Basic Configuration
Before you begin using CPS vDRA, perform the following basic configurations in CPS DRA:
-
Configure Systems
-
Configure Diameter Application
-
Configure Routing AVP Definitions
Configure Systems
In CPS DRA, navigate to the System and Plugin Configuration.
Configure the stack in DRA Configuration plugin.
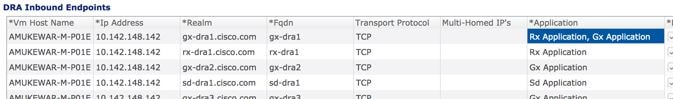
Configure the DRA Inbound Endpoints for incoming peer connections and DRA Outbound Endpoints for outgoing peer connection.
You can choose the Transport Protocol as TCP and SCTP depending on your requirement.
You can also specify the IPv4 or IPv6 address configuration for the stack connection.
The following image shows a sample configuration.
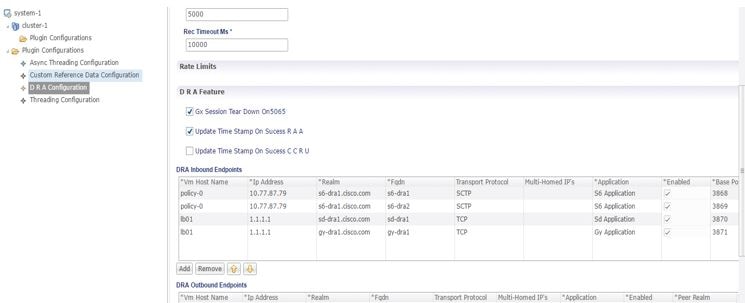
For more information, see DRA Configuration.
Configure Diameter Application
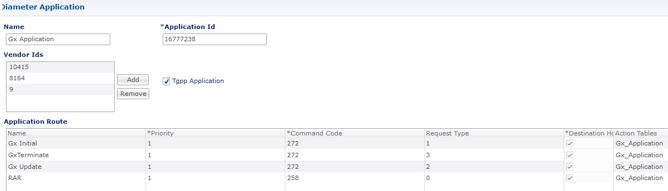
Configure the Diameter applications that are required to be connected over various interfaces with CPS vDRA.
The following image is a sample of a Gx application configuration:
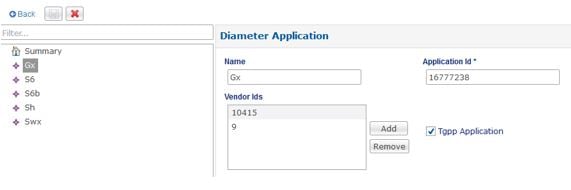
For more information, see Diameter Application.
Configure Multiple Diameter Applications for a Peer Connection
Previously, vDRA supported a single application on a peer connection. In this release, vDRA supports multiple applications on a peer connection.
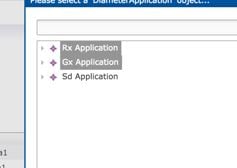
To configure multiple applications for a peer connection, go to vDRA Inbound Endpoints in DRA Plugin configuration. In the Applications field, select the button as shown:
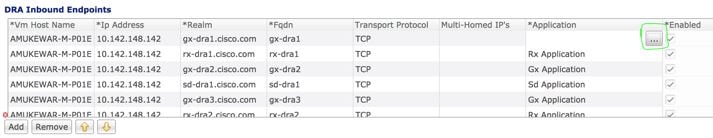
Select all the applications you require.
The following example shows multiple Diameter applications for a peer connection:
Configure Routing AVP Definitions
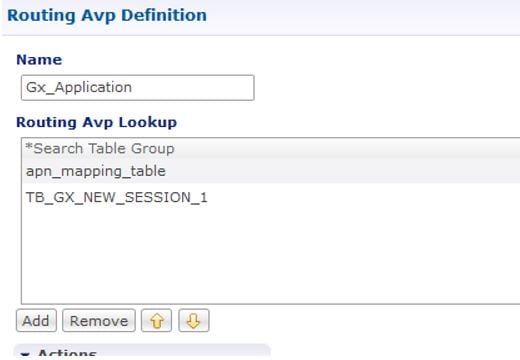
Configure the Routing AVP definitions to route calls on the basis of the AVPs that are present in diameter message.
In the Routing AVP Definition page, you specify the Application name and the table for table-driven routing.
In the Diameter Application page, configure the Application Route for table-driven routing.
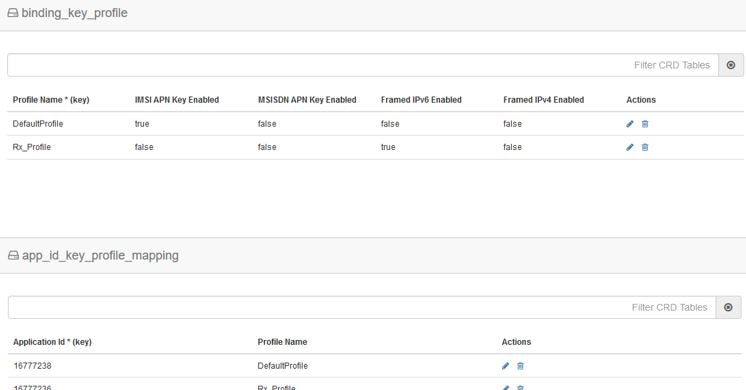
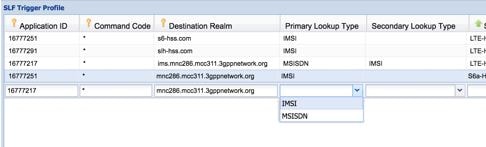
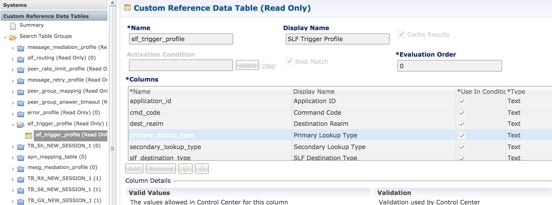
The following screenshots show a sample configuration:

 Feedback
Feedback