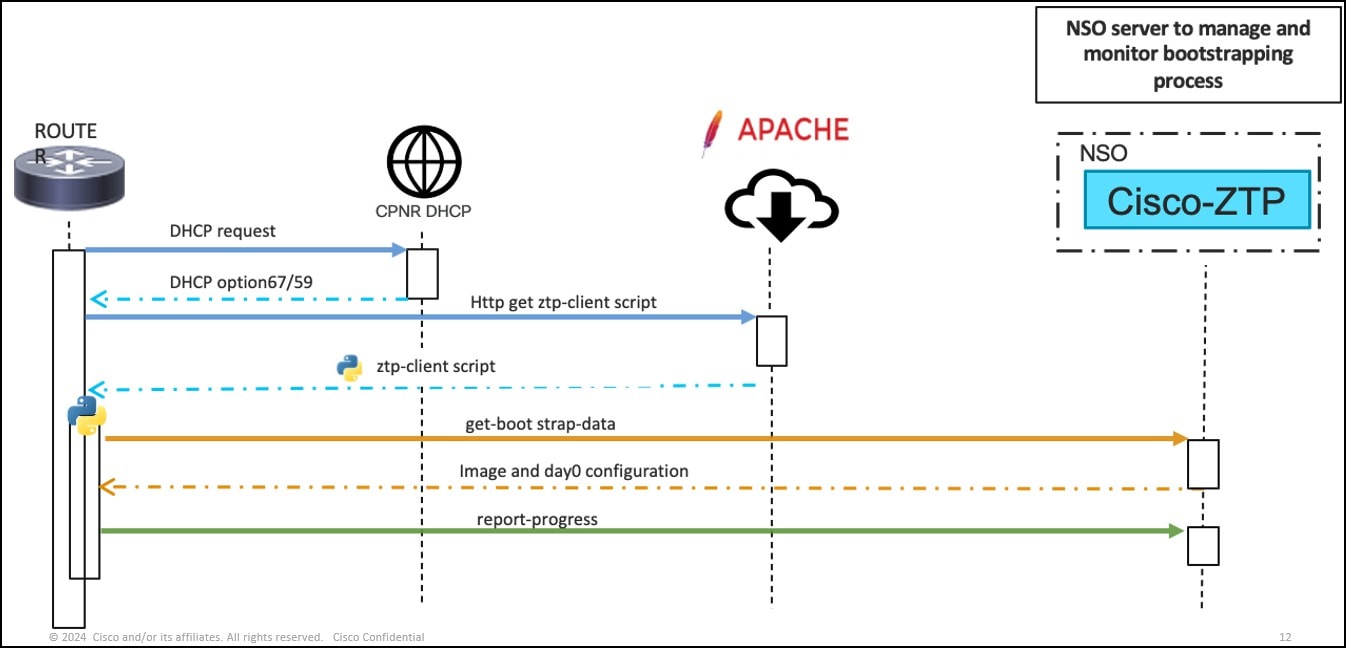
The Device Onboarding package defines two callback action APIs for the Device Onboarding- client interactions. The get-bootstrap-data callback action returns the bootstrapping configuration, the day-0 configuration generated for the device, and the OS image
information as configured on the ZTP-profile. The Device Onboarding-client script then processes the OS image details and
applies the day-0 configuration to the device.
During the bootstrap process, the Device Onboarding-client script reports the progress using the report-progress callback
action. The get-bootstrap-data and report-progress actions must contain the unique identifier of the device. The get-bootstrap-data API call also includes the: device vendor, model, OS-name, and OS-version. Similarly, the report-progress API call includes an optional message.
If both the management resource pool and explicit management IP address configurations are not set and the Device Onboarding-profile
defines the device as managed, the Device Onboarding-client script must retrieve the management IP address from the device and post it to NSO thru the
report-progress action callback.
This is a sample of the get-bootstrapping-data call back script.
curl -i -u ztpclient:topsecret \
-H "Content-Type:application/yang-data+json" \
-X POST \
-d '{"input":{ "model" : "CSR1KV","os-name" : "cisco-ioxr","vendor" :
"Cisco","unique-id" : "AAO124GF","os-version" : "12.1"}}' \
http://nsoztpserver:8090/restconf/operations/cisco-ztp:ztp/classic/get-bootstrapping-data
<< Response body >>
{
"cisco-ztp:output": { "bootstrap-information": {
"boot-image": {
"os-name": "cisco-ioxr",
"os-version": "12.3",
"download-uri": "http://sample.domain/8894-235/ios-xr-
12.3.tar.gz",
"md5-hash-value": "195b174c9a13de04ca44f51c222d14b0"
},
"day-0-configuration": "!! IOS XR\nusername admin\n group root-lr\n password 0 admin\n!\nhostname xr_2\n!\nvrf Mgmt-intf\n address-family ipv4 unicast\n!\ninterface MgmtEth0/RSP0/CPU0/0\n vrf Mgmt-intf\n ipv4 address 192.168.20.1 255.255.255.0\n!\nrouter static\n vrf Mgmt-intf\n address- family ipv4 unicast\n 0.0.0.0/0 192.168.122.1 110\n !\n!\nssh server v2\nssh server vrf Mgmt-intf\n\n"
}
}
}
** report-progress callback **
curl -i -u ztpclient:topsecret \
-H "Content-Type:application/yang-data+json" \
-X POST \
-d '{"input" : {"unique-id": "AAO124GF","progress-type": "bootstrap- complete"}}' \
http://nsoztpserver:8090/restconf/operations/cisco-ztp:ztp/classic/report-progress
<< Response header >>
HTTP/1.1 204 No Content

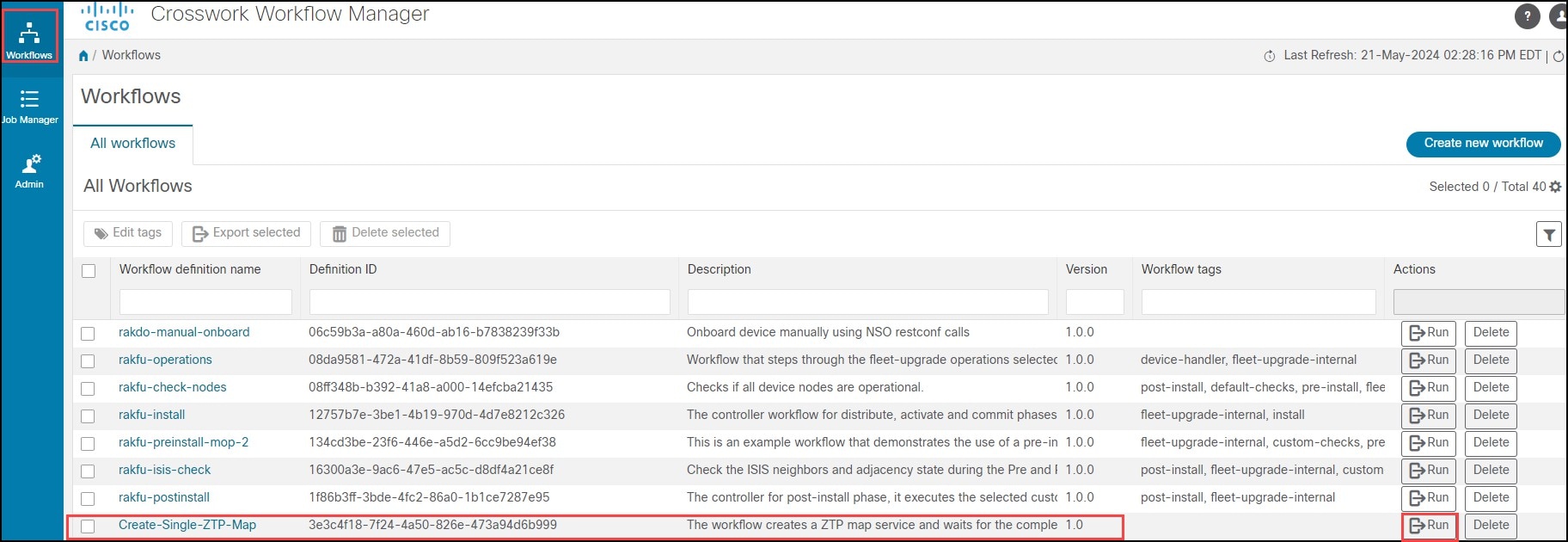
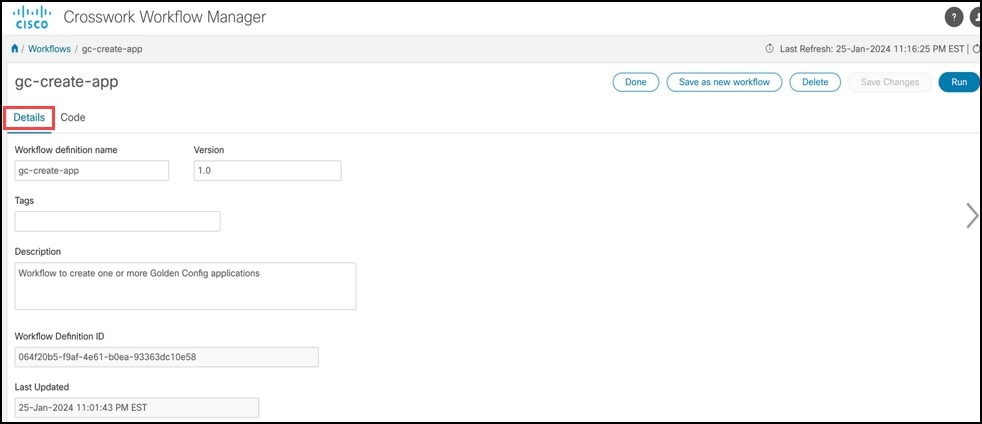
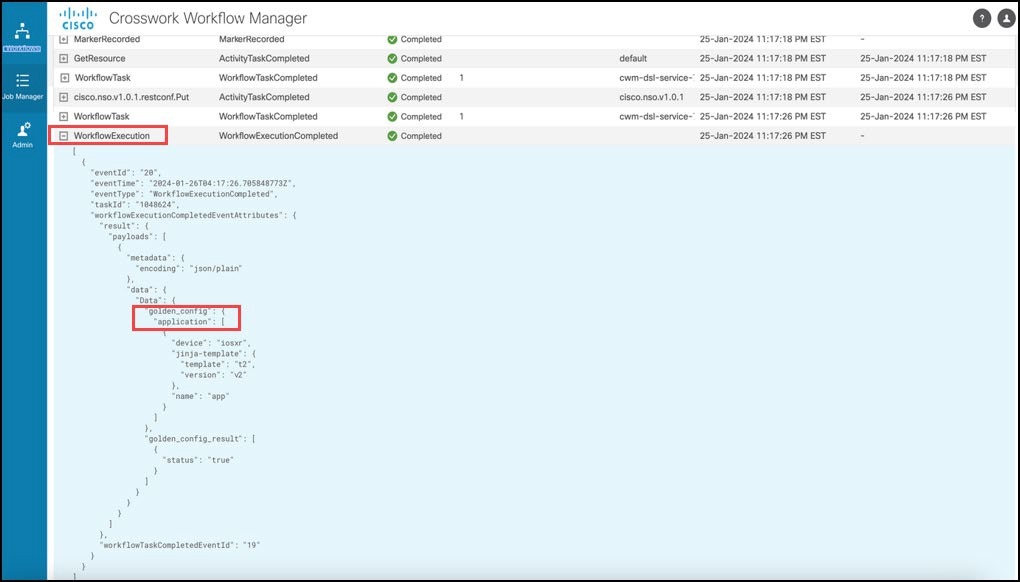
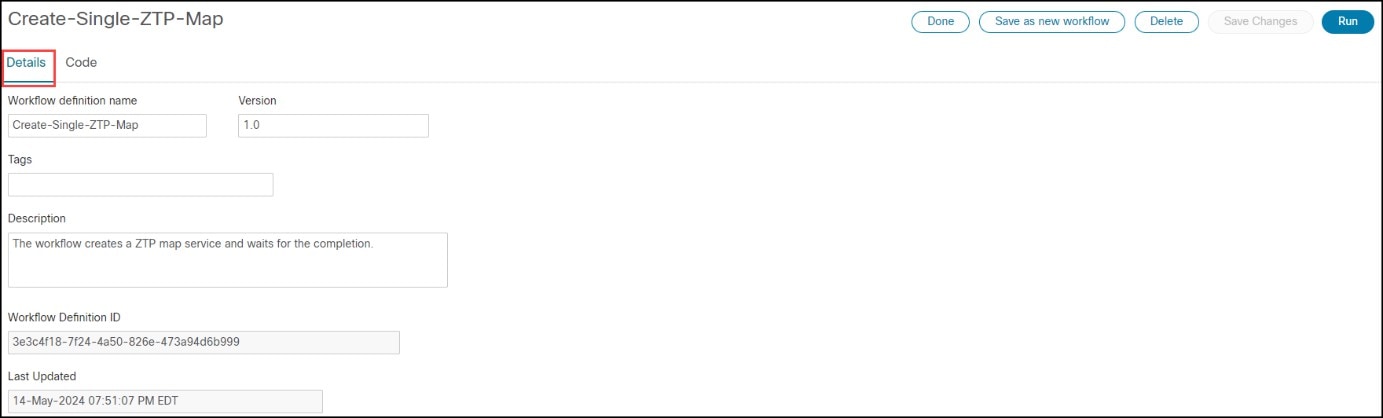 Click the Workflow Name to open the Workflow screen. (Details tab is the default.) The Workflow Definition ID and Update Date are auto filled.
Click the Workflow Name to open the Workflow screen. (Details tab is the default.) The Workflow Definition ID and Update Date are auto filled.
 Feedback
Feedback